Mise en œuvre de l'authentification 802.1X sur les appareils mobiles
Ce guide complet fournit aux leaders informatiques un plan technique pour la mise en œuvre de l'authentification 802.1X sur les appareils iOS et Android. Il couvre l'architecture, la sélection de la méthode EAP, le provisionnement MDM et le dépannage pour garantir un accès réseau mobile sécurisé et évolutif.
Écouter ce guide
Voir la transcription du podcast
- Résumé exécutif
- Approfondissement technique : Architecture et méthodes EAP
- Sélection de la méthode EAP pour les appareils mobiles
- Guide de mise en œuvre
- 1. Configuration du serveur RADIUS
- 2. Configuration de l'infrastructure sans fil
- 3. Provisionnement des appareils mobiles (MDM)
- Bonnes pratiques
- Dépannage et atténuation des risques
- Retour sur investissement et impact commercial

Résumé exécutif
La mise en œuvre de l'authentification 802.1X sur les appareils mobiles n'est plus facultative pour les environnements d'entreprise. Qu'il s'agisse de gérer un bureau d'entreprise, un hôtel de 500 chambres ou un stade, la dépendance aux clés pré-partagées (PSKs) présente un risque de sécurité inacceptable. Ce guide fournit un plan technique complet pour le déploiement de 802.1X sur les parcs d'appareils iOS et Android. Nous aborderons les exigences architecturales, la sélection de la méthode du protocole d'authentification extensible (EAP), le provisionnement de la gestion des appareils mobiles (MDM) et les modes de défaillance courants.
En passant à 802.1X, les organisations obtiennent un contrôle d'accès réseau granulaire, une sécurité accrue du WiFi invité et la conformité aux cadres réglementaires tels que PCI DSS et GDPR. Cette transition nécessite une orchestration minutieuse entre l'infrastructure sans fil, le serveur RADIUS et les points d'extrémité mobiles.
Approfondissement technique : Architecture et méthodes EAP
La norme IEEE 802.1X définit le contrôle d'accès réseau basé sur les ports, composé de trois composants principaux : le demandeur (appareil mobile), l'authentificateur (point d'accès sans fil ou contrôleur) et le serveur d'authentification (RADIUS).
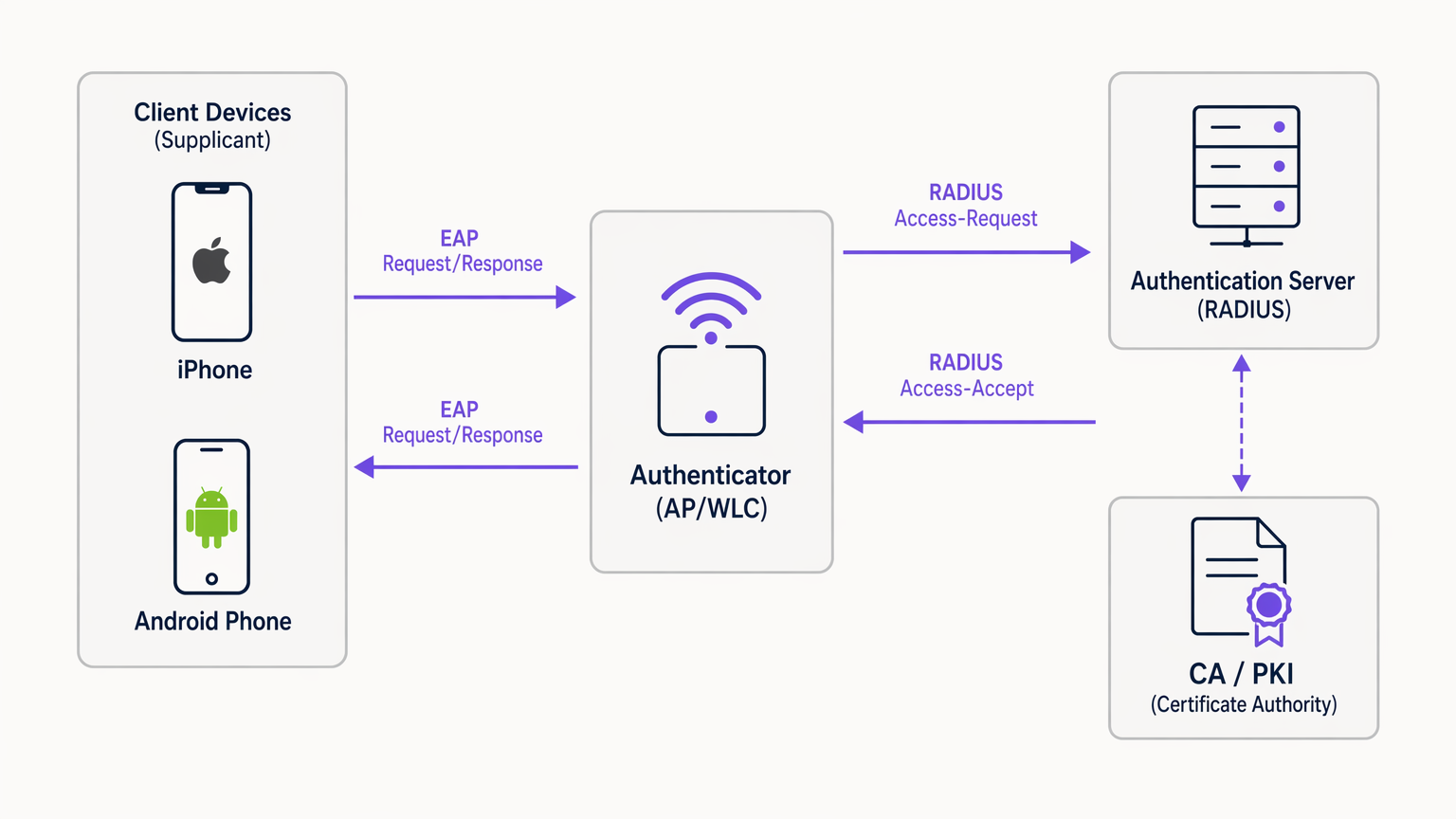
Lorsqu'un appareil mobile tente de se connecter, l'authentificateur bloque tout le trafic, à l'exception des paquets EAP over LAN (EAPoL), jusqu'à ce que le serveur RADIUS valide avec succès les identifiants. Le choix de la méthode EAP dicte la posture de sécurité et la complexité du déploiement.
