Technical Guides
Deep, expert-led technical guides on guest WiFi, analytics, captive portals, and venue technology.
357 guides
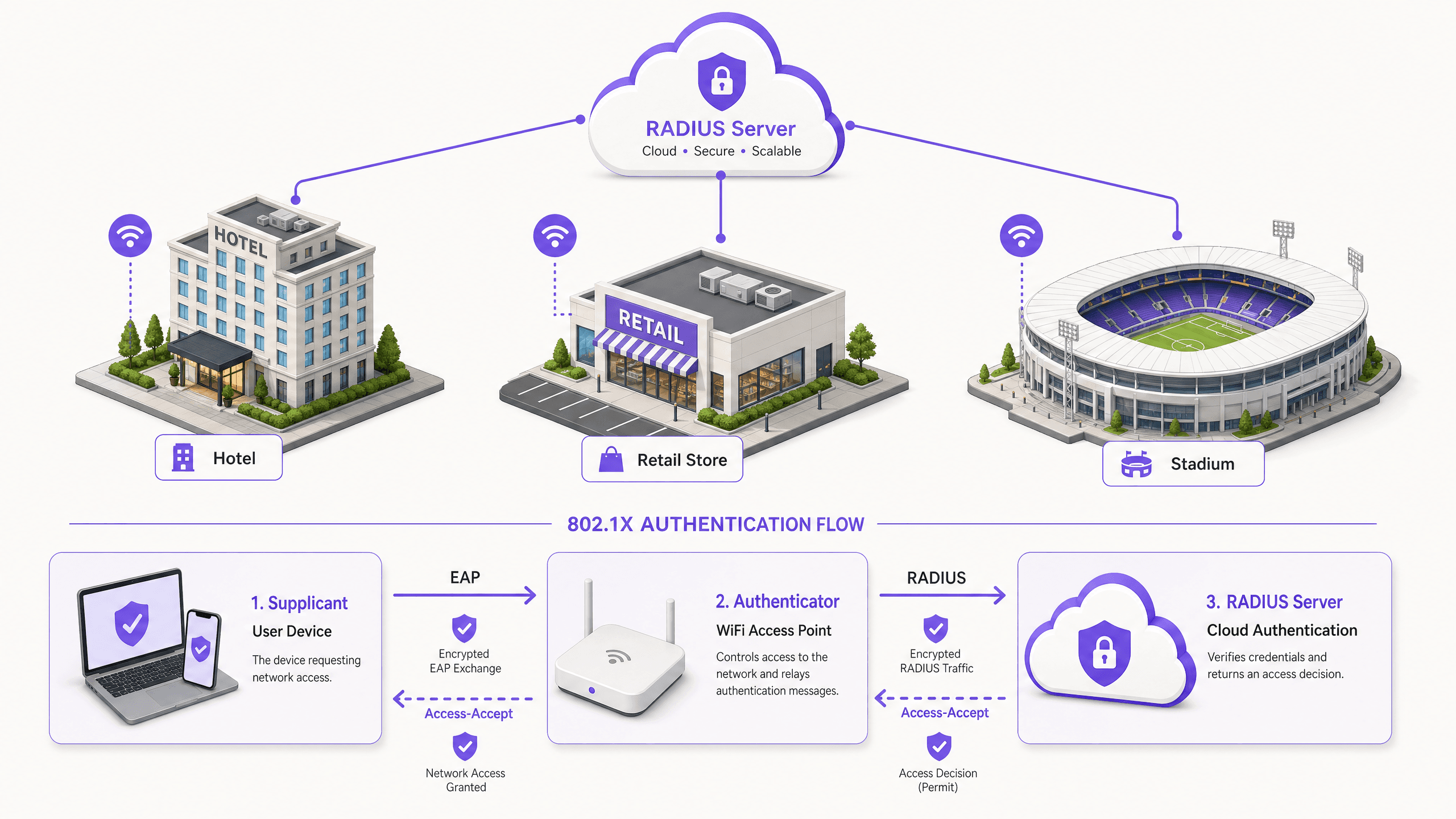
How to Implement 802.1X Authentication with Cloud RADIUS
This technical reference guide provides a comprehensive framework for implementing 802.1X authentication with Cloud RADIUS across distributed enterprise estates. It details the architecture, EAP method selection, deployment sequencing, and risk mitigation strategies required to secure network access while eliminating the operational overhead of on-premises infrastructure.
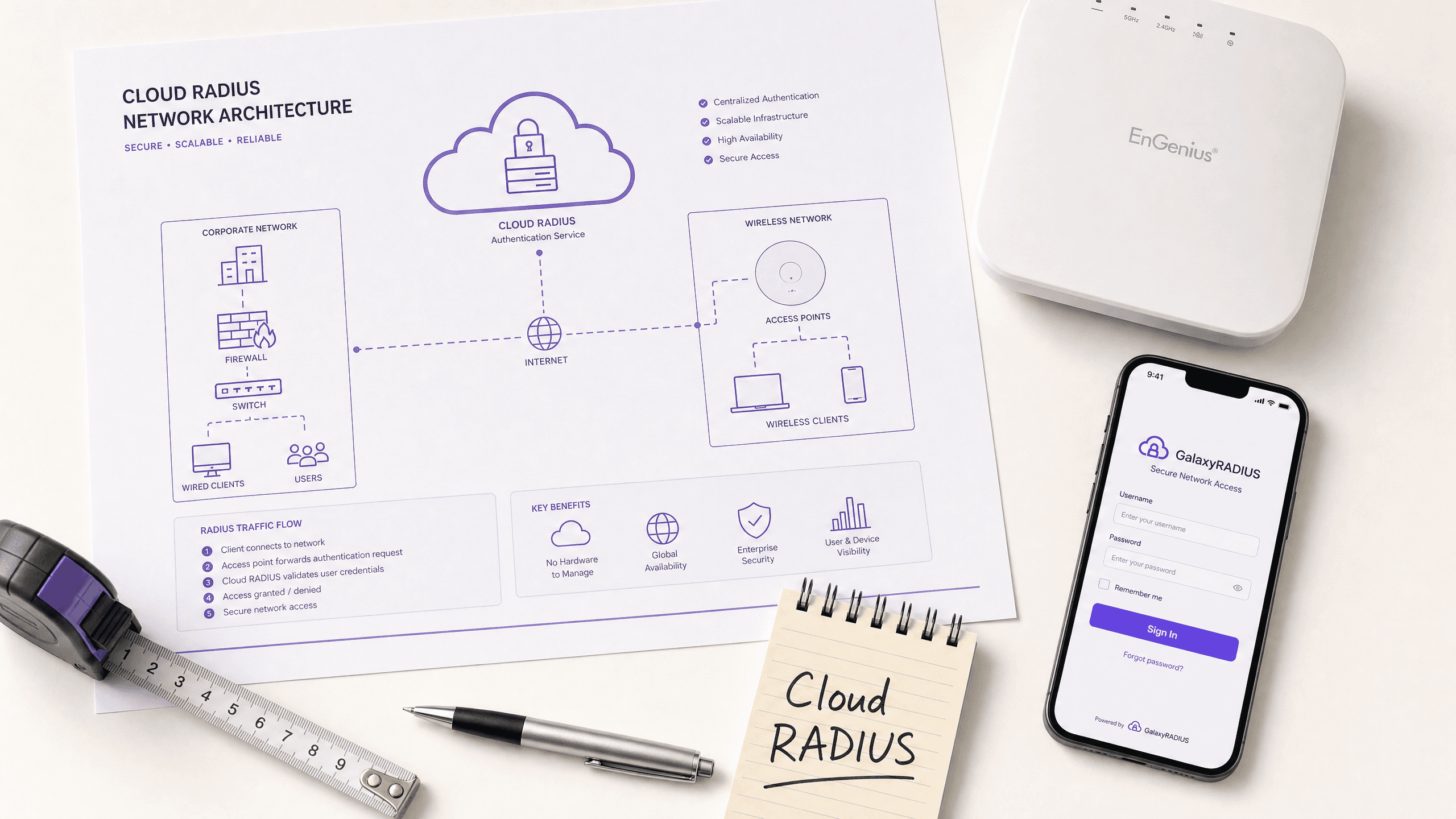
What is Cloud RADIUS? A Comprehensive Guide to RADIUS as a Service
This comprehensive guide explores Cloud RADIUS (RADIUS as a Service), detailing its architecture, EAP methods, and implementation strategies. It provides IT leaders with actionable insights on migrating from on-premise servers to a scalable, secure, and compliant cloud-based authentication model.
