Social WiFi: What It Is and How It Drives Customer Engagement
This authoritative technical reference guide covers the architecture, deployment, and business value of Social WiFi — the practice of authenticating guest network users via OAuth 2.0 social login on a captive portal. It provides IT managers, network architects, and venue operations directors with actionable guidance on technical implementation, GDPR compliance, and leveraging captured first-party data for targeted customer engagement. Venue operators across hospitality, retail, and events sectors will find concrete deployment frameworks and real-world scenarios that demonstrate measurable ROI.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: Architecture and Standards
- The OAuth 2.0 Authentication Flow
- Walled Garden Configuration
- MAC Randomisation and Identity Persistence
- Network Segmentation and Security
- Implementation Guide
- Step 1: Infrastructure Readiness Assessment
- Step 2: Captive Portal Design and UX Optimisation
- Step 3: GDPR Compliance Configuration
- Step 4: CRM and Marketing Automation Integration
- Best Practices
- Walled Garden Maintenance
- Consent Record Management
- Splash Page A/B Testing
- Network Segmentation Review
- Troubleshooting & Risk Mitigation
- ROI & Business Impact
- Key Performance Indicators
- Hospitality Case Study
- Retail Case Study

Executive Summary
For modern physical venues — from retail chains and hotels to stadiums and conference centres — providing guest WiFi is no longer a differentiator; it is a baseline expectation. However, traditional deployments using open networks or pre-shared keys (PSKs) represent a significant missed opportunity. They provide connectivity but yield zero actionable intelligence about the users on the network.
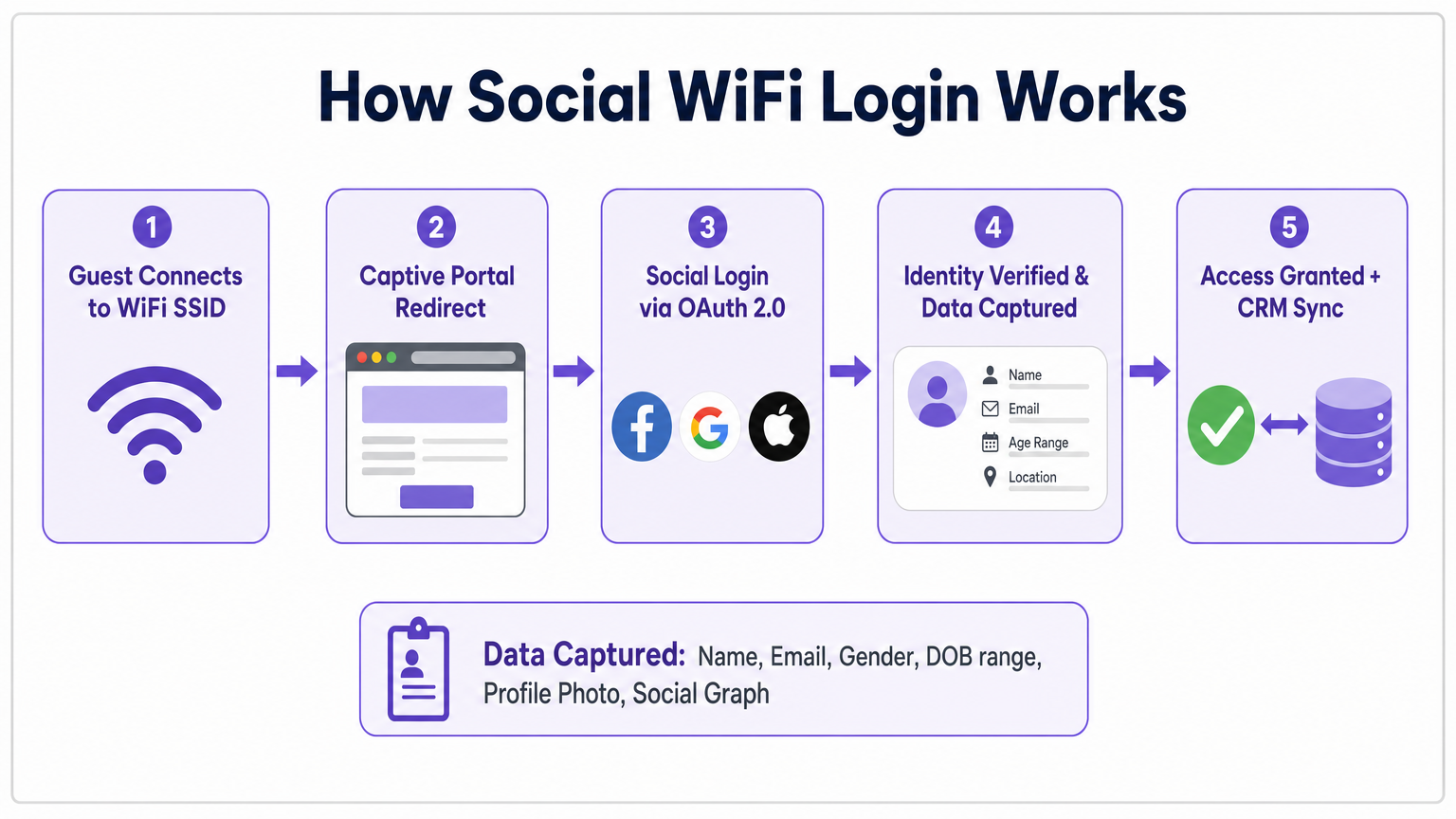
Social WiFi transforms this dynamic. By leveraging OAuth 2.0 via a captive portal, venues can authenticate users through their existing social media identities — Facebook, Google, Apple, or LinkedIn. This approach replaces anonymous MAC addresses with verified user profiles, capturing essential demographic and contact data at the point of access.