Sélection de la méthode EAP pour les appareils mobiles
Les systèmes d'exploitation mobiles ont des niveaux de prise en charge native variables pour les méthodes EAP. Les deux normes dominantes pour les déploiements d'entreprise sont EAP-TLS et PEAP-MSCHAPv2.
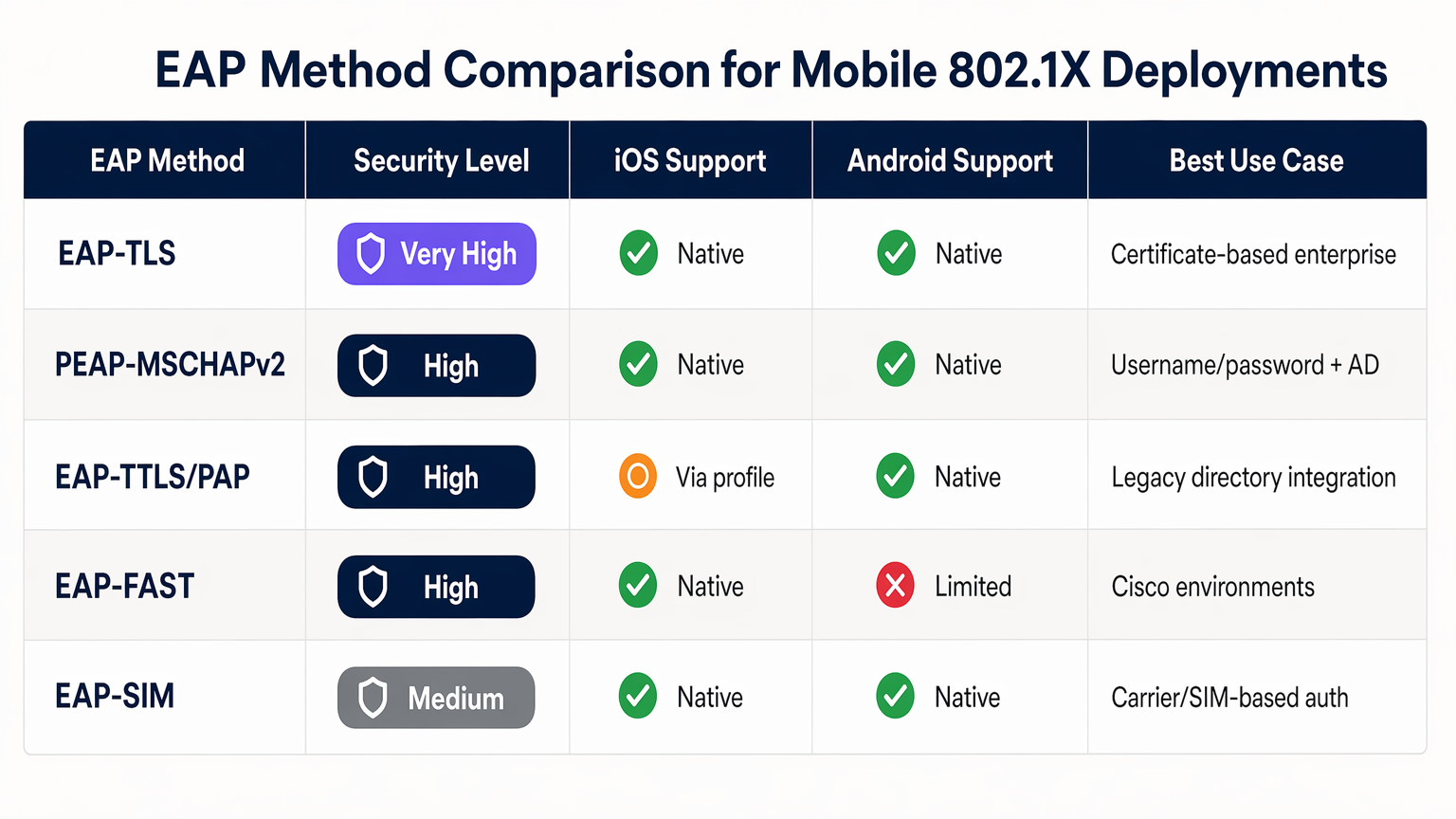
EAP-TLS est la méthode la plus sécurisée, reposant sur une authentification mutuelle basée sur des certificats. Elle élimine les risques de vol d'identifiants mais nécessite une infrastructure à clé publique (PKI) robuste et un MDM pour la distribution des certificats. Les appareils iOS et Android prennent en charge EAP-TLS nativement.