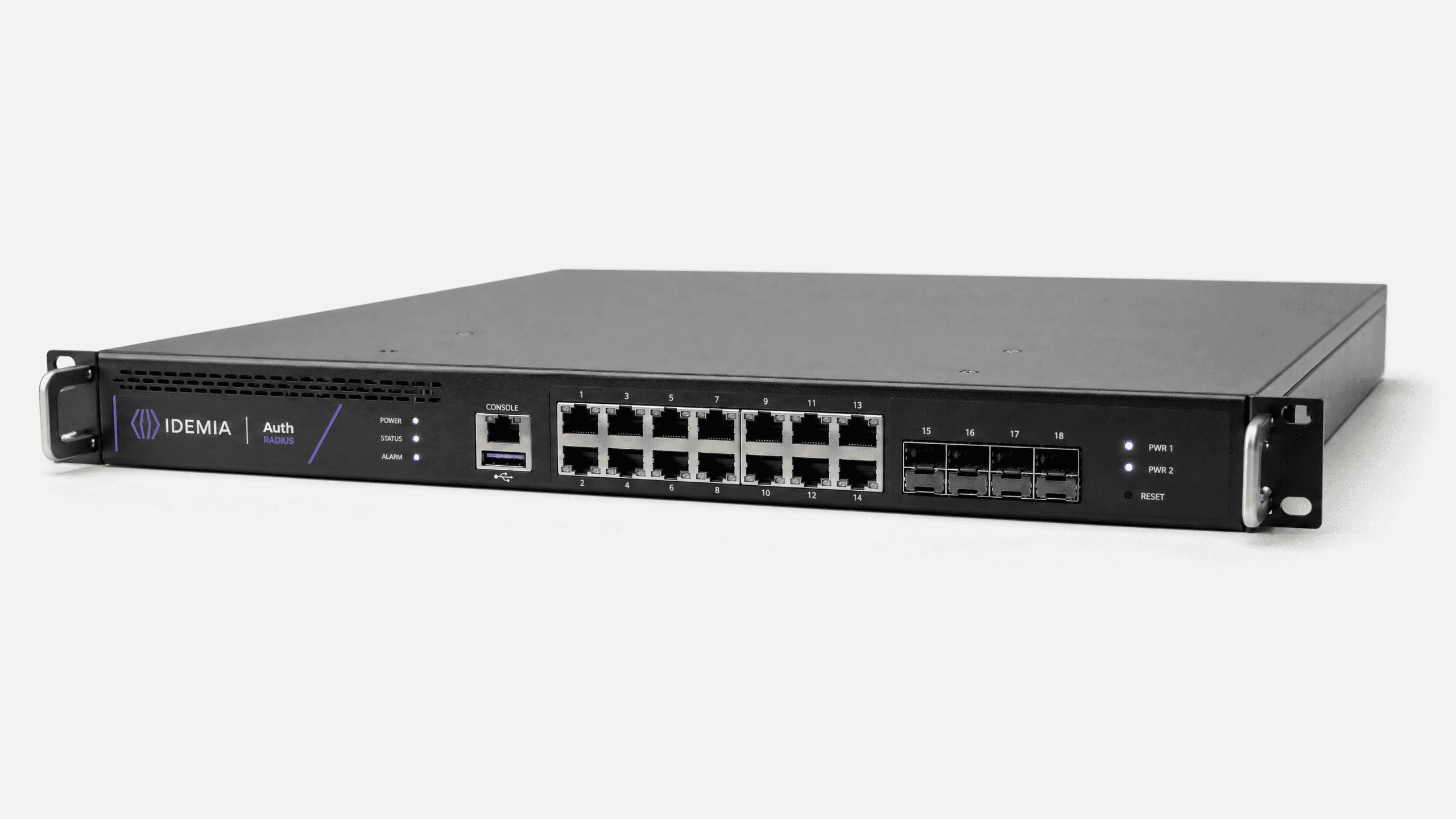
Migrating from On-Premises RADIUS (NPS) to RADIUS as a Service
This authoritative guide details the technical architecture, implementation methodology, and business impact of migrating from on-premises Microsoft Network Policy Server (NPS) to a cloud-native RADIUS as a Service model. It provides IT leaders and network architects with practical frameworks to reduce operational overhead, eliminate single points of failure, and secure enterprise authentication across distributed venues.
