Captive Portal Customization and Security Best Practices
This guide provides a comprehensive technical reference for IT managers, network architects, and CTOs deploying captive portals across hospitality, retail, events, and public-sector environments. It covers the full deployment lifecycle — from VLAN architecture and authentication method selection through to GDPR compliance, portal hijacking prevention, and backend integration. Organisations that implement these practices will reduce security risk, achieve regulatory compliance, and transform guest Wi-Fi into a measurable business asset.
🎧 Listen to this Guide
View Transcript
Executive Summary
Deploying a secure and highly customised captive portal is no longer just a networking requirement; it is a critical intersection of infrastructure security, user experience, and data governance. For CTOs, network architects, and IT directors, the challenge lies in balancing seamless access with stringent security controls across diverse environments like Hospitality , Retail , and large public venues. This guide outlines the technical architecture, deployment strategies, and security best practices necessary to build resilient captive portals. By implementing robust authentication methods, proper VLAN segmentation, and adhering to compliance standards such as GDPR and PCI DSS, organisations can mitigate risks while extracting actionable intelligence through platforms like Purple's WiFi Analytics .

Technical Deep-Dive
Architecture and Traffic Flow
A robust captive portal deployment relies on a structured traffic flow that isolates unauthenticated users while providing a clear path to authentication. When a user connects to the Guest WiFi , the access point or wireless LAN controller (WLC) intercepts their initial HTTP/HTTPS requests. This traffic is redirected to the captive portal hosted either locally or in the cloud. The architecture must support dynamic VLAN assignment: unauthenticated users are placed in a restricted 'pre-auth' VLAN with access limited strictly to the captive portal and essential services (DNS and DHCP). Upon successful authentication via a RADIUS server, the WLC receives a Change of Authorisation (CoA) message, moving the user to a 'post-auth' VLAN with internet access.
