Technical Guides
Deep, expert-led guides covering guest WiFi, analytics, captive portals, and modern venue technology. Each guide includes diagrams, worked examples, and audio podcasts.
249 guides
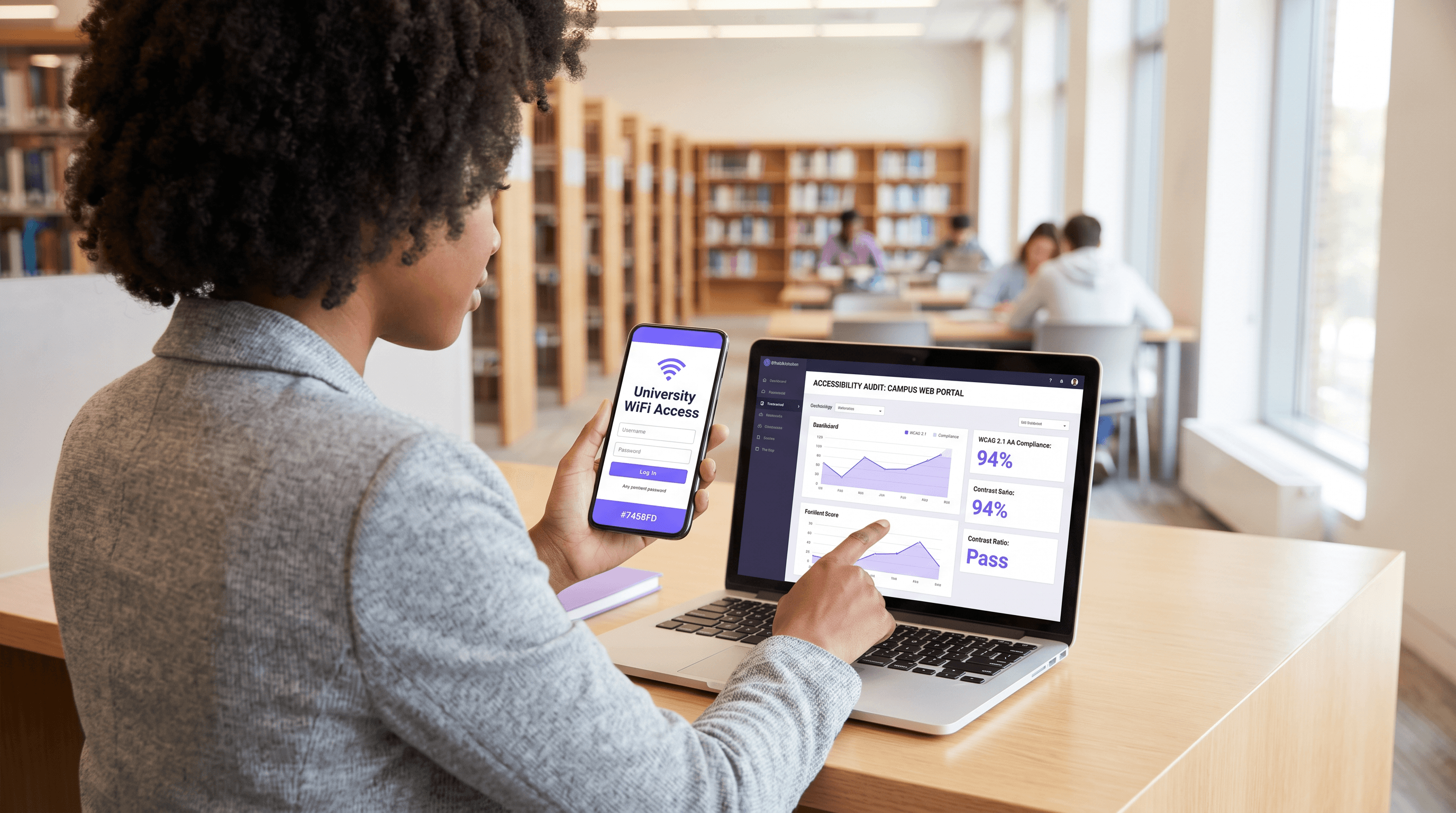
Captive Portal Accessibility: WCAG 2.1 Compliance Guide
This authoritative guide details how to design, test, and deploy captive portals that meet WCAG 2.1 AA accessibility standards. Essential reading for venue operators and IT teams navigating UK and US public-sector compliance mandates.
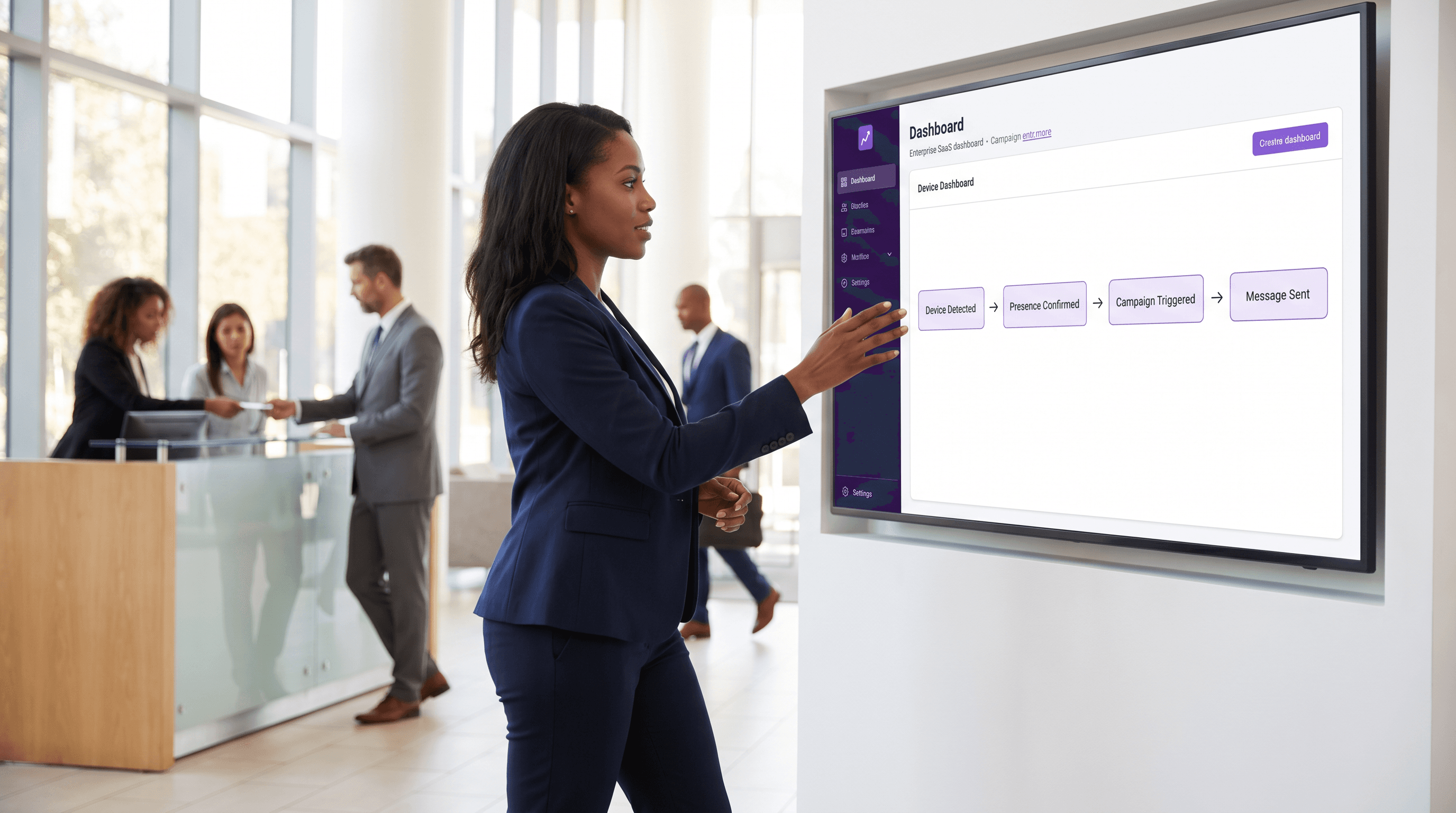
Event-Driven Marketing Automation Triggered by WiFi Presence
This architectural reference guide provides senior IT and operations leaders with a blueprint for designing event-driven marketing automation triggered by WiFi presence. It covers infrastructure requirements, latency management, deduplication strategies, and privacy compliance frameworks necessary for enterprise-scale deployments.
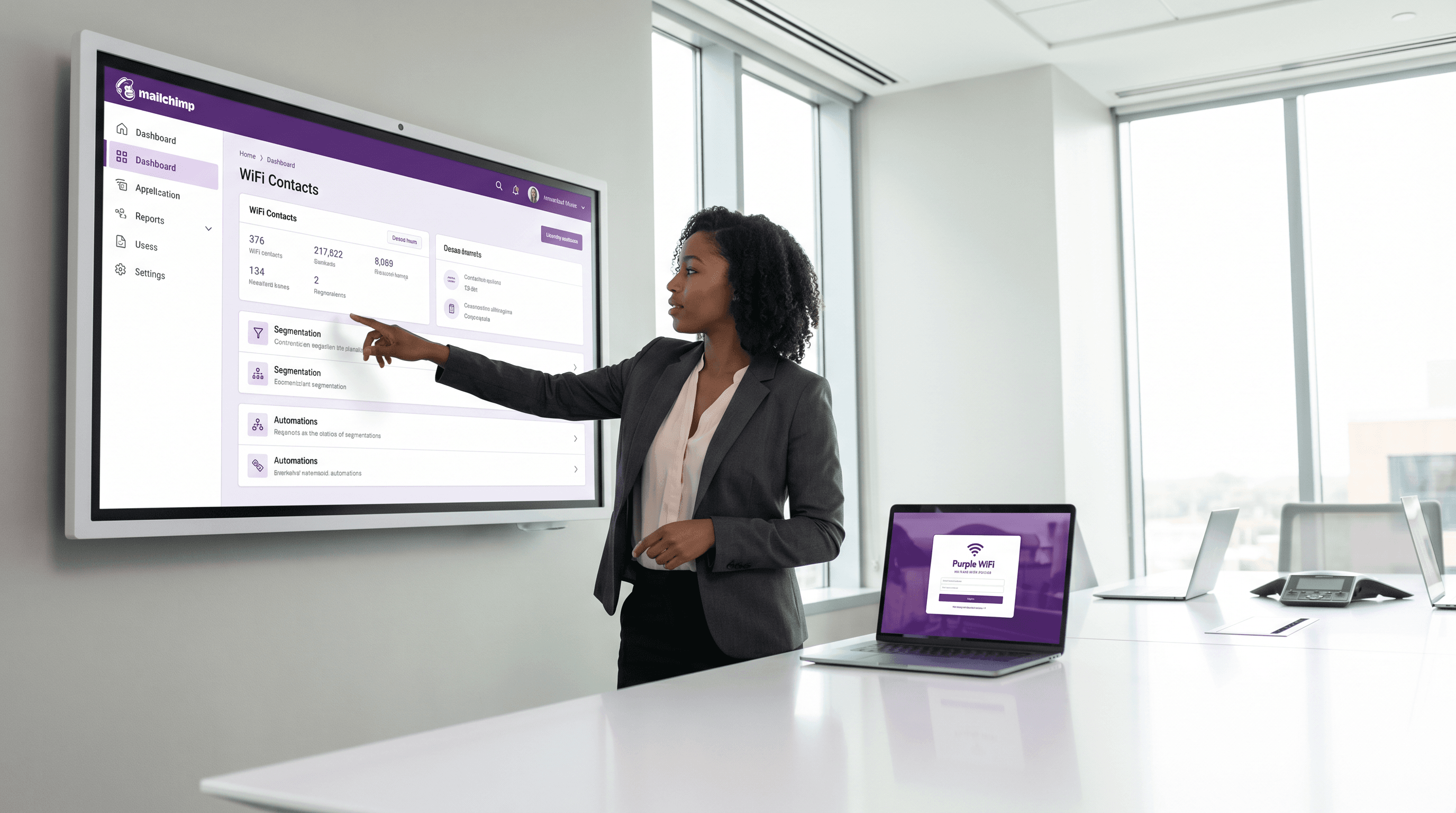
Mailchimp Plus Purple: Automated Email Marketing from WiFi Sign-ups
This authoritative guide details how to integrate Purple's guest WiFi platform with Mailchimp to automate email marketing from WiFi sign-ups. It covers architectural setup, segmentation tagging strategies, and the implementation of automated welcome journeys to convert on-premise footfall into engaged digital audiences.