PEAP-MSCHAPv2 encapsule l'échange d'authentification dans un tunnel TLS, permettant l'utilisation d'identifiants Active Directory. Bien que plus facile à déployer sans PKI, elle est vulnérable à la collecte d'identifiants si l'appareil client n'est pas strictement configuré pour valider le certificat du serveur.
Guide de mise en œuvre
Le déploiement de 802.1X nécessite une configuration coordonnée de l'infrastructure réseau et du parc mobile.
1. Configuration du serveur RADIUS
Le serveur RADIUS (par exemple, Microsoft NPS, Cisco ISE ou des alternatives cloud comme JumpCloud) doit être configuré pour prendre en charge la méthode EAP choisie. Pour PEAP, installez un certificat de serveur émis par une autorité de certification (CA) de confiance. Pour EAP-TLS, configurez le serveur pour qu'il fasse confiance à l'autorité de certification émettant les certificats clients. Assurez-vous que le serveur RADIUS est intégré à votre service d'annuaire (AD, LDAP) ou à votre fournisseur d'identité.
2. Configuration de l'infrastructure sans fil
Configurez vos points d'accès (APs) ou votre contrôleur de réseau local sans fil (WLC) pour diffuser un SSID avec la sécurité WPA2-Enterprise ou WPA3-Enterprise. Spécifiez l'adresse IP et le secret partagé du serveur RADIUS. Activez la comptabilité RADIUS pour suivre les sessions utilisateur, ce qui est crucial pour l' analyse WiFi et le dépannage.
Pour les déploiements avancés, consultez notre guide sur la mise en œuvre de WPA3-Enterprise pour une sécurité sans fil améliorée .
3. Provisionnement des appareils mobiles (MDM)
La configuration manuelle de 802.1X sur les appareils mobiles est fortement déconseillée en raison des erreurs utilisateur et des risques de sécurité (par exemple, les utilisateurs acceptant des certificats de serveurs malveillants). Utilisez une solution MDM (Jamf, Intune, Workspace ONE) pour pousser un profil de configuration WiFi.
- iOS : Utilisez Apple Configurator ou MDM pour pousser un profil contenant le SSID, la méthode EAP et la chaîne de certificats de serveur de confiance. Pour EAP-TLS, le profil doit également déployer le certificat client.
- Android : Android 11+ exige strictement la validation du certificat du serveur. Le MDM doit pousser le certificat CA vers le magasin de confiance de l'appareil en même temps que le profil WiFi.
Bonnes pratiques
- Exiger la validation du certificat du serveur : Ne jamais autoriser les appareils à se connecter sans valider le certificat du serveur RADIUS. Cela prévient les attaques de l'homme du milieu.
- Utiliser le MDM pour le provisionnement : Compter sur les utilisateurs pour configurer manuellement les paramètres 802.1X entraîne une surcharge de support et des vulnérabilités de sécurité.
- Segmenter le trafic : Placez les utilisateurs authentifiés 802.1X sur un VLAN distinct du trafic invité ou des appareils IoT.
- Mettre en œuvre le RADIUS Cloud : Pour les environnements distribués comme les chaînes de commerce de détail ou les établissements d' hôtellerie , le RADIUS cloud réduit les dépendances d'infrastructure sur site.
Dépannage et atténuation des risques
Les modes de défaillance les plus courants dans les déploiements mobiles 802.1X concernent les certificats et les délais d'attente.
- Erreurs de confiance des certificats : Si les appareils iOS invitent les utilisateurs à faire confiance à un certificat, ou si les appareils Android refusent de se connecter, la chaîne de certificats complète (CA racine et intermédiaires) est probablement manquante dans le profil MDM.
- Latence RADIUS : Les appareils mobiles abandonneront la connexion si le serveur RADIUS met plus de 2 à 3 secondes à répondre. Assurez-vous que votre infrastructure RADIUS est correctement dimensionnée, en particulier dans les environnements à haute densité.
- Inadéquation EAP : Assurez-vous que la méthode EAP configurée sur le WLC correspond au serveur RADIUS et au profil client.
Retour sur investissement et impact commercial
Mise en œuvre de Le 802.1X réduit considérablement le risque d'accès non autorisé