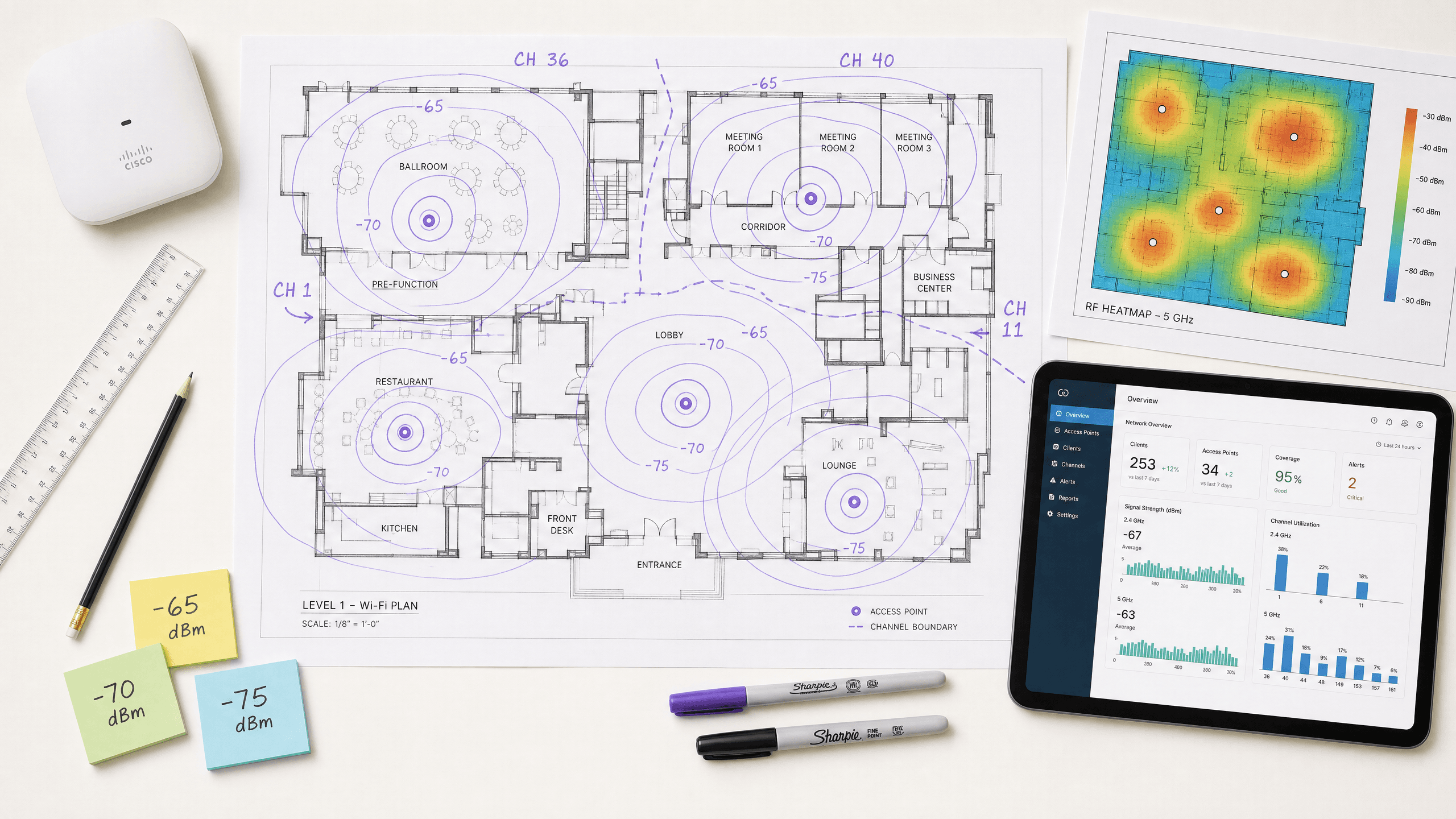
Understanding RSSI and Signal Strength for Optimum Channel Planning
This guide provides a comprehensive technical deep-dive into RSSI, Signal-to-Noise Ratio (SNR), and RF propagation principles for optimum channel planning. It equips IT managers, network architects, and venue operations directors with actionable strategies to mitigate Co-Channel and Adjacent Channel Interference, optimise AP placement, and leverage analytics for measurable business impact across hospitality, retail, and public sector environments.
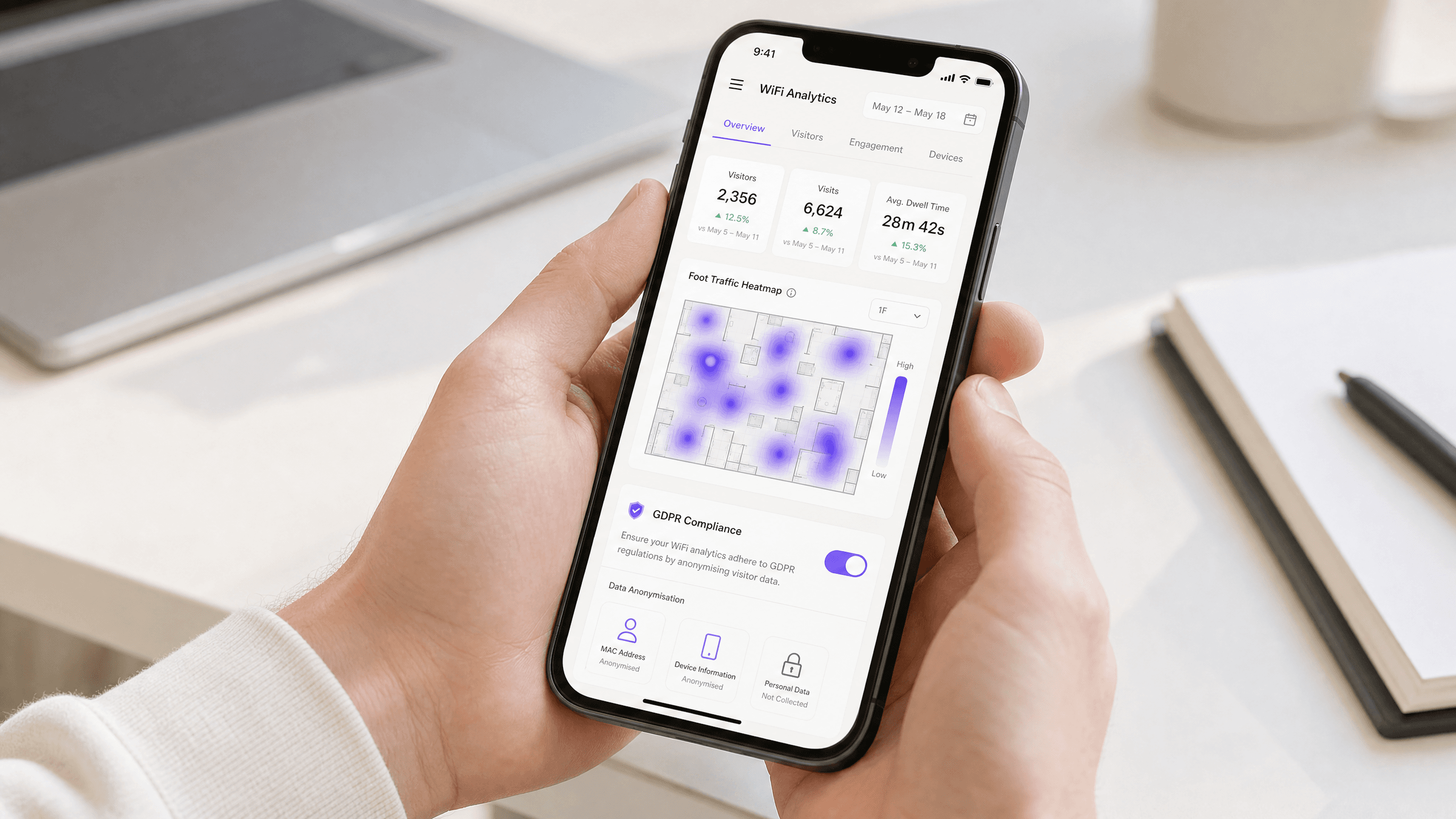
Privacy by Design: Anonymising WiFi Data for GDPR Compliance
This authoritative guide details the technical architecture and implementation strategies for anonymising WiFi data to ensure GDPR compliance. It provides IT leaders and network architects with actionable frameworks for balancing robust venue analytics with strict data privacy requirements.