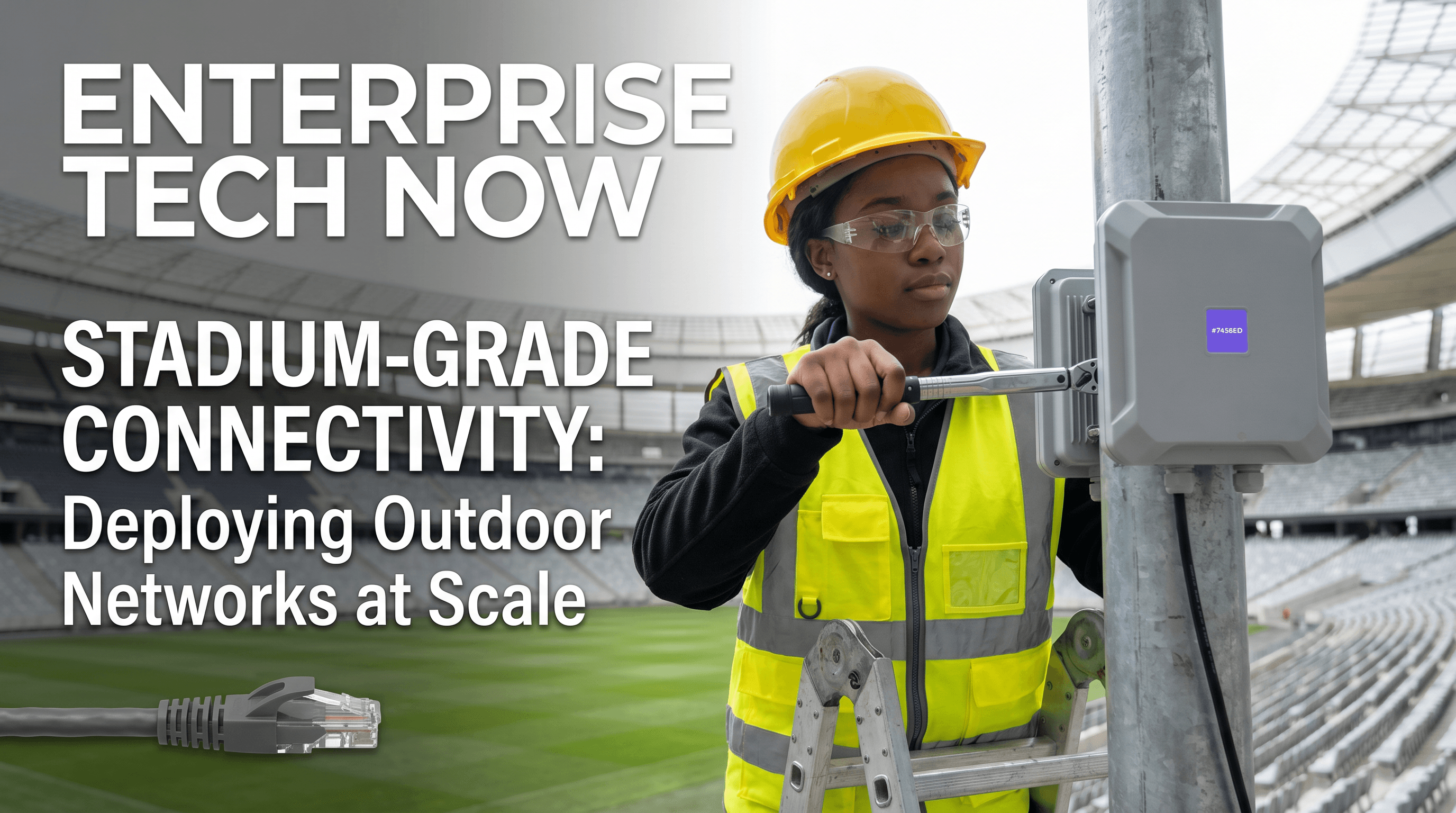
Outdoor WiFi Deployment: Weatherproofing, PoE, and Mesh Options
This authoritative guide details the critical engineering considerations for outdoor WiFi deployment, focusing on weatherproofing (IP ratings), Power over Ethernet (PoE) strategies for long cable runs, and the architectural trade-offs between mesh and wired backhaul. It provides actionable recommendations for IT leaders to ensure resilient, high-performance connectivity in hostile outdoor environments.
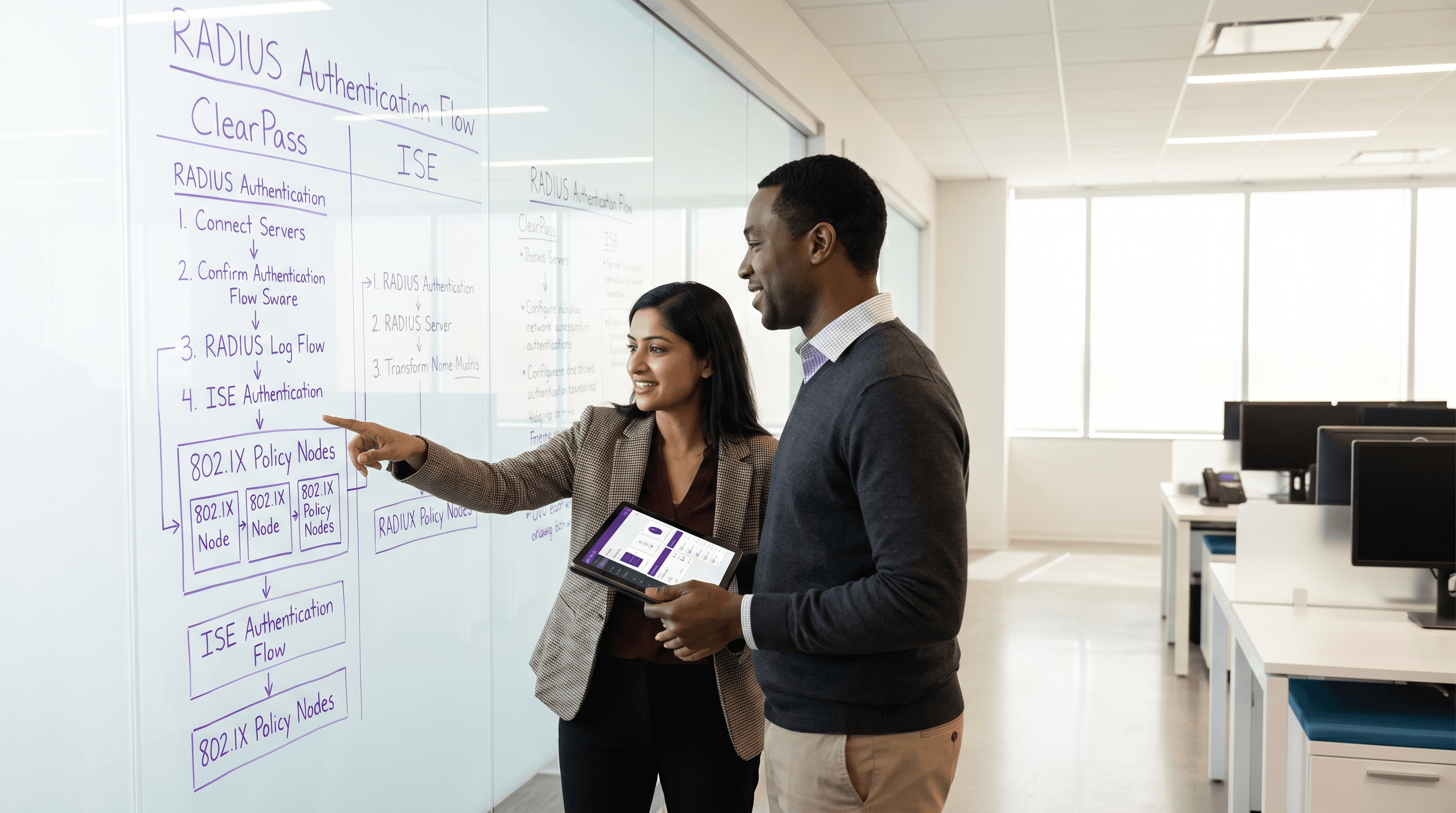
Aruba ClearPass vs Cisco ISE: NAC Platform Comparison
This technical reference guide provides a detailed, vendor-neutral comparison of Aruba ClearPass and Cisco ISE. It equips network architects and IT managers with actionable insights into architecture, deployment complexity, licensing, and integration ecosystems to drive informed NAC platform decisions.