The walled garden is a critical configuration element. It defines the set of URLs and IP ranges accessible before authentication. A poorly scoped walled garden is one of the most common vectors for DNS tunnelling attacks, where a malicious actor encapsulates arbitrary IP traffic within DNS queries to bypass the portal entirely. Restricting pre-auth DNS resolution to only the portal's own domain and known identity providers is a non-negotiable baseline.
Authentication Mechanisms
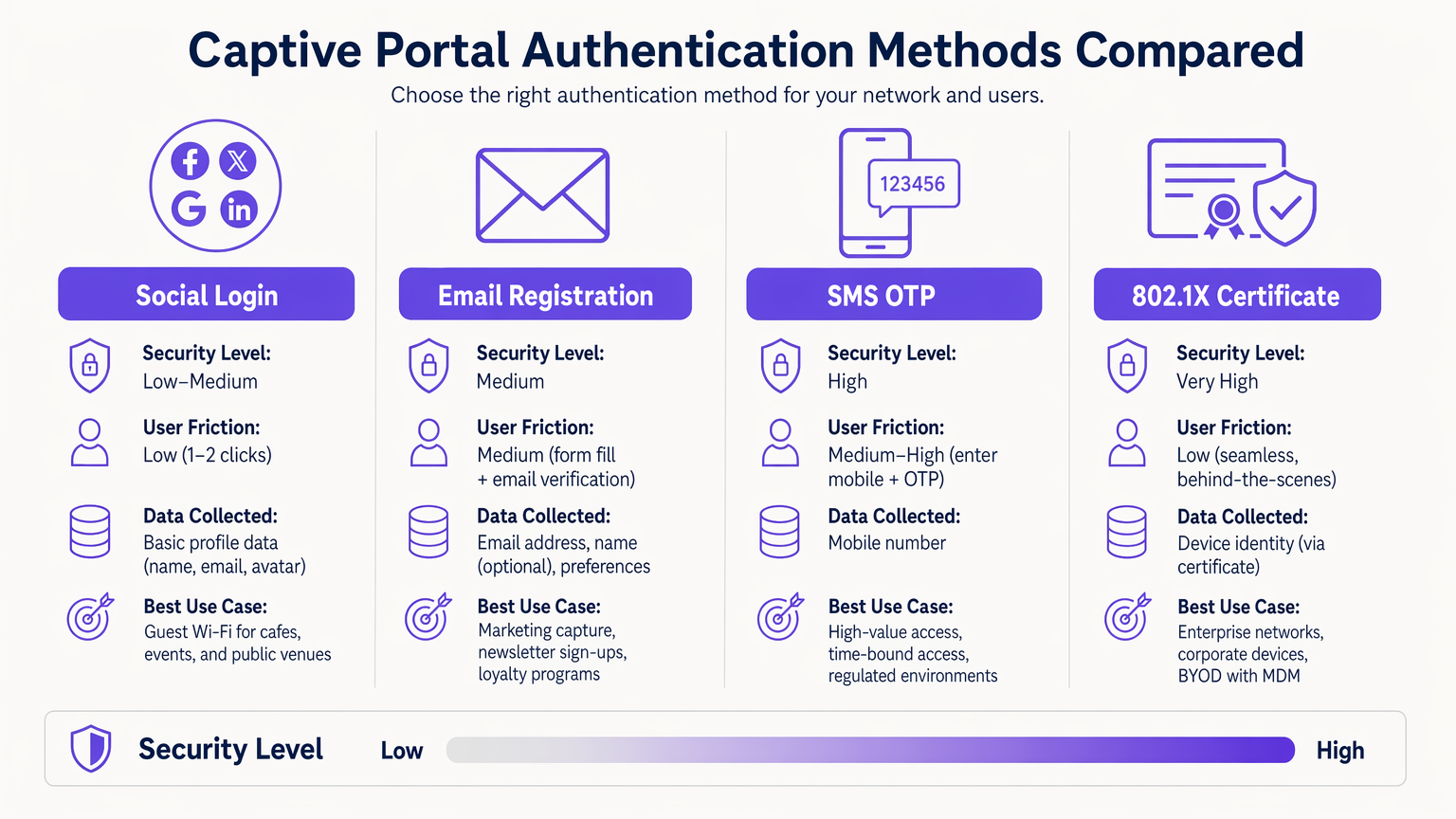
Selecting the right authentication mechanism is a risk-versus-friction trade-off that must be made deliberately for each deployment context.
| Method | Security Level | User Friction | Primary Use Case |
|---|---|---|---|
| 802.1X Certificate | Very High | Very Low (seamless) | Corporate BYOD, staff networks |
| SMS OTP | High | Medium-High | High-value or time-bound access |
| Email Registration | Medium | Medium | Marketing data capture, loyalty |
| Social Login (OAuth 2.0) | Low-Medium | Low | Guest Wi-Fi, public venues |
| Passpoint / Hotspot 2.0 | High | Very Low (automatic) | Returning users, roaming |
802.1X Certificate-Based Authentication is the gold standard for enterprise environments. It provides seamless, highly secure access using device certificates managed via an MDM platform, eliminating the risk of credential theft. For common deployment issues, refer to Troubleshooting Windows 11 802.1X Authentication Issues .
Passpoint (Hotspot 2.0) deserves particular attention. It enables automatic, secure roaming between Wi-Fi networks using WPA2/WPA3-Enterprise security. Purple acts as a free identity provider for services like OpenRoaming under the Connect licence, facilitating seamless connectivity without manual portal interaction for returning users.
Portal Design and Customisation
The portal's design directly impacts authentication conversion rates. A portal that takes more than three seconds to load on a mobile device will see significant drop-off. Use lightweight HTML/CSS, minimise JavaScript dependencies, and serve assets from a CDN. The portal must be fully responsive — in hospitality and retail environments, the majority of connections originate from mobile devices.
Branding is also a compliance issue. Under GDPR, the portal must present a clear, affirmative consent mechanism before collecting any PII. Pre-ticked checkboxes do not meet the standard for freely given, specific, informed, and unambiguous consent. The privacy policy and terms of service must be linked and accessible without completing authentication.
Implementation Guide
Deploying a captive portal requires a methodical approach across infrastructure, software, and compliance dimensions.
