Purple vs GlobalReach Technology: Carrier-Grade WiFi Compared
This guide provides an authoritative technical comparison of Purple and GlobalReach Technology across captive portal capabilities, WBA OpenRoaming readiness, carrier offload architecture, and commercial models. It is written for IT managers, network architects, and CTOs at hotels, retail chains, stadiums, and municipalities who need to make a platform decision this quarter. The core finding is that while GlobalReach leads in deep MNO carrier offload and standards authorship, Purple disrupts the market with a hardware-agnostic overlay and a genuinely free OpenRoaming Identity Provider tier, making carrier-grade WiFi accessible to any venue without upfront software licensing costs.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive
- Architecture and Standards Compliance
- The OpenRoaming Paradigm Shift
- Platform Comparison at a Glance
- Implementation Guide
- Phase 1: Network Assessment and Hardware Compatibility
- Phase 2: RADIUS and AAA Configuration
- Phase 3: Captive Portal and User Journey Design
- Phase 4: OpenRoaming Enablement
- Phase 5: Analytics, Monitoring, and Optimisation
- Best Practices
- Troubleshooting & Risk Mitigation
- ROI & Business Impact
- References

Executive Summary
The era of open, unencrypted guest WiFi networks is over. As user expectations rise and the threat landscape evolves, venue operators and IT managers face a critical transition from legacy captive portals to secure, carrier-grade WiFi architectures like Passpoint (Hotspot 2.0) and WBA OpenRoaming. This guide provides an authoritative technical reference comparing two major players in the carrier-grade WiFi and captive portal space: Purple and GlobalReach Technology.
For IT managers, network architects, and CTOs at large public venues, Retail chains, Hospitality groups, and municipalities, the choice between these platforms dictates the trajectory of network security, user experience, and commercial ROI. While GlobalReach Technology offers a formidable, bespoke platform deeply integrated into Mobile Network Operator (MNO) infrastructure for cellular offload, Purple disrupts the market with a hardware-agnostic, cloud-native intelligence overlay. Crucially, Purple has democratised access to secure roaming by offering its Connect platform and OpenRoaming Identity Provider (IDP) services completely free of software licence fees, accelerating the adoption of profile-based authentication across enterprise estates.
This reference guide unpacks the technical architecture, implementation realities, and business impact of both platforms, providing actionable guidance for deploying secure, compliant, and commercially viable public WiFi this quarter.