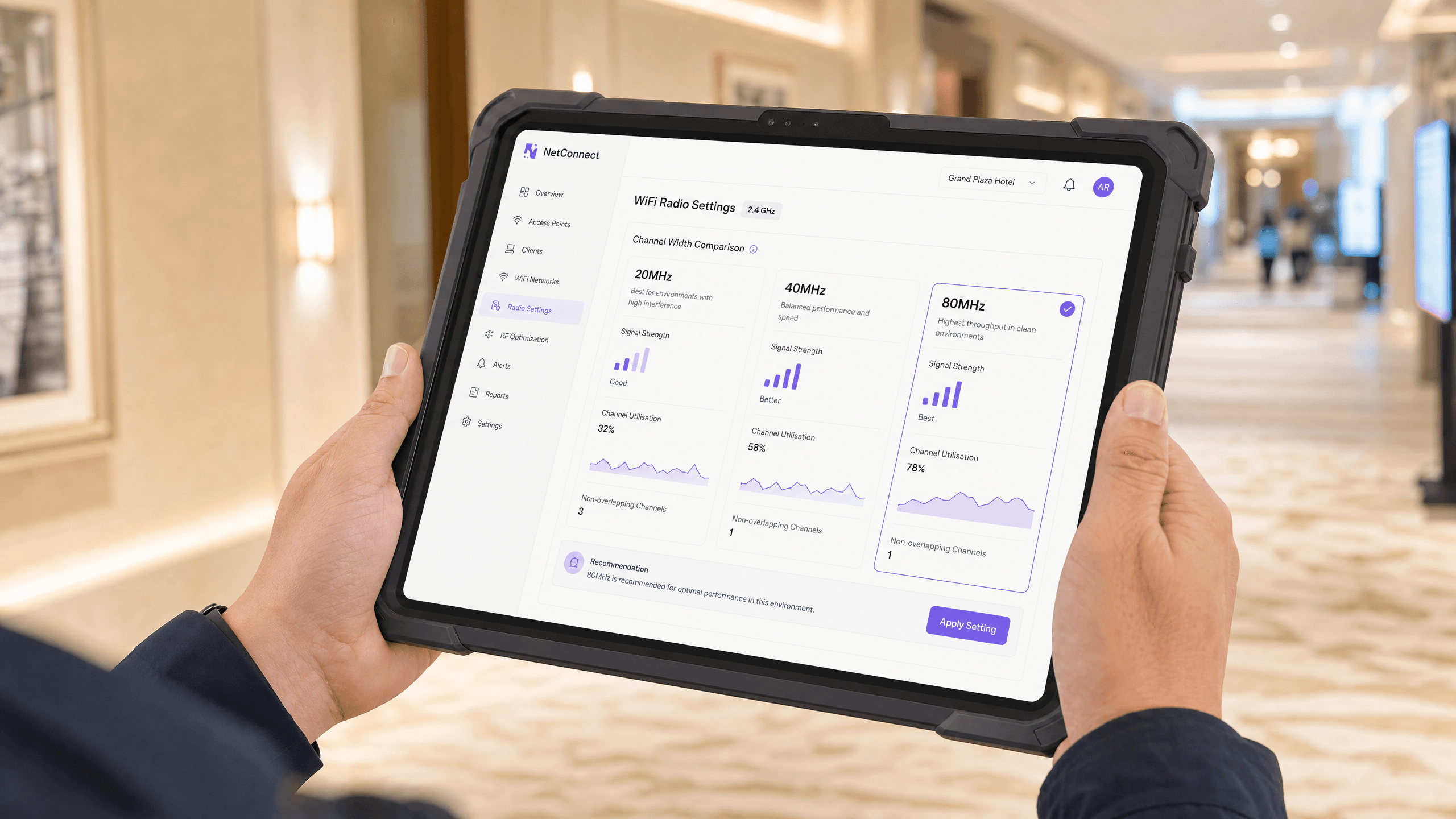
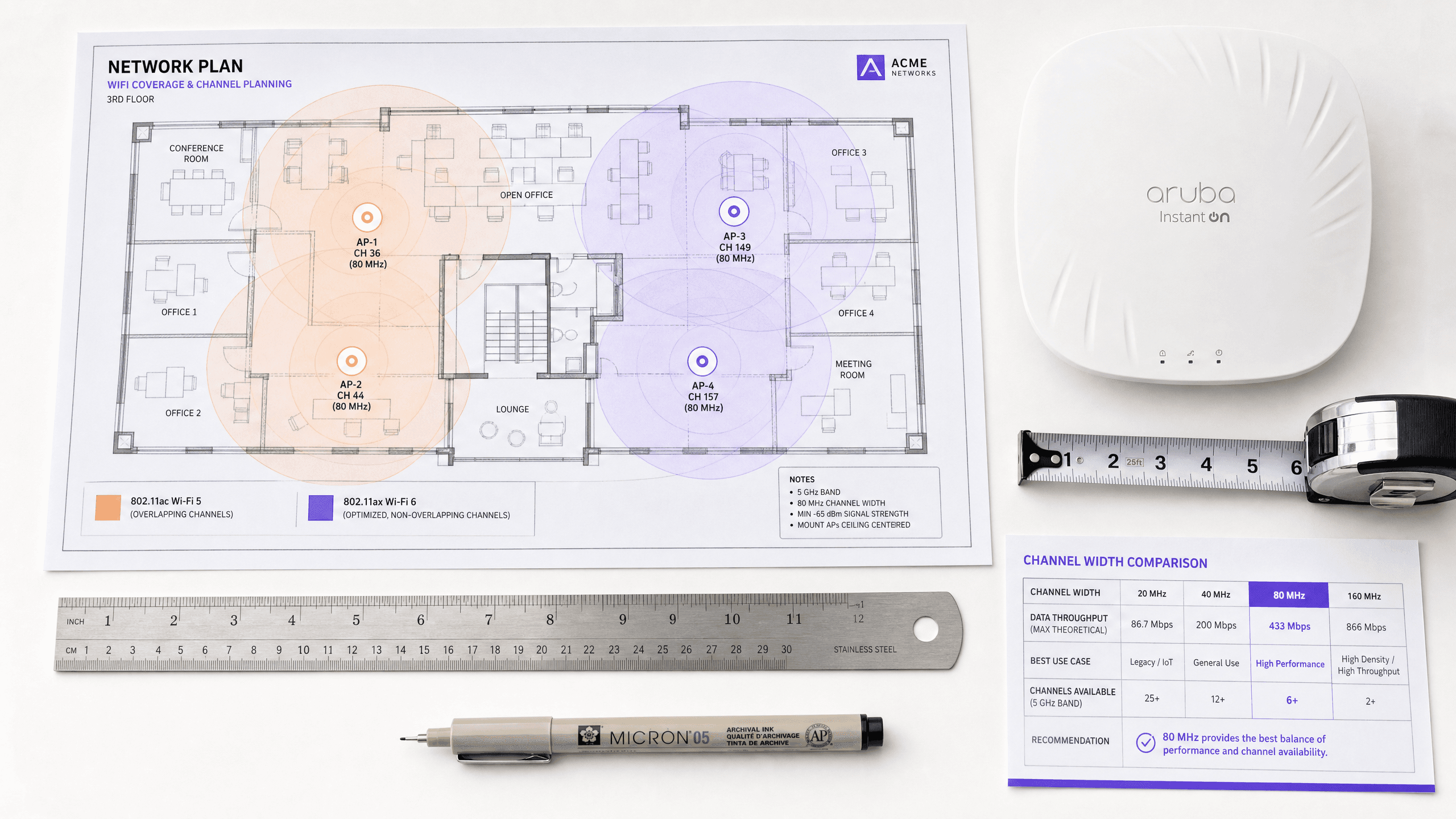
20MHz vs 40MHz vs 80MHz: Which Channel Width Should You Use?