Step 1 — Infrastructure Preparation: Ensure your WLCs and access points support WPA3-SAE and dynamic VLAN assignment. Validate that your RADIUS infrastructure can handle the expected peak authentication load — for large venues, consider deploying RADIUS proxies locally to reduce WAN latency. If you are deploying specific hardware, consult resources like Your Guide to a Wireless Access Point Ruckus for vendor-specific configuration guidance.
Step 2 — VLAN and Firewall Architecture: Create dedicated VLANs for pre-auth guest traffic, post-auth guest traffic, staff, and IoT devices. Apply ACLs at the distribution layer to prevent any cross-VLAN communication. Guest VLANs must never route to corporate or POS network segments.
Step 3 — Walled Garden Configuration: Define the minimum required set of domains and IP ranges for pre-auth access. This must include the portal hostname, CDN domains for portal assets, and identity provider endpoints (e.g., accounts.google.com, graph.facebook.com for social login). Include captive portal detection endpoints for major operating systems (connectivitycheck.gstatic.com for Android, captive.apple.com for iOS) to ensure the portal triggers correctly.
Step 4 — Portal Deployment and Integration: Deploy the portal with a valid TLS certificate from a trusted CA. Integrate with your CRM or marketing platform via API to ensure captured data flows directly into your customer data infrastructure. Purple's WiFi Analytics platform provides out-of-the-box integrations with major CRM systems.
Step 5 — MAC Address Randomisation Handling: Modern iOS and Android devices use randomised MAC addresses. Transition your session management to rely on authenticated session tokens or device certificates rather than static MAC addresses to ensure a consistent experience for returning users.
Step 6 — Testing and Validation: Test across iOS, Android, Windows, and macOS. Simulate peak load scenarios to validate RADIUS throughput. Conduct penetration testing specifically targeting the walled garden configuration and DNS filtering controls.
Best Practices
Network Security Controls
