HTTPS Captive Portals in 2026: Why HSTS and Browser Hardening Are Breaking the Old Patterns
This guide details how HSTS and browser HTTPS-first policies are breaking legacy HTTP-intercept captive portals in 2026. It provides actionable technical guidance for network architects to implement modern alternatives, including the CAPPORT API and Passpoint (Hotspot 2.0), ensuring secure and reliable guest WiFi access.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: Why HSTS Breaks the Intercept Pattern
- The HSTS Preload Problem
- Browser Hardening: HTTPS-First Mode
- Modern Alternatives: CAPPORT and Passpoint
- 1. The CAPPORT API (RFC 8908 and RFC 8910)
- 2. Passpoint (Hotspot 2.0) and OpenRoaming
- Implementation Guide
- Phase 1: Stabilise Existing Portals with CAPPORT
- Phase 2: Deploy Passpoint for Secure, Seamless Access
- Phase 3: The Hybrid Progressive Onboarding Model
- Best Practices
- Troubleshooting & Risk Mitigation
- ROI & Business Impact

Executive Summary
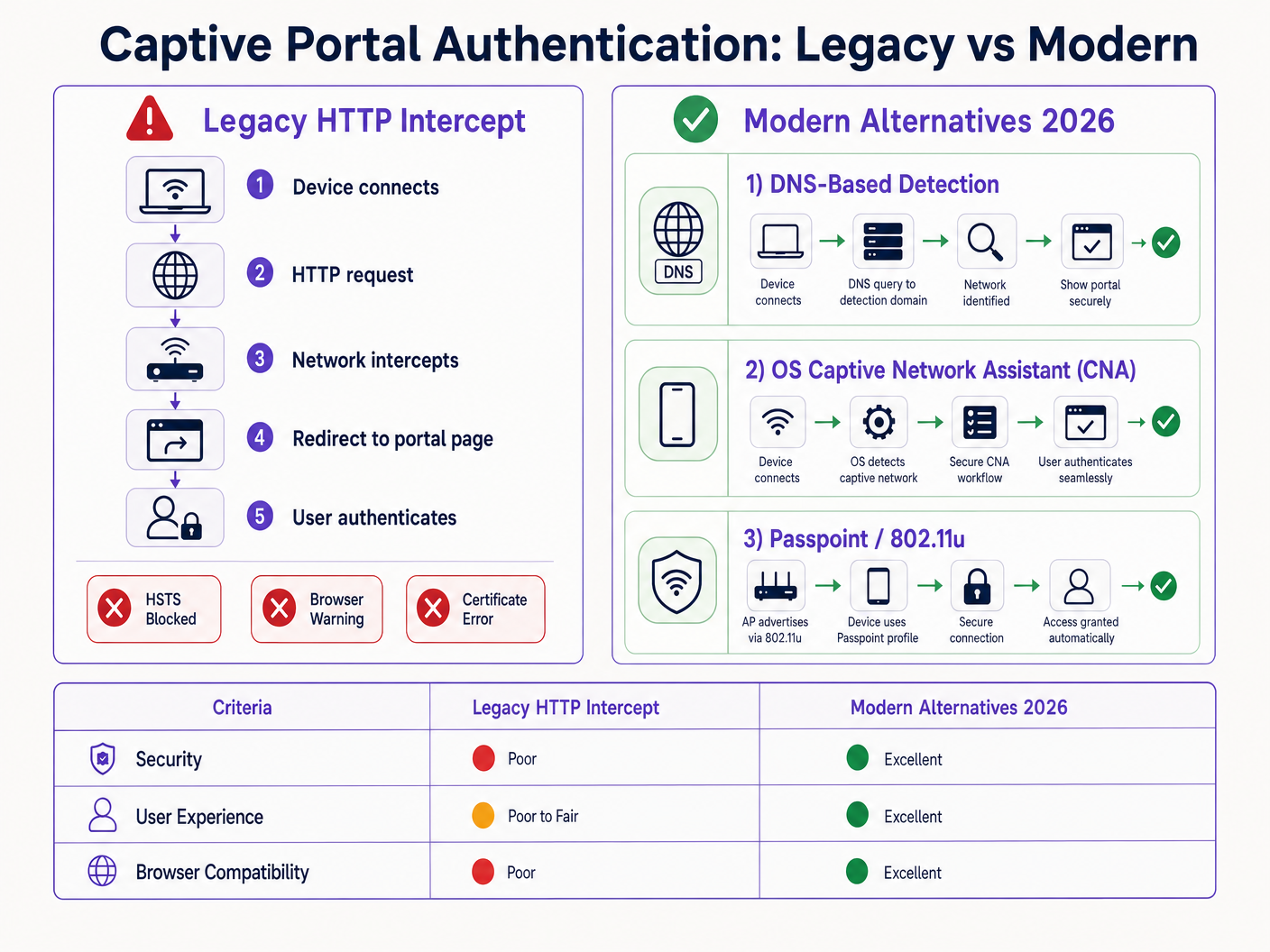
The legacy captive portal pattern—intercepting HTTP traffic and issuing a 302 redirect—is dead. Driven by HTTP Strict Transport Security (HSTS) and aggressive browser hardening, the traditional 'intercept and redirect' mechanism is failing at scale across Hospitality , Retail , and enterprise environments. As of 2026, with Chrome enforcing HTTPS-first behaviour by default and the HSTS preload list exceeding 100,000 domains, network controllers can no longer rely on unencrypted HTTP requests to trigger portal detection.
For IT managers and network architects, this represents a critical architectural shift. Maintaining seamless Guest WiFi access now requires modernising your onboarding flow. This guide details the technical mechanisms breaking legacy portals and outlines the vendor-neutral implementation path forward: deploying the CAPPORT API (RFC 8908/8910) for immediate stability, and migrating to Passpoint (Hotspot 2.0) and OpenRoaming for secure, zero-touch connectivity.
Technical Deep-Dive: Why HSTS Breaks the Intercept Pattern
The traditional captive portal relies on a fundamental assumption: the client device will make an unencrypted HTTP request on port 80 that the network access server (NAS) or controller can intercept and redirect to the portal's splash page.
