What Types of Customer Data Can WiFi Capture?
This authoritative guide details the four core categories of customer data captured by enterprise WiFi platforms: identity, behavioural, declared, and device metadata. It provides actionable architecture, compliance, and deployment guidance for IT leaders to transform guest network infrastructure into a secure, first-party data asset.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: The Four Categories of WiFi Data
- 1. Identity Data (Declared Identifiers)
- 2. Behavioural Data (Network Analytics)
- 3. Declared Data (Progressive Profiling)
- 4. Device & Network Metadata
- Implementation Guide: Architecting for Data Capture
- Overcoming MAC Randomisation
- Progressive Profiling vs. Friction
- Best Practices & Compliance
- ROI & Business Impact

Executive Summary
For enterprise venues—from Retail estates to Hospitality groups—guest WiFi has evolved from a basic amenity into a critical data acquisition channel. However, many organisations still deploy wireless networks as pure IT infrastructure, missing the opportunity to capture high-signal, first-party customer intelligence. This guide details the exact types of customer data an enterprise Guest WiFi platform can capture, the technical architecture required to do so securely, and the compliance frameworks necessary to protect it. We explore the four primary data categories: identity, behavioural, declared, and device metadata. For CTOs and network architects, the objective is clear: implement a robust WiFi Analytics layer that delivers measurable ROI through CRM enrichment, while strictly adhering to data minimisation and GDPR principles.
Technical Deep-Dive: The Four Categories of WiFi Data
When a user associates with an enterprise wireless network, the platform can capture data across four distinct categories. Understanding the technical mechanisms and limitations of each is essential for effective deployment.
1. Identity Data (Declared Identifiers)
Identity data is explicitly provided by the user during the authentication process at the captive portal (splash page). This is the foundation of your first-party data strategy.
- Email Address & Phone Number: Captured via standard form fields. These serve as the primary persistent identifiers for CRM integration.
- Social Login Profile: Captured via OAuth integration (e.g., Facebook, Google, Apple). Depending on user consent, this can yield rich profile data including name, age range, and verified email.
Technical Architecture Note: The capture of identity data must be coupled with an auditable consent log. The platform must record the timestamp, IP address, MAC address, and the specific Terms & Conditions presented to the user. Purple's architecture automates this logging to ensure Article 7 GDPR compliance.
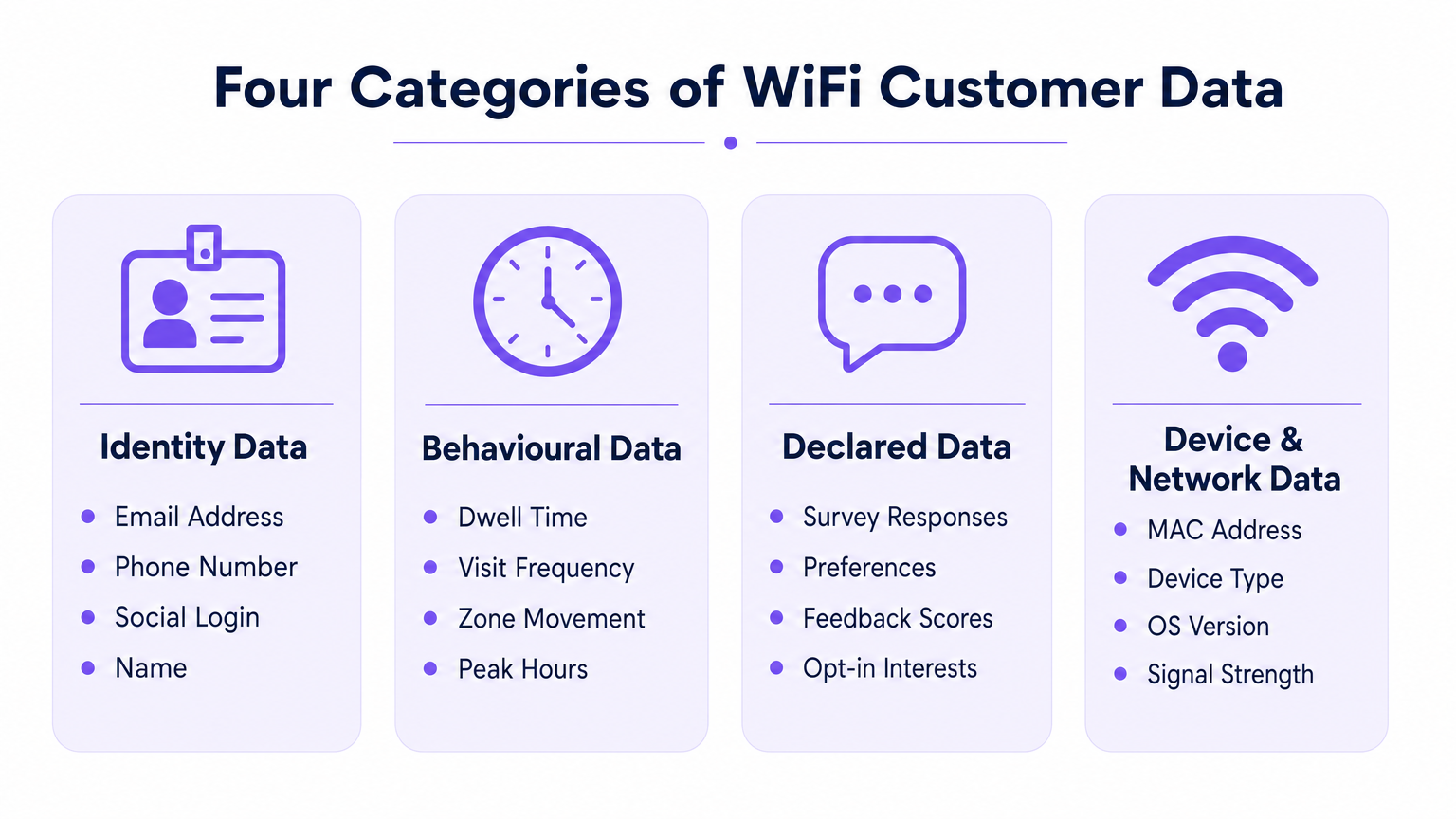
2. Behavioural Data (Network Analytics)
Behavioural data is derived passively from the device's interaction with the network infrastructure. It does not require active user input beyond maintaining a connection.
- Presence & Dwell Time: The duration a device remains associated with the network. High dwell times in specific zones (e.g., a hotel bar or retail display) correlate strongly with conversion intent.
