Technical Guides
Deep, expert-led guides covering guest WiFi, analytics, captive portals, and modern venue technology. Each guide includes diagrams, worked examples, and audio podcasts.
249 guides
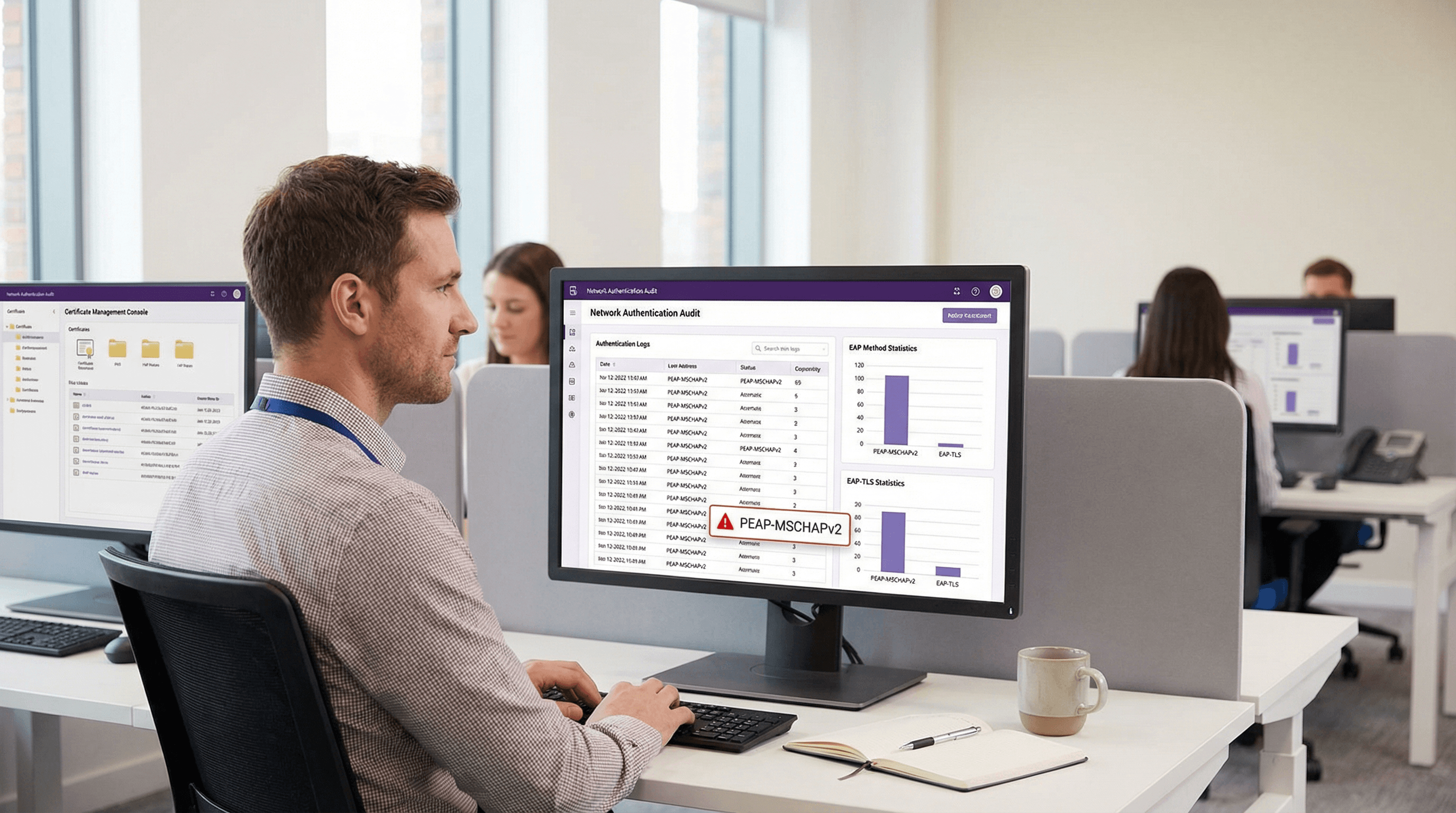
PEAP-MSCHAPv2: Why It Is Still Common, Why It Is Risky, and How to Move On
A comprehensive technical reference guide detailing the critical security vulnerabilities of PEAP-MSCHAPv2, including evil twin attacks and credential capture. It provides a practical, vendor-neutral roadmap for IT teams to migrate enterprise WiFi networks to secure, certificate-based EAP-TLS authentication.
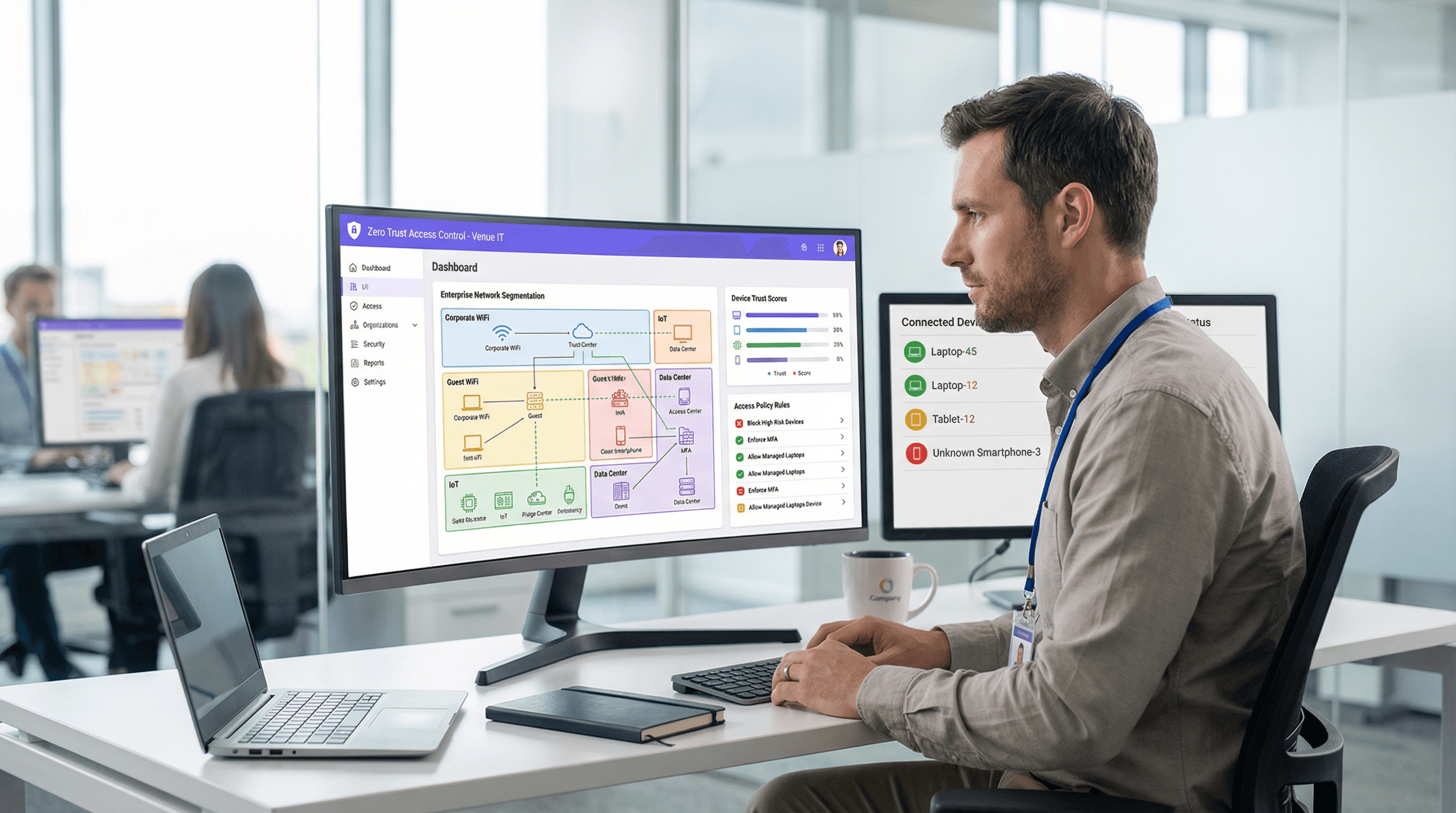
Zero Trust WiFi Architecture: Applying Zero Trust to Venue Networks
A comprehensive technical reference guide detailing how venue operators can apply Zero Trust principles to enterprise WiFi networks. It covers continuous verification, micro-segmentation, and device posture enforcement to secure hospitality, retail, and public-sector environments against lateral movement and compliance risks.