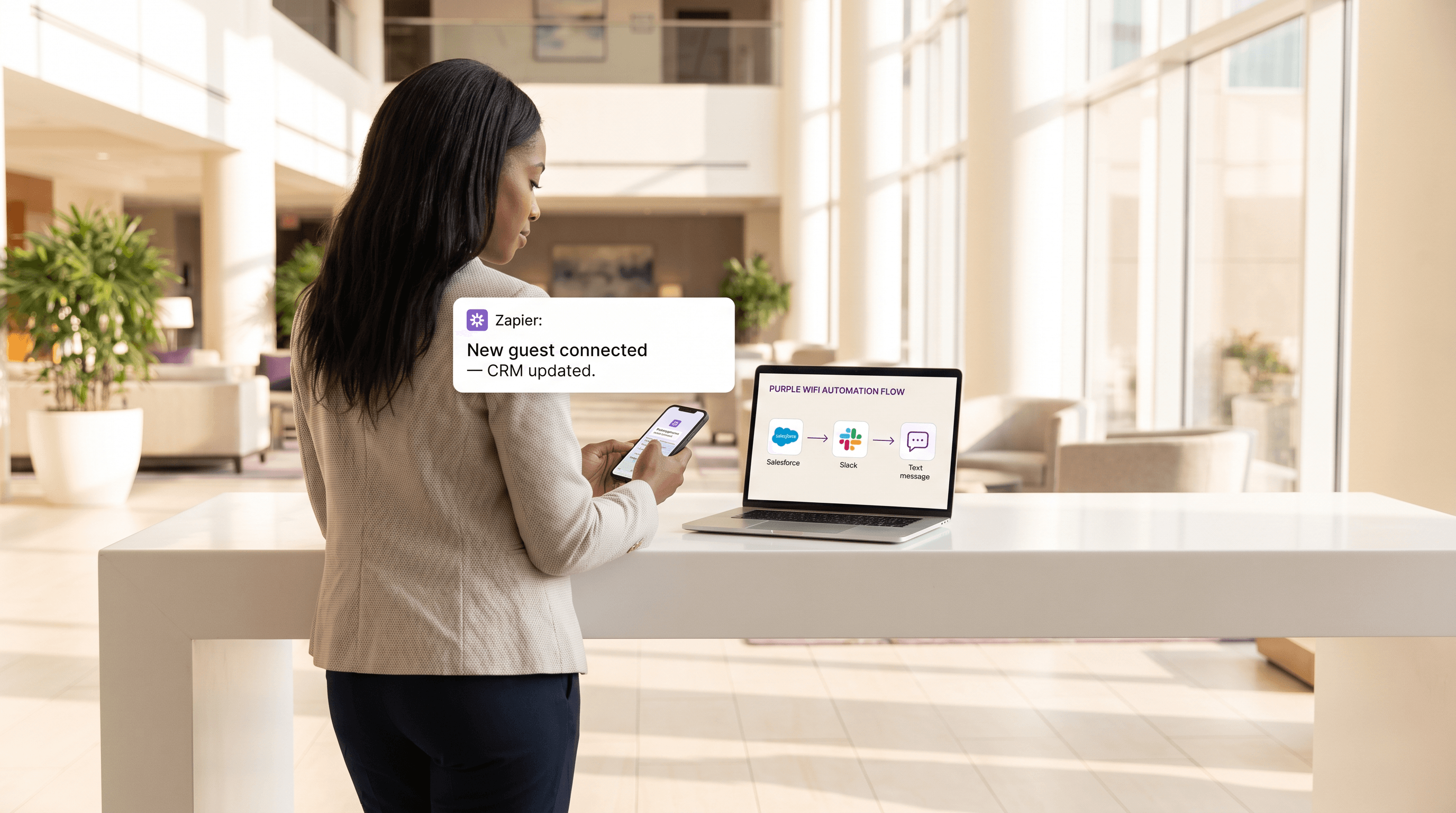
Connecting WiFi Events to 1,500+ Apps with Zapier and Purple
This guide details the technical architecture and practical implementation of integrating Purple WiFi with Zapier. It provides venue operators and IT teams with actionable recipes to automate CRM synchronisation, guest communications, and operational alerts without writing custom code.
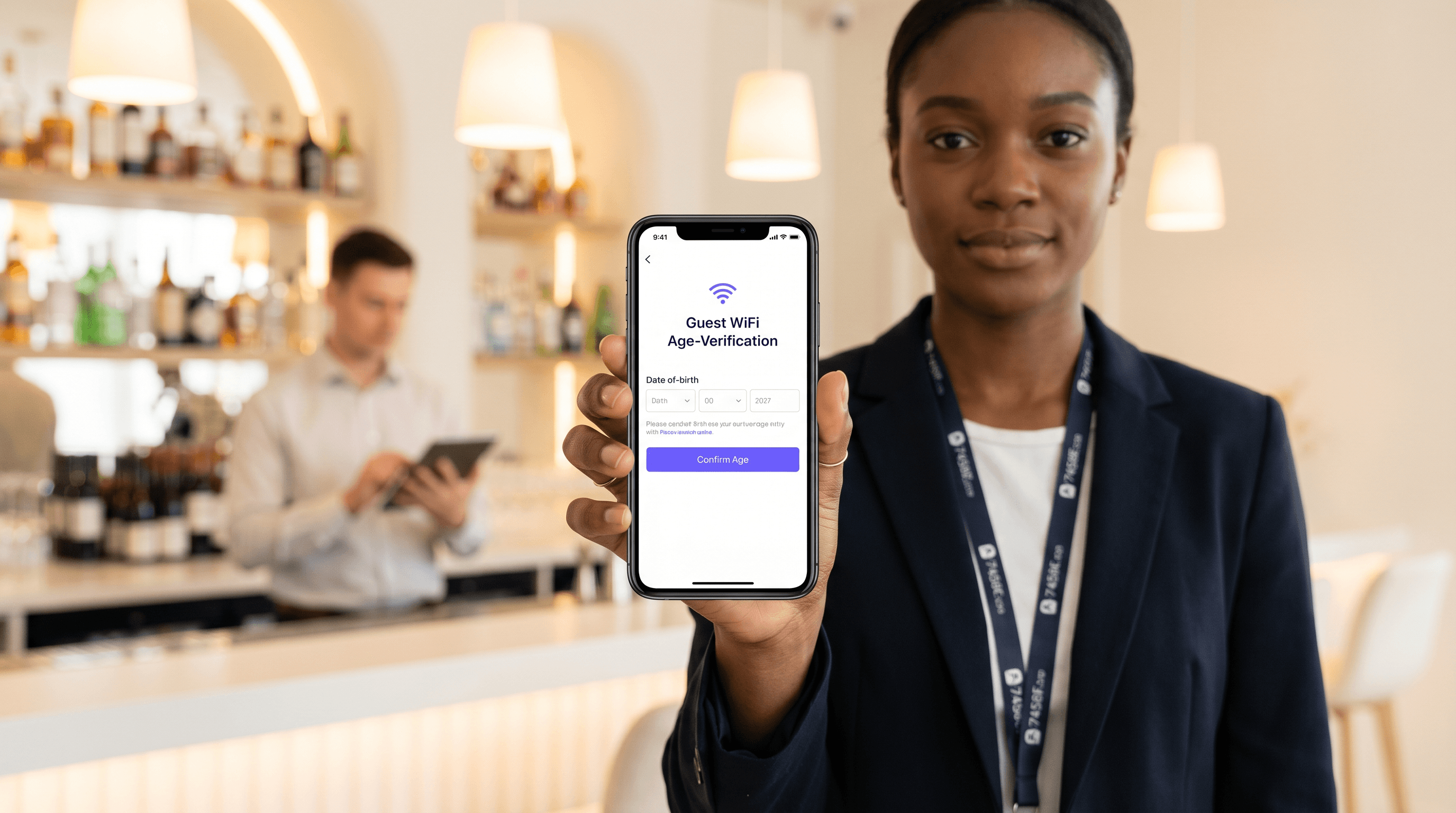
Age Verification on Guest WiFi: Compliance for Gaming, Alcohol, and Adult Venues
This authoritative technical reference guide explores the implementation of age verification on guest WiFi networks for high-risk venues like casinos, bars, and stadiums. It details compliance strategies, architectural deployment models, and the balance between regulatory requirements and user onboarding friction.

WiFi 7 MLO Explained: Multi-Link Operation for Seamless Roaming
This technical reference guide provides a comprehensive deep-dive into WiFi 7 Multi-Link Operation (MLO) for enterprise network architects and IT leaders. It demystifies the three MLO operating modes (eMLSR, NSTR, and STR), explains how MLO supersedes legacy band steering, and delivers actionable deployment guidance backed by real-world trial data from the Wireless Broadband Alliance. Venue operators in hospitality, retail, and large public spaces will find concrete implementation strategies and ROI evidence to support WiFi 7 investment decisions.

Rogue AP Detection: Protecting Venue WiFi from Impersonation Attacks
This guide provides a comprehensive technical reference for IT managers, network architects, and venue operations directors on deploying Wireless Intrusion Prevention Systems (WIPS) to detect and neutralise rogue access points and evil twin attacks. It covers detection methodologies, legal countermeasures, compliance requirements, and real-world implementation scenarios across hospitality, retail, and public-sector environments. Organisations that implement the strategies outlined here will strengthen their wireless security posture, reduce compliance risk, and protect both their infrastructure and their users from WiFi impersonation threats.
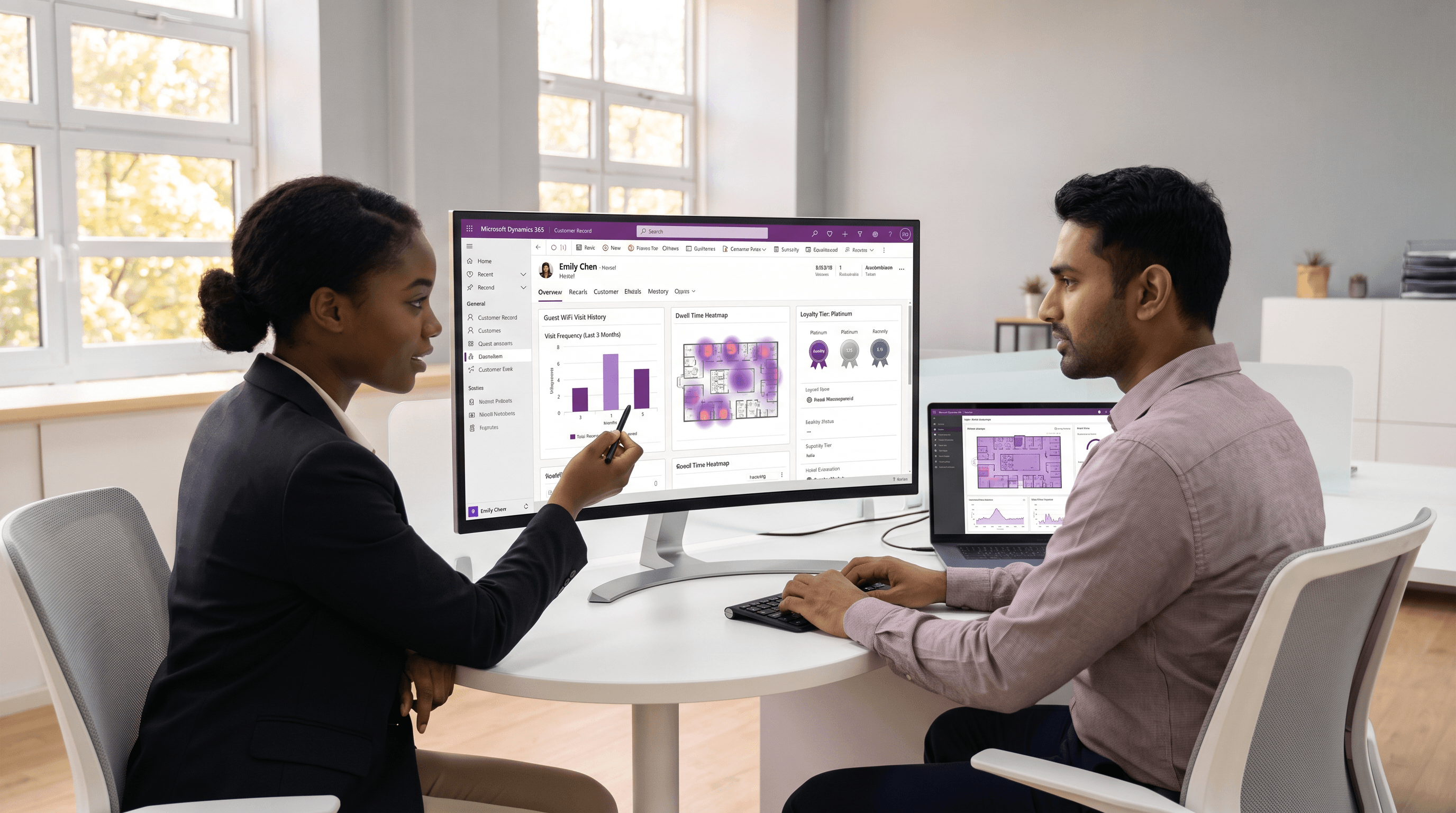
Microsoft Dynamics 365 and Guest WiFi Data Enrichment
This technical reference guide details the architecture, data modelling, and field mapping required to integrate guest WiFi data with Microsoft Dynamics 365. It provides actionable implementation strategies for IT managers and network architects to enrich unified customer profiles and drive measurable ROI in physical venues.