For IT managers, network architects, and CTOs, deploying social wifi requires strategic alignment of network infrastructure, security protocols, and data compliance frameworks — principally GDPR. When implemented correctly using an enterprise platform like Purple's Guest WiFi solution, it shifts the WiFi network from a pure cost centre to a strategic asset that drives measurable ROI through targeted marketing and enhanced customer engagement. This guide covers what social wifi is, how the technical architecture works, what data you actually get, the compliance implications, and how to use social connections for marketing at scale.
Technical Deep-Dive: Architecture and Standards
Understanding what is social wifi marketing requires a clear view of the underlying technical stack. The implementation relies on a seamless interaction between local network infrastructure, the captive portal, and external identity providers.
The OAuth 2.0 Authentication Flow
The sequence below describes a standard Social WiFi authentication event:
- Association: The client device connects to the open Guest SSID broadcast by the access points.
- Interception: The network controller or gateway intercepts HTTP requests (and HTTPS via DNS interception) and issues a redirect to the captive portal URL.
- Captive Portal Presentation: The user's Captive Network Assistant (CNA) — the lightweight browser built into iOS, Android, Windows, and macOS — displays the branded splash page.
- Social Login Initiation: The user selects a social provider (e.g., Google). The portal constructs an OAuth 2.0 authorisation request and redirects the client to the provider's authentication endpoint.
- Consent Grant: The user authenticates with their social provider and explicitly grants the requested data scopes to the captive portal application.
- Token Exchange: The provider returns an authorisation code to the portal's callback URL. The portal server-side exchanges this for an access token and retrieves the user's profile data via the provider's API.
- Network Access Grant: The captive portal platform signals the network controller — typically via a RADIUS Change of Authorisation (CoA) message or a vendor-specific API call — to authorise the client's MAC address and move it to the authenticated VLAN.
- CRM Synchronisation: The captured profile data is pushed to the venue's CRM or marketing automation platform in real time.
Walled Garden Configuration
A critical and frequently misconfigured element of any social wifi network deployment is the Walled Garden — the pre-authentication access control list (ACL) on the network controller that defines which IP addresses and domains a device may reach before it has been granted full internet access.