For a comprehensive overview of the broader security landscape, refer to Securing Guest WiFi Networks: Best Practices and Implementation .
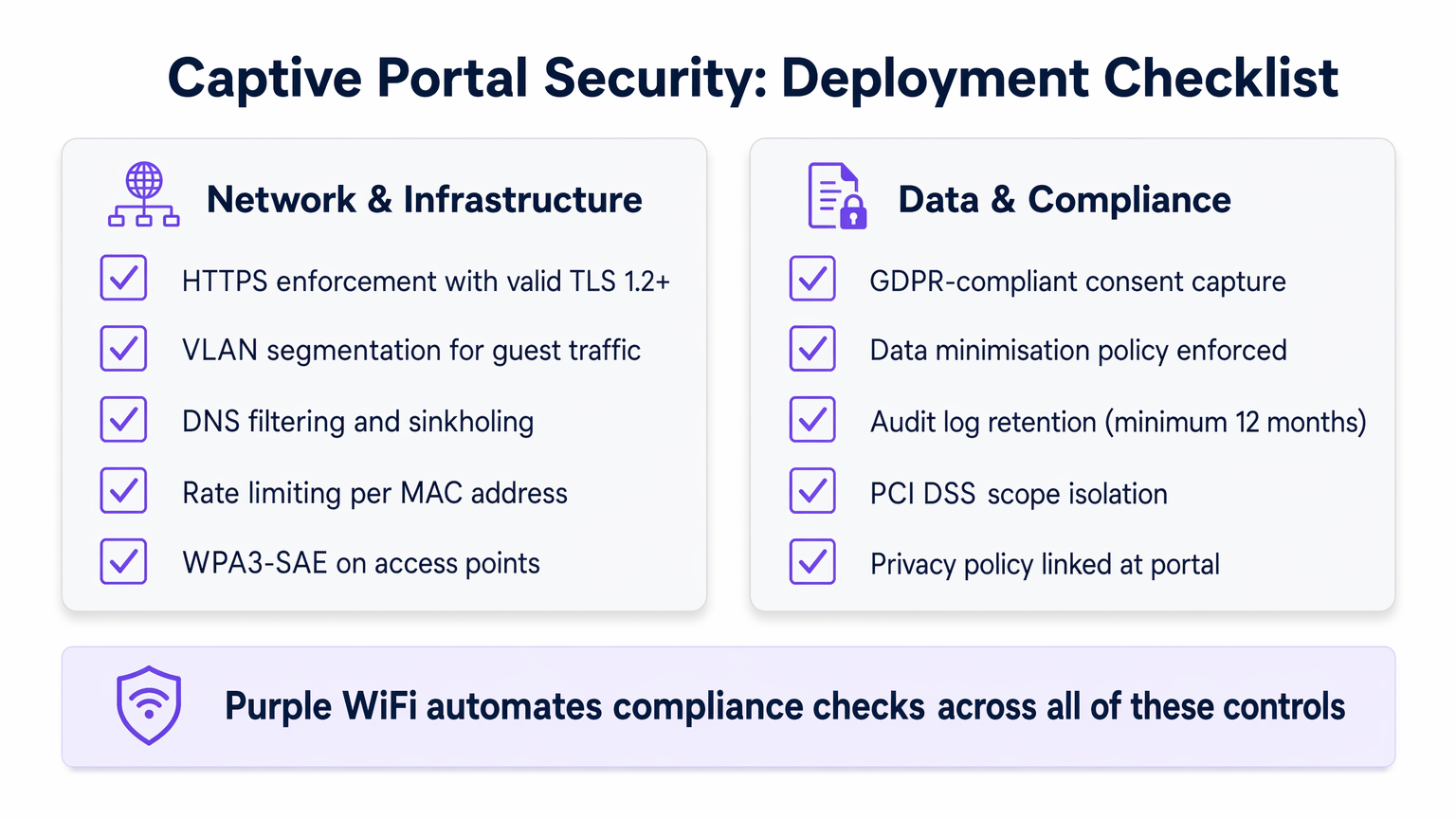
Enforce HTTPS: All portal traffic must be encrypted using TLS 1.2 or higher. Implement HTTP Strict Transport Security (HSTS) headers to prevent protocol downgrade attacks. A self-signed certificate will cause browser warnings and destroy user trust; always use a certificate from a trusted CA.
Client Isolation: Enable client isolation on guest access points to prevent device-to-device communication on the guest network. This mitigates lateral movement by malicious actors who have connected to the network.
Rate Limiting: Implement per-MAC-address rate limiting in the pre-auth state to prevent brute-force attacks against the portal and to limit the impact of DNS tunnelling attempts.
WPA3-SAE: Where hardware supports it, deploy WPA3-SAE (Simultaneous Authentication of Equals) on guest SSIDs. This provides forward secrecy, ensuring that even if a session key is compromised, historical traffic cannot be decrypted.
Data Privacy and Compliance
Captive portals are prime data collection points, making compliance a critical engineering requirement rather than an afterthought.
GDPR and CCPA Compliance: Explicit, affirmative consent must be captured before collecting any PII. Implement a double opt-in mechanism for marketing communications. Ensure your data processor agreements with third-party platforms are current.
Data Minimisation: Collect only what is strictly necessary. For a guest Wi-Fi deployment, this typically means an email address and explicit marketing consent. Avoid collecting date of birth, phone numbers, or demographic data unless there is a clear, documented business justification.
PCI DSS Scope Isolation: Retail environments must ensure the guest network is entirely out of PCI DSS scope. This requires strict physical and logical separation from POS systems, validated annually by a Qualified Security Assessor (QSA).
Audit Log Retention: Maintain authentication logs for a minimum of 12 months to support incident investigation and regulatory requests. Ensure logs are stored in a tamper-evident format.