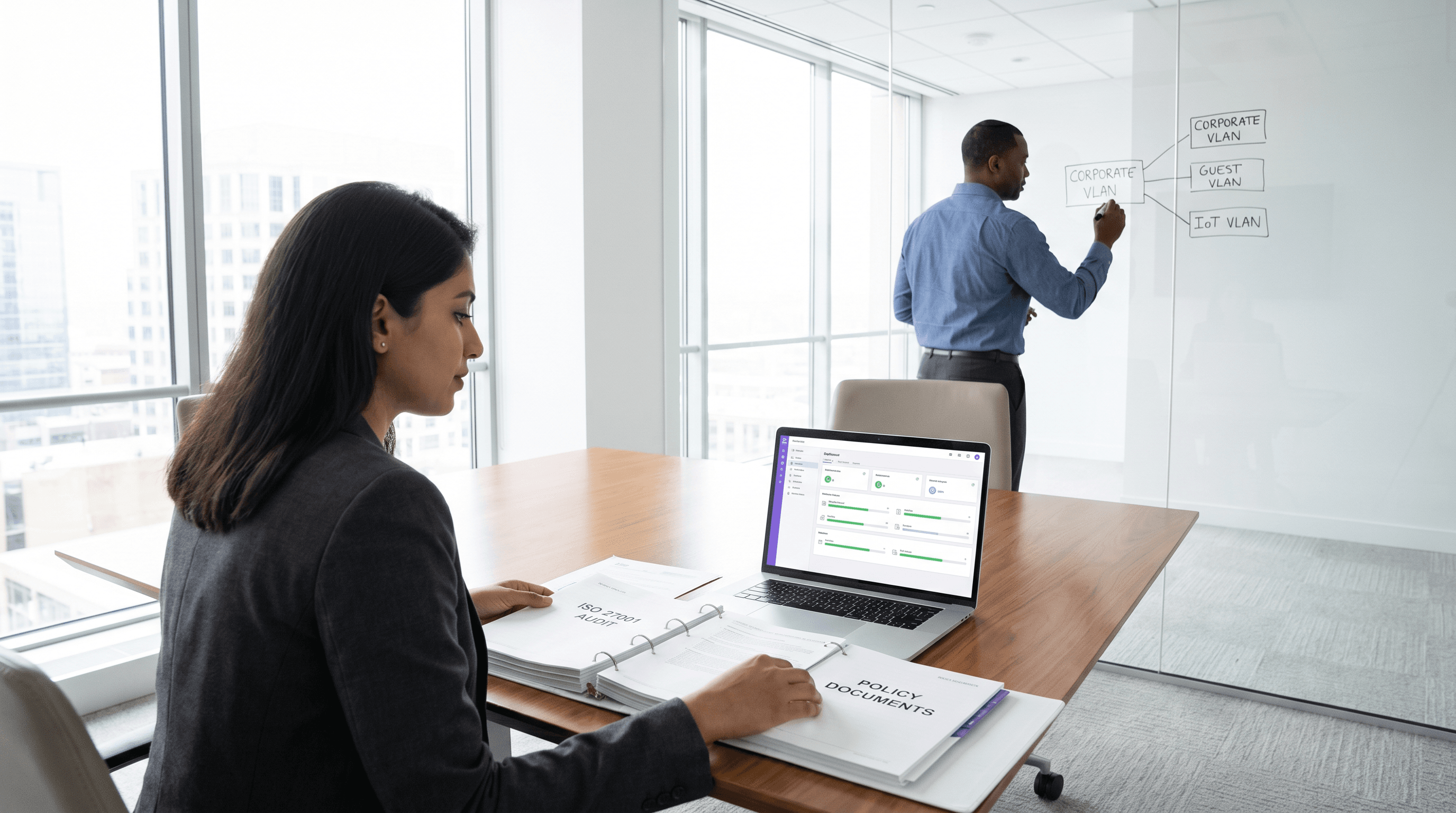
ISO 27001 Guest WiFi: A Compliance Primer
This authoritative technical reference maps guest WiFi deployments directly to ISO 27001:2022 controls, detailing network segregation, logging, and risk treatment requirements. It provides actionable guidance for IT managers and network architects on generating audit-ready evidence and leveraging vendor SOC 2 attestations to satisfy ISMS supplier assurance mandates.
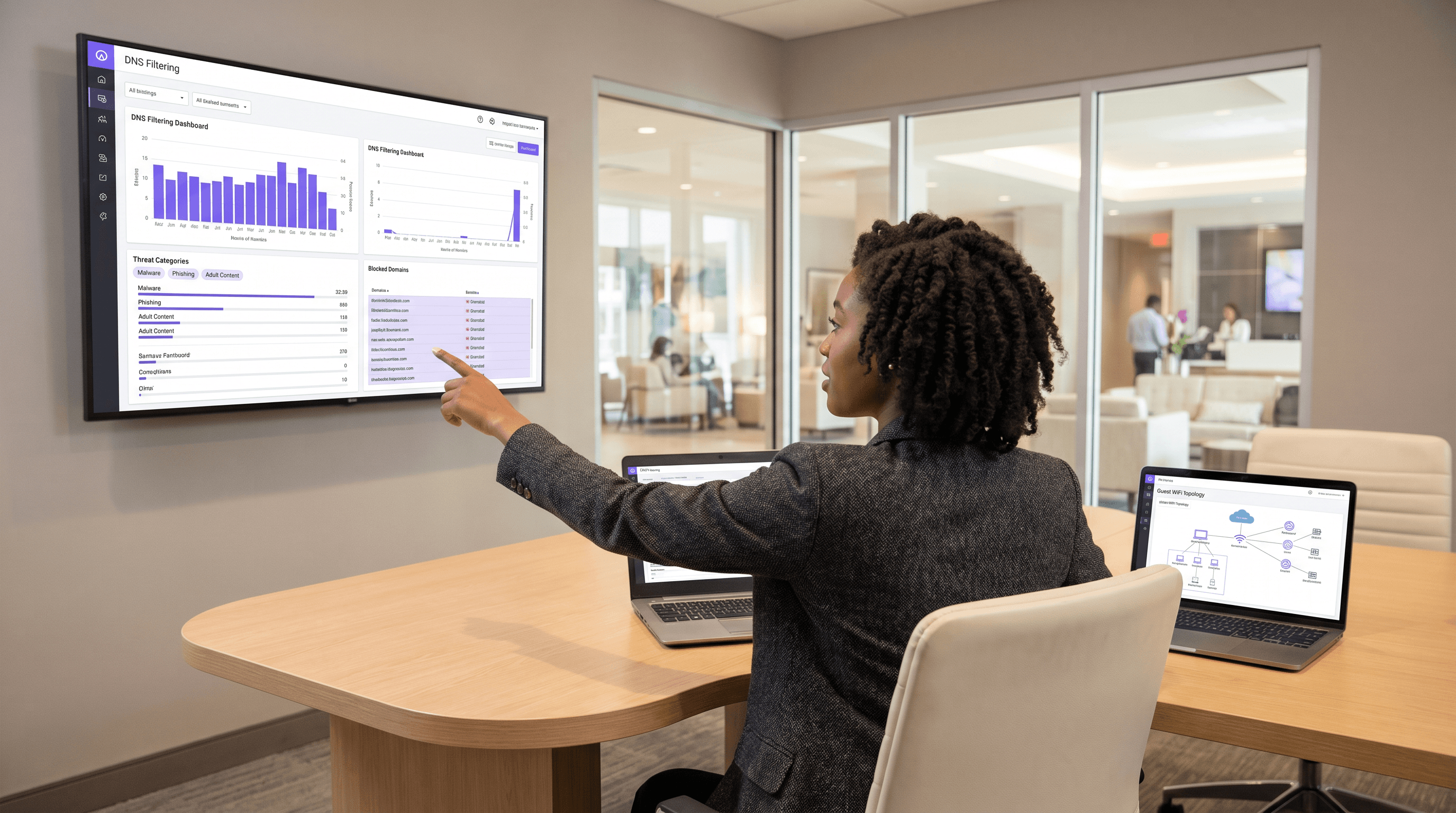
DNS Filtering for Guest WiFi: Blocking Malware and Inappropriate Content
This guide provides IT managers, network architects, and venue operations directors with a definitive technical reference for deploying DNS filtering on guest WiFi networks. It covers the architecture of DNS-level threat blocking, a vendor comparison of leading cloud DNS services, step-by-step implementation guidance, and real-world case studies from hospitality and retail environments. DNS filtering is the most cost-effective first line of defence against malware, phishing, and inappropriate content on public-facing networks, and this guide equips teams to deploy it confidently and in compliance with PCI DSS, GDPR, and HIPAA requirements.