This guide provides a definitive, vendor-neutral technical reference for IT managers, network architects, and venue operations directors on selecting the correct WiFi channel width — 20MHz, 40MHz, or 80MHz — across enterprise deployments in hospitality, retail, events, and public sector environments. It covers the underlying IEEE 802.11 mechanics, real-world capacity trade-offs, and step-by-step deployment guidance to help teams make the right call this quarter. Understanding channel width selection is one of the highest-impact decisions in any wireless LAN design, directly impacting throughput, interference, client density support, and the reliability of guest-facing services.
What is a WLC (Wireless LAN Controller) and Do You Still Need One?
This comprehensive guide explores the evolution of Wireless LAN Controllers (WLCs) and provides a technical framework for determining the right architecture in 2026. It covers traditional hardware, cloud-managed, and controller-less models, detailing their impact on compliance, scalability, and guest experience.

Power over Ethernet (PoE) for Access Points: An Implementation Guide
This guide provides infrastructure technicians, network architects, and IT decision-makers with a definitive technical reference for deploying Power over Ethernet (PoE) access points across enterprise venues including hotels, retail estates, stadiums, and public-sector facilities. It covers IEEE standards from 802.3af through 802.3bt, power budget calculation, cabling requirements, VLAN segmentation, and security compliance, with concrete implementation scenarios and measurable ROI benchmarks. Understanding PoE architecture is foundational to any [Guest WiFi](/guest-wifi) or [WiFi Analytics](/guest-wifi-marketing-analytics-platform) deployment, as the reliability of the physical layer directly determines the quality of data capture, user experience, and operational uptime.

Mesh Network vs Access Points: Which is Better for Large Venues?
This technical guide provides a definitive comparison between mesh networks and traditional wired access points for large-scale venues, covering architecture, performance trade-offs, and deployment strategy. It equips IT managers, network architects, and CTOs with actionable frameworks to design high-performance, compliant WiFi infrastructures for hospitality, retail, events, and public-sector environments. The guide also maps these architectural decisions to Purple's hardware-agnostic guest WiFi and analytics platform, demonstrating how the right infrastructure choice drives measurable business outcomes.

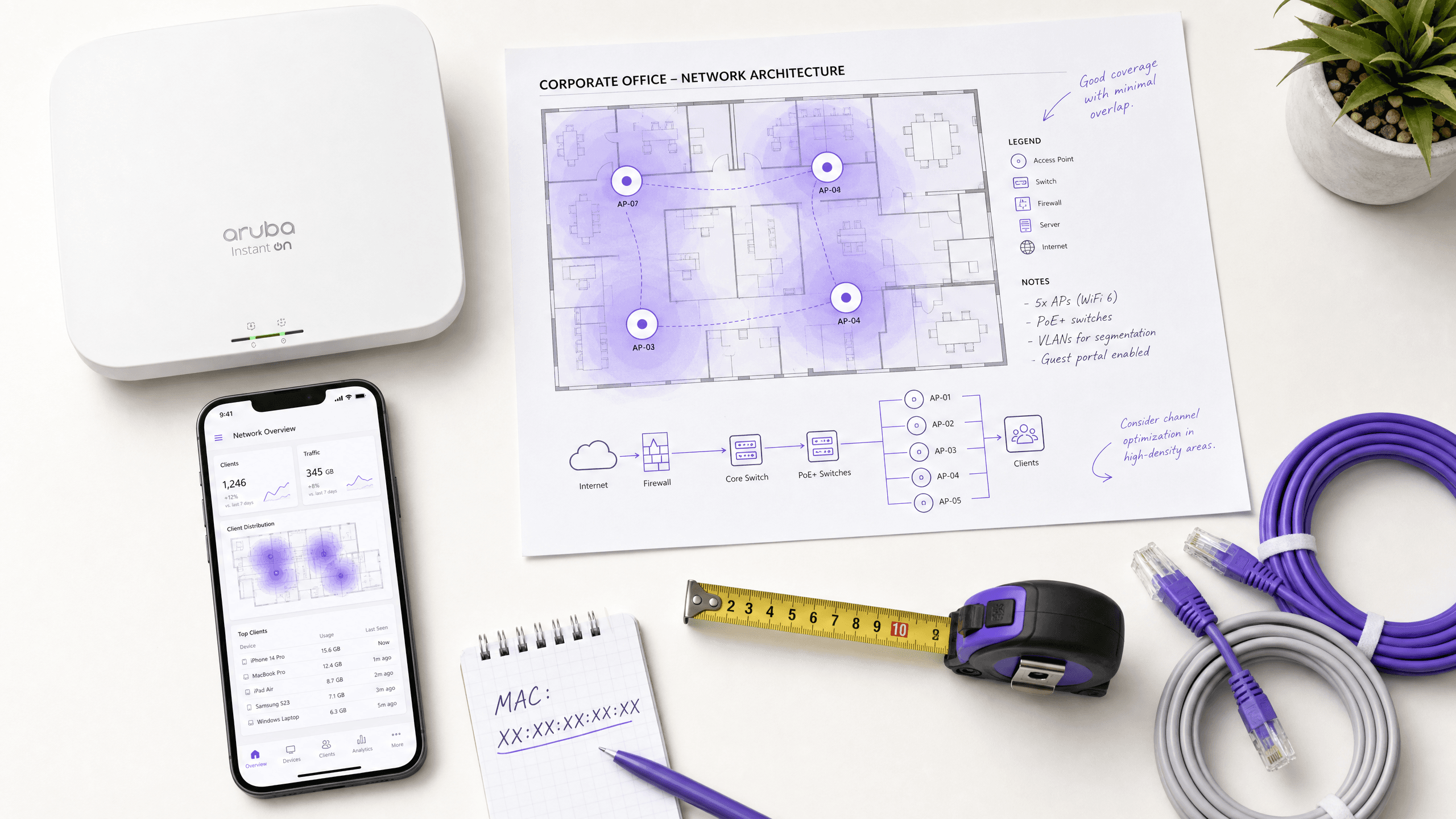
The Best Wi-Fi Access Points for Enterprise and Homelabs
This technical guide evaluates the best enterprise Wi-Fi access points for 2025-2026, covering Wi-Fi 6E and Wi-Fi 7 hardware from Cisco, HPE Aruba, Ruckus, Juniper Mist, and Ubiquiti across high-density hospitality, retail, and public venue deployments. It provides actionable architecture strategies, vendor comparisons, security frameworks, and ROI metrics for IT leaders building next-generation wireless networks. Purple's hardware-agnostic guest WiFi and analytics platform is mapped throughout as the intelligence layer that transforms network infrastructure into a first-party data asset.