Technical Deep-Dive
Architecture and Standards Compliance
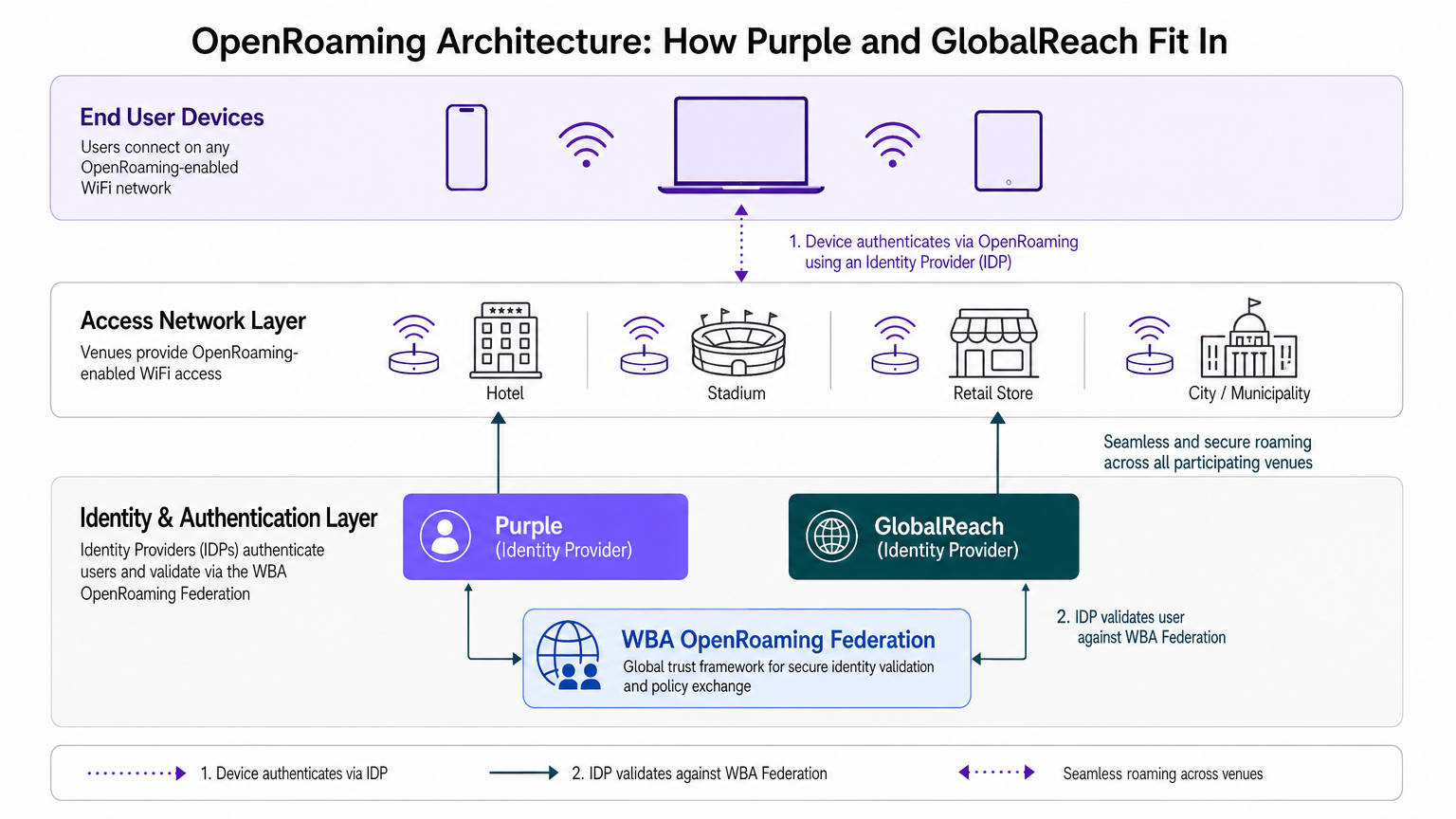
Both Purple and GlobalReach Technology are built upon the foundation of IEEE 802.1X and the Extensible Authentication Protocol (EAP), providing enterprise-grade encryption and mitigating the risks associated with open SSIDs, such as Evil Twin attacks and rogue access points. Both platforms are verified Identity Providers (IDPs) within the Wireless Broadband Alliance (WBA) OpenRoaming federation, supporting Passpoint (Hotspot 2.0) for seamless, automatic onboarding.
GlobalReach Technology: The Carrier-First Approach
GlobalReach's Odyssys platform is engineered for massive scale and complex roaming agreements, primarily serving MNOs, MVNOs, and large municipalities. Their reference deployments include LinkNYC in Manhattan, the London Underground, and carrier offload programmes for AT&T and Virgin Media. Their architecture relies on a proprietary cloud RADIUS and AAA infrastructure designed to handle high-volume carrier offload. GlobalReach excels in scenarios requiring bespoke engineering to integrate WiFi seamlessly into a telco's core network, allowing mobile traffic to offload onto high-performance WiFi to save CapEx and improve service performance. Their captive portal capabilities are robust, supporting sponsored WiFi, video advertising injection, and complex terms-and-conditions reacceptance policies across multi-venue chains. Critically, GlobalReach sits on the WBA Board and their senior team co-authored the Passpoint and Hotspot 2.0 standards — a pedigree that gives them unmatched technical authority in the carrier-grade segment.
Purple: The Hardware-Agnostic Overlay
Purple approaches carrier-grade WiFi as a cloud-native intelligence overlay that integrates with existing infrastructure — be it Cisco, Meraki, Aruba, Ruckus, or Ubiquiti. This infrastructure-agnostic model eliminates the need to rip and replace access points. Purple's SecurePass product leverages EAP-TLS, iPSK, and Passpoint to deliver passwordless, profile-based authentication. By abstracting complex RADIUS infrastructure into RADIUS-as-a-Service, Purple enables venues to deploy enterprise-grade security without managing certificate authorities or on-premises RADIUS servers. Furthermore, Purple's global user base of over 440 million profiles creates a network effect, allowing returning users to connect seamlessly across different venues, effectively countering the challenges posed by MAC randomisation in modern mobile operating systems (iOS 14+). Purple's DNS-level ad and tracker blocking can reclaim up to 38% of network bandwidth, providing a tangible operational benefit alongside security improvements.