Troubleshooting & Risk Mitigation
Even well-architected deployments encounter predictable failure modes. The following table outlines the most common issues and their resolutions.
| Issue | Root Cause | Resolution |
|---|---|---|
| Portal not triggering on iOS/Android | CPD endpoints blocked in walled garden | Add captive.apple.com and connectivitycheck.gstatic.com to walled garden |
| RADIUS authentication timeouts | High WAN latency to RADIUS server | Deploy local RADIUS proxy; check firewall rules on UDP 1812/1813 |
| DNS tunnelling detected | Overly permissive pre-auth DNS | Implement DNS sinkholing; restrict pre-auth DNS to portal resolver only |
| Returning users re-prompted every visit | MAC randomisation breaking session tracking | Migrate to cookie-based or certificate-based session management |
| Portal SSL certificate warning | Expired or self-signed certificate | Deploy auto-renewing certificate via Let's Encrypt or enterprise CA |
| IoT devices unable to connect | Headless devices cannot complete portal flow | Implement MAC Authentication Bypass (MAB) for registered IoT devices |
For environments with complex clinical or regulated network requirements, such as NHS trusts or private hospitals, additional controls apply. See WiFi in Hospitals: A Guide to Secure Clinical Networks for sector-specific guidance. Similarly, transport hubs with distributed RADIUS infrastructure present unique latency challenges — see Your Guide to Enterprise In Car Wi Fi Solutions for high-density, distributed deployment patterns relevant to Transport environments.
ROI & Business Impact
A properly implemented captive portal transforms a cost centre into a strategic asset with measurable returns.
Data Acquisition and CRM Integration: By offering seamless Wi-Fi, venues capture valuable first-party data at the point of connection. This data feeds directly into CRM systems, enabling targeted marketing campaigns. Hospitality operators using Purple's platform have reported authentication-to-email-capture rates of 60–75%, with measurable increases in repeat visit rates when that data is used for personalised outreach.
Operational Efficiency: Automated onboarding and self-service access reduce helpdesk burden. In enterprise deployments using 802.1X, the elimination of shared passwords reduces the IT overhead associated with credential rotation.
Compliance as a Competitive Differentiator: Organisations that can demonstrate GDPR-compliant data capture and PCI DSS scope isolation are increasingly preferred by enterprise clients and public-sector procurement teams. Compliance is not just a risk mitigation exercise; it is a commercial advantage.
Measurable KPIs: Track authentication conversion rate (target: >70%), average session duration, return visitor rate, and CRM data enrichment rate. These metrics, available through Purple's WiFi Analytics platform, provide the business case for continued investment in the portal infrastructure.
In Healthcare settings, reliable and secure connectivity demonstrably improves patient and visitor satisfaction scores, with several NHS trusts reporting CSAT improvements of 15–20% following structured guest Wi-Fi deployments.
Key Terms & Definitions
Captive Portal
A network access control mechanism that intercepts HTTP/HTTPS traffic from unauthenticated clients and redirects them to a web-based authentication or registration page before granting internet access.
IT teams encounter this as the primary onboarding mechanism for guest Wi-Fi. The portal is the enforcement boundary between untrusted devices and the network, and its configuration directly impacts both security posture and user experience.
VLAN Segmentation
The practice of dividing a physical network into multiple logical networks (VLANs) to isolate traffic between different user groups or system types, enforced via 802.1Q tagging and ACLs.
Critical for any deployment where guest users share physical infrastructure with corporate systems or POS terminals. Proper VLAN segmentation is a prerequisite for PCI DSS compliance in retail environments.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol (RFC 2865) that provides centralised Authentication, Authorisation, and Accounting (AAA) for network access. In captive portal deployments, the RADIUS server validates credentials and instructs the WLC to assign the appropriate VLAN via Change of Authorisation (CoA).
The backbone of enterprise Wi-Fi authentication. IT teams must size RADIUS infrastructure for peak concurrent authentication load and ensure low latency between WLCs and the RADIUS server to prevent authentication timeouts.
Walled Garden
A restricted set of URLs, IP addresses, and domains that unauthenticated users are permitted to access before completing the captive portal flow. All other traffic is blocked.
A misconfigured walled garden is one of the most common security vulnerabilities in captive portal deployments. It must be as restrictive as possible while including captive portal detection endpoints for major operating systems to ensure the portal triggers correctly.
MAC Authentication Bypass (MAB)
A mechanism that allows headless devices (those without a browser, such as IoT sensors, smart TVs, or printers) to bypass the captive portal by pre-registering their MAC address in the RADIUS server.