To complete the OAuth flow, the client device must be able to reach the identity providers' authentication servers before authentication is complete. This means the Walled Garden must include the relevant endpoints for every social provider offered on the splash page. Because major providers such as Google and Facebook use dynamic IP ranges served from large CDNs, it is best practice to configure Walled Gardens using domain names (FQDNs) where the controller supports DNS-based ACLs, rather than static IP ranges that will inevitably become stale.
Failure to maintain an accurate Walled Garden is the single most common cause of Social WiFi deployment failures in production environments.
MAC Randomisation and Identity Persistence
Modern iOS (since iOS 14) and Android (since Android 10) devices generate a randomised MAC address for each network they associate with. This privacy feature directly undermines the traditional approach of using hardware addresses to identify and track returning visitors.
Social WiFi directly solves this problem. Because the user authenticates with a persistent social identity — their Google account, for instance — the platform can identify them across sessions regardless of the MAC address their device presents. This makes authenticated profiles substantially more valuable than any hardware-based tracking approach, and it is a key reason why wifi social network solutions are increasingly the default for enterprise venue deployments.
Network Segmentation and Security
The Guest SSID used for Social WiFi is typically an open (unencrypted) network to facilitate the captive portal redirect mechanism. This is architecturally acceptable provided strict network segmentation is enforced. The guest VLAN must be isolated from all internal corporate infrastructure, point-of-sale systems, and any network segment that falls within PCI DSS scope. A flat network where guest traffic can reach internal systems is a critical security failure.
For venues operating in regulated environments — such as Healthcare facilities — additional controls are required. The guest network must be treated as an untrusted segment, and any integration with clinical systems must be explicitly scoped and approved. For further context on secure clinical deployments, see WiFi in Hospitals: A Guide to Secure Clinical Networks .
Implementation Guide
Deploying a robust Social WiFi solution requires careful planning across network infrastructure, data governance, and marketing integration. The following steps apply to most enterprise venue deployments.
Step 1: Infrastructure Readiness Assessment
Before configuring any captive portal, audit your existing wireless infrastructure. Confirm that your access point controllers support external captive portals and RADIUS CoA. Major enterprise vendors — Cisco Meraki, Aruba Networks, Ruckus, Extreme Networks, and Fortinet — all support this capability, but the specific configuration method varies. Verify that your controller firmware is current, as older versions may have known issues with CNA detection or RADIUS CoA handling.
For Hospitality deployments, assess access point density against expected peak concurrent client counts. A 200-room hotel with a full-occupancy scenario of 400+ devices requires careful RF planning to avoid association bottlenecks that will manifest as slow portal loads and poor user experience.
Step 2: Captive Portal Design and UX Optimisation
The captive portal is the digital front door to your venue. The majority of authentications will occur on smartphones, so the splash page must be mobile-first, lightweight, and fast-loading. Target a page weight under 200KB and a time-to-interactive under two seconds on a 4G connection.
Offer the social login providers most relevant to your demographic. For most consumer venues, Google and Facebook cover the vast majority of users. Apple Sign In is increasingly important for iOS-dominant demographics. Always provide a form-based email login as a fallback for users without social accounts.
The splash page must also satisfy GDPR requirements (detailed below), which means it must include clearly separated consent checkboxes and a visible link to your privacy policy — all without making the page feel like a compliance obstacle.
Step 3: GDPR Compliance Configuration

Operating a data-capturing network in the UK or EU requires strict adherence to GDPR. The lawful basis for processing personal data in a Social WiFi context is typically Consent. This has direct implications for splash page design and backend data management.
Consent must be freely given, specific, informed, and unambiguous. You must not bundle acceptance of network terms of service with consent to marketing communications — these must be independent, un-pre-ticked checkboxes. Your privacy policy must be clearly accessible before the user logs in. You must practice data minimisation: only request the OAuth scopes genuinely necessary for your stated purpose. And you must maintain a mechanism for users to exercise their right to erasure.