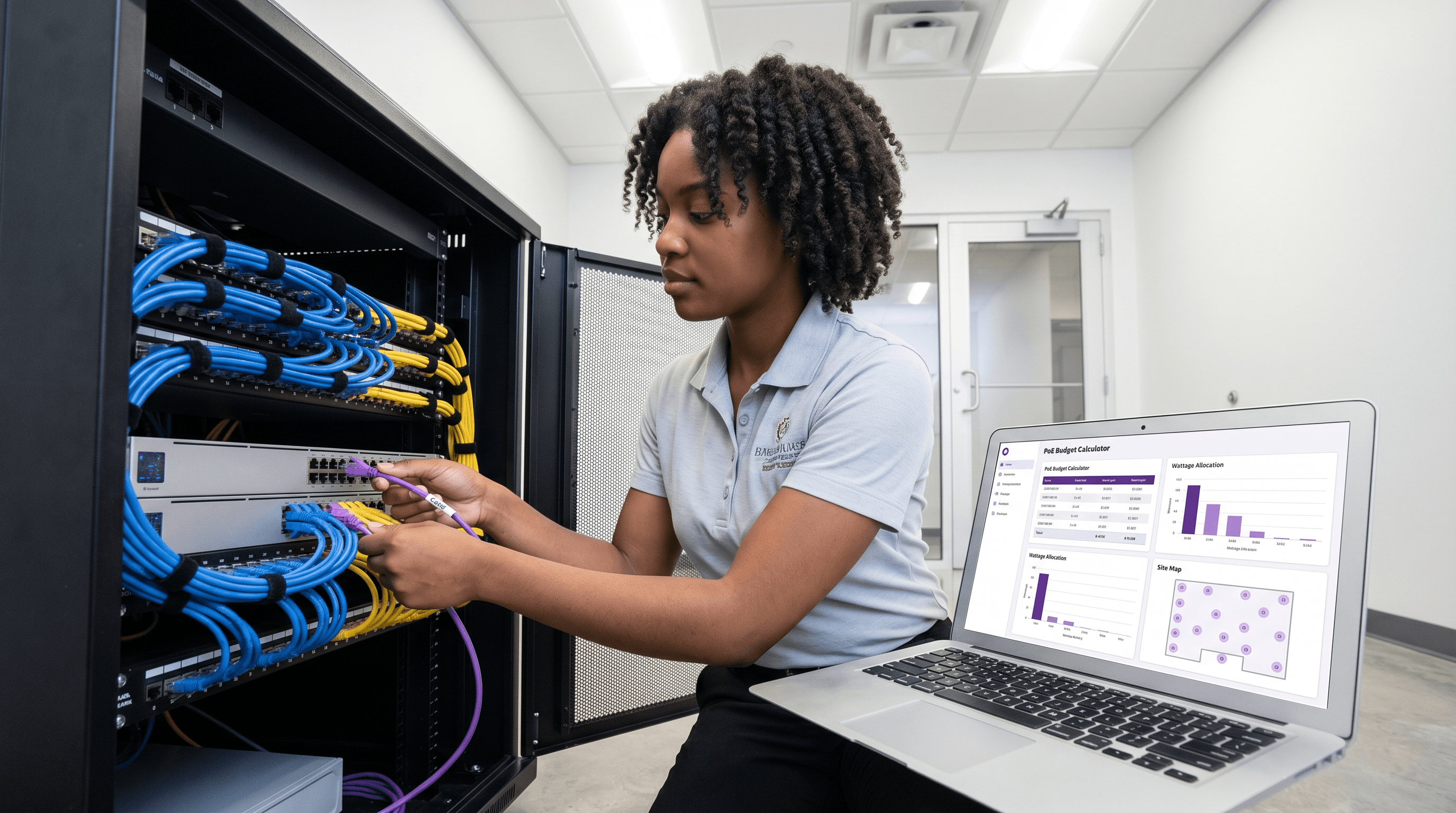
PoE Budget Planning for Multi-Site WiFi Deployments
This guide provides a practical framework for calculating Power over Ethernet (PoE) budgets across multi-site WiFi deployments. It covers the transition to PoE++ for WiFi 6E and 7, switch sizing strategies, and methods to future-proof infrastructure while mitigating the risks of power oversubscription.
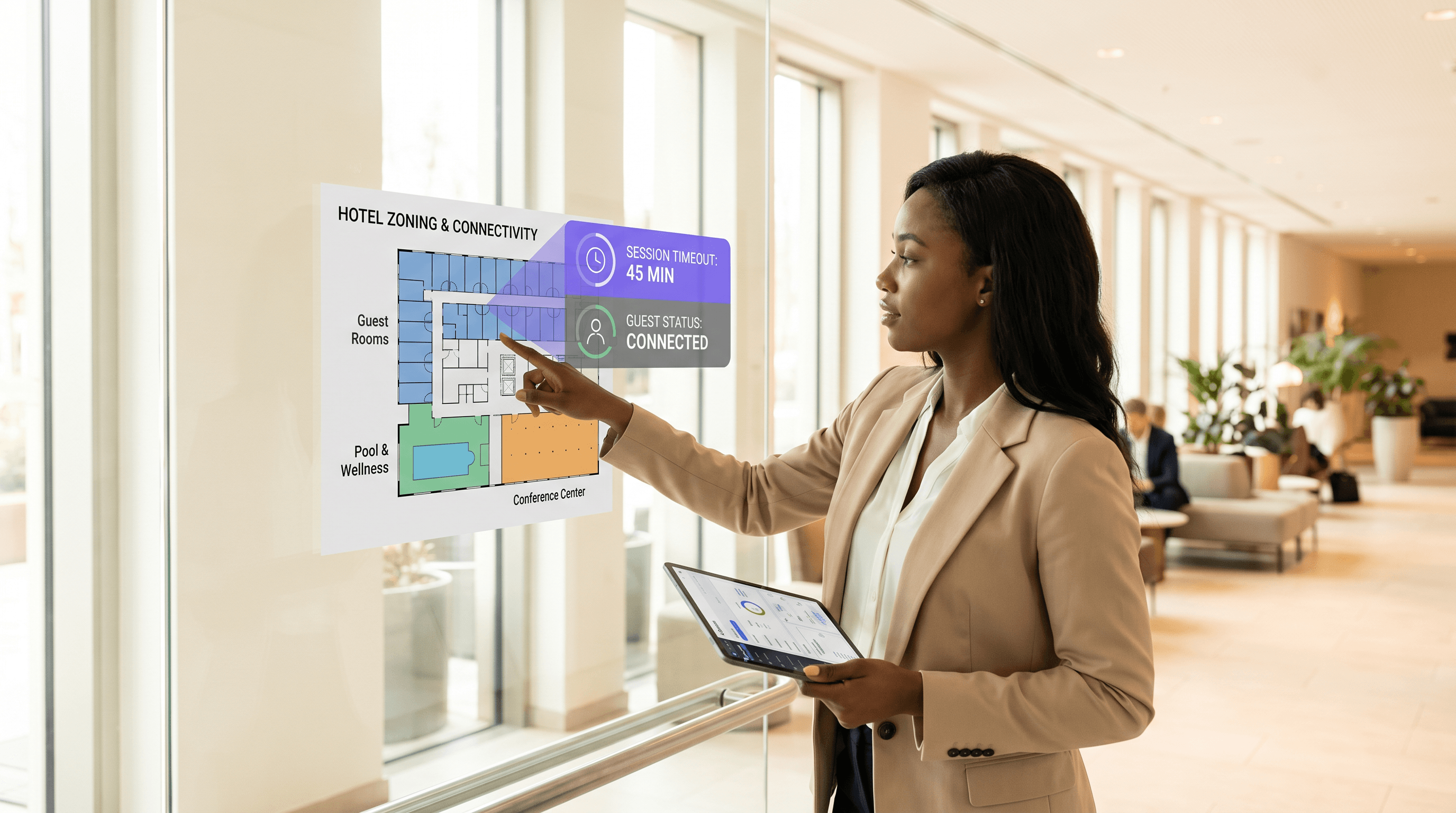
Guest WiFi Session Timeouts: Balancing UX and Security
This guide provides a practical framework for configuring guest WiFi session timeouts, balancing seamless user experience with robust security. It covers idle timeouts, absolute timeouts, re-authentication strategies, and industry-specific deployment scenarios for IT and venue operations leaders.
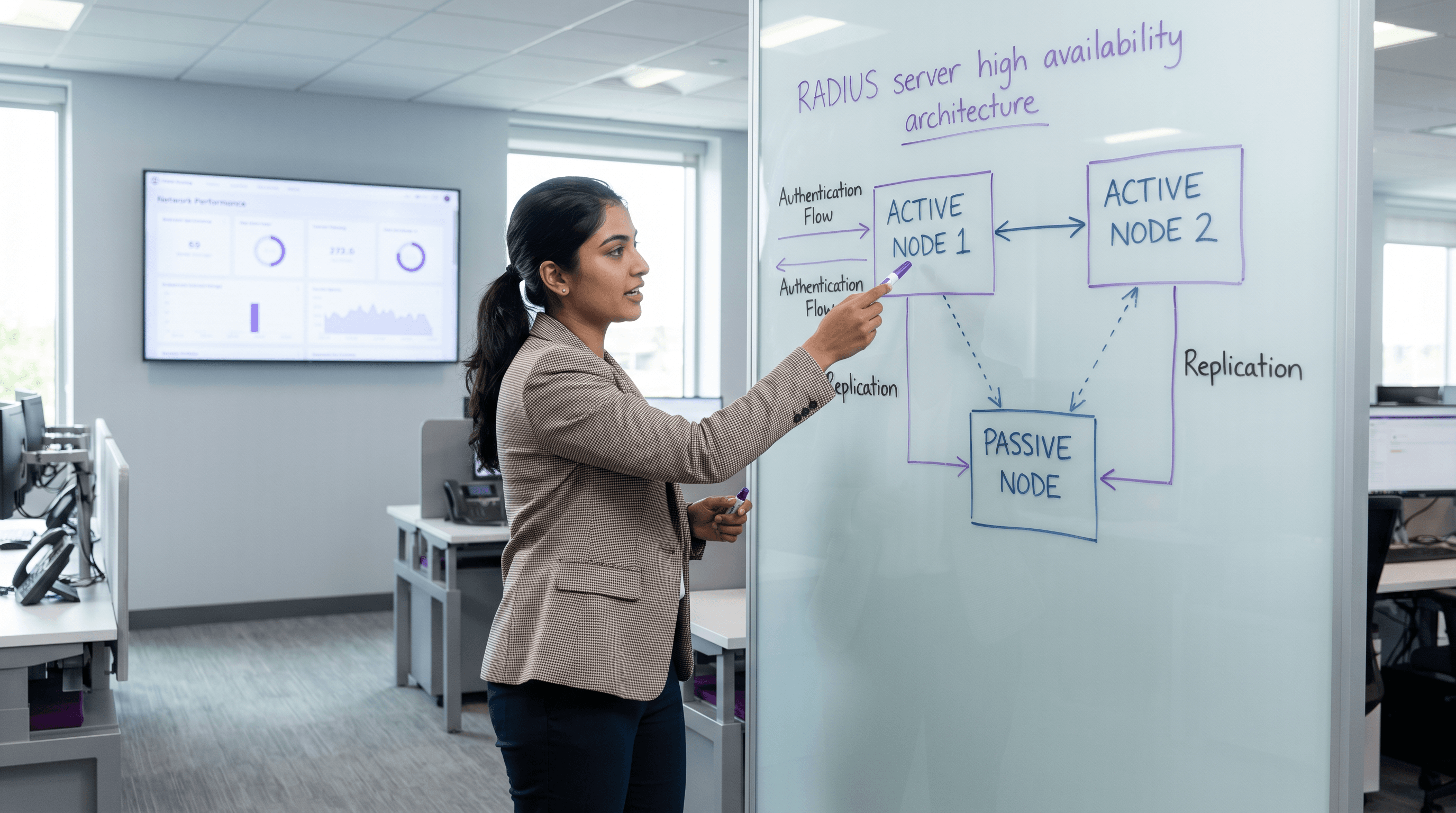
RADIUS Server High Availability: Active-Active vs Active-Passive
A definitive technical reference guide for IT managers and network architects evaluating RADIUS high availability architectures. It contrasts Active-Active and Active-Passive deployments, details database replication requirements, and explains how Cloud RADIUS mitigates failover latency for enterprise venues.