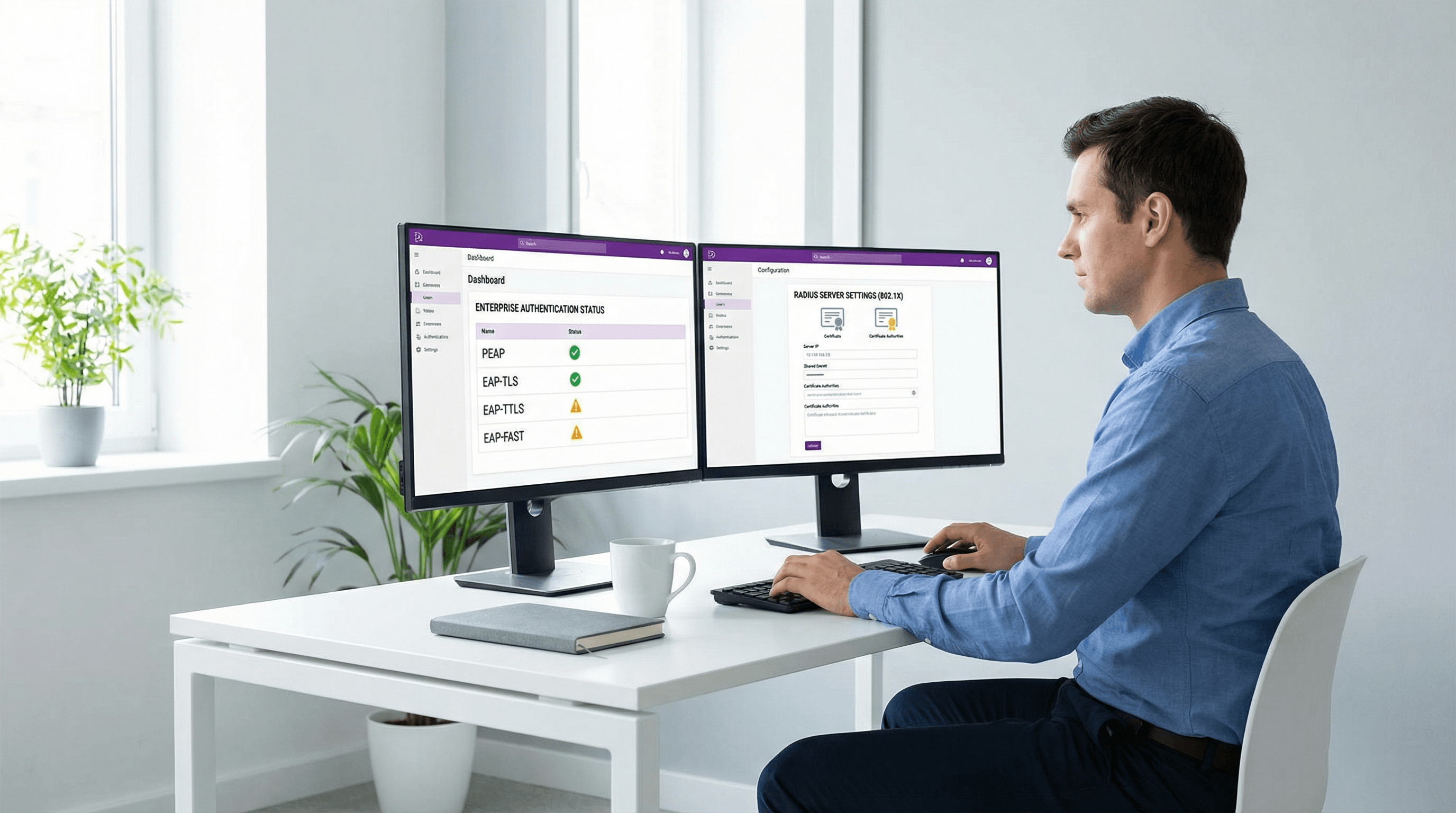
EAP Methods Compared: PEAP, EAP-TLS, EAP-TTLS, and EAP-FAST
This authoritative technical reference guide provides a side-by-side comparison of PEAP, EAP-TLS, EAP-TTLS, and EAP-FAST for enterprise WiFi authentication. It delivers actionable guidance on security posture, deployment complexity, and device compatibility to help IT managers and network architects choose the optimal 802.1X deployment strategy.
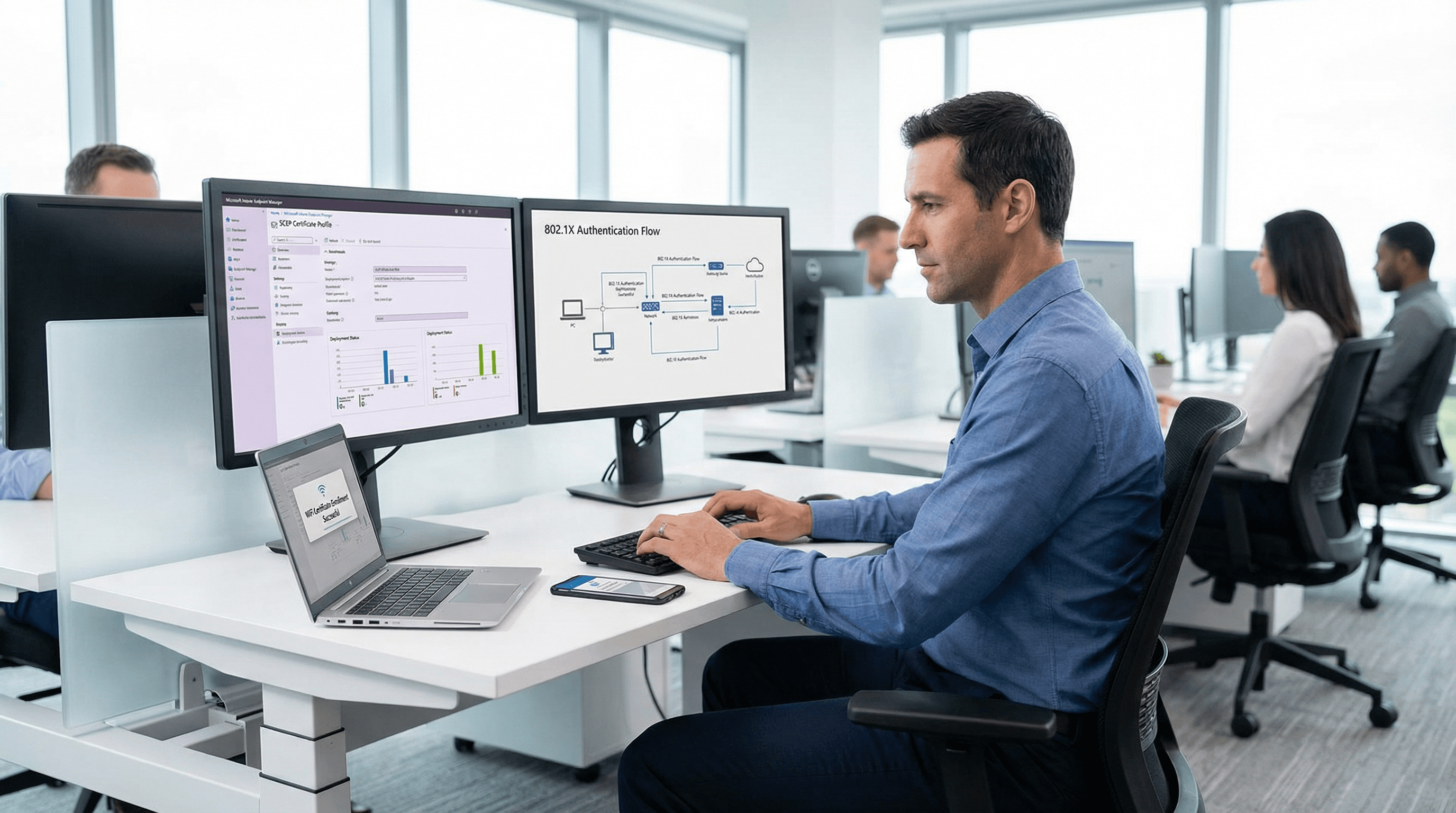
Microsoft Intune WiFi Certificate Deployment via SCEP and PKCS
This guide provides a step-by-step technical reference for deploying WiFi authentication certificates via Microsoft Intune using SCEP and PKCS. It is designed for IT managers and network architects implementing passwordless 802.1X WiFi to ensure seamless, secure connectivity across enterprise environments.