The OpenRoaming Paradigm Shift
WBA OpenRoaming is transforming the WiFi experience by enabling devices to automatically and securely connect to participating networks using a federated identity model. More than 3,000 OpenRoaming certificates have been issued, and over 800 end entities are actively using the standard today.
"WBA OpenRoaming is redefining Guest Public WiFi by enabling a seamless, automatic, and secure experience for every user... breaking down financial and technical barriers, we are elevating WiFi into a trusted global utility." — Tiago Rodrigues, President and CEO, Wireless Broadband Alliance.
While both vendors support OpenRoaming as verified IDPs, their commercial models differ significantly. GlobalReach typically operates on an enterprise-contract model with bespoke pricing and professional services, appropriate for the MNO and large operator market. In contrast, Purple has disrupted the market by offering its entry-level Connect platform and OpenRoaming enablement completely free of software licence fees. This strategic move removes the financial friction for venues, allowing any hotel, retail store, or municipality to act as an OpenRoaming hotspot and leverage Purple as a free IDP, thereby democratising access to secure, seamless connectivity.
Platform Comparison at a Glance
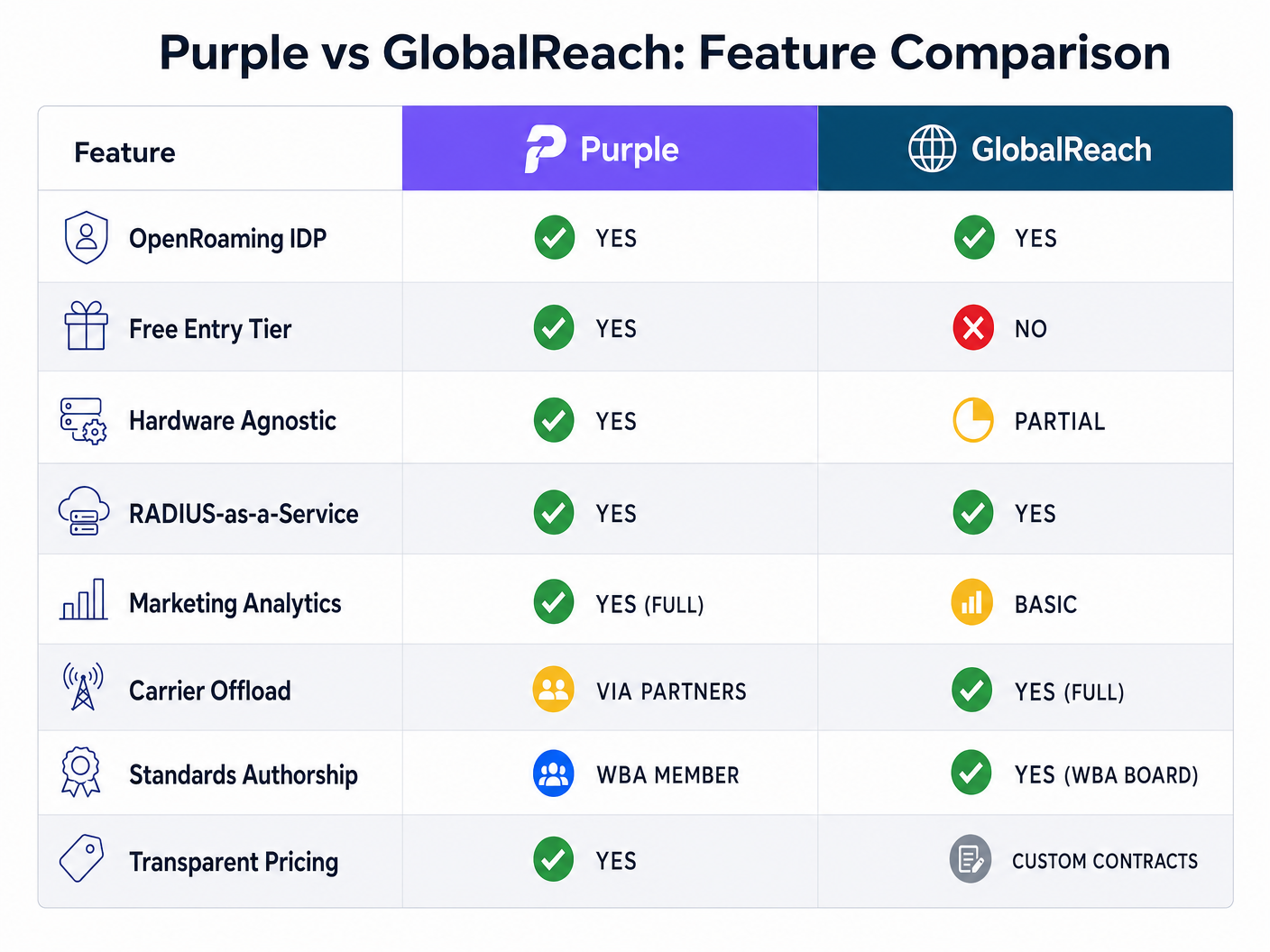
| Capability | Purple | GlobalReach |
|---|---|---|
| WBA OpenRoaming IDP | Yes (free under Connect) | Yes (enterprise contract) |
| Free Entry Tier | Yes (Connect) | No |
| Hardware Agnostic | Yes (full overlay) | Partial (vendor integrations) |
| RADIUS-as-a-Service | Yes (cloud-native) | Yes (public/private cloud) |
| Marketing Analytics | Full (heatmaps, dwell time, automation) | Basic (session and presence data) |
| Carrier Offload (MNO) | Via partners | Yes (native, proven at scale) |
| Standards Authorship | WBA Member | WBA Board Member, Passpoint co-author |
| Transparent Pricing | Yes | Custom enterprise contracts |
| DNS-Level Filtering | Yes (38% bandwidth reclaim) | Not published |
| User Profile Network | 440M+ profiles | Not published |
Implementation Guide
Deploying a carrier-grade WiFi solution requires careful planning and execution. The following phases outline a vendor-neutral approach, highlighting specific integration points for both Purple and GlobalReach.
Phase 1: Network Assessment and Hardware Compatibility
