GDPR and WiFi: A Compliance Guide for Businesses
A comprehensive guide for IT leaders and venue operators on managing GDPR compliance within enterprise WiFi networks. It covers data mapping, lawful bases for processing, splash page consent design, and automated retention policies.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: What Data Are You Actually Collecting?
- Lawful Basis for Processing
- Splash Page Architecture and Consent Design
- Implementation Guide: A Step-by-Step Approach
- Step 1: Data Mapping and ROPA
- Step 2: Configure the Captive Portal
- Step 3: Implement Automated Data Retention
- Step 4: Execute Data Processing Agreements (DPAs)
- Best Practices
- Troubleshooting & Risk Mitigation
- ROI & Business Impact

Executive Summary
For CTOs, IT managers, and venue operations directors, guest WiFi is a double-edged sword. On one hand, it is a critical utility for guest experience and a powerful engine for WiFi Analytics . On the other, it represents a significant surface area for data protection risk. If you operate Guest WiFi in Retail , Hospitality , or Transport , you are processing personal data under the General Data Protection Regulation (GDPR).
This guide cuts through the legal jargon to provide a practical, technical framework for compliance. We cover the specific data points captured by network infrastructure, how to design captive portals that meet the threshold for explicit consent, and how to implement automated retention policies that protect your organisation from regulatory enforcement while enabling valuable business insights.
Listen to our 10-minute executive briefing:
Technical Deep-Dive: What Data Are You Actually Collecting?
A common misconception among network architects is that MAC addresses and IP addresses are purely technical identifiers. Under GDPR, if a data point can be used—directly or indirectly—to identify a natural person, it constitutes personal data.