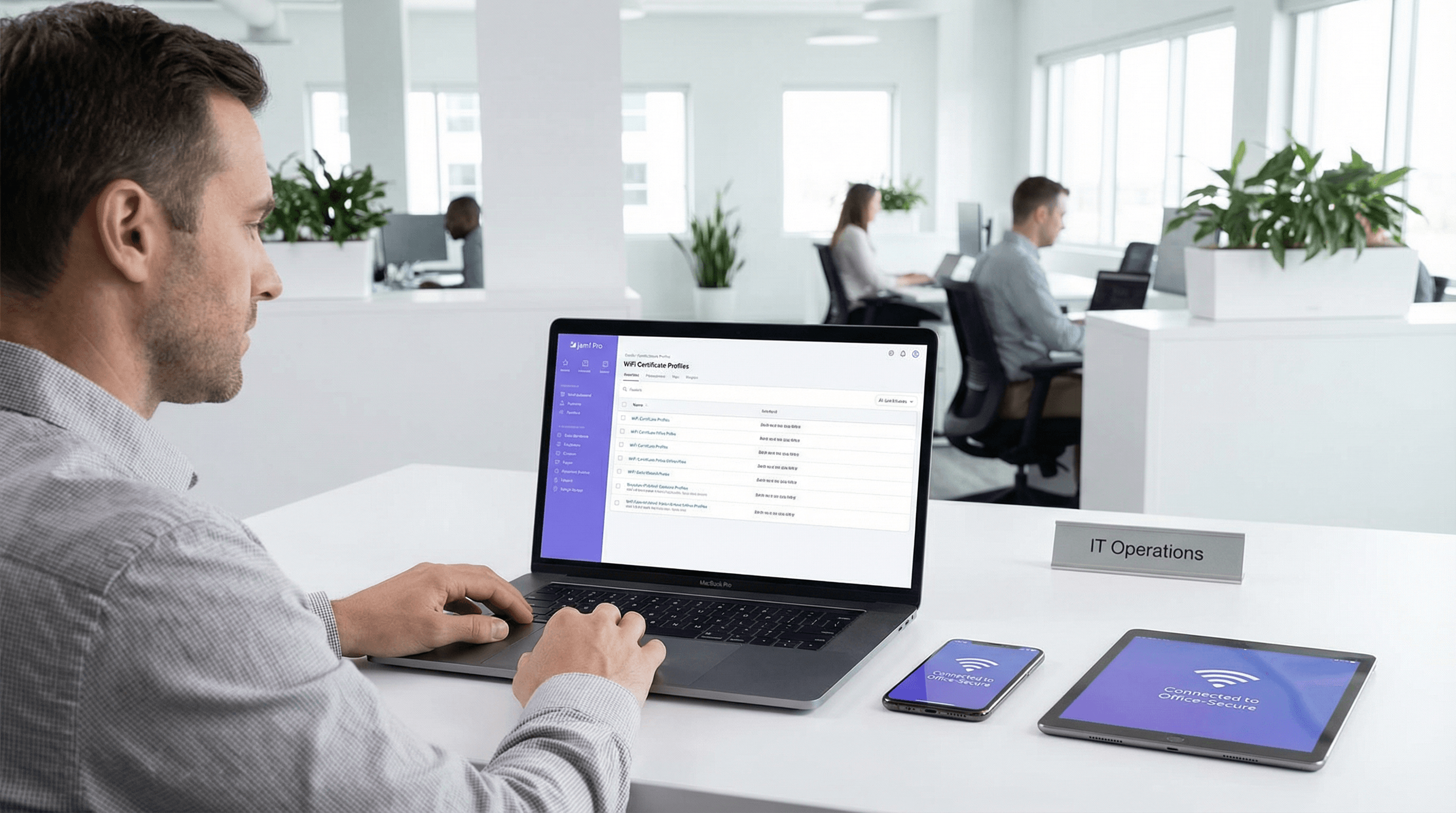
Jamf and RADIUS: Certificate-Based WiFi Authentication for Apple Device Fleets
This technical reference guide provides IT managers, network architects, and CTOs with actionable steps to deploy certificate-based 802.1X WiFi authentication for Apple device fleets using Jamf Pro and RADIUS. It covers the full SCEP certificate provisioning workflow, WiFi configuration profile structure, RADIUS integration requirements, and real-world implementation scenarios from healthcare and enterprise environments. The guide is essential for any organisation seeking to eliminate password-based WiFi vulnerabilities, reduce helpdesk overhead, and achieve compliance with PCI DSS and GDPR network access standards.
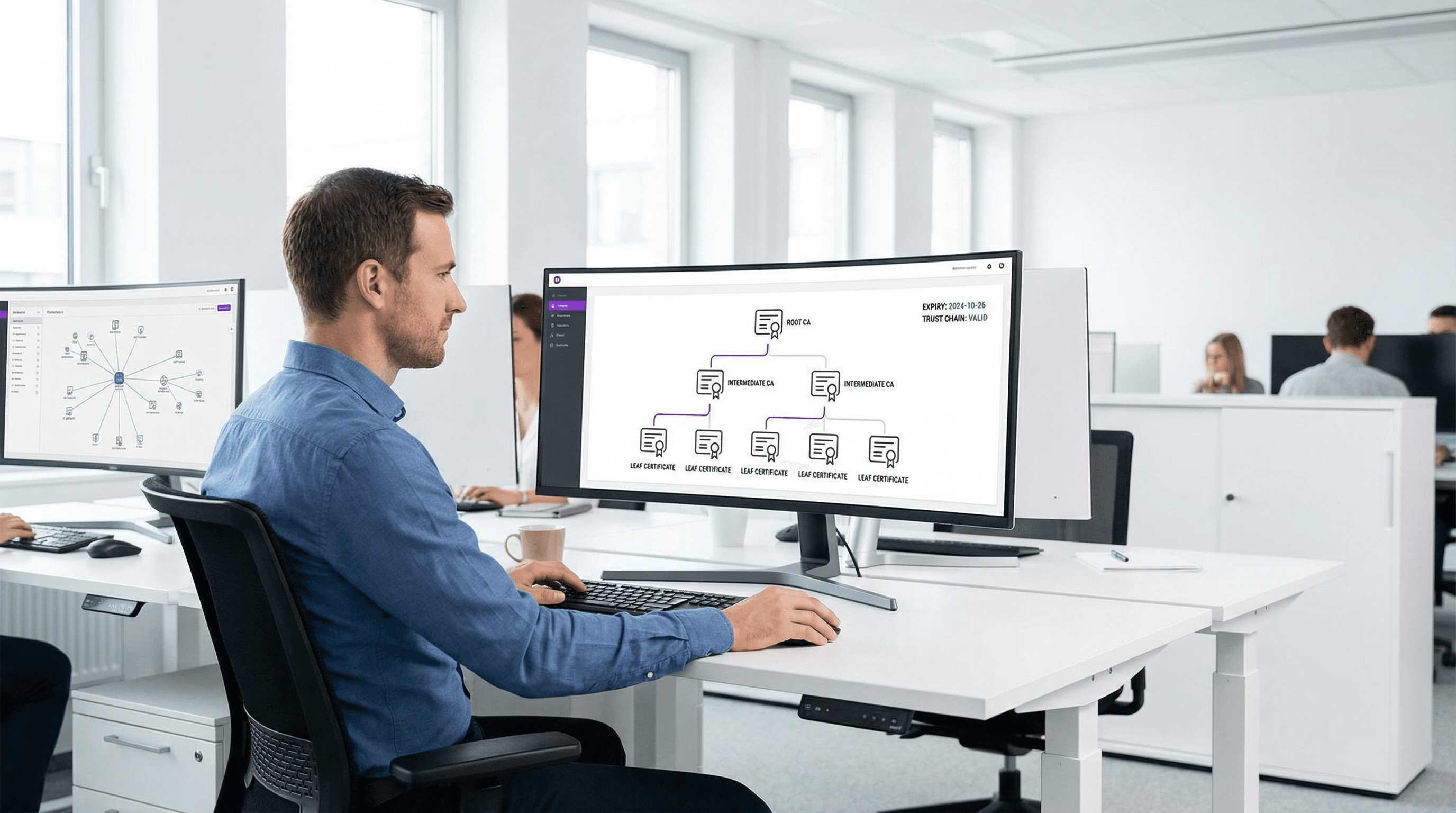
PKI Fundamentals for WiFi Administrators: Certificates, CAs, and Trust Chains
This technical reference guide explains the foundational concepts of Public Key Infrastructure (PKI) for enterprise WiFi administrators, covering certificate authorities, trust chains, and X.509 certificates. It details how PKI underpins EAP-TLS mutual authentication and provides actionable deployment guidance for IT teams in hospitality, retail, and public-sector environments. Understanding PKI is a mandatory prerequisite for deploying certificate-based staff WiFi authentication with Purple.