Before selecting a platform, evaluate your existing Wireless LAN Controller (WLC) and access point (AP) infrastructure. Verify that your APs support Passpoint (Hotspot 2.0) and IEEE 802.1X. Most modern enterprise APs from Cisco, Aruba, and Meraki are Passpoint-ready. Purple is strictly hardware-agnostic and operates as an overlay, requiring no hardware changes. GlobalReach is also highly compatible but may require deeper integration for specific carrier offload scenarios. If you are a Transport operator deploying on trains or buses, ensure your mobile routers (e.g., Cradlepoint, Teldat) are supported by your chosen platform. For Healthcare environments, verify that your network segmentation design allows for separate guest and clinical SSIDs before enabling OpenRoaming on the guest network.
Phase 2: RADIUS and AAA Configuration
Secure authentication relies on robust RADIUS infrastructure. Configure your WLC to point to the cloud RADIUS servers provided by your chosen vendor. Establish secure tunnels (RadSec) if required by your security policies, particularly for PCI DSS-compliant environments. Both platforms provide cloud-hosted RADIUS. Purple abstracts this into RADIUS-as-a-Service, simplifying deployment for IT teams without dedicated identity management expertise. GlobalReach provides both public and private cloud RADIUS options, supporting VPN and firewall authentication in addition to WiFi, which is relevant for complex enterprise environments.
Phase 3: Captive Portal and User Journey Design
Even with Passpoint, a captive portal is often necessary for initial onboarding, terms acceptance, or fallback access for non-Passpoint devices. Design a clean, branded captive portal journey. Ensure compliance with local data privacy regulations (GDPR, CCPA) during data capture. For specific regional guidance, refer to resources like PIPEDA Compliance for Guest WiFi in Canada . Purple offers a drag-and-drop splash page editor with robust marketing automation integration. GlobalReach provides pre-designed templates and a content manager suitable for sponsored WiFi and video advertising campaigns.
Phase 4: OpenRoaming Enablement
Enable seamless roaming to improve user experience and security. Register as an OpenRoaming participant and configure your network to broadcast the OpenRoaming Organisation Identifier (OI) and route authentication requests to your IDP. With Purple Connect, this phase is significantly streamlined, as Purple acts as the free IDP. Venues can toggle OpenRoaming on without incurring additional software licence fees. For GlobalReach deployments, OpenRoaming enablement is part of the enterprise contract and typically involves professional services engagement.