This assumption is no longer valid.
The HSTS Preload Problem
HTTP Strict Transport Security (HSTS), defined in RFC 6797, allows a web server to declare that web browsers should only interact with it using secure HTTPS connections. When a user attempts to access an HSTS-protected domain via HTTP, the browser internally upgrades the request to HTTPS before any network traffic is sent.
Because the request is encrypted, the network controller cannot inspect the host header or issue an HTTP 302 redirect. Instead, the controller intercepts the HTTPS traffic and presents its own portal certificate. Since this certificate does not match the requested domain (e.g., google.com), the browser throws a fatal NET::ERR_CERT_AUTHORITY_INVALID error. The user is blocked, and the portal never loads.
The HSTS Preload list exacerbates this issue. Browsers hardcode a list of domains that must always be accessed via HTTPS, even on the first visit. In 2026, this list includes virtually all major consumer destinations. When a guest connects to your network and types a common URL, the browser forces HTTPS, triggering the certificate error and breaking the captive portal flow.
Browser Hardening: HTTPS-First Mode
Beyond HSTS, browser vendors have systematically hardened their default behaviours. In late 2025, Google announced that Chrome 154 (released in October 2026) would enable "Always Use Secure Connections" by default for all users on public sites. Safari and Firefox have implemented similar HTTPS-first modes.
This means that even for domains not on the HSTS preload list, the browser will attempt an HTTPS connection first. The HTTP intercept pattern is effectively obsolete.
Modern Alternatives: CAPPORT and Passpoint
To restore functionality and improve the user experience, network architects must transition to modern captive portal detection mechanisms and authentication frameworks.
1. The CAPPORT API (RFC 8908 and RFC 8910)
The Internet Engineering Task Force (IETF) addressed the captive portal detection problem with the CAPPORT architecture. Instead of relying on intercepted web traffic, CAPPORT provides an explicit signalling mechanism.