For a comprehensive overview of how these requirements interact with your marketing strategy, see How Does WiFi Marketing Work? .
Step 4: CRM and Marketing Automation Integration
The data captured via Social WiFi is only valuable if it is operationalised. Integrate your WiFi analytics platform with your existing CRM — Salesforce, HubSpot, or a sector-specific system — via API or webhook. Configure automated workflows to trigger on new profile creation: a welcome email, a loyalty programme invitation, or a post-visit survey.
For Retail environments, this integration enables immediate personalisation. A customer who has previously purchased in a specific category can be served a relevant offer the moment they authenticate at any store in the estate. For Transport hubs, the data feeds into passenger flow analytics and commercial tenant performance reporting.
Best Practices
Walled Garden Maintenance
Treat your Walled Garden configuration as a living document. Social providers update their CDN and authentication endpoint IP ranges regularly. Assign ownership of Walled Garden maintenance to a named team member and schedule quarterly reviews. Subscribe to the developer changelogs of each social provider you support.
Consent Record Management
Maintain a timestamped record of each user's consent, including which version of your privacy policy was in force at the time of consent. This is essential for demonstrating compliance in the event of a regulatory inquiry. Your WiFi platform should provide this audit trail natively.
Splash Page A/B Testing
Treat your captive portal as a conversion funnel. Test variations of your splash page — different social provider ordering, different value propositions, different imagery — and measure the impact on authentication completion rates. A 10% improvement in completion rate across a high-footfall venue translates directly to thousands of additional profiles per month.
Network Segmentation Review
Conduct an annual review of your guest VLAN segmentation to ensure it remains isolated as your network evolves. Infrastructure changes — new switches, controller upgrades, VLAN reconfigurations — can inadvertently introduce routing paths between guest and corporate segments.
Troubleshooting & Risk Mitigation
Even with careful planning, specific failure modes are common in Social WiFi deployments.
| Failure Mode | Symptoms | Root Cause | Mitigation |
|---|---|---|---|
| CNA Not Triggering | Users see no portal; assume WiFi is broken | Controller not responding to OS detection probes | Configure DNS interception for captive.apple.com, connectivitycheck.gstatic.com, etc. |
| OAuth Flow Timeout | Social login page fails to load or hangs | Walled Garden missing provider endpoints | Audit and update Walled Garden; use FQDN-based rules |
| Slow Portal Load | High abandonment rate at splash page | Portal hosted on distant server; heavy page assets | Use CDN; optimise page weight; test on mobile connections |
| Returning Users Not Recognised | Analytics show inflated new-user counts | MAC randomisation breaking device tracking | Rely on authenticated identity, not MAC; use persistent cookies |
| RADIUS CoA Failure | Authentication completes but internet access not granted | RADIUS shared secret mismatch; firewall blocking CoA port (UDP 3799) | Verify RADIUS configuration; open CoA port on controller firewall |
For venues with complex multi-site deployments, the Indoor Positioning System: UWB, BLE, & WiFi Guide provides additional context on how WiFi-based positioning data can complement Social WiFi analytics.
ROI & Business Impact
The business case for Social WiFi is well-established across multiple venue categories. The WiFi Analytics platform underpinning a Social WiFi deployment provides the measurement framework to quantify this value.
Key Performance Indicators
| KPI | Measurement Method | Typical Outcome |
|---|---|---|
| CRM Database Growth Rate | New authenticated profiles per month | 200–400% increase vs. web sign-up alone |
| Email Marketing Open Rate | Campaign analytics post-deployment | 25–40% (vs. 15–20% industry average for purchased lists) |
| Return Visit Rate | Repeat MAC/identity appearances | Measurable uplift within 90 days |
| Campaign Conversion Rate | Attributed transactions from WiFi-triggered campaigns | 3–8x higher than untargeted broadcast |
| Data Quality Score | Email deliverability rate on captured addresses | 85–95% (social accounts have verified emails) |
Hospitality Case Study
A 350-room UK hotel group deployed Social WiFi across four properties using the Purple platform. Within 60 days, they had captured over 12,000 verified guest profiles with email opt-ins. Automated post-stay email sequences achieved a 34% open rate and a 6.2% direct booking conversion — measurably reducing OTA commission costs. The IT deployment took less than two working days per property, with the primary effort focused on Walled Garden configuration and CRM API integration.