Phase 5: Analytics, Monitoring, and Optimisation
Post-deployment, establish a baseline for key metrics: concurrent user counts, authentication success rates, session duration, and RADIUS latency. Purple's WiFi Analytics platform provides heatmaps, dwell time analysis, and footfall data that can be fed directly into marketing automation workflows. For Guest WiFi environments, this data is critical for demonstrating ROI and optimising the user journey. For IoT-heavy deployments, consider how your chosen platform handles device onboarding at scale — a topic covered in depth in our Internet of Things Architecture: A Complete Guide .
Best Practices
Prioritise Profile-Based Authentication. Transition away from open SSIDs and shared passwords (WPA2-PSK). Implement EAP-TLS, iPSK, or Passpoint to ensure each user or device has a unique, cryptographically verifiable identity. This is the single most impactful security improvement available to venue operators today.
Embrace Hardware Agnosticism. Avoid vendor lock-in by choosing an intelligence overlay that integrates with your existing APs and controllers. This protects your CapEx investment and provides flexibility for future hardware refreshes. Purple's infrastructure-agnostic model is the clearest example of this approach in the market.
Leverage Network Effects. Choose an identity provider with a large existing user base. With 440 million profiles, Purple increases the likelihood that visitors to your venue will automatically connect via existing profiles, reducing onboarding friction and improving the user experience from day one.
Implement DNS-Level Filtering. Enhance security and optimise bandwidth by blocking malicious domains, ads, and trackers at the DNS level. This can reclaim significant network capacity and protect users from phishing attacks, particularly relevant in high-density public WiFi environments.
Plan for MAC Randomisation. iOS 14+ and Android 10+ randomise MAC addresses by default. Any deployment that relies on MAC-based tracking for seamless return visits will fail. The only reliable mitigation is profile-based authentication via Passpoint or EAP-TLS.
Document Your Data Retention Policies. Both GDPR and CCPA impose strict requirements on how you collect and store user data during WiFi onboarding. Ensure your captive portal data capture is compliant before go-live, and establish clear data retention and deletion workflows.
Troubleshooting & Risk Mitigation
Risk: MAC Randomisation Breaking Analytics and Seamless Reconnection. Modern OS features (iOS 14+, Android 10+) randomise MAC addresses, breaking traditional captive portal tracking and requiring users to repeatedly log in. The mitigation is to deploy Passpoint/OpenRoaming. Because authentication is based on a cryptographic profile rather than a MAC address, the user's identity remains consistent even if the device's MAC address changes.
Risk: Rogue Access Points (Evil Twins). Attackers broadcast an SSID identical to your venue's network to intercept user credentials and traffic. IEEE 802.1X and Passpoint require the client device to verify the network's identity (via server certificates) before establishing a connection, completely neutralising the Evil Twin threat. This is a fundamental security improvement over any open SSID or WPA2-PSK network.
Risk: High Latency in Cloud RADIUS. Slow authentication responses from cloud RADIUS servers can lead to connection timeouts and poor user experience, particularly in high-density environments like stadiums. Ensure your vendor provides a globally distributed, highly available RADIUS infrastructure. Monitor authentication latency metrics within the platform's dashboard and establish SLA requirements before contract signature.
Risk: Passpoint Compatibility on Legacy Hardware. If your access points are more than five years old, they may not support Passpoint Release 2 or the Online Sign-Up (OSU) flow. Conduct a full hardware audit before committing to a platform. Both Purple and GlobalReach provide hardware compatibility matrices.
Risk: Compliance Gaps in Data Capture. Deploying a captive portal without a properly configured GDPR or CCPA consent flow exposes the venue to regulatory risk. Ensure your chosen platform provides compliant consent mechanisms and that your data processing agreements with the vendor are in place before go-live.
ROI & Business Impact
The transition to a carrier-grade WiFi platform delivers measurable business impact across three primary vectors.
Cost Reduction (CapEx and OpEx). For MNOs, carrier offload via platforms like GlobalReach significantly reduces the CapEx required for macro-cell expansion in dense urban areas. For venue operators, adopting a hardware-agnostic overlay like Purple eliminates the need for expensive hardware upgrades. Purple's free Connect tier removes the software licensing costs associated with OpenRoaming enablement entirely, making the ROI calculation straightforward for venues with existing Passpoint-capable hardware.