Essential for any venue deploying IoT devices on the same physical infrastructure as guest Wi-Fi. MAB devices should always be assigned to a dedicated, restricted IoT VLAN, never to the general guest VLAN.
Passpoint (Hotspot 2.0)
A Wi-Fi Alliance specification (based on IEEE 802.11u) that enables automatic, secure authentication to Wi-Fi networks using WPA2/WPA3-Enterprise, eliminating the need for manual portal interaction for credentialed users.
Increasingly relevant for venues with high return-visitor rates, such as hotels and transport hubs. Purple provides identity provider services for OpenRoaming, a Passpoint-based global roaming network, under the Connect licence.
Change of Authorisation (CoA)
A RADIUS extension (RFC 5176) that allows the RADIUS server to dynamically modify an active session — typically to reassign a user to a different VLAN after successful authentication via the captive portal.
The mechanism that enables dynamic VLAN assignment in captive portal deployments. Without CoA support, the WLC cannot move a user from the pre-auth VLAN to the post-auth VLAN without forcing a full re-association.
DNS Tunnelling
An attack technique that encodes arbitrary data within DNS query and response packets to bypass network access controls, including captive portals, by exploiting the fact that DNS traffic is often permitted in the pre-auth state.
A significant risk in captive portal deployments with permissive pre-auth DNS configurations. Mitigated by restricting pre-auth DNS resolution to a controlled resolver and implementing DNS sinkholing and rate-limiting.
WPA3-SAE (Simultaneous Authentication of Equals)
The authentication protocol introduced in WPA3 that replaces the Pre-Shared Key (PSK) handshake with a Dragonfly key exchange, providing forward secrecy and resistance to offline dictionary attacks.
The recommended encryption standard for guest SSIDs on modern hardware. Forward secrecy ensures that compromising one session key does not expose historical traffic, which is particularly important on shared guest networks.
TLS (Transport Layer Security)
A cryptographic protocol that provides encrypted communication between a client and server. For captive portals, TLS 1.2 or higher is required to protect credentials and PII transmitted during the authentication flow.
All captive portal traffic must be served over HTTPS with a valid TLS certificate from a trusted CA. A self-signed certificate will trigger browser security warnings, destroying user trust and reducing authentication conversion rates.
Case Studies
A 200-room hotel group with 15 properties needs to deploy a branded captive portal that captures guest email addresses for their loyalty programme, handles peak loads of 500 concurrent authentications per property, and complies with GDPR. Their existing infrastructure uses a mix of Cisco and Ruckus access points. How should they approach this deployment?
The recommended architecture is a cloud-hosted captive portal with local RADIUS proxies at each property. Deploy a central RADIUS server (or use a managed RADIUS-as-a-Service) with local proxy instances at each site to handle authentication requests with sub-100ms latency regardless of WAN conditions. Configure dynamic VLAN assignment: VLAN 10 for pre-auth guests, VLAN 20 for post-auth guests, VLAN 30 for staff (802.1X authenticated). The walled garden must include the portal domain, CDN assets, and social login provider endpoints. For the portal itself, use email registration with a GDPR-compliant double opt-in flow: the user enters their email, receives a confirmation link, and is granted access upon clicking. This ensures verified email capture. Integrate the portal API with the hotel's CRM (e.g., Salesforce or HubSpot) to push new contacts in real time. For the Cisco/Ruckus mixed environment, use RADIUS CoA (RFC 5176) for post-authentication VLAN assignment — both vendors support this natively. Test the walled garden configuration specifically on iOS 16+ and Android 12+ to validate captive portal detection behaviour with MAC randomisation enabled.
A national retail chain with 80 stores needs to deploy guest Wi-Fi across all locations. Their POS systems are on the same physical network infrastructure. They need to ensure PCI DSS compliance while capturing marketing consent from shoppers. What is the correct network architecture?