Retail Case Study
A national fashion retailer with 85 stores standardised on Social WiFi across the estate. By aggregating authentication data with point-of-sale records, the marketing team identified that customers who authenticated to the in-store WiFi had a 23% higher average basket value than those who did not. Targeted push notifications sent to WiFi-authenticated users within 24 hours of a store visit achieved a 12% redemption rate on personalised discount codes — a campaign that would have been impossible without the first-party data infrastructure Social WiFi provided.
For implementation support, platform documentation, and industry-specific deployment guides, visit purple.ai .
Key Terms & Definitions
Social WiFi
A guest network authentication mechanism that uses OAuth 2.0 to allow users to log in to a captive portal using their existing social media accounts, capturing verified identity and demographic data in the process.
The primary subject of this guide. IT teams encounter this when evaluating guest network strategies for venues with a marketing or data capture objective.
Captive Portal
A web page that a user is required to view and interact with before access is granted to a public network. Implemented via HTTP interception and DNS redirection at the network controller level.
The primary user interface for Social WiFi and the mechanism through which data capture and consent collection occurs.
OAuth 2.0
An open standard for access delegation that allows a user to grant a third-party application limited access to their account on another service, without sharing their password. Defined in RFC 6749.
The underlying protocol that enables secure social login. The WiFi operator never sees the user's social media password; they receive only the data scopes the user explicitly consents to share.
Walled Garden
A restricted set of IP addresses or domains that a device is permitted to access before it has completed authentication on the network. Implemented as a pre-authentication ACL on the network controller.
Essential for allowing the device to reach social media authentication servers during the OAuth flow. Misconfiguration is the most common cause of Social WiFi deployment failures.
RADIUS CoA (Change of Authorisation)
An extension to the RADIUS protocol (RFC 5176) that allows a RADIUS server to dynamically modify the authorisation attributes of an active session — for example, moving a device from a pre-authentication VLAN to a full-access VLAN.
The mechanism by which the captive portal platform instructs the network controller to grant internet access once the social login is successfully completed.
MAC Randomisation
A privacy feature in modern operating systems (iOS 14+, Android 10+) where the device presents a randomly generated MAC address when associating with a WiFi network, rather than its hardware-burned address.
Directly undermines hardware-based visitor tracking. Social WiFi mitigates this by anchoring sessions to authenticated user identities rather than device MAC addresses.
Data Minimisation
The GDPR principle (Article 5(1)(c)) that personal data collected must be adequate, relevant, and limited to what is necessary in relation to the purposes for which it is processed.
Directly governs which OAuth scopes you are permitted to request during social login. Requesting a user's full social graph to provide WiFi access is unlikely to satisfy this principle.
CNA (Captive Network Assistant)
A lightweight pseudo-browser built into operating systems (iOS, Android, Windows, macOS) that automatically detects the presence of a captive portal and displays it to the user without requiring them to open a full browser.
Understanding CNA detection behaviour — and the specific HTTP probes each OS uses — is essential for ensuring the splash page appears automatically when a user connects to the guest SSID.
First-Party Data
Information a company collects directly from its own customers or audience, which it owns and controls, as opposed to second-party (partner) or third-party (purchased) data.
Social WiFi is one of the most effective mechanisms for physical venues to build a large, high-quality first-party data asset, particularly as third-party cookies and device fingerprinting become less viable.
Case Studies
A 200-room hotel needs to implement a guest WiFi solution that captures actionable marketing data, ensures GDPR compliance, and provides a seamless experience for international guests who may use different social platforms.