When a device associates with a WiFi Access Point, the network controller logs the MAC address. When the user passes through the captive portal, they are assigned an IP address. Both are personal data. If your splash page includes a registration form, you are also capturing explicitly identifiable information such as names, email addresses, and potentially demographic data.
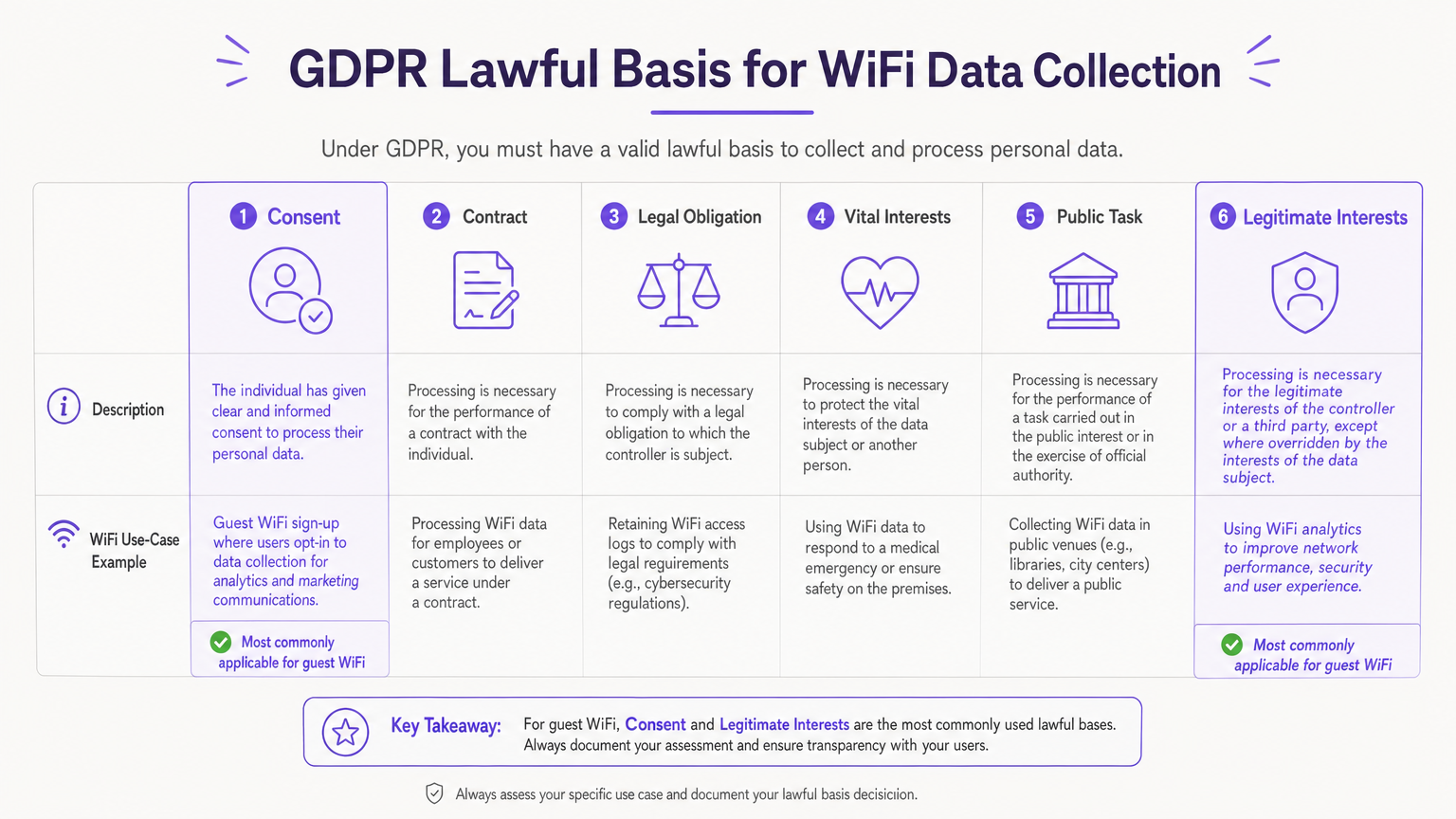
Lawful Basis for Processing
Article 6 of the GDPR requires a lawful basis for processing any personal data. For guest WiFi deployments, two bases are primarily relevant:
- Legitimate Interests: Often used for processing underlying network connection data (MAC addresses, session logs) necessary to provide a secure and functional service. This requires a documented Legitimate Interests Assessment (LIA).
- Consent: The mandatory basis for processing data for direct marketing purposes. Consent must be freely given, specific, informed, and unambiguous.
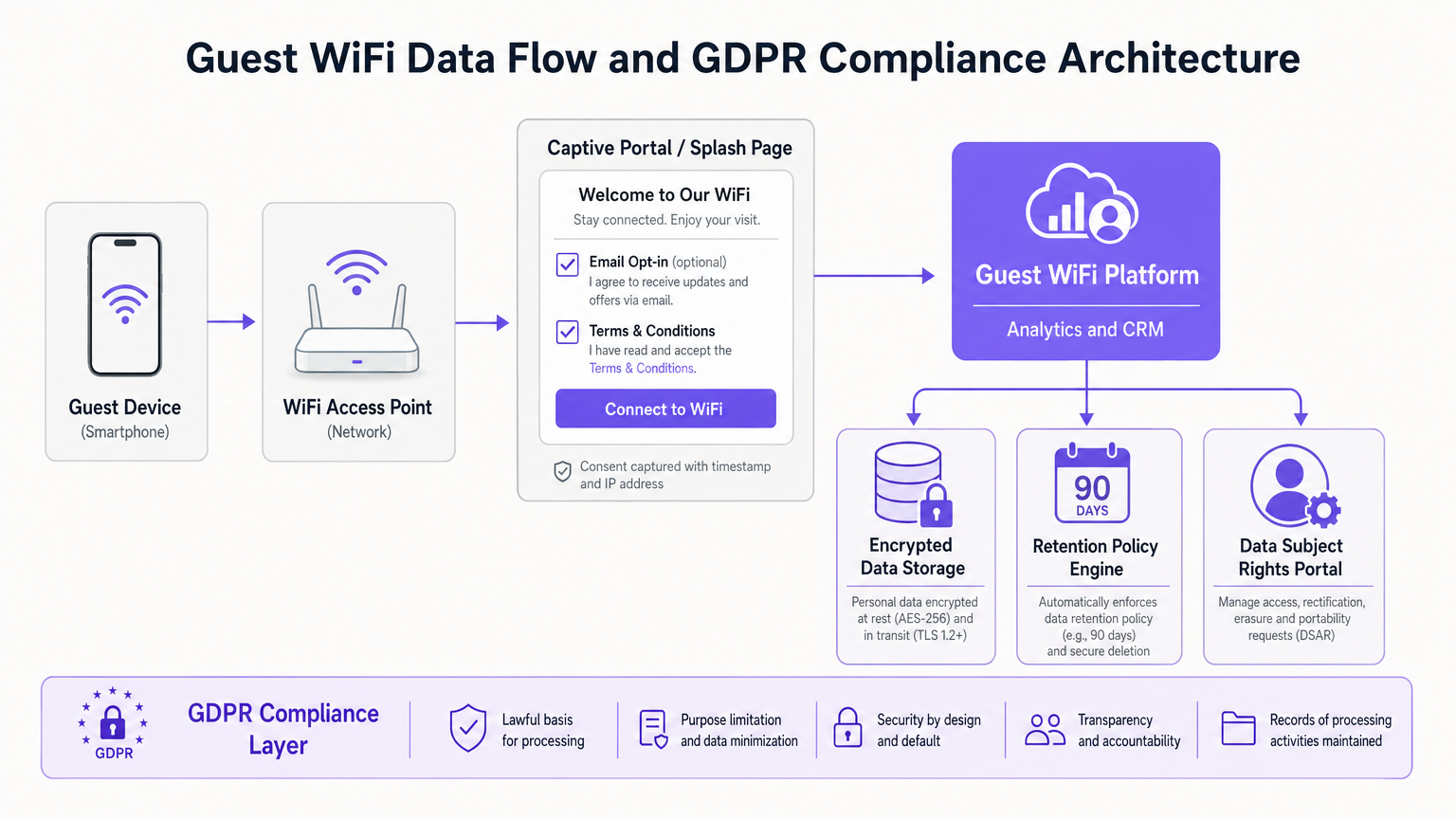
Splash Page Architecture and Consent Design
The splash page is the critical interface for GDPR compliance. A compliant architecture must separate the acceptance of terms and conditions from marketing consent.
- No Pre-ticked Boxes: Marketing opt-ins must require a deliberate action by the user.
- Unbundled Consent: You cannot make network access conditional upon agreeing to receive marketing communications.
- Granularity: If you are collecting data for multiple purposes (e.g., email marketing, SMS marketing, third-party sharing), each requires a separate consent mechanism.
- Transparency: A clear link to your organisation's Privacy Notice must be present before the user connects.
Implementation Guide: A Step-by-Step Approach
Deploying a compliant guest WiFi solution requires moving beyond static policies to technical enforcement.
Step 1: Data Mapping and ROPA
Before configuring any systems, map the data flow. Document exactly what data your access points, controllers, and analytics platforms collect. This forms your Record of Processing Activities (ROPA) under Article 30.
Step 2: Configure the Captive Portal