Cisco Meraki vs. Aruba: A Technical Comparison for Guest WiFi
An authoritative technical comparison of Cisco Meraki and HPE Aruba for enterprise guest WiFi deployments. This guide provides actionable insights for IT managers and architects on architecture, authentication, network segmentation, and hardware-agnostic analytics integration.

Comparing Controller-Based v. Cloud-Managed Access Points
This technical reference guide compares controller-based and cloud-managed Access Point architectures for enterprise environments. It provides IT leaders with a vendor-neutral framework for assessing deployment models, total cost of ownership, and integration capabilities with guest intelligence platforms like Purple.

Access Point vs. Router: A Guide for Commercial Networking
This comprehensive guide explores the technical distinctions between access points and routers, providing actionable deployment strategies for commercial environments. It equips IT managers and venue operators with the knowledge required to architect scalable, secure, and high-performance wireless networks.

WiFi Repeater v. Extender: Enterprise Use Cases
This technical reference guide provides a definitive comparison between WiFi repeaters and extenders for enterprise environments. It equips IT managers and network architects with the decision frameworks needed to deploy the correct hardware for specific venue requirements, ensuring optimal performance, compliance, and ROI.
Heatmapping vs Presence Analytics: Technical Differences
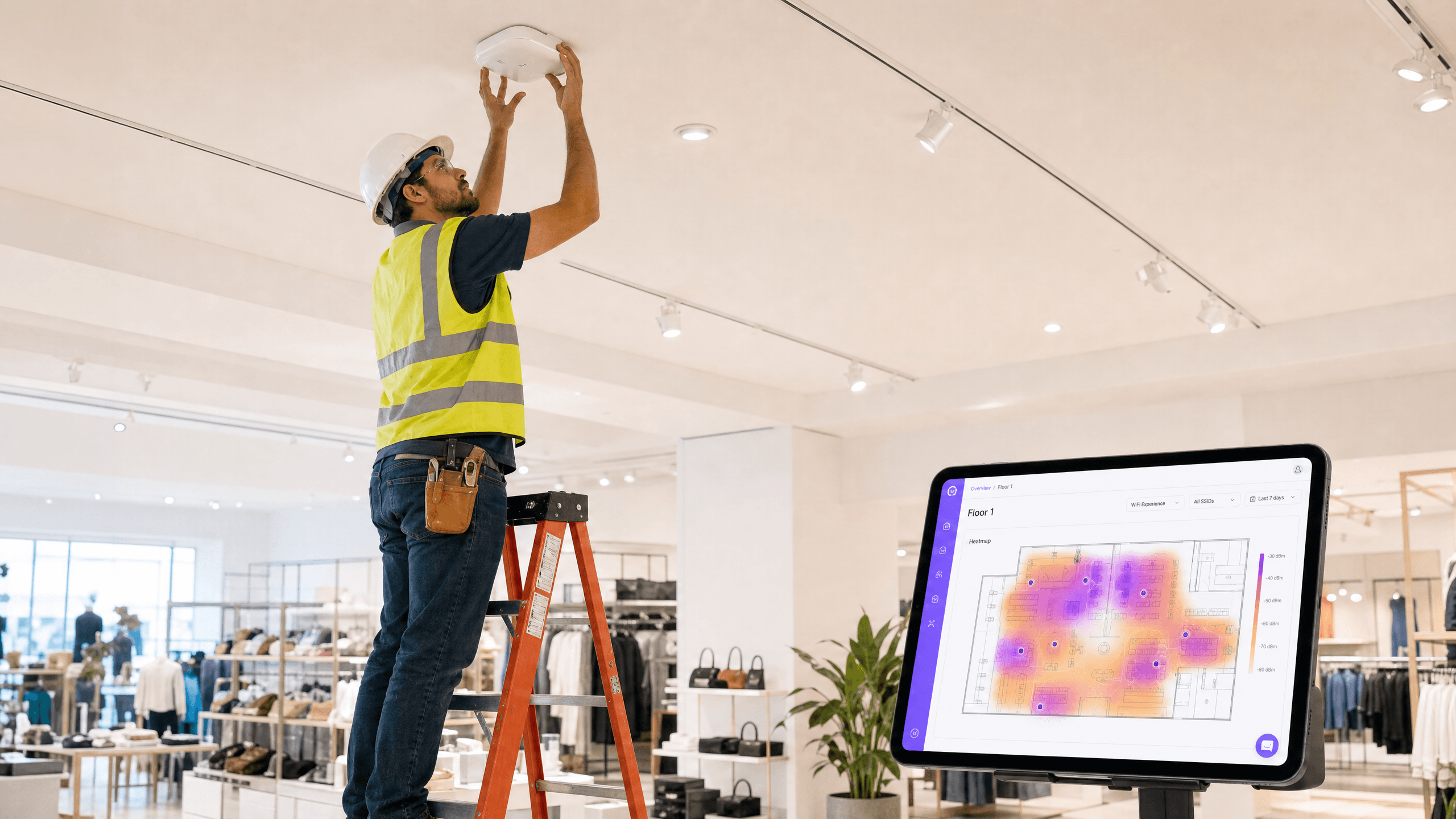
This authoritative technical guide details the critical architectural and operational differences between WiFi heatmapping and presence analytics for enterprise venue operators. It provides IT leaders, network architects, and operations directors with actionable deployment frameworks, real-world implementation scenarios, and vendor-neutral best practices for extracting maximum ROI from their existing wireless infrastructure.