OFDMA Explained: How WiFi 6 Handles Dense Environments
This guide provides an advanced technical deep-dive into OFDMA (Orthogonal Frequency Division Multiple Access), the foundational multi-user technology of the IEEE 802.11ax (WiFi 6) standard. It explains how OFDMA differs from legacy OFDM, why it is critical for high-density venue deployments, and delivers actionable implementation guidance for network architects and IT directors. Venue operators in hospitality, retail, healthcare, and events will find concrete deployment strategies, client-side requirements, and ROI frameworks to justify and execute a WiFi 6 infrastructure refresh.
Network Onboarding UX: Designing a Frictionless WiFi Setup Experience
This guide provides a comprehensive technical framework for designing a frictionless WiFi network onboarding UX, covering captive portal detection mechanics across iOS, Android, Windows, and macOS, and detailing self-service certificate enrolment for 802.1X staff networks. It equips IT managers, network architects, and venue operations directors with actionable strategies to reduce helpdesk overhead, improve first-connection success rates, and maintain GDPR and PCI DSS compliance across hospitality, retail, and campus environments.
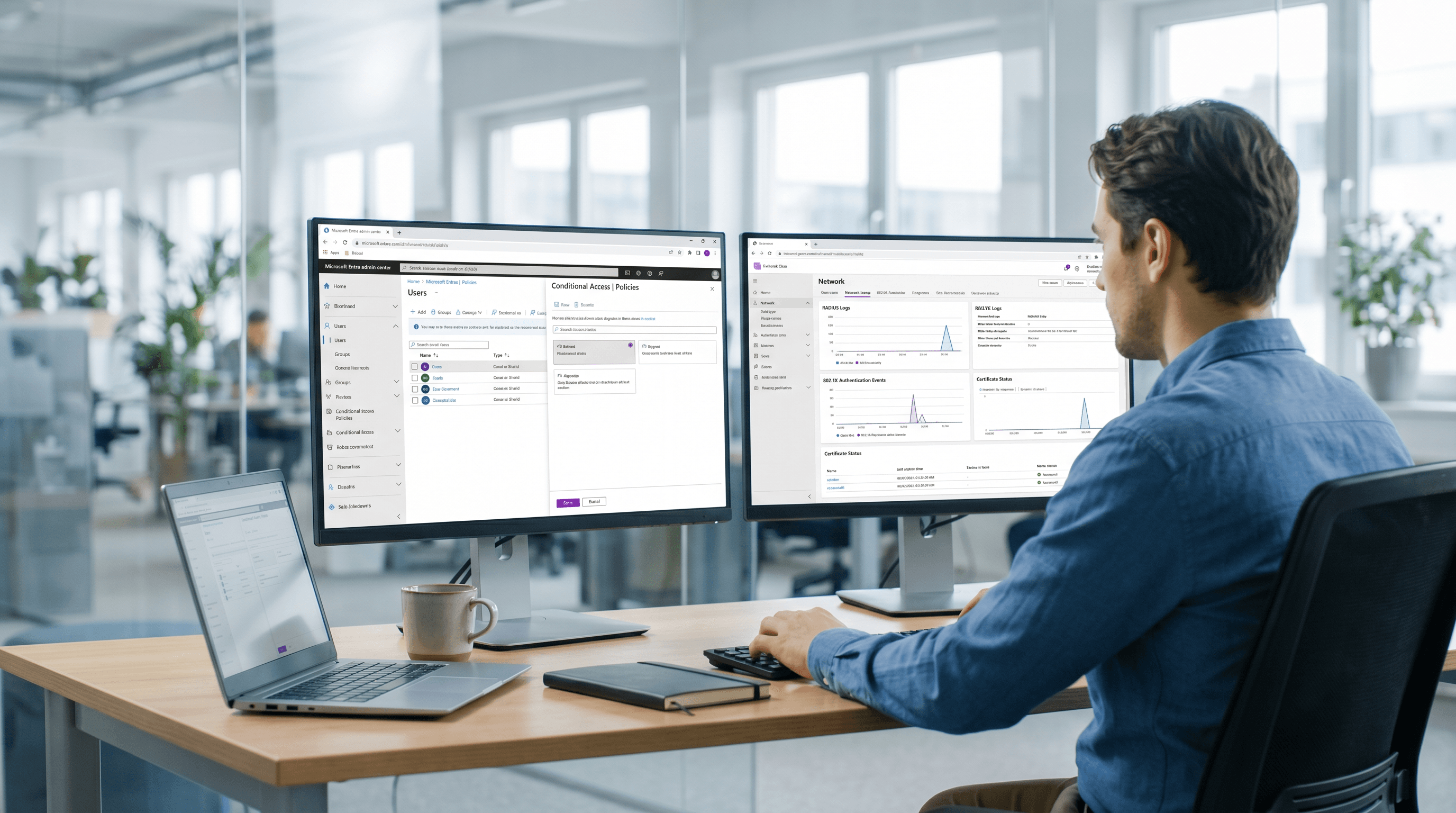
Azure AD and Entra ID WiFi Authentication: Integration and Configuration Guide
This technical reference guide provides IT managers, network architects, and venue operations directors with a practical roadmap for integrating Microsoft Entra ID (Azure AD) with enterprise WiFi networks using RADIUS and 802.1X. It covers the architectural decision between on-premise Windows NPS and cloud-native RADIUS, the deployment of certificate-based EAP-TLS authentication via Microsoft Intune, and the operational best practices for securing wireless access across hospitality, retail, and public-sector environments. For organisations already invested in the Microsoft 365 and Entra ID ecosystem, this guide bridges the gap between cloud identity management and physical network security.
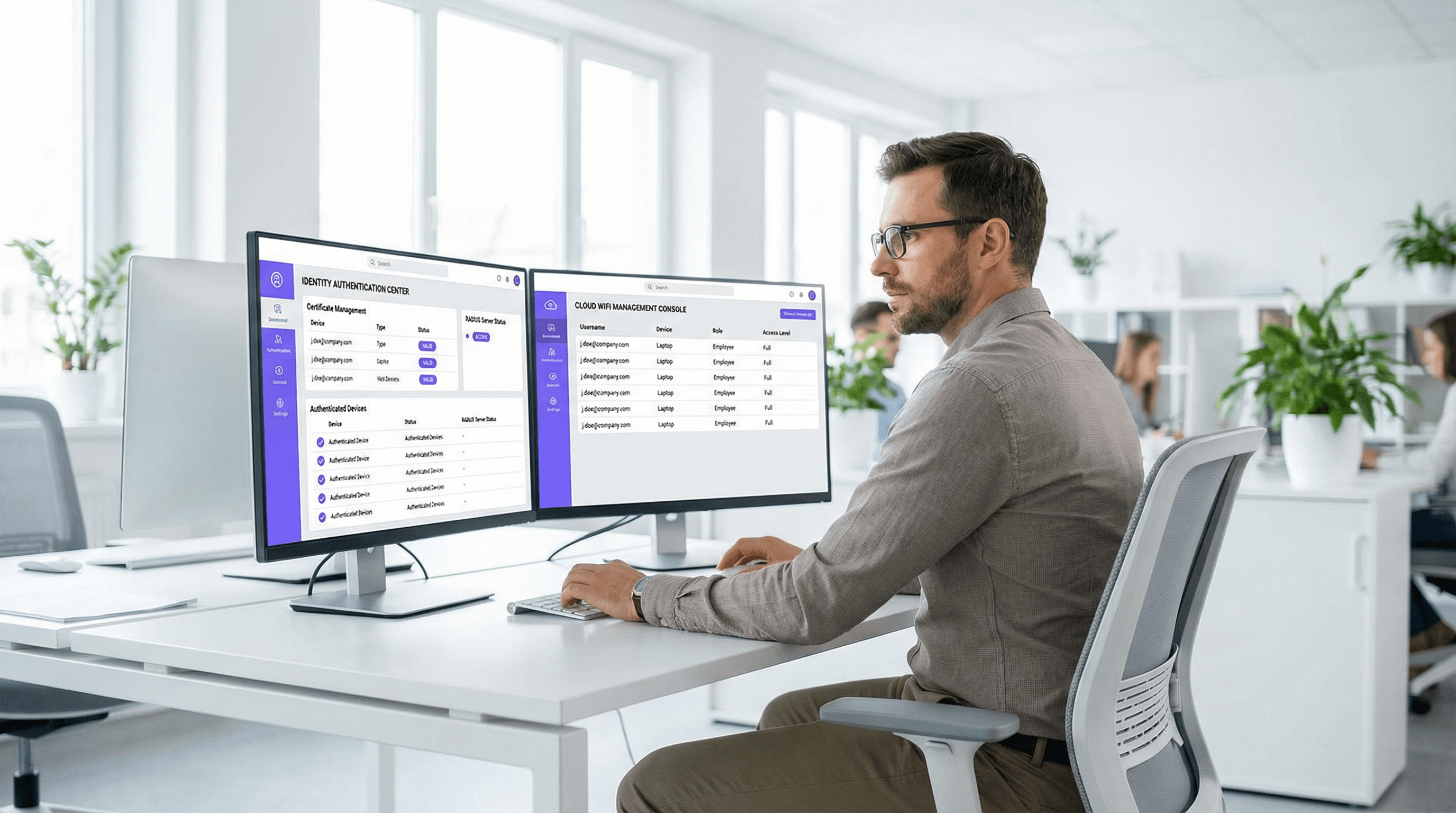
Passwordless WiFi Authentication: Moving Beyond Pre-Shared Keys
This guide provides IT managers, network architects, and venue operations directors with a practical roadmap for eliminating shared WiFi passwords and migrating to identity-based, certificate-driven authentication. It covers the security and compliance failures of PSK-based networks, the technical architecture of 802.1X and EAP-TLS, and the role of Identity PSK (iPSK) as a critical transition technology for IoT and legacy devices. Venue operators in hospitality, retail, and the public sector will find actionable migration strategies, real-world implementation scenarios, and measurable business outcomes to justify the investment.