Implement a splash page that strictly adheres to the consent design principles outlined above. Ensure that the platform captures a verifiable timestamp and IP address alongside any consent given, creating an immutable audit trail.
Step 3: Implement Automated Data Retention
Article 5(1)(e) dictates that data must not be kept longer than necessary. Manual deletion processes are prone to failure. Configure your Guest WiFi platform to automatically purge network logs (e.g., after 90 days for security purposes) and unengaged marketing contacts according to your defined retention schedule.
Step 4: Execute Data Processing Agreements (DPAs)
If you utilise a third-party vendor for WiFi analytics or captive portal management, they act as a Data Processor. Article 28 mandates a signed DPA detailing the scope, nature, and purpose of the processing, as well as the security measures the processor must implement.
Best Practices
- Anonymisation and Aggregation: When utilising WiFi Analytics for footfall or dwell time analysis, ensure the data is anonymised or aggregated to mitigate privacy risks.
- Regular Audits: Treat GDPR compliance as an ongoing programme. Conduct annual audits of your splash page configuration, retention settings, and vendor DPAs.
- Data Subject Rights: Ensure you have a clear process for handling Data Subject Access Requests (DSARs) and requests for erasure (the right to be forgotten) within the statutory one-month timeframe.
Troubleshooting & Risk Mitigation
Common Failure Mode: "Consent Walls" Many venues attempt to force marketing consent by hiding the "Connect" button until the marketing box is ticked. This invalidates the consent under GDPR, as it is not "freely given." Fix: Offer clear, separate options. Provide an incentive for marketing opt-in (e.g., a discount code), but ensure a path to connect without opting in.
Common Failure Mode: Stale Data Accumulating years of guest data without a purging mechanism increases your risk profile in the event of a breach. Fix: Leverage platforms like Purple that offer automated retention policy engines to enforce your data lifecycle rules programmatically.