- RFC 8910 (Captive-Portal Identification): The network uses DHCP (Option 114) or IPv6 Router Advertisements to provide the client device with the URI of the captive portal API.
- RFC 8908 (Captive Portal API): The client queries the provided URI (a JSON endpoint) to determine if it is captive and to obtain the URL of the user-facing portal page.
When implemented, the client OS (iOS, Android, Windows) natively detects the portal before the user opens a browser. The OS launches its Captive Network Assistant (CNA) and loads the portal URL directly over a secure HTTPS connection. This eliminates the need for HTTP interception and avoids certificate errors.
2. Passpoint (Hotspot 2.0) and OpenRoaming
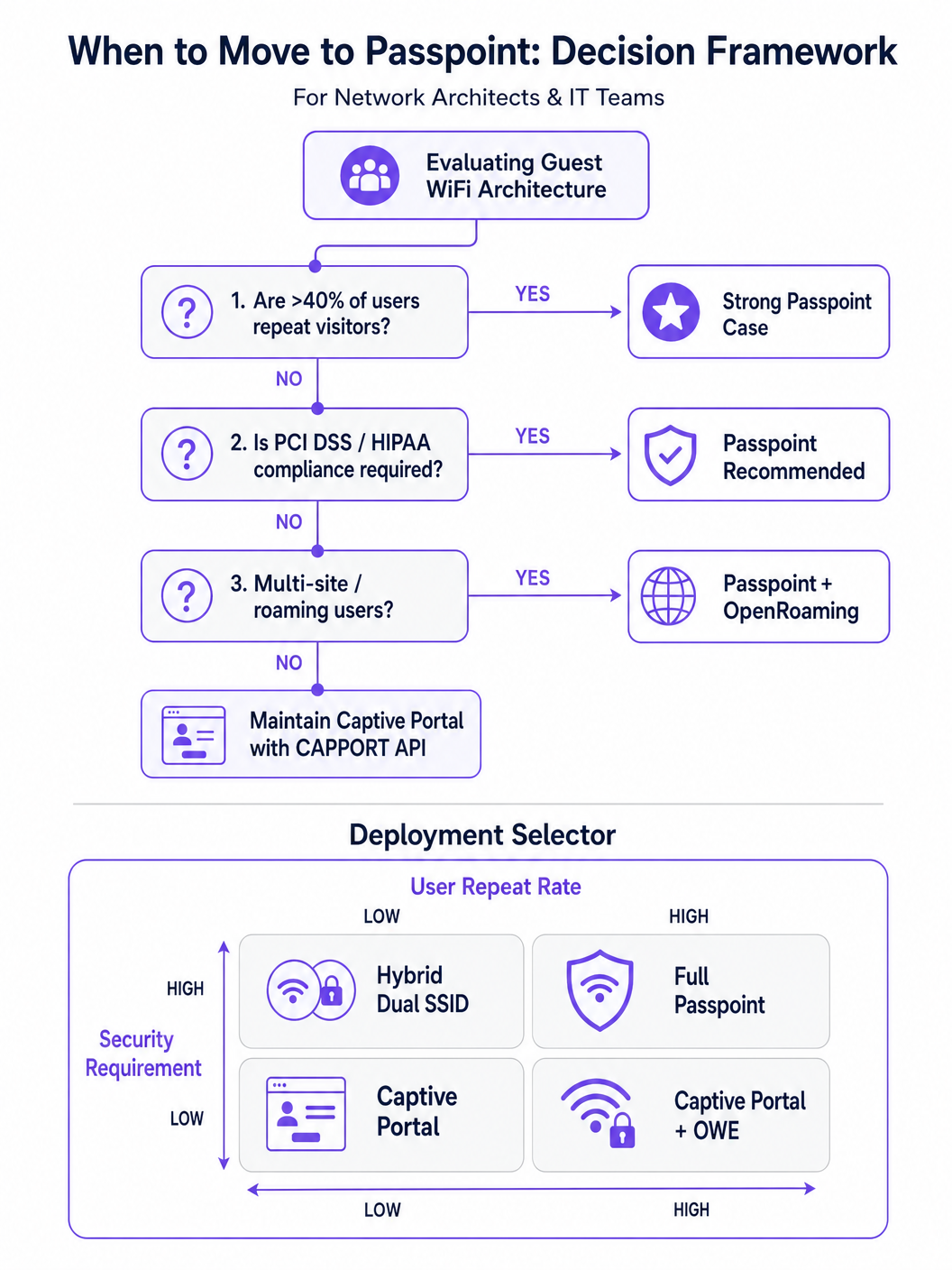
For environments with repeat visitors or high security requirements, Passpoint (based on IEEE 802.11u) is the definitive replacement for the captive portal.