Revenue Generation and Marketing. Moving beyond basic connectivity, platforms like Purple provide robust Guest WiFi and WiFi Analytics capabilities. Capturing first-party data in a GDPR-compliant manner allows marketing teams to trigger automated campaigns based on dwell time and footfall, driving repeat visits and increased spend in Retail and Hospitality environments. For large venue operators, the ability to offer sponsored WiFi and in-portal advertising (a GlobalReach strength) provides an additional direct revenue stream.
Risk Mitigation and Compliance. Deploying enterprise-grade encryption (WPA3-Enterprise, 802.1X) protects the venue from liability associated with data breaches on open networks. It also ensures compliance with stringent data protection regulations (GDPR, CCPA) and industry standards (PCI DSS). The cost of a single data breach or regulatory fine far exceeds the investment in a compliant, carrier-grade WiFi platform.
For indoor positioning and location-based services that extend the value of your WiFi investment, see our guide on Indoor Positioning System: UWB, BLE, & WiFi , and for transport-specific deployments, our guide on Enterprise In-Car WiFi Solutions provides relevant architecture patterns.
References
[1] GlobalReach Technology, "Why Use Passpoint for Wi-Fi Offload," globalreachtech.com. [2] Purple AI, "Passwordless WiFi: EAP-TLS, iPSK & Certificate Auth," purple.ai. [3] Purple AI, "Purple's free initiative to accelerate OpenRoaming™ adoption for businesses," purple.ai, Nov. 21, 2025. [4] GlobalReach Technology, "GlobalReach Passpoint," globalreachtech.com. [5] Wireless Broadband Alliance, "WBA OpenRoaming Profile Signup," wballiance.com.
Key Terms & Definitions
WBA OpenRoaming
A Wireless Broadband Alliance (WBA) standard that enables devices to automatically and securely connect to participating WiFi networks using a federated identity model, without requiring manual login. It uses IEEE 802.1X and Passpoint (Hotspot 2.0) as its technical foundation.
IT teams encounter this when evaluating carrier-grade WiFi platforms. It matters because it eliminates the need for captive portal logins for returning users, significantly improving the user experience and security posture of public WiFi deployments.
Identity Provider (IDP)
In the context of WBA OpenRoaming, an IDP is an organisation that issues and manages the digital credentials (certificates or profiles) that allow a user's device to authenticate automatically to any participating OpenRoaming network. Both Purple and GlobalReach are verified OpenRoaming IDPs.
IT teams encounter this when configuring OpenRoaming. The choice of IDP determines the cost model and the scope of the user profile network available to the venue.
Passpoint (Hotspot 2.0)
A Wi-Fi Alliance certification programme that defines a set of protocols (based on IEEE 802.11u and IEEE 802.1X) for seamless, secure WiFi onboarding. Passpoint-enabled devices automatically discover and connect to compatible networks using pre-provisioned credentials, without requiring user interaction.
IT teams encounter this when designing enterprise WiFi networks that need to eliminate captive portal friction. It is the technical foundation for both WBA OpenRoaming and carrier offload deployments.
Carrier Offload
The process by which a Mobile Network Operator (MNO) routes cellular data traffic from its macro-cell network onto a WiFi network, reducing load on the cellular infrastructure and improving service quality for subscribers. Passpoint and EAP-SIM/AKA are the key enabling technologies.
IT teams at municipalities and large venue operators encounter this when negotiating with MNO partners. It matters because it can provide a revenue stream for the venue operator and reduce CapEx for the MNO.
RADIUS-as-a-Service
A cloud-hosted implementation of the Remote Authentication Dial-In User Service (RADIUS) protocol, eliminating the need for venue operators to deploy and manage on-premises RADIUS servers. The service handles authentication, authorisation, and accounting (AAA) for WiFi connections.
IT teams encounter this when deploying IEEE 802.1X-based WiFi without the budget or expertise to manage on-premises AAA infrastructure. Purple's RADIUS-as-a-Service is a key enabler for its hardware-agnostic deployment model.
EAP-TLS (Extensible Authentication Protocol - Transport Layer Security)
An EAP method that uses X.509 certificates on both the client and server to provide mutual authentication. It is considered the most secure EAP method for WiFi authentication and is the foundation of Purple's SecurePass passwordless WiFi product.