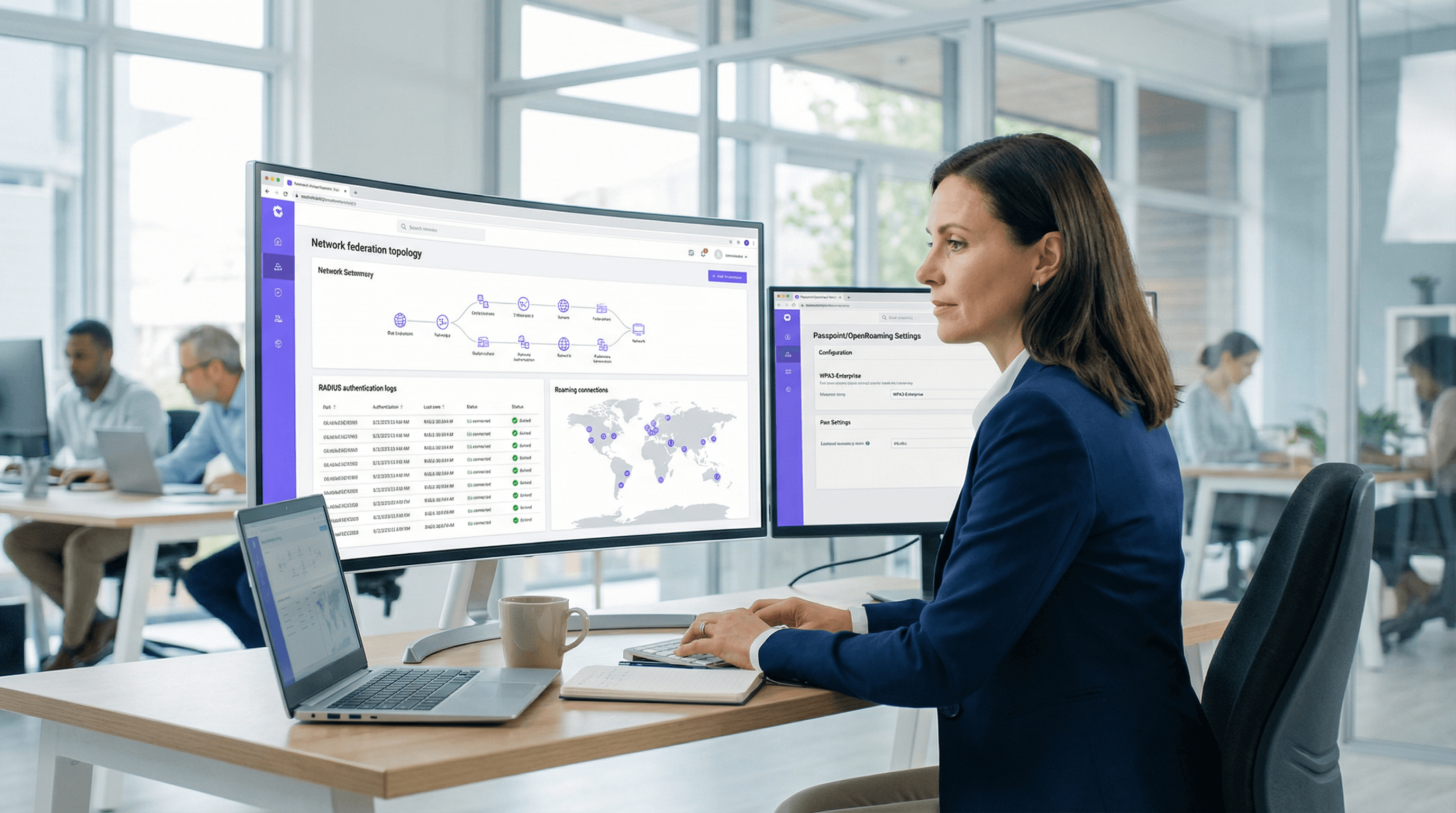
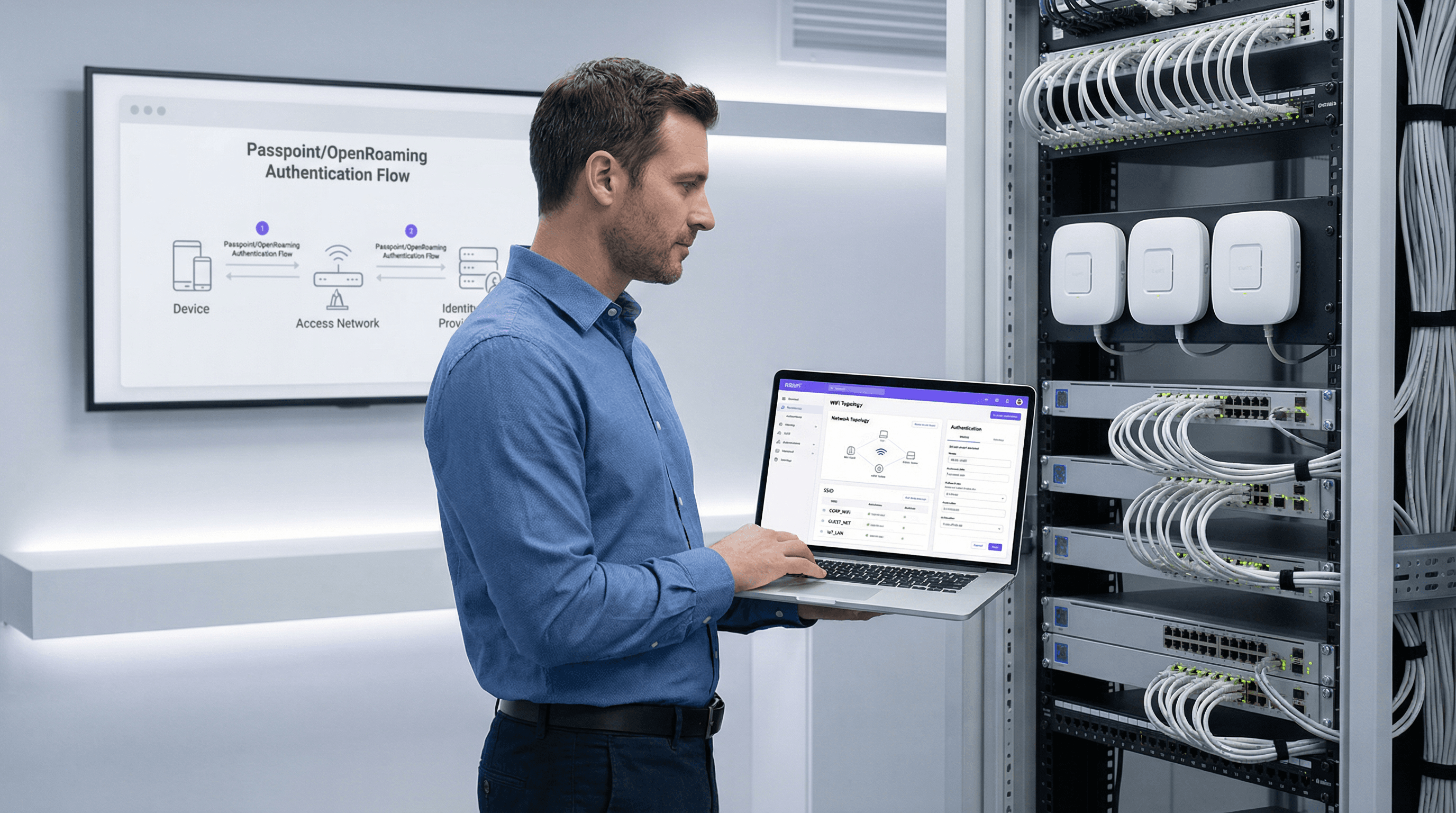
The Ultimate Guide to OpenRoaming Architecture and Authentication
This guide provides an authoritative technical reference on WBA OpenRoaming architecture, covering the Passpoint foundation, RADIUS federation, RadSec mTLS security, and step-by-step deployment guidance for enterprise venues. It equips IT managers, network architects, and venue operators with the knowledge to replace captive portals with seamless, secure, and compliant Wi-Fi connectivity that delivers measurable ROI.