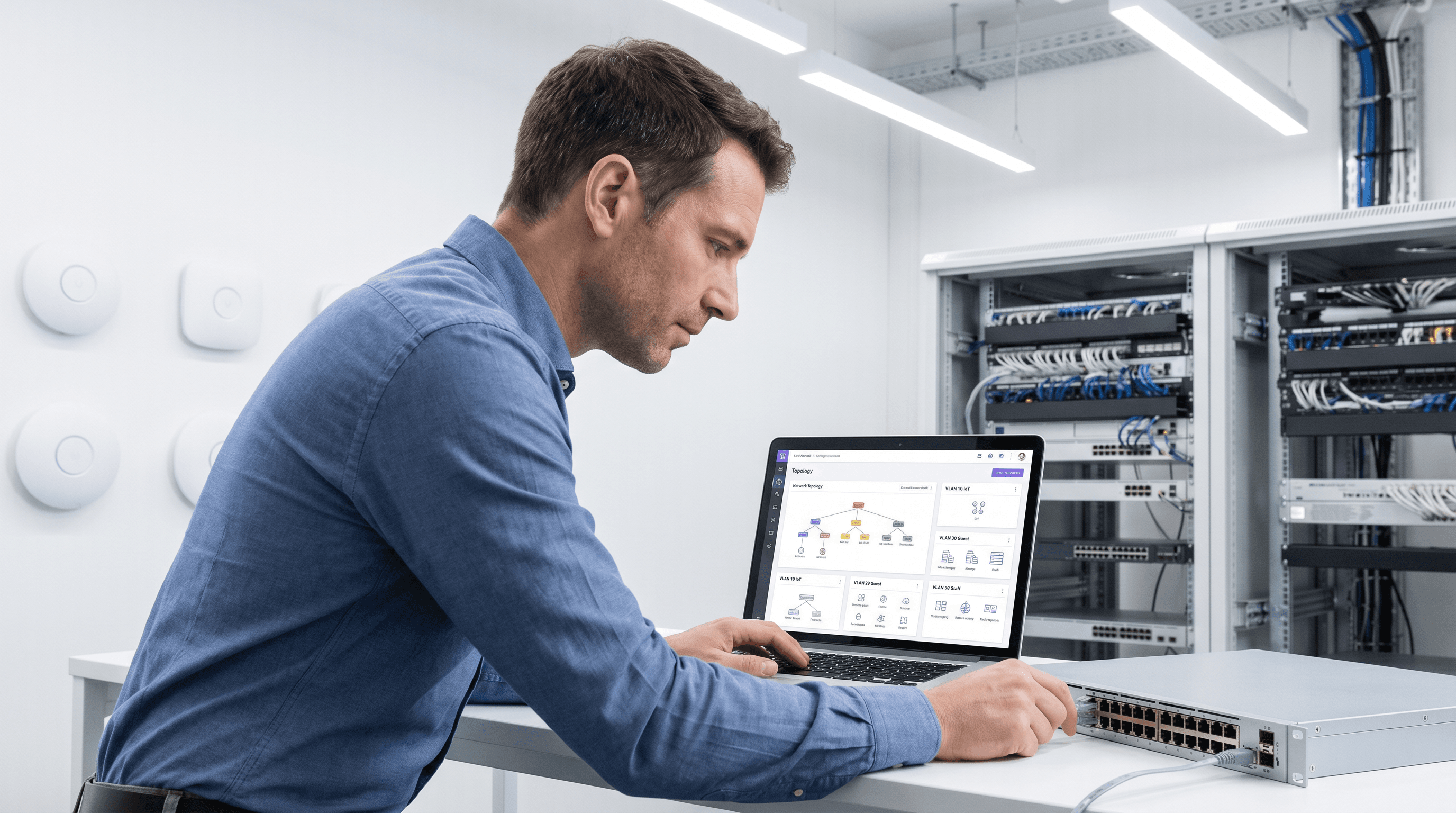
IoT Device Segmentation on WiFi: Isolating Non-Standard Devices
This guide provides practical, enterprise-grade strategies for securely segmenting non-standard IoT devices on venue WiFi networks. Learn how to implement VLAN isolation, MAC-based authentication, and strict firewall policies to protect your core infrastructure from vulnerable smart devices.
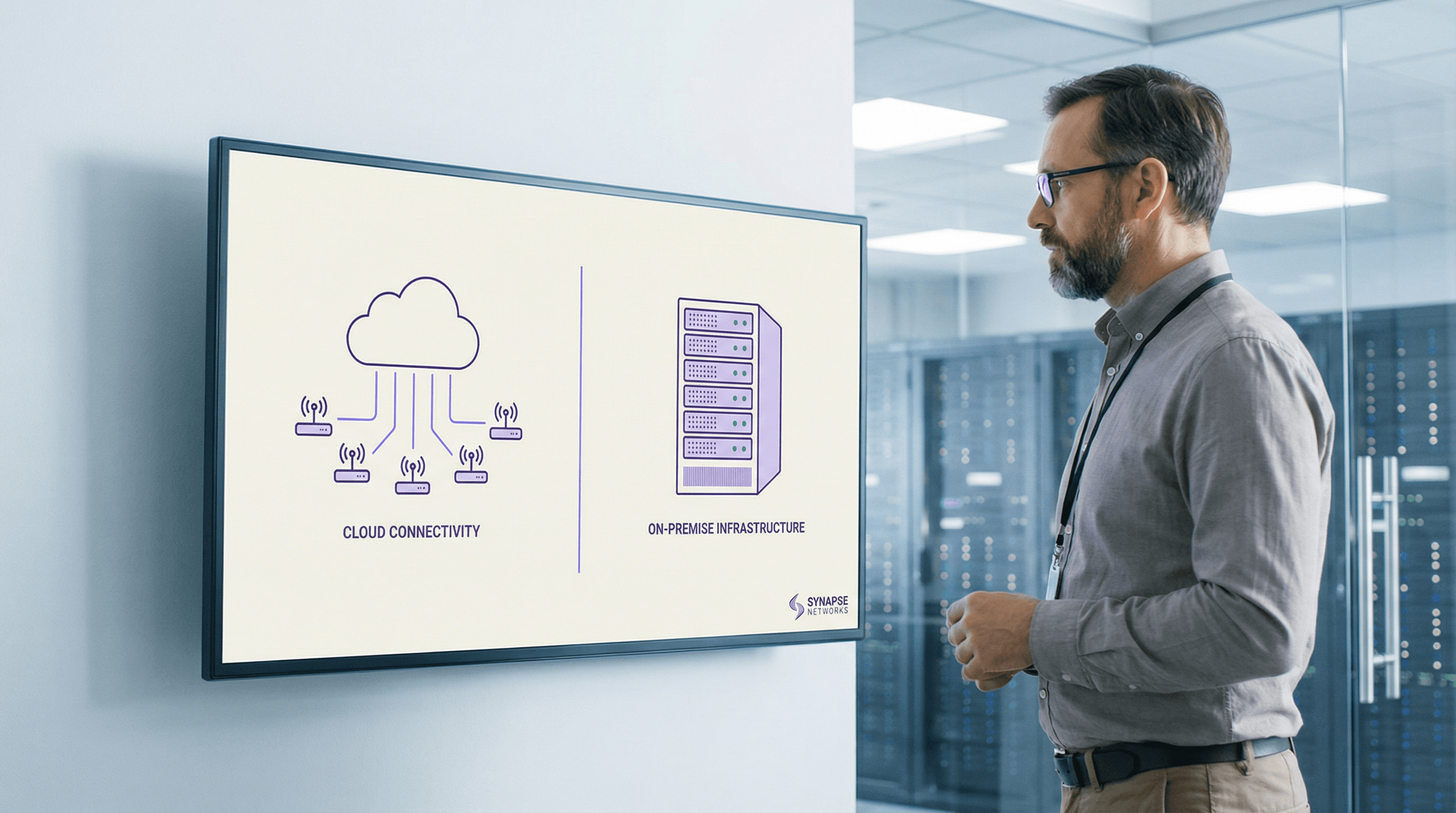
Cloud RADIUS vs On-Premise RADIUS: Decision Guide for IT Teams
This guide provides IT directors, network architects, and venue operations teams with a definitive framework for choosing between cloud-hosted RADIUS services and traditional on-premise RADIUS servers. It covers the technical architecture, latency and reliability trade-offs, total cost of ownership, and compliance considerations for multi-site hospitality, retail, and public-sector deployments. By the end, readers will have a clear decision model aligned to their specific infrastructure constraints and organisational risk appetite.