Deploy an enterprise Guest WiFi platform (e.g., Purple) integrated with the existing WLAN controllers via external captive portal and RADIUS CoA. Configure the splash page to offer Google, Facebook, and Apple Sign In, with a form-based email fallback. Implement Walled Garden rules for all three providers using FQDN-based ACLs. Design the splash page with two independent consent checkboxes: one for terms of service (required) and one for marketing communications (optional). Link the privacy policy prominently. Integrate the platform with the hotel PMS and CRM via API to sync guest profiles and trigger automated post-stay email sequences. Set a data retention policy of 24 months with automated purge. Sign a Data Processing Agreement with the WiFi platform vendor.
A national retail chain with 85 stores wants to understand customer demographics and cross-store visitation patterns without requiring users to download a mobile app, and without relying on MAC address tracking.
Standardise the Guest SSID and captive portal configuration across all store locations using a centralised WiFi management platform. Implement Social WiFi with Google and Facebook login as primary options. Configure the platform to use authenticated user identity (not MAC address) as the primary tracking key, supplemented by persistent first-party cookies for sessions where the same device re-authenticates. Aggregate authentication events across all stores in the analytics platform to build cross-store visitation profiles. Segment the resulting audience by visit frequency, store location, and demographic attributes for targeted campaign activation.
Scenario Analysis
Q1. You are deploying Social WiFi at a new stadium with 40,000 capacity. Users are connecting to the SSID, but when they tap 'Login with Facebook', the page times out and fails to load. Standard form-based email login works correctly. What is the most likely cause, and what is your immediate remediation step?
💡 Hint:Consider what network access the device has before authentication is complete, and which specific traffic is required for the OAuth flow.
Show Recommended Approach
The Walled Garden (pre-authentication ACL) on the network controller is misconfigured or missing the necessary IP ranges and domains for Facebook's authentication servers. The device cannot reach Facebook's OAuth endpoints before it has been granted full internet access. Immediate remediation: identify the current Walled Garden configuration on the controller, add the required Facebook authentication domains (including facebook.com, fbcdn.net, and related CDN domains), and test the flow. Longer-term: switch to FQDN-based Walled Garden rules if the controller supports them, to avoid future breakage from IP range changes.
Q2. A retail client wants to track how often specific customers visit their stores across the country. Their current approach relies entirely on MAC address logging. They have noticed that their 'returning visitor' metric has dropped sharply over the past 18 months. What is the most likely cause, and how does Social WiFi address it?
💡 Hint:Consider privacy features introduced in major mobile operating systems since 2020.
Show Recommended Approach
The drop in returning visitor recognition is almost certainly caused by MAC address randomisation, introduced in iOS 14 and Android 10. Devices now present a different, randomly generated MAC address for each network, making it impossible to link visits across sessions using hardware addresses alone. Social WiFi addresses this by anchoring each session to a verified, persistent user identity (e.g., their Google account). Provided the user authenticates at each visit, the platform can identify them regardless of their current MAC address, restoring accurate return visit tracking.
Q3. Your marketing director wants to collect users' email addresses, phone numbers, date of birth, and their full Facebook friends list during the WiFi login process. As the IT Manager responsible for GDPR compliance, which specific principle do you invoke, and what is your recommended approach?
💡 Hint:Consider the GDPR principle governing the scope and volume of personal data collection.
Show Recommended Approach
You invoke the principle of Data Minimisation under GDPR Article 5(1)(c). You must only collect personal data that is adequate, relevant, and limited to what is necessary for the stated purpose. Collecting a user's entire Facebook friends list to provide WiFi access and basic marketing is disproportionate and almost certainly unlawful. The recommended approach is to restrict OAuth scopes to the minimum necessary: typically name, email address, and optionally age range and gender. Phone number and friends list should not be requested. Document the rationale for each scope requested as part of your data governance records.