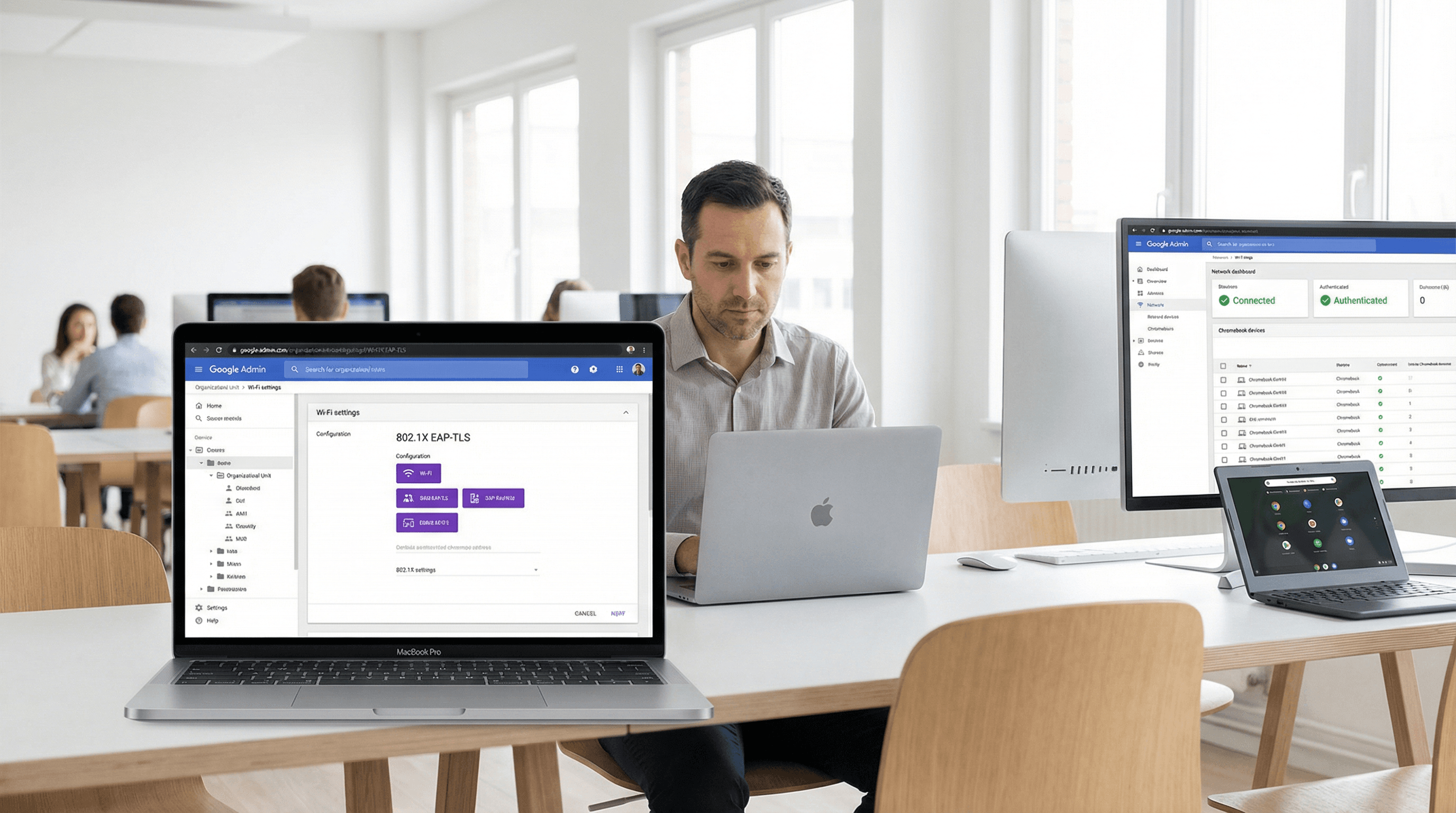
Google Workspace WiFi Authentication: Chromebook and LDAP Integration
A definitive technical reference for IT administrators deploying secure WiFi in Google Workspace environments. This guide covers 802.1X certificate deployment to managed Chromebooks via Google Admin Console, Google Secure LDAP integration as a RADIUS backend, and architecture decisions for education, media, and enterprise venues. It provides actionable implementation steps, real-world case studies, and a direct comparison of EAP methods to help teams move from vulnerable shared PSKs to robust, identity-based network access control.
RADIUS Accounting: Tracking Sessions, Usage, and Audit Logs
This guide provides a comprehensive technical reference on RADIUS accounting — how it records WiFi session start, stop, and interim-update data, what attributes are captured, and how to leverage that data for security auditing, GDPR compliance, and capacity planning. It is essential reading for network operations and security teams who need defensible audit trails from WiFi authentication events, and for venue operators seeking to integrate session data into SIEM platforms and analytics dashboards.
How Passpoint (Hotspot 2.0) Transforms the Guest Wi-Fi Experience
A comprehensive technical reference guide detailing how Passpoint (Hotspot 2.0) and 802.11u protocols replace traditional captive portals with seamless, secure, cellular-like Wi-Fi roaming. It provides IT leaders with architectural overviews, implementation frameworks, and the business case for adopting credential-based authentication to solve MAC randomisation challenges and improve guest experience.
The Future of Seamless Connectivity: Passpoint and OpenRoaming Explained
This technical reference guide provides actionable insights for IT leaders on transitioning from traditional captive portals to Passpoint and OpenRoaming. It details the underlying IEEE 802.11u and WPA3 standards, secure authentication flows, and real-world deployment strategies to improve seamless connectivity, enhance security, and drive measurable ROI in enterprise venues.
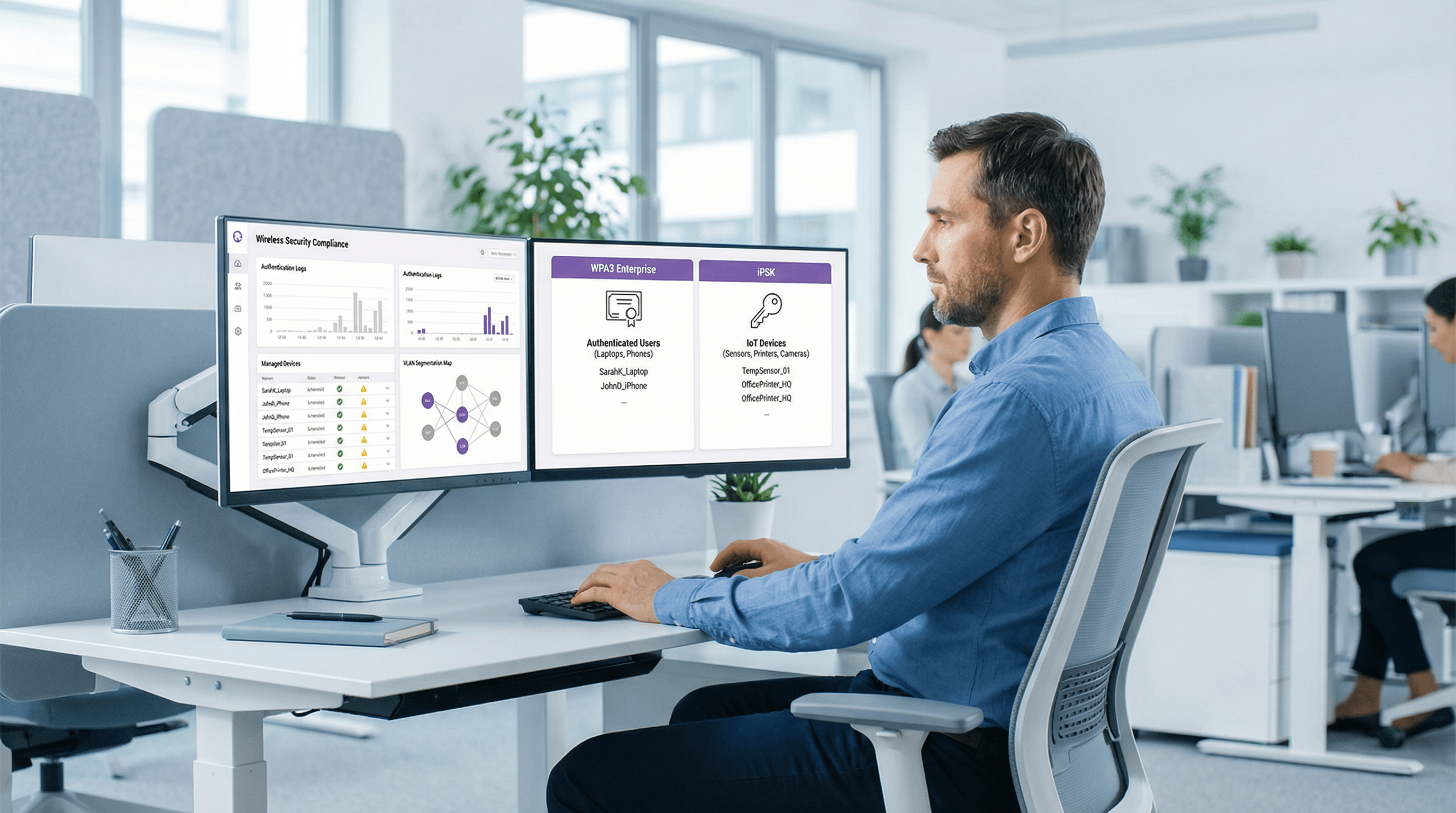
WPA3 Enterprise vs iPSK: Choosing the Right Security Model
This guide provides a definitive technical comparison between WPA3 Enterprise and Identity Pre-Shared Key (iPSK) for enterprise WiFi networks. It empowers IT leaders to choose the optimal security model for their venues, balancing robust 802.1X authentication with the flexibility required for IoT and legacy devices.