Passpoint operates at the MAC layer. Before associating with the Access Point (AP), the client device uses the Access Network Query Protocol (ANQP) to discover the network's capabilities and roaming consortiums. If the device holds a matching credential (e.g., a profile installed during a previous visit or via an identity provider), it automatically authenticates using 802.1X and WPA2/WPA3-Enterprise.
This approach provides cellular-like, zero-touch connectivity. It encrypts traffic over the air, mitigating the risks of open networks and evil twin attacks. OpenRoaming, built on Passpoint, extends this by federating identity providers, allowing users to roam seamlessly across different venues. Notably, Purple acts as a free identity provider for services like OpenRoaming under the Connect license, facilitating broad adoption without per-user licensing fees.
Implementation Guide
Deploying a resilient guest access architecture requires a phased approach, moving from immediate remediation to strategic transformation.
Phase 1: Stabilise Existing Portals with CAPPORT
If you must maintain a traditional Captive Portal for data capture or WiFi Analytics , you must implement CAPPORT to bypass HSTS breakage.
- Configure DHCP Option 114: Update your DHCP server or network controller to broadcast Option 114, pointing to your portal's API endpoint (e.g.,
https://portal.yourvenue.com/capport). - Implement the RFC 8908 API: Ensure your portal server responds to the API request with valid JSON indicating the captive state and the user-facing URL.
- Use a Dedicated, Valid Hostname: The portal must be served over HTTPS using a valid, CA-signed certificate. Never use a self-signed certificate or a hostname that is on the HSTS preload list.
- Allowlist OS Probes: Ensure that the OS-level Captive Portal detection probes (e.g.,
captive.apple.com,connectivitycheck.gstatic.com) are permitted through the walled garden pre-authentication.
Phase 2: Deploy Passpoint for Secure, Seamless Access
Transitioning to Passpoint significantly enhances security and user experience, particularly in Healthcare and Transport deployments.
- Verify Infrastructure Support: Ensure your APs and controllers support Hotspot 2.0/Passpoint and 802.1X authentication.
- Configure ANQP Profiles: Define the venue name, roaming consortium OIs, and NAI realms in your network controller.
- Establish a RADIUS/AAA Backend: Implement a RADIUS server capable of handling EAP authentication (e.g., EAP-TLS, EAP-TTLS).
- Implement Profile Provisioning: Use an Online Sign-Up (OSU) server or integrate with a platform like Purple SecurePass to provision Passpoint profiles to user devices.
Phase 3: The Hybrid Progressive Onboarding Model
For venues that require both seamless access and initial data capture (e.g., retail environments looking to drive loyalty), a hybrid approach is optimal.
- First Visit: The user connects to an open SSID and is directed to a CAPPORT-enabled Captive Portal. The portal captures necessary data (e.g., email, terms acceptance) and provisions a Passpoint profile to the device.
- Subsequent Visits: The user's device automatically detects the Passpoint network via ANQP and authenticates seamlessly using 802.1X. The Captive Portal is bypassed entirely.
Best Practices
- Avoid 'Frictionless' Marketing Speak: Focus on the technical reality. Passpoint requires initial provisioning friction to achieve long-term seamlessness.
- Segment Guest Traffic: Regardless of the authentication method, guest traffic must be logically separated from corporate networks using VLANs and firewalls, aligning with Internet of Things Architecture: A Complete Guide .