- Visit Frequency & Recency: Tracking the delta between visits to distinguish first-time visitors from loyal returners.
- Zone-Level Movement: By triangulating Received Signal Strength Indicator (RSSI) data across multiple access points, platforms can map user journeys through a physical space. For a deeper dive into the underlying technology, see our guide on Indoor Positioning System: UWB, BLE, & WiFi Guide .
3. Declared Data (Progressive Profiling)
Declared data goes beyond basic identity, capturing explicit preferences directly from the user. This data has the highest signal quality because it relies on direct input rather than inference.
- Survey Responses: Post-authentication or post-visit surveys (e.g., Net Promoter Score, facility feedback).
- Preference Capture: In-session prompts gathering specific interests (e.g., dietary requirements in Healthcare or product interests in retail).
4. Device & Network Metadata
This data is generated by the device hardware and operating system during the 802.11 association process.
- MAC Address: The hardware identifier. Crucial constraint: Since iOS 14 and Android 10, per-network MAC randomisation is the default. MAC addresses can no longer be reliably used as persistent cross-visit identifiers without an authenticated user record.
- Device Type & OS Version: Extracted from the HTTP User-Agent string during portal rendering or via DHCP fingerprinting.
- Data Usage: Throughput metrics (upload/download volume), which assist in capacity planning and identifying bandwidth-heavy users.
Implementation Guide: Architecting for Data Capture
Deploying a data-centric WiFi network requires architectural decisions that balance user experience with data yield.
Overcoming MAC Randomisation
The most significant architectural shift in recent years is the deprecation of the MAC address as a persistent identifier. To track repeat visits accurately, the architecture must anchor the user profile to the authenticated credential (email/phone) rather than the device hardware.
- Session Initiation: Device connects with a randomised MAC.
- Authentication: User provides email via the captive portal.
- Profile Binding: The platform binds the current randomised MAC session to the persistent email profile.
- Subsequent Visits: If the device presents a new randomised MAC, the user must re-authenticate (often seamlessly via a returning user flow or profile-based authentication like OpenRoaming) to re-bind the session to their profile.
Progressive Profiling vs. Friction
Do not ask for every data point on the first connection. High-friction captive portals suffer from high abandonment rates. Implement progressive profiling: ask for an email address on visit one, a phone number on visit three, and a preference survey on visit five.
For specific guidance on securing this data once captured, refer to How to Protect Customer Data Collected via WiFi .
Best Practices & Compliance
Treat guest WiFi as a data strategy project, not just an IT deployment. Compliance must be built into the architecture from day one.