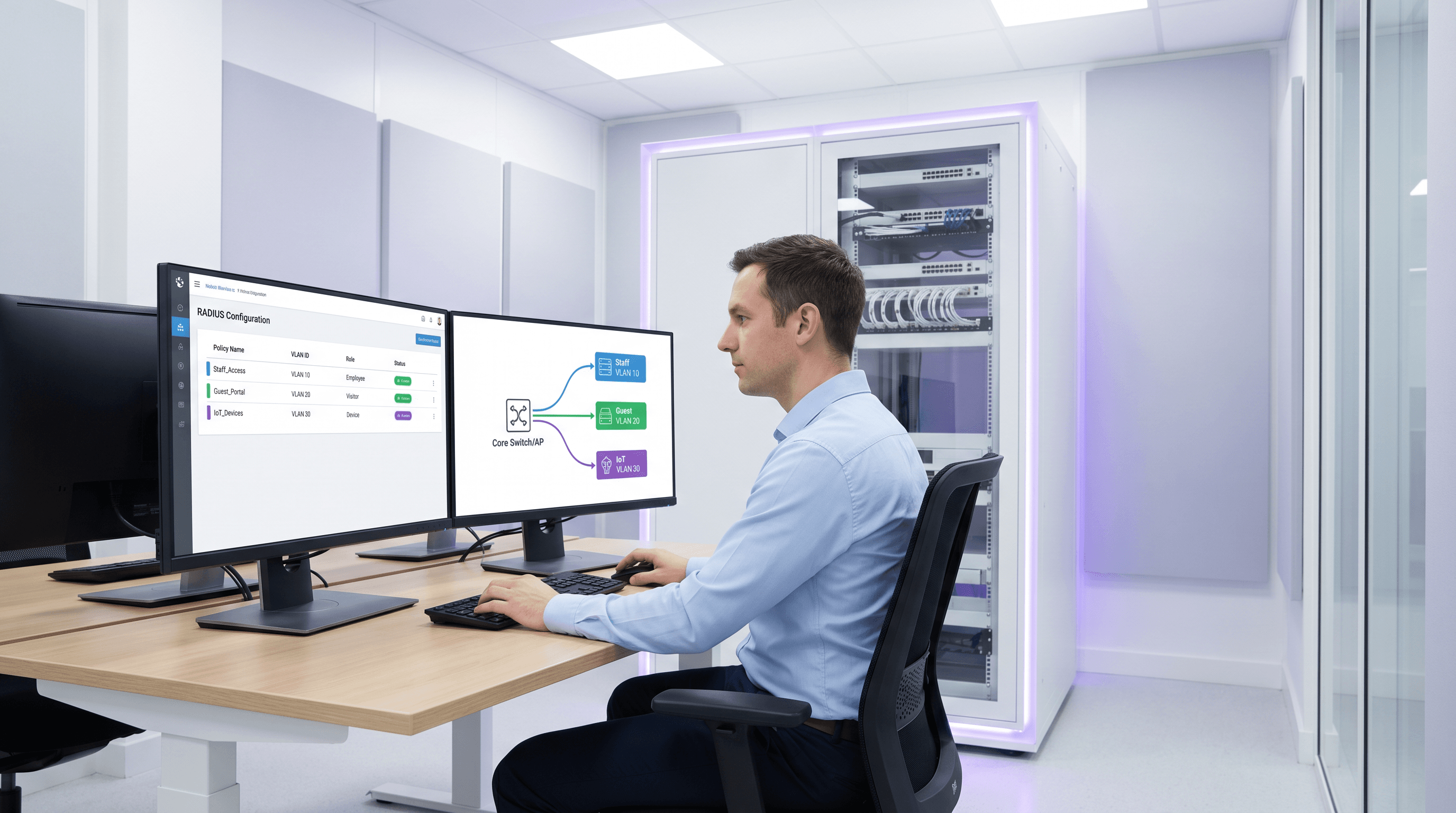
Dynamic VLAN Assignment with RADIUS: Segmenting Users by Role
This guide provides a comprehensive technical overview of implementing dynamic VLAN assignment using RADIUS attributes. It details how enterprise venues can automate network segmentation for staff, guests, and IoT devices to enhance security and reduce manual configuration overhead.
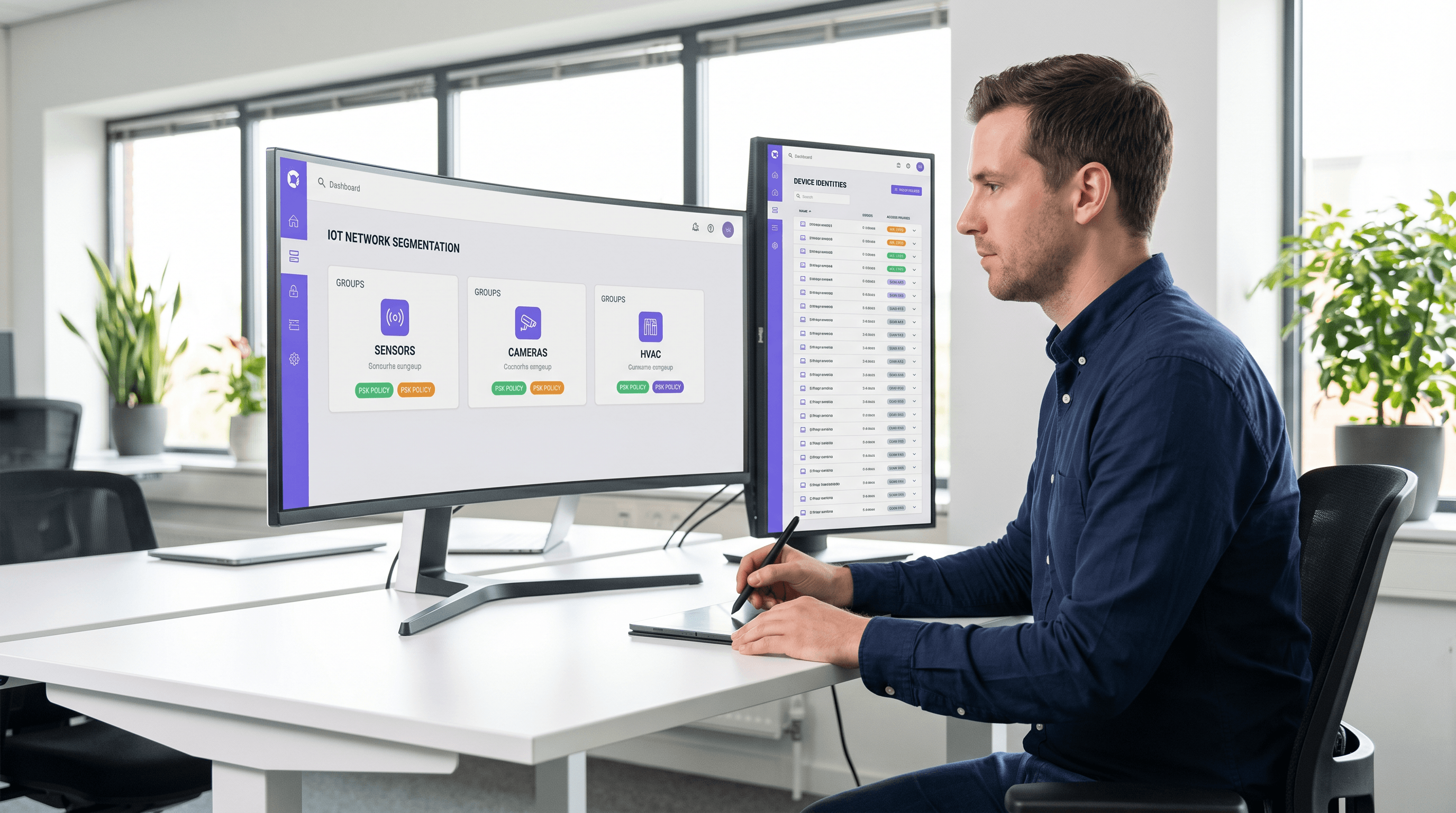
Implementing iPSK (Identity Pre-Shared Key) for Secure IoT Networks
This authoritative guide details how to implement Identity Pre-Shared Key (iPSK) architecture to secure enterprise IoT environments. It provides actionable deployment steps, VLAN segmentation strategies, and compliance frameworks for hospitality, retail, and public-sector network operators.