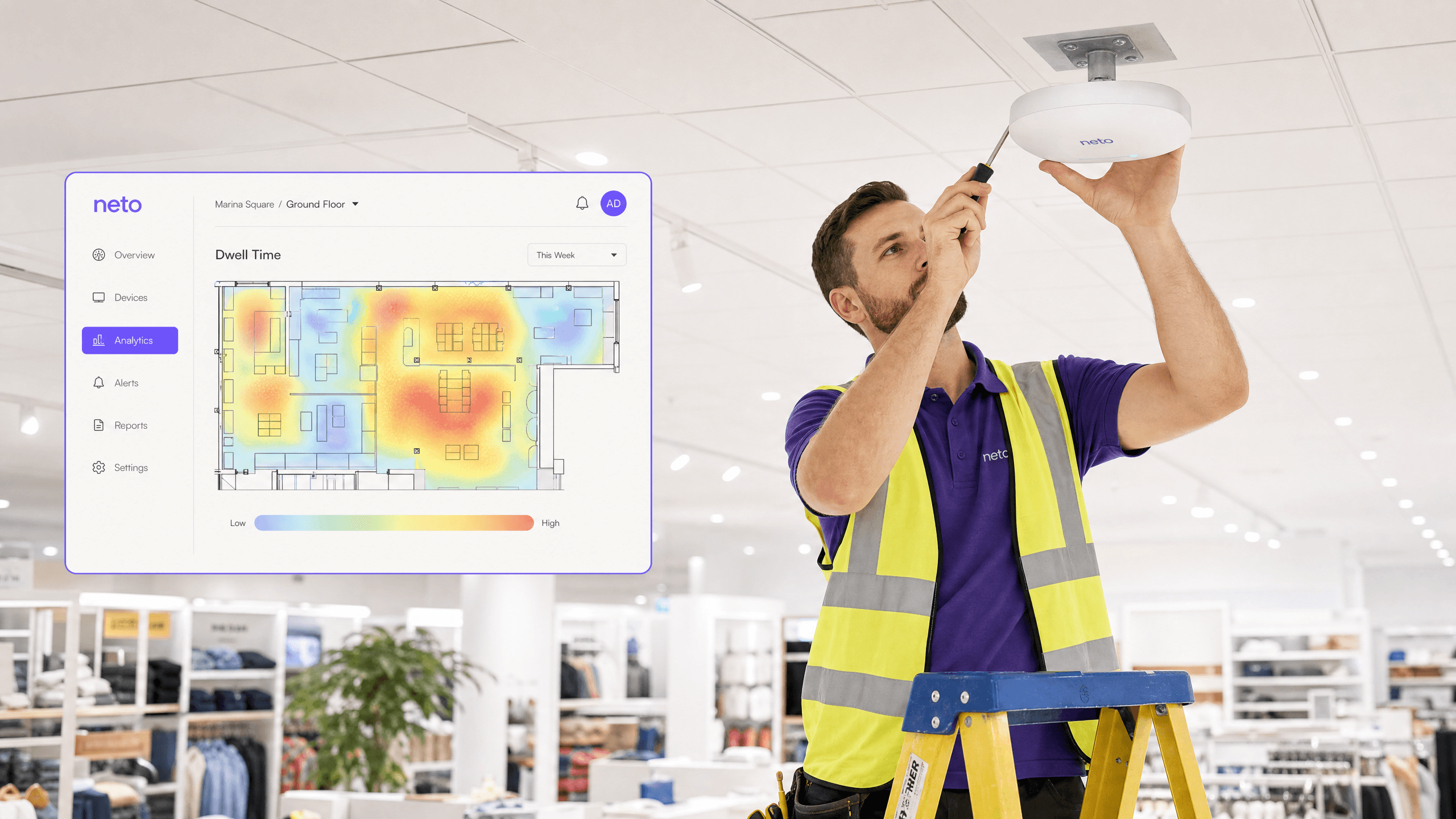
How to Calculate Dwell Time Using WiFi Location Analytics
This guide provides a comprehensive technical reference for calculating WiFi dwell time using WiFi location analytics, covering the full architecture from 802.11 probe request capture through RSSI-based trilateration to geofenced zone analysis. It is designed for IT managers, network architects, and venue operations directors who need to deploy accurate, scalable location intelligence across retail, hospitality, healthcare, and public sector environments. Readers will gain actionable implementation guidance, real-world case studies, and a clear framework for translating raw spatial data into measurable business outcomes.

What is a Probe Request? Understanding How Devices Discover Networks
This technical reference guide provides a deep-dive into IEEE 802.11 probe requests, active versus passive scanning, and the impact of MAC randomisation on venue analytics. It delivers actionable implementation strategies for network architects to optimise high-density deployments, mitigate probe storms, and ensure accurate, GDPR-compliant data collection using authenticated identity layers.
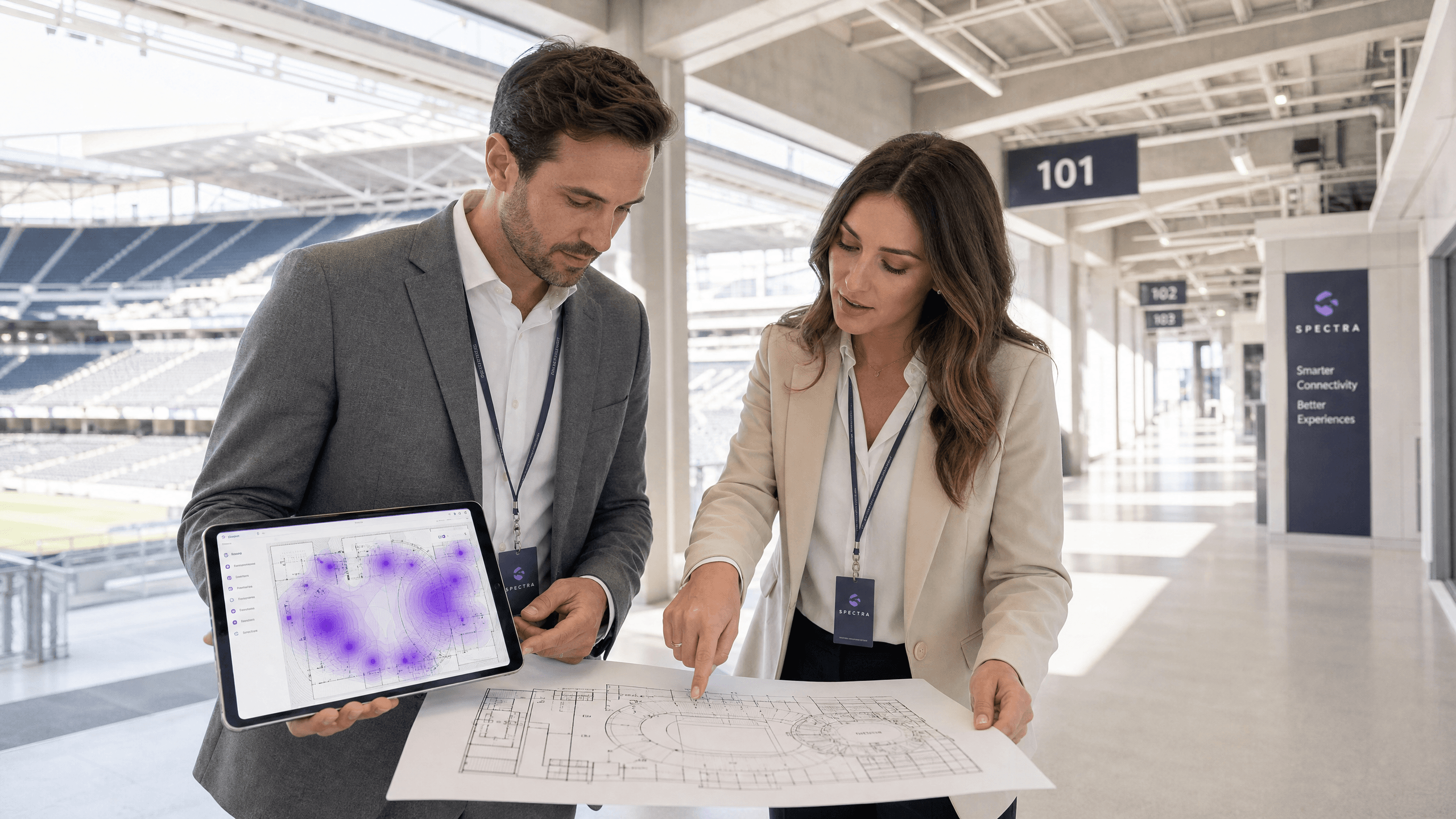
The Mechanics of WiFi Wayfinding: Trilateration and RSSI Explained
This authoritative guide details the technical mechanics of WiFi wayfinding, explaining how trilateration and RSSI measurements determine device location. It provides actionable deployment strategies, calibration methodologies, and architectural best practices for IT leaders deploying location services in enterprise venues.