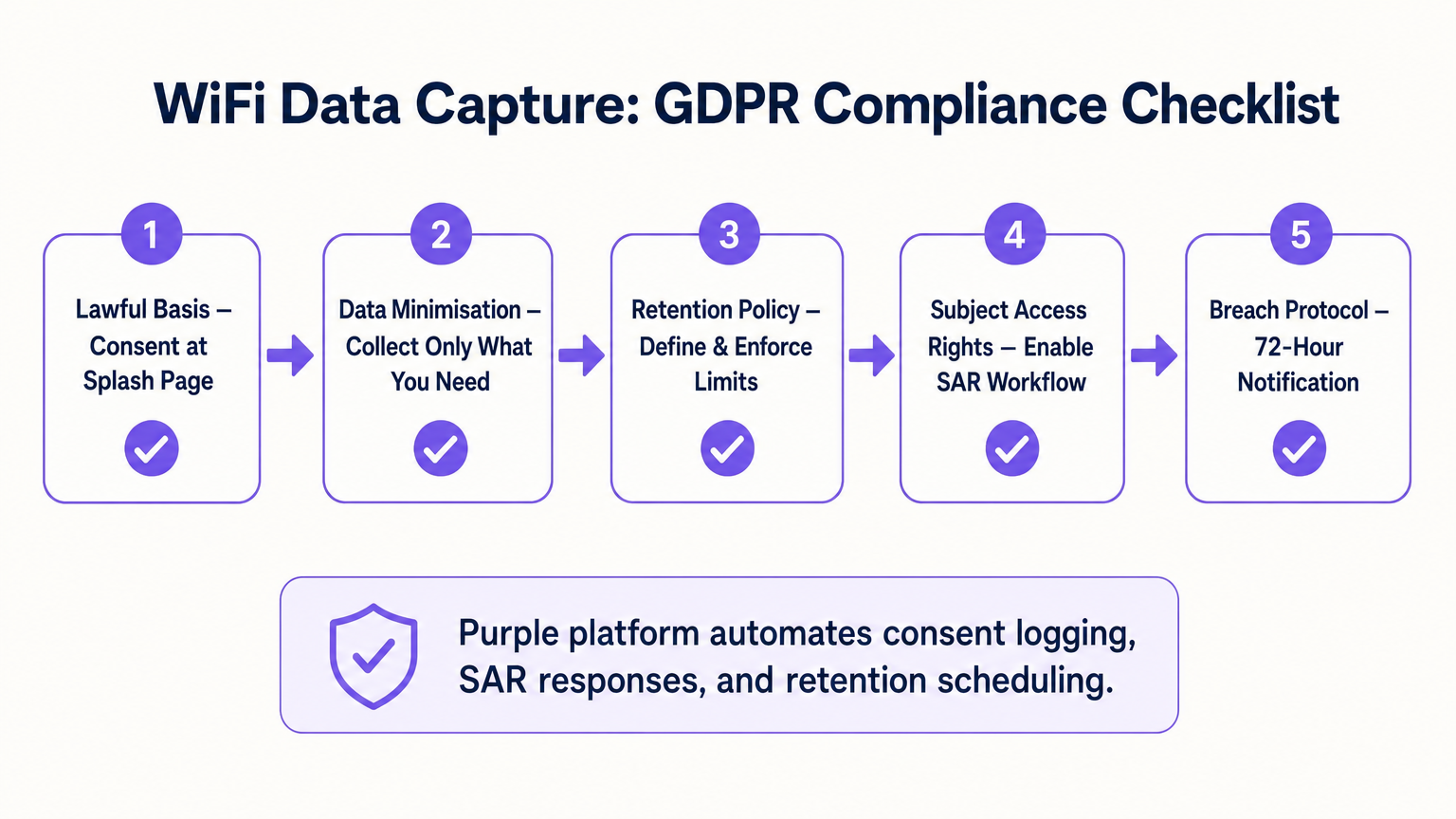
- Lawful Basis & Consent: Ensure the captive portal explicitly separates Terms of Service acceptance from Marketing Consent. Pre-ticked boxes are non-compliant under GDPR.
- Data Minimisation: Only collect data you have a commercial use case for. If you do not have an SMS marketing strategy, do not mandate phone number collection.
- Automated Retention: Configure the platform to automatically purge inactive profiles after a defined period (e.g., 24 months) to comply with storage limitation principles.
- Subject Access Requests (SAR): Ensure your platform has an automated workflow to export or delete a user's data within the statutory 30-day window upon request.
ROI & Business Impact
The ROI of a WiFi analytics platform is measured by its integration with the broader martech stack. By pushing identity, behavioural, and declared data via API into platforms like Salesforce or HubSpot, venues can trigger automated workflows. For example, a Transport hub can automatically email a lounge discount to a passenger whose dwell time exceeds 45 minutes. The ultimate business impact is the conversion of anonymous foot traffic into a marketable, segmented database.