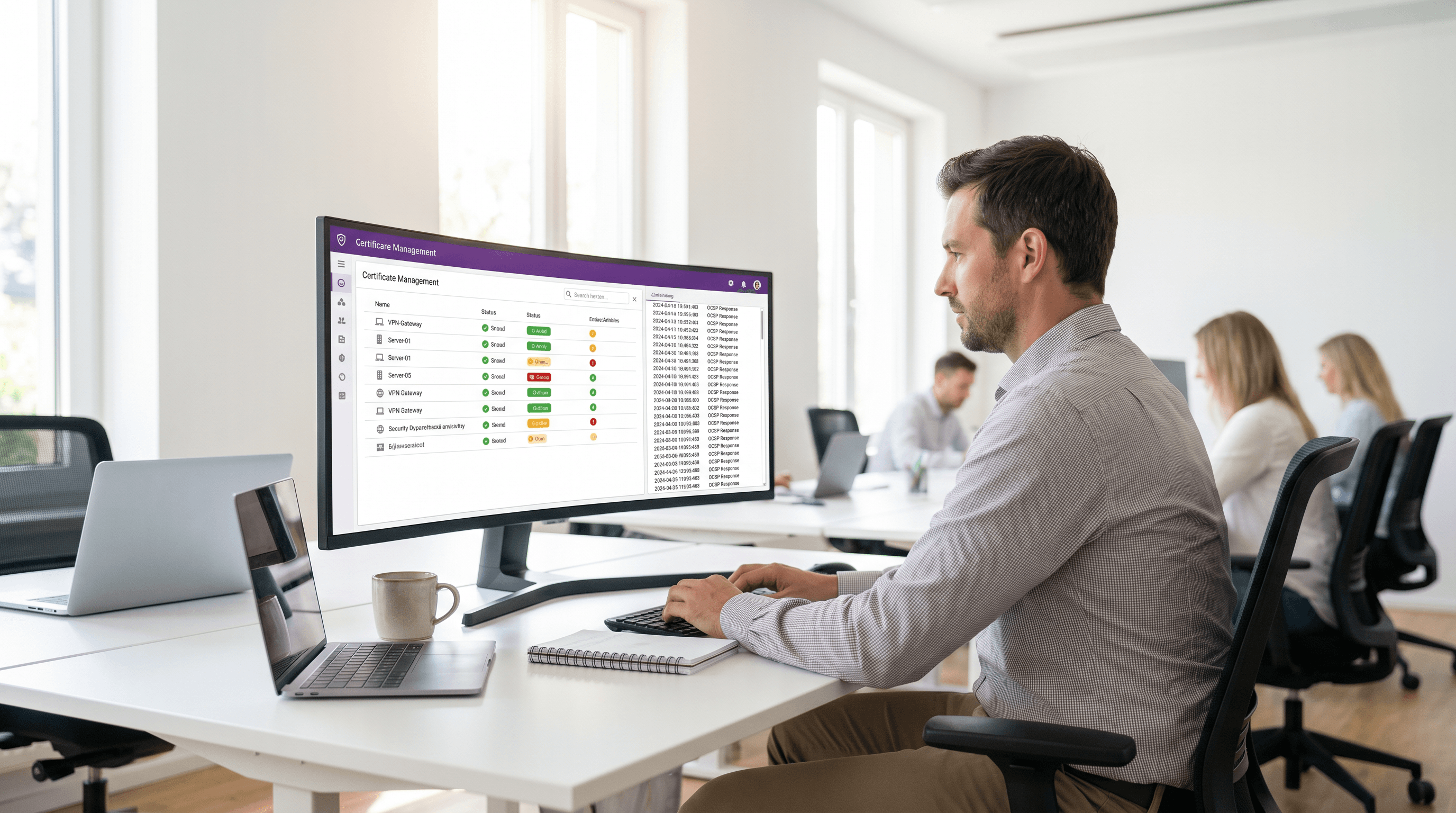
OCSP and Certificate Revocation for WiFi Authentication
This comprehensive guide explores the critical mechanisms of certificate revocation in enterprise WiFi environments, focusing on the transition from CRLs to OCSP. It provides actionable implementation strategies for IT teams managing large-scale, high-density networks where real-time security and low latency are paramount.
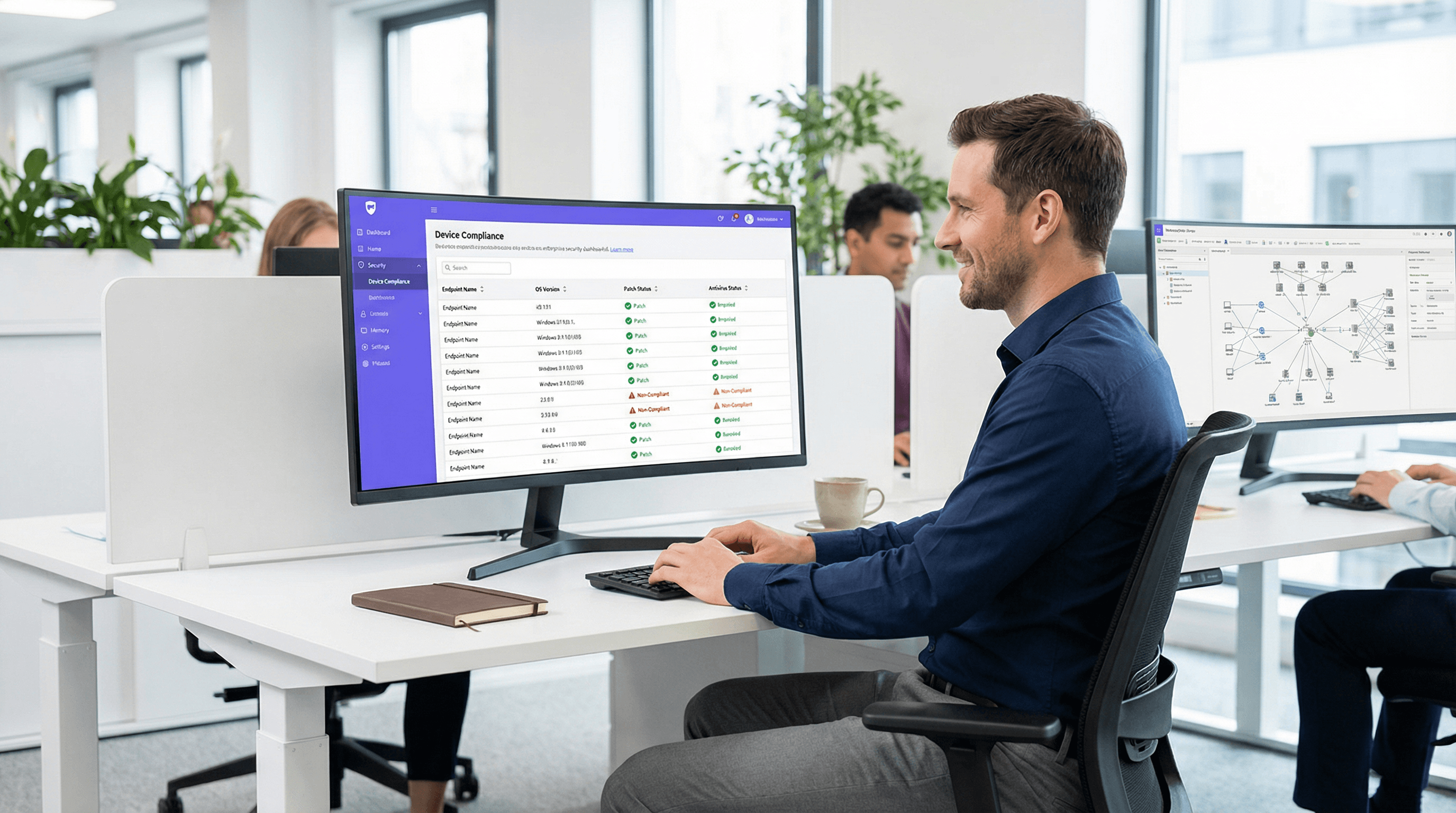
Device Posture Assessment for Network Access Control
This technical guide explains how device posture assessment works for Network Access Control (NAC), detailing the architecture, MDM integration, and remediation flows required to implement Zero Trust WiFi in enterprise and venue environments.