- Monitor Certificate Expiry: A lapsed TLS certificate on your portal or RADIUS server will cause catastrophic authentication failures. Implement automated renewal and monitoring.
- Comply with Data Privacy Regulations: Ensure your data capture and retention policies align with local laws. For specific regional guidance, refer to resources like the Brazil LGPD and Guest WiFi: A Compliance Guide .
Troubleshooting & Risk Mitigation
- Symptom: iOS devices show a blank CNA screen.
- Cause: The portal page contains resources (images, scripts) hosted on external domains that are blocked by the walled garden.
- Fix: Host all essential portal assets locally or add the required external domains to the pre-auth allowlist.
- Symptom: Android devices display a certificate warning instead of the portal.
- Cause: The controller is intercepting HTTPS traffic to a preloaded HSTS domain, or the portal's TLS certificate is invalid/self-signed.
- Fix: Implement CAPPORT and ensure the portal uses a CA-signed certificate on a dedicated hostname.
- Symptom: Passpoint profile installation fails on Windows 11.
- Cause: The provisioning server's certificate chain is incomplete or untrusted by the OS.
- Fix: Verify that the full certificate chain (including intermediate CAs) is served during the TLS handshake.
ROI & Business Impact
Transitioning from legacy HTTP intercept portals to modern CAPPORT and Passpoint architectures delivers measurable business value:
- Reduced Support Tickets: Eliminating HSTS-related certificate errors directly reduces IT helpdesk volume regarding guest connectivity issues.
- Increased Connection Rates: Reliable OS-level portal detection ensures more guests successfully complete the onboarding flow, expanding your reachable audience for marketing initiatives.
- Enhanced Security Posture: Moving to Passpoint and WPA3-Enterprise mitigates the risks associated with open networks, protecting against eavesdropping and evil twin attacks, which is critical for compliance in sectors like finance and healthcare.
- Improved User Experience: Zero-touch roaming via Passpoint drives higher user satisfaction and repeat engagement, supporting broader digital initiatives like Indoor Positioning System: UWB, BLE, & WiFi Guide and Your Guide to Enterprise In Car Wi Fi Solutions .
Key Terms & Definitions
HSTS (HTTP Strict Transport Security)
A web security policy mechanism that forces web browsers to interact with domains only via secure HTTPS connections, preventing protocol downgrade attacks and HTTP interception.
When IT teams see an increase in certificate errors on guest networks, HSTS enforcement on popular domains is typically the root cause, breaking legacy redirect mechanisms.
HSTS Preload List
A hardcoded list built into modern web browsers containing domains that must always be accessed via HTTPS, even on the very first visit.
If a user attempts to navigate to a preloaded domain (like google.com) while behind a legacy captive portal, the browser will refuse the HTTP connection, preventing the portal redirect.
CAPPORT (Captive Portal Architecture)
An IETF standard (RFC 8908 and 8910) that uses DHCP or IPv6 Router Advertisements to explicitly signal the presence and URL of a captive portal to a client device.
Implementing CAPPORT is the primary remediation strategy for network architects to fix broken portal detection on modern iOS, Android, and Windows devices.
Passpoint (Hotspot 2.0)
A Wi-Fi Alliance specification based on IEEE 802.11u that enables devices to automatically discover and securely authenticate to Wi-Fi networks without user intervention.
Used in enterprise and multi-site deployments to replace captive portals entirely, providing cellular-like roaming and WPA3-Enterprise security.
ANQP (Access Network Query Protocol)
A layer 2 protocol used by client devices to query Access Points for network information (like roaming partners and supported authentication types) before associating.
ANQP is the discovery mechanism that allows a Passpoint-enabled device to determine if it has the correct credentials to join a specific network silently.
CNA (Captive Network Assistant)
The OS-level pseudo-browser that automatically opens when a device detects it is behind a captive portal, allowing the user to authenticate before gaining full internet access.
IT teams must ensure their walled garden allows access to the OS-specific probe URLs (e.g., captive.apple.com) so the CNA triggers correctly.
OpenRoaming
A global Wi-Fi roaming federation that allows users to connect automatically and securely across different venues using a single set of credentials provided by an identity provider.