The non-negotiable first step is network segmentation. Deploy dedicated SSIDs: one for guest access (captive portal) and one for staff/POS (802.1X, WPA3-Enterprise). Assign these to separate VLANs with ACLs at the distribution switch layer that explicitly deny any traffic between the guest VLAN and the POS VLAN. The guest VLAN should route directly to the internet via a dedicated uplink or VLAN-tagged subinterface, never through the corporate routing infrastructure. For the captive portal, use email registration with explicit marketing consent capture. The consent checkbox must be unchecked by default and must clearly state the marketing purpose. Integrate the portal with the retail chain's marketing platform (e.g., Klaviyo or Dotdigital) via API. Implement DNS filtering on the guest VLAN to block known malicious domains and prevent DNS tunnelling. Conduct an annual PCI DSS scope review with a QSA to validate that the guest network remains out of scope. Document the network segmentation controls in the PCI DSS compliance evidence pack.
Scenario Analysis
Q1. A conference centre hosts 50 events per year, ranging from 200-person seminars to 5,000-person trade shows. They want a single captive portal deployment that can handle both scenarios. The IT team is concerned about RADIUS capacity at peak load and about ensuring the portal triggers correctly on all devices. What architecture decisions should they prioritise?
💡 Hint:Consider the difference in authentication load between a 200-person and a 5,000-person event, and think about what happens to the RADIUS server if it is the single point of failure.
Show Recommended Approach
The architecture must be designed for the peak case (5,000 concurrent users) but must remain cost-effective for smaller events. Deploy a cloud-hosted RADIUS service with auto-scaling capability rather than a fixed on-premises RADIUS server. This eliminates the capacity planning problem. For captive portal detection reliability, ensure the walled garden includes all major OS captive portal detection endpoints (Apple, Google, Microsoft). Use a CDN to serve portal assets to minimise load time regardless of concurrent user count. Implement per-AP rate limiting to prevent any single access point from overwhelming the RADIUS server during simultaneous association bursts (common when a session break ends at a large event). Consider deploying Passpoint for returning attendees to eliminate portal friction entirely for credentialed users.
Q2. An NHS trust wants to deploy guest Wi-Fi across a 600-bed hospital. Clinical staff use the same physical network infrastructure. The trust's Information Governance team has flagged concerns about patient data exposure and GDPR compliance for visitor data capture. What are the three most critical architectural controls to implement?
💡 Hint:Think about the three distinct user groups (patients/visitors, clinical staff, medical devices) and the data sensitivity associated with each.
Show Recommended Approach
The three critical controls are: (1) Strict VLAN segmentation with three separate VLANs — guest/visitor (captive portal), clinical staff (802.1X WPA3-Enterprise), and medical devices (MAB with dedicated IoT VLAN). ACLs must prevent any cross-VLAN traffic. (2) GDPR-compliant consent capture on the visitor portal, with data minimisation enforced — collect only email and explicit marketing consent, with automated 30-day purge for inactive records. The portal must link to the trust's privacy notice. (3) Client isolation on the guest SSID to prevent device-to-device communication, which is particularly important in a healthcare environment where patients may be vulnerable to social engineering or device exploitation. See the dedicated guide at WiFi in Hospitals for further sector-specific controls.
Q3. A retail IT director has received a finding from their PCI DSS QSA stating that the guest Wi-Fi network is 'potentially in scope' for PCI DSS because the guest VLAN is routed through the same core switch as the POS VLAN. The QSA has given them 90 days to remediate. What is the fastest path to achieving scope isolation without replacing the core switch?
💡 Hint:Physical replacement of infrastructure is not always necessary — consider what logical controls can achieve the same outcome as physical separation, and what evidence the QSA will need to close the finding.
Show Recommended Approach
The fastest remediation path is to implement explicit deny ACLs on the core switch between the guest VLAN and all POS VLANs, combined with a network penetration test to validate that no traffic path exists between the two segments. Document the ACL rules and the test results as evidence for the QSA. Additionally, configure the guest VLAN to route directly to the internet via a dedicated subinterface or VLAN-tagged uplink to the ISP, bypassing the corporate routing table entirely. This removes the guest VLAN from the corporate routing domain, which is the strongest logical isolation achievable without physical separation. The QSA will typically accept this as a compensating control if it is accompanied by a documented penetration test confirming no cross-VLAN traffic paths exist.