IT teams encounter this when deploying enterprise-grade, passwordless WiFi. It requires a Public Key Infrastructure (PKI) to issue and manage client certificates, which Purple abstracts via its cloud platform.
MAC Randomisation
A privacy feature in modern mobile operating systems (iOS 14+, Android 10+) that causes the device to use a different, randomised MAC address each time it connects to a WiFi network. This prevents tracking across networks and over time, but breaks legacy captive portal systems that rely on MAC addresses for user identification.
IT teams encounter this when diagnosing why returning users are repeatedly prompted to log in to the captive portal. The only reliable mitigation is profile-based authentication via Passpoint or EAP-TLS.
Online Sign-Up (OSU)
A Passpoint Release 2 feature that allows users to provision a Passpoint credential (certificate or username/password) directly from a device, without requiring a separate app or manual configuration. The device discovers the OSU server via the WiFi network and completes the provisioning process automatically.
IT teams encounter this when deploying Passpoint for the first time. OSU is the mechanism by which first-time users transition from a captive portal to a persistent Passpoint profile, enabling seamless reconnection on future visits.
IEEE 802.1X
An IEEE standard for port-based network access control, providing an authentication framework for devices connecting to a LAN or WLAN. It requires a supplicant (client device), an authenticator (access point), and an authentication server (RADIUS) to complete the authentication exchange.
IT teams encounter this as the foundational standard for enterprise WiFi security. It is the basis for WPA2-Enterprise, WPA3-Enterprise, and Passpoint deployments, and is a prerequisite for any carrier-grade WiFi platform.
Case Studies
A 500-room conference hotel in central London is running a legacy open SSID with a basic captive portal. The IT director needs to replace it with a solution that meets GDPR requirements, handles up to 3,000 concurrent users during large events, and provides the marketing team with footfall analytics. The hotel uses Cisco Meraki access points. What is the recommended deployment path?
The recommended path is to deploy Purple as a cloud-native overlay on the existing Meraki infrastructure. Step 1: Configure the Meraki dashboard to point to Purple's cloud RADIUS servers using the standard Meraki captive portal integration. Step 2: Build a branded captive portal using Purple's drag-and-drop editor, configuring GDPR-compliant data capture with explicit consent mechanisms. Step 3: Enable OpenRoaming under Purple's free Connect licence, broadcasting the OpenRoaming OI alongside the standard SSID. Step 4: Configure a secondary Passpoint SSID for returning users who have already completed the OSU flow, enabling automatic, seamless reconnection. Step 5: Connect Purple's analytics dashboard to the marketing team's CRM for automated campaign triggers based on dwell time and visit frequency. The entire deployment can be completed in days, not weeks, with no additional hardware investment and zero software licensing costs for the Connect tier.
A major city municipality is deploying free public WiFi across 200 kiosks and transport hubs, with the goal of providing carrier offload for a Tier 1 MNO partner. The MNO requires deep integration with their subscriber identity management (SIM-based authentication) and wants to monetise the WiFi estate through roaming agreements. What platform should the municipality evaluate?
This deployment profile maps directly to GlobalReach Technology's core competency. Step 1: Engage GlobalReach's professional services team to scope the MNO integration requirements, specifically the RADIUS proxy configuration needed to route SIM-based authentication (EAP-SIM/AKA) to the MNO's Home Subscriber Server (HSS). Step 2: Deploy GlobalReach's Odyssys platform as the AAA backbone, configuring it to handle both captive portal onboarding for non-SIM devices and Passpoint/OpenRoaming for SIM-capable devices. Step 3: Configure the OpenRoaming federation to allow the MNO's subscribers to automatically connect to the municipal WiFi network using their cellular identity. Step 4: Establish roaming agreements through GlobalReach's managed roaming service to allow the municipality to monetise the WiFi estate by providing coverage to the MNO's subscribers. Step 5: Deploy GlobalReach's analytics dashboard to provide the municipality with session data and the MNO with offload reporting.
Scenario Analysis
Q1. A regional retail chain with 80 stores across the UK is currently running WPA2-PSK on all guest networks. Their IT team has reported that approximately 40% of guest WiFi sessions are from returning customers who are repeatedly prompted to enter the shared password. The marketing director wants to use WiFi data for footfall analytics and automated loyalty campaigns. The stores use a mix of Aruba and Ubiquiti access points. What is the recommended platform strategy, and what specific technical changes are required?