Venues adopt OpenRoaming to provide seamless access for guests, leveraging identity providers like Purple to manage authentication without complex bilateral agreements.
Walled Garden
A restricted network environment where unauthenticated users can only access a specific set of pre-approved IP addresses or domains necessary for the login process.
Misconfigured walled gardens that block OS detection probes or external portal assets are a leading cause of blank screens and failed guest onboarding.
Case Studies
A 400-room enterprise hotel is experiencing a 30% drop in successful guest WiFi connections. Users report seeing 'Your connection is not private' (NET::ERR_CERT_AUTHORITY_INVALID) errors on their smartphones when trying to access the network. The hotel currently uses a legacy open SSID that intercepts port 80 traffic to redirect to a branded splash page.
The IT team must immediately implement the CAPPORT API (RFC 8908/8910). First, configure the network controller's DHCP server to broadcast Option 114, providing the URI of the captive portal API. Second, deploy the RFC 8908 JSON endpoint on the portal server. Third, ensure the portal is hosted on a dedicated subdomain (e.g., wifi.hoteldomain.com) with a valid, CA-signed TLS certificate. Finally, verify that OS detection URLs (like captive.apple.com) are allowed pre-authentication.
A large retail chain with 500 locations wants to implement seamless WiFi roaming for their loyalty app users, eliminating the need for customers to interact with a captive portal on every visit, while still maintaining high security standards (WPA3).
The architect should deploy a Passpoint (Hotspot 2.0) architecture. The initial onboarding can occur via the retailer's loyalty app, which provisions a Passpoint profile (credential) to the user's device. The APs across all 500 locations must be configured to broadcast the appropriate ANQP roaming consortium OIs. A centralized RADIUS infrastructure will handle the 802.1X EAP authentication when the device automatically associates with the network.
Scenario Analysis
Q1. Your organisation is deploying a new guest WiFi network across 50 regional offices. Security policy mandates that all wireless traffic must be encrypted over the air, but the marketing team insists on capturing user email addresses upon first connection. Which architecture should you propose?
💡 Hint:Consider how to balance the requirement for initial data capture with the mandate for over-the-air encryption.
Show Recommended Approach
Propose a hybrid progressive onboarding architecture. First-time users connect to an open SSID and are directed to a CAPPORT-enabled captive portal to provide their email address. Upon submission, the portal provisions a Passpoint profile to the device. The device then automatically transitions to a secure, WPA3-Enterprise encrypted Passpoint SSID for all subsequent traffic and future visits. This satisfies marketing's data capture requirement while enforcing security policy for the vast majority of network usage.
Q2. A client complains that their newly designed, highly customized captive portal page is displaying a blank white screen on all modern iOS devices, although it works perfectly on older Android phones. The portal relies heavily on external web fonts and a third-party analytics script.
💡 Hint:Think about how the iOS Captive Network Assistant (CNA) interacts with external resources before the device is fully authenticated.
Show Recommended Approach
The issue is a misconfigured walled garden. The iOS CNA is attempting to render the portal page, but the external domains hosting the web fonts and analytics scripts are blocked by the network controller pre-authentication. Because these resources cannot load, the CNA stalls and displays a blank screen. The solution is to either host all required assets locally on the portal server or add the specific external domains (FQDNs) to the controller's pre-authentication allowlist.
Q3. During a network audit, you discover that the legacy captive portal is intercepting traffic and serving a self-signed certificate. You are tasked with upgrading the system to use the CAPPORT API. What specific certificate requirements must be met for the new portal server?
💡 Hint:Consider how modern browsers and OS CNAs handle certificate validation during the captive portal detection phase.
Show Recommended Approach
The new portal server must be accessed via a dedicated Fully Qualified Domain Name (FQDN) that is NOT on the HSTS preload list. Furthermore, it must use a valid TLS certificate issued by a publicly trusted Certificate Authority (CA). Self-signed certificates will be rejected by the OS CNA and modern browsers, preventing the portal from loading and halting the onboarding process.