802.1X Authentication: Securing Network Access on Modern Devices
This guide provides a comprehensive, actionable overview of IEEE 802.1X authentication for senior IT professionals and network architects. It details the critical steps for securing network access across diverse enterprise environments, focusing on practical, vendor-neutral deployment guidance to mitigate risk, ensure compliance, and deliver a seamless, secure user experience.
Securing Networks with Wi-Fi 7: A Technical Deep Dive
This guide provides a comprehensive technical reference on Wi-Fi 7 security features for enterprise IT teams, covering the mandatory enforcement of WPA3 encryption, the security implications of Multi-Link Operation (MLO), and the practical challenges of supporting legacy devices during migration. It equips network architects, IT managers, and CTOs at hotels, retail chains, stadiums, and public-sector organisations with actionable deployment strategies, compliance guidance aligned to PCI DSS and GDPR, and real-world case studies with measurable outcomes. Understanding these changes is critical for any organisation planning a wireless infrastructure upgrade this year, as Wi-Fi 7 represents a fundamental shift in the security baseline for enterprise wireless networks.
Guest WiFi Marketing: The Ultimate Guide to Capturing Leads, Driving Sales, and Enhancing Customer Experience
This guide provides a technical deep-dive into leveraging guest WiFi for marketing, lead capture, and customer analytics. It offers actionable strategies for IT managers and venue operators to transform their WiFi from a cost centre into a powerful, ROI-driven marketing platform, covering architecture, implementation, and compliance.
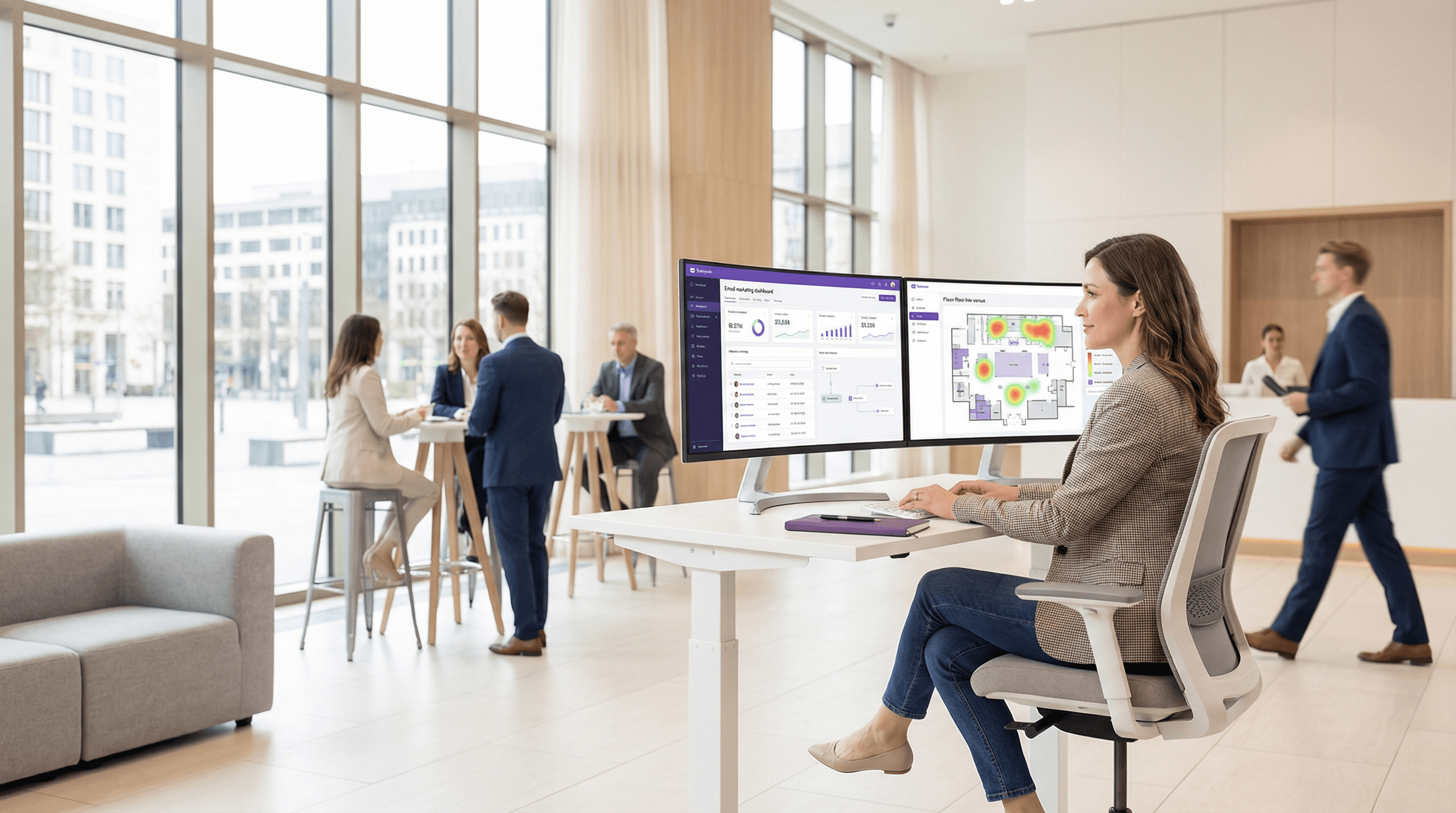
dotdigital (formerly Dotmailer): Integration Guide, Best Practices, and Troubleshooting for Purple AI Users
This guide provides Purple AI users — particularly IT managers, network architects, and CTOs at hotels, retail chains, stadiums, and conference centres — with a definitive technical reference for deploying and optimising the dotdigital (formerly Dotmailer) connector. It covers the end-to-end integration architecture, step-by-step configuration, GDPR-compliant data handling, automation programme design, and a structured troubleshooting framework. Organisations that implement this integration correctly convert guest WiFi logins into a high-value, consent-gated marketing database that drives measurable revenue outcomes.
MDU Login: Simplifying WiFi Access in Multi-Dwelling Units
This technical reference guide provides IT managers, network architects, and CTOs with a definitive framework for deploying and managing WiFi access in Multi-Dwelling Units (MDUs), covering the trade-offs between shared PSK, WPA3-Enterprise 802.1X, and Identity PSK (iPSK) authentication models. It addresses the core operational challenges of RF interference, security segmentation, and resident lifecycle management, and demonstrates how a managed WiFi platform such as Purple transforms connectivity from a cost centre into a measurable revenue asset. Drawing on real-world deployment scenarios and referencing standards including IEEE 802.1X, WPA3, GDPR, and PCI DSS, the guide equips venue operators with the architecture, implementation steps, and ROI metrics needed to make an informed investment decision this quarter.

Metropolitan Area Networks (MANs): A Deep Dive into Technologies, Applications, and Future Trends
This guide provides a comprehensive technical reference on Metropolitan Area Networks (MANs) for IT leaders and network architects. It covers core technologies, deployment strategies, and business considerations for implementing high-performance, city-scale networks. The content is tailored for decision-makers in hospitality, retail, events, and public-sector organisations.

Understanding and Hardening RADIUS Against MD5 Collision Attacks
This guide provides a comprehensive technical reference on the RADIUS MD5 collision vulnerability (CVE-2024-3596, 'Blast-RADIUS'), explaining how man-in-the-middle attackers can exploit weaknesses in the MD5-based Response Authenticator to forge authentication approvals without knowing user credentials. It is essential reading for IT managers, network architects, and CTOs operating enterprise WiFi in hospitality, retail, events, and public-sector environments who need to assess their exposure, apply immediate mitigations, and plan a strategic migration to modern authentication standards. The guide covers the full attack lifecycle, a phased hardening roadmap, real-world deployment scenarios, and compliance implications under PCI DSS, GDPR, and ISO 27001.

The Definitive Timeline of WiFi: From ALOHAnet to WiFi 7 and Beyond
This guide provides a definitive technical timeline of WiFi, tracing its origins from the 1971 ALOHAnet experiment through every major IEEE 802.11 standard to the ratification of WiFi 7 in 2024 and the emerging WiFi 8 roadmap. It is designed for IT managers, network architects, and CTOs who need to understand the engineering evolution of wireless technology to make informed infrastructure investment decisions. By contextualising each generation's innovations within real-world deployment scenarios across hospitality, retail, and large venues, the guide delivers actionable guidance on upgrading, securing, and future-proofing enterprise wireless networks.