How to Track Unique Devices on Enterprise Wireless Networks
This guide provides a comprehensive technical overview of tracking unique devices across enterprise wireless networks. It addresses modern challenges like MAC randomisation and details implementation strategies for venue operators and IT teams to maintain accurate analytics and user identification.
Wi-Fi 6 vs Wi-Fi 5: Does it Solve Channel Interference?
This guide provides a technical deep-dive into how Wi-Fi 6 (802.11ax) addresses channel interference in high-density enterprise environments through OFDMA and BSS Coloring. It equips IT managers, network architects, and CTOs with actionable deployment strategies, real-world case studies from hospitality and healthcare, and a framework for evaluating the ROI of infrastructure upgrades in venues where wireless performance is business-critical.
How MAC Address Randomization Affects Guest WiFi Analytics
This guide provides a technical deep-dive into how MAC address randomization impacts guest WiFi analytics. It offers practical strategies for IT leaders and network architects to restore visibility, ensure accurate metrics, and maintain compliance across large-scale deployments. Covering the mechanics of per-network and ephemeral randomization, identity resolution architecture, and real-world deployment scenarios, this is the definitive reference for any organisation relying on WiFi-derived spatial data.
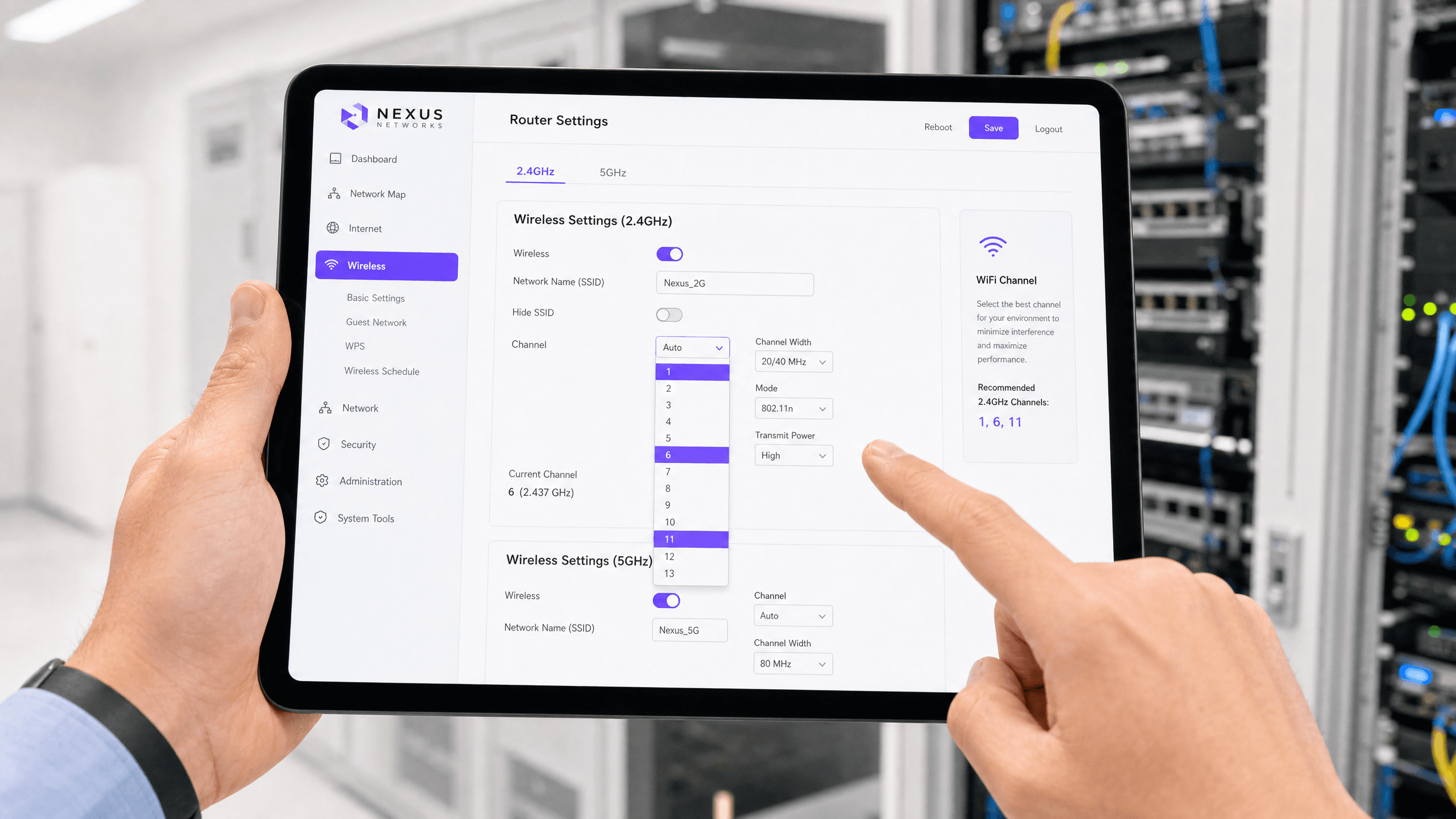
How to Change Your Router's Default Channel
This authoritative technical reference guide provides IT managers and network architects with actionable strategies for configuring WiFi channels to mitigate interference, maximise throughput, and ensure a stable RF foundation for enterprise applications like Purple Guest WiFi and Analytics.

DFS Channels: What They Are and When to Avoid Them
This authoritative guide breaks down the technical and operational realities of Dynamic Frequency Selection (DFS) channels in the 5 GHz band. Venue operators and IT teams will learn how to assess radar risk, configure Channel Availability Checks (CAC), and deploy robust fallback plans to protect high-density wireless environments from sudden connectivity drops.
How to Fix Slow WiFi Without Upgrading Your Internet Plan
A comprehensive technical reference guide for IT managers and network architects on optimising enterprise WiFi performance without increasing ISP bandwidth. Covers RF tuning, client density management, QoS implementation, and how to leverage WiFi analytics to diagnose and resolve bottlenecks.