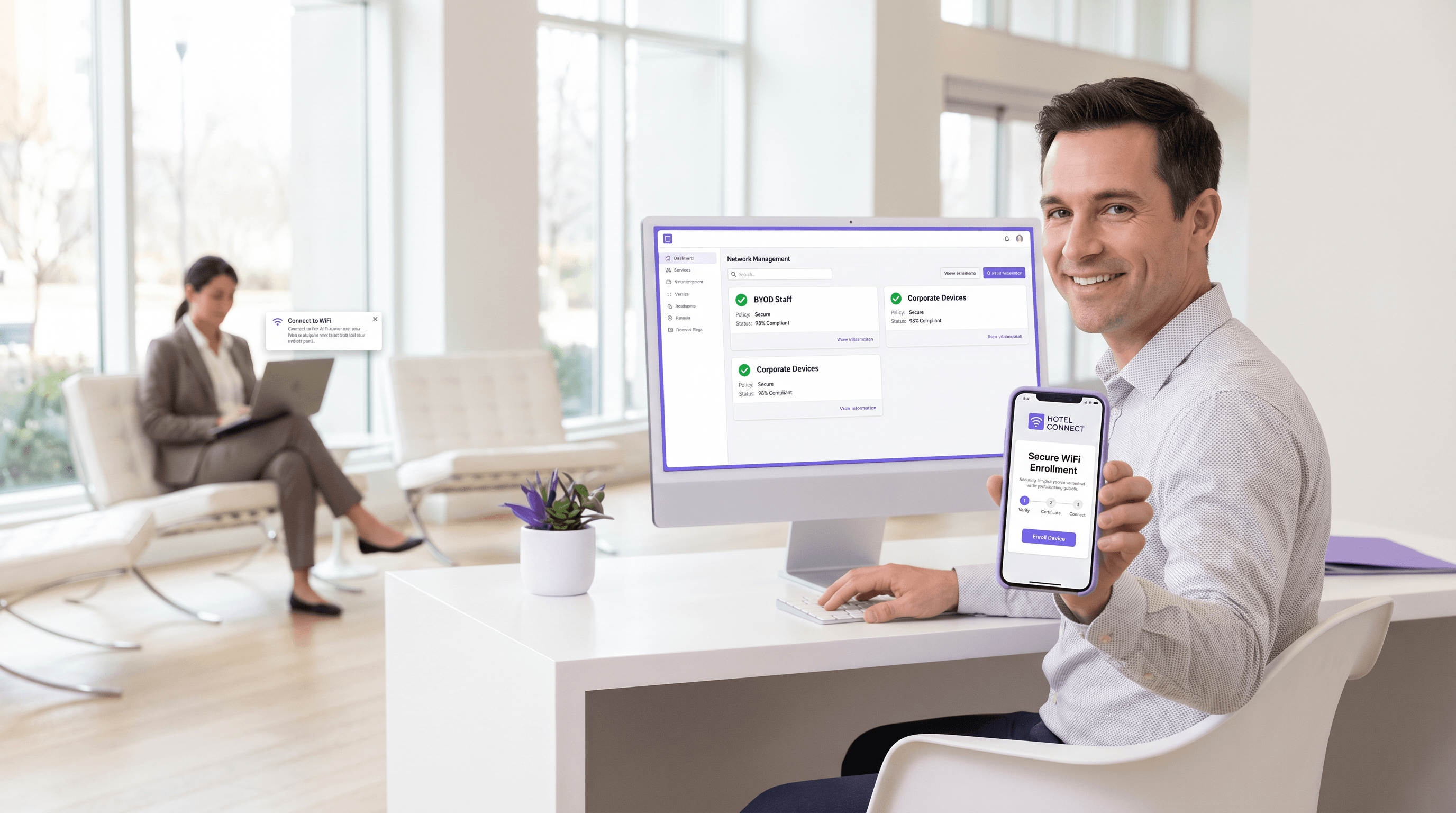
BYOD WiFi Onboarding: Managing Unmanaged Devices in Hotels and Retail
This technical reference guide provides actionable strategies for onboarding employee-owned (BYOD) devices onto enterprise WiFi networks in hospitality and retail environments without requiring full MDM enrolment. It covers self-service certificate enrolment flows, 802.1X authentication, and policy enforcement to ensure secure access for unmanaged devices.
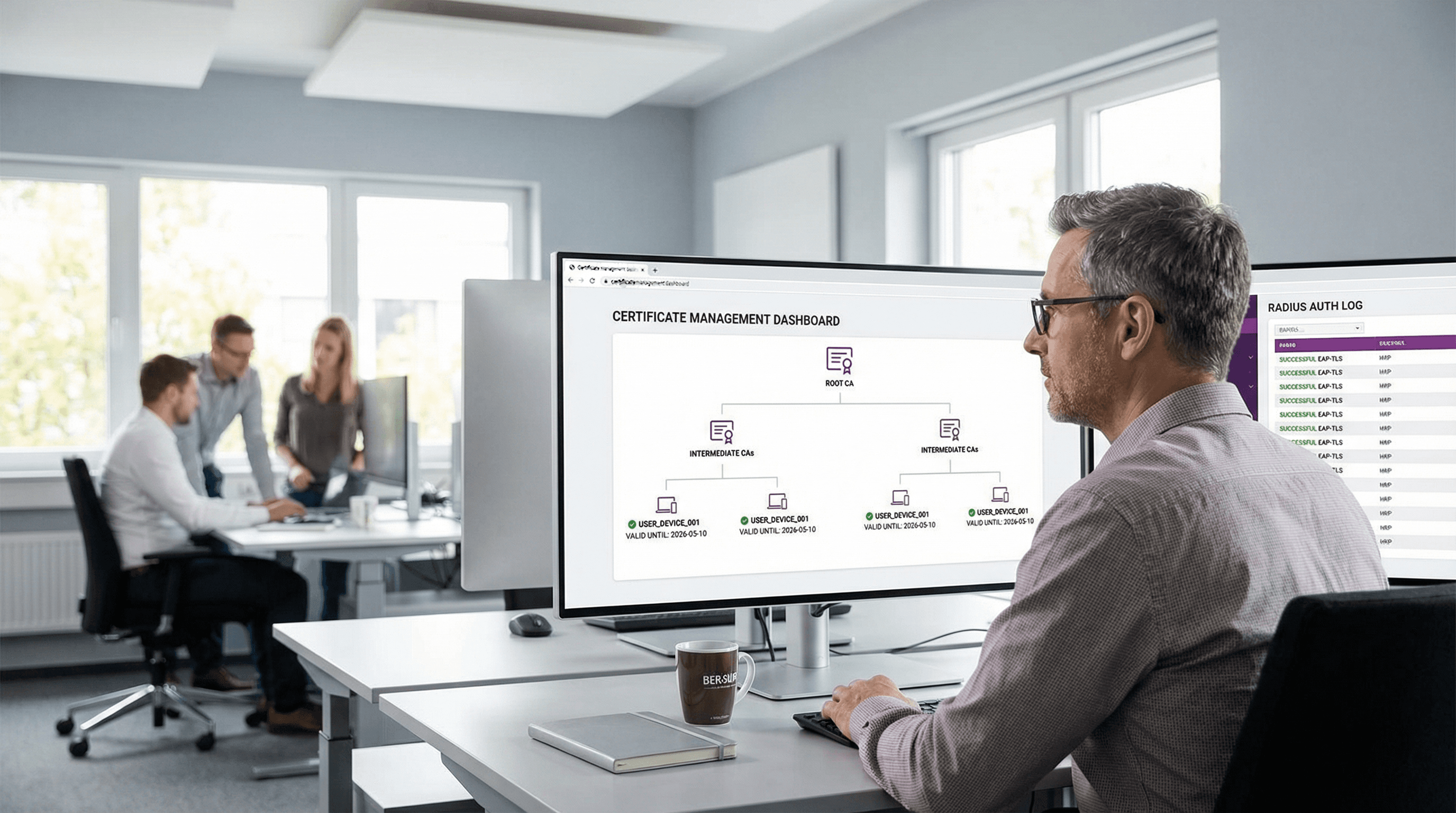
EAP-TLS Authentication Explained: Certificate-Based WiFi Security
EAP-TLS is the gold standard for enterprise WiFi security, replacing vulnerable password-based authentication with robust, mutually authenticated digital certificates. This guide provides IT managers and network architects with a comprehensive technical deep-dive into the EAP-TLS handshake, architectural requirements, and practical deployment strategies for mixed-device environments.
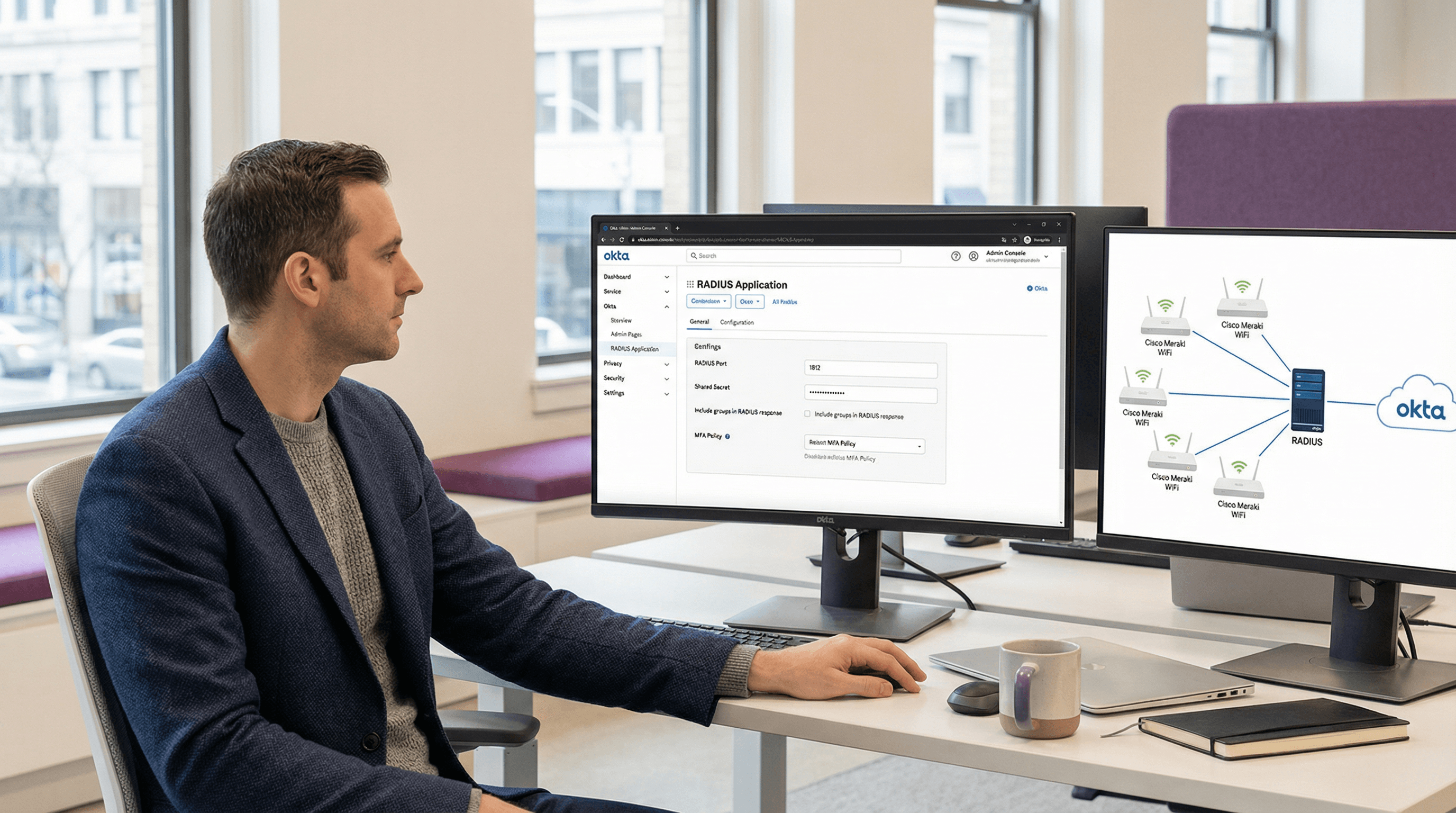
Okta and RADIUS: Extending Your Identity Provider to WiFi Authentication
This guide provides a comprehensive technical reference for IT administrators at Okta-centric organisations who want to extend their cloud identity provider to WiFi authentication using the Okta RADIUS agent. It covers the full authentication architecture, MFA enforcement trade-offs, dynamic VLAN assignment via RADIUS attribute mapping, and the critical decision between password-based EAP-TTLS and certificate-based EAP-TLS. Venue operators and enterprise IT teams will find actionable deployment guidance, real-world case studies from hospitality and retail, and a clear framework for integrating Okta RADIUS alongside dedicated guest WiFi solutions.