💡 Hint:Consider the MAC randomisation implications of the current WPA2-PSK setup, and evaluate which platform's pricing model and hardware compatibility best suits an 80-store rollout.
Show Recommended Approach
The recommended strategy is to deploy Purple as a hardware-agnostic overlay across all 80 stores. The current WPA2-PSK setup is fundamentally broken for returning user identification due to MAC randomisation in iOS 14+ and Android 10+. The solution requires: (1) Deploying Purple's cloud RADIUS on both Aruba and Ubiquiti APs via standard 802.1X configuration; (2) Replacing the shared PSK with a captive portal for first-time visitors, capturing GDPR-compliant first-party data; (3) Enabling OpenRoaming under Purple's free Connect licence, so returning customers who have completed the OSU flow reconnect automatically and securely without any login prompt; (4) Connecting Purple's analytics dashboard to the marketing team's CRM for automated loyalty campaign triggers. The free Connect tier makes the business case straightforward for an 80-store rollout. If the marketing director requires advanced segmentation and automated campaign triggers, the Engage tier should be evaluated. GlobalReach is not the recommended choice here as the retail chain does not require MNO carrier offload or bespoke carrier engineering.
Q2. A national rail operator is deploying WiFi across 150 stations and wants to offer seamless connectivity to passengers who are subscribers of three different MNO partners. The MNOs want their subscribers to connect automatically using their SIM credentials, without any captive portal interaction. The operator also wants to provide a captive portal for non-subscriber passengers. Which platform is most appropriate, and what are the key technical integration requirements?
💡 Hint:The requirement for SIM-based authentication (EAP-SIM/AKA) and MNO subscriber identity management is the critical differentiator in this scenario.
Show Recommended Approach
GlobalReach Technology is the most appropriate platform for this deployment. The requirement for SIM-based authentication (EAP-SIM/AKA) and integration with three MNOs' Home Subscriber Servers (HSS) requires carrier-grade RADIUS engineering that GlobalReach has demonstrated at scale in comparable deployments (London Underground, AT&T LinkNYC). The key technical integration requirements are: (1) Deploying GlobalReach's Odyssys platform as the AAA backbone at each station; (2) Configuring RADIUS proxy rules to route EAP-SIM/AKA authentication requests to each MNO's HSS; (3) Establishing OpenRoaming federation agreements with each MNO to allow their subscribers to roam onto the station WiFi; (4) Configuring a separate captive portal SSID for non-subscriber passengers, with GDPR-compliant data capture; (5) Establishing commercial roaming agreements through GlobalReach's managed roaming service to define the revenue-sharing model with each MNO. Purple is not the recommended choice here because it does not natively support EAP-SIM/AKA at the depth required for direct MNO HSS integration.
Q3. A large outdoor music festival is planning to deploy temporary WiFi infrastructure for 50,000 attendees over three days. The event organiser wants to capture attendee data for post-event marketing, offer sponsored WiFi with branded captive portals for two corporate sponsors, and ensure the network is secure and GDPR-compliant. The deployment uses hired Cisco Meraki access points. What platform and configuration approach would you recommend?
💡 Hint:Consider the temporary nature of the deployment, the sponsored WiFi requirement, and the GDPR compliance obligation when evaluating both platforms.
Show Recommended Approach
Purple is the recommended platform for this deployment. The temporary nature of the event, the Meraki hardware, and the requirement for GDPR-compliant data capture with marketing automation all align with Purple's strengths. The recommended configuration is: (1) Deploy Purple's cloud RADIUS on the hired Meraki APs — no hardware changes required; (2) Build two branded captive portal journeys using Purple's drag-and-drop editor, one for each corporate sponsor, with sponsor branding and GDPR-compliant consent flows; (3) Configure GDPR-compliant data capture to collect attendee email addresses and opt-in consent for post-event marketing; (4) Enable OpenRoaming under the free Connect licence to allow attendees who are already OpenRoaming users to connect automatically and securely; (5) Use Purple's analytics dashboard to monitor concurrent user counts and session data in real time during the event; (6) Export the GDPR-compliant attendee data to the event organiser's CRM post-event for automated follow-up campaigns. The free Connect tier and the ability to deploy on hired hardware without a long-term contract make Purple the practical choice for a temporary event deployment. GlobalReach's enterprise contract model is not suited to a three-day event deployment.