ROI & Business Impact
Compliance is often viewed as a cost centre, but a well-architected, GDPR-compliant WiFi deployment actually drives business value. By building trust through transparent data practices, venues see higher quality data capture. When guests explicitly opt-in, the resulting marketing database is highly engaged, driving better conversion rates for retail promotions or hospitality loyalty programmes. For more on maximizing this value, see our guide on How to Collect First-Party Data Through WiFi .
Key Terms & Definitions
Captive Portal
The web page that users are directed to before gaining access to a public WiFi network, used for authentication and consent capture.
This is the primary interface where IT teams must implement GDPR-compliant consent mechanisms.
Data Controller
The entity that determines the purposes and means of the processing of personal data.
The venue operator (e.g., the hotel or retailer) is typically the Data Controller and holds primary legal responsibility.
Data Processor
An entity that processes personal data on behalf of the controller.
Third-party vendors, such as cloud WiFi analytics platforms (like Purple), act as Data Processors and require a DPA.
Data Processing Agreement (DPA)
A legally binding contract between a Data Controller and a Data Processor regulating how personal data is handled.
IT managers must ensure a signed DPA is in place with every vendor in the WiFi technology stack.
Lawful Basis
The legal justification under Article 6 of the GDPR required to process personal data.
IT teams must document whether they are relying on Consent, Legitimate Interests, or another basis for each data type collected.
Legitimate Interests Assessment (LIA)
A documented risk assessment demonstrating that the processing of personal data is necessary and balanced against the individual's rights.
Required when retaining network logs for security purposes without explicit user consent.
Record of Processing Activities (ROPA)
A formal document detailing all personal data processing activities within an organisation.
The output of the initial data mapping exercise, required by Article 30 for most enterprise deployments.
Data Subject Access Request (DSAR)
A request from an individual to access the personal data an organisation holds about them.
IT teams must have technical mechanisms in place to extract and provide a user's WiFi session and registration data within one month.
Case Studies
A 200-room hotel needs to implement guest WiFi. The marketing director wants to capture email addresses to promote the hotel restaurant, but the IT director is concerned about GDPR compliance regarding network logs.
- The IT team configures the network controllers to retain MAC addresses and session data for 90 days under the lawful basis of 'Legitimate Interests' (for network security and troubleshooting), documenting this in an LIA.
- The captive portal is designed with two distinct sections: a mandatory checkbox for accepting the Terms of Service, and an optional, unticked checkbox for restaurant marketing emails.
- The hotel updates its Privacy Notice to clearly state these two distinct processing activities and links to it from the splash page.
A large retail chain uses WiFi analytics to track customer footfall and dwell time across 50 stores. They want to ensure this tracking doesn't violate GDPR.
The retail chain configures their WiFi analytics platform to immediately hash or pseudonymise MAC addresses upon collection. They use this aggregated data to generate heatmaps and footfall trends without identifying individual shoppers. They also place clear signage at store entrances informing customers that anonymised WiFi analytics are in use.
Scenario Analysis
Q1. Your marketing team wants to increase the size of their email database. They propose changing the guest WiFi splash page so that the 'Connect to Internet' button only becomes active after the user ticks a box agreeing to receive promotional offers. Is this compliant?
💡 Hint:Consider the GDPR definition of 'freely given' consent.
Show Recommended Approach
No, this is not compliant. This creates a 'consent wall' or bundled consent. Under GDPR, consent must be freely given. If access to the service (the WiFi) is made conditional on consenting to marketing, the consent is invalid. The marketing opt-in must be separate and optional.
Q2. A guest requests a copy of all data your venue holds on them (a DSAR). Your IT team exports their CRM profile showing their name and email, but ignores the WiFi controller logs containing their MAC address and connection times. Have you fulfilled the DSAR?
💡 Hint:Think about what constitutes 'personal data' under GDPR.
Show Recommended Approach
No. Because MAC addresses and connection logs can be linked to the identified individual (especially since they registered via the captive portal), those logs constitute personal data. A complete DSAR response must include the network-level data associated with their device.
Q3. You are migrating to a new cloud-based WiFi analytics provider. The vendor provides a standard Terms of Service document online. Is this sufficient for GDPR compliance?
💡 Hint:Review the requirements for engaging third-party data processors.
Show Recommended Approach
No. Under Article 28, you must have a formal, written Data Processing Agreement (DPA) in place with the vendor. The DPA must specifically detail the nature, purpose, and duration of the processing, the types of personal data involved, and the security obligations of the processor.