Key Terms & Definitions
Captive Portal
A web page that a user of a public-access network is obliged to view and interact with before access is granted. It is the primary mechanism for capturing identity data and consent.
IT teams configure this to balance security, branding, and data capture requirements.
MAC Randomisation
A privacy feature in modern OSs (iOS, Android) where the device generates a temporary, random MAC address for each specific WiFi network it joins, preventing cross-network tracking.
This forces network architects to rely on authenticated user profiles rather than hardware identifiers for repeat visit tracking.
Dwell Time
The total duration a device remains continuously associated with the WiFi network or a specific zone within the network.
Used by operations and marketing to gauge engagement, queue lengths, or intent to purchase.
Progressive Profiling
The practice of collecting user data incrementally over multiple sessions rather than demanding all information during the initial interaction.
Crucial for maintaining high WiFi connection rates while still building rich customer profiles over time.
First-Party Data
Information a company collects directly from its customers and owns entirely, typically gathered via direct interactions like WiFi authentication.
Highly valuable as third-party cookies deprecate; it provides the most accurate and compliant foundation for marketing.
Received Signal Strength Indicator (RSSI)
A measurement of the power present in a received radio signal. Used in WiFi analytics to estimate the distance between a device and an access point.
The technical metric underlying zone-level movement tracking and indoor positioning.
Subject Access Request (SAR)
A mechanism under GDPR allowing individuals to request a copy of their personal data, or request its deletion.
IT must ensure the WiFi platform can easily query and export or purge specific user records to meet the 30-day compliance window.
Data Minimisation
The principle that a data controller should limit the collection of personal information to what is directly relevant and necessary to accomplish a specified purpose.
A core compliance requirement; prevents venues from hoarding unnecessary data that increases breach liability.
Case Studies
A 200-room hotel needs to increase direct bookings and reduce OTA (Online Travel Agency) commissions. They currently offer open, unauthenticated WiFi.
The hotel deploys a captive portal requiring email or social authentication. They implement progressive profiling: on the first connection, they capture email and marketing consent. On the third connection during the stay, a micro-survey captures the reason for travel (Business/Leisure). Post-checkout, the CRM uses the WiFi identity data to send a targeted 'Book Direct' offer for their next stay, bypassing the OTA.
A large retail chain wants to measure the impact of a new store layout on customer engagement, but their current WiFi only tracks total daily connections.
The IT team upgrades the network to support zone-level analytics by calibrating multiple access points. They define virtual zones within the analytics platform corresponding to key departments. They can now measure not just presence, but 'Zone Dwell Time'. By comparing dwell times in the newly laid-out zones against historical benchmarks, they quantify the layout's impact on engagement.
Scenario Analysis
Q1. Your marketing team wants to track how often specific customers return to your stadium over a season. The current network uses open access (no portal) and tracks MAC addresses. Why will this fail, and what must you change?
💡 Hint:Consider recent changes in mobile operating system privacy features.
Show Recommended Approach
It will fail due to MAC randomisation; modern devices present a different MAC address on subsequent visits, breaking the tracking. You must implement a captive portal to force authentication (e.g., via email or ticketing integration) and anchor the repeat visit tracking to that persistent user credential rather than the hardware MAC.
Q2. A venue director requests that the new WiFi splash page collects Name, Email, Phone, Date of Birth, Postcode, and Dietary Preferences to build a comprehensive CRM database immediately. How should the IT architect respond?
💡 Hint:Balance data yield against the user experience and connection drop-off rates.
Show Recommended Approach
The architect should advise against this due to the Friction vs. Yield trade-off. A 6-field form will cause massive connection abandonment. Instead, recommend progressive profiling: capture Name and Email on the first visit, and use subsequent visits to prompt for Phone or Dietary Preferences. Furthermore, under data minimisation principles, Date of Birth should not be collected unless there is a strict legal requirement (e.g., age-gated venues).
Q3. During a security audit, the compliance team asks how the WiFi platform proves that a user opted into marketing communications. What specific data points must the system be able to produce?
💡 Hint:Think about the requirements of GDPR Article 7 regarding the demonstration of consent.
Show Recommended Approach
The system must produce a definitive audit trail for that specific user. This includes the timestamp of the consent action, the IP address and MAC address used during the session, the exact version of the Terms & Conditions/Privacy Policy presented at that time, and the specific checkbox (which must have been actively opted-in, not pre-ticked) that the user interacted with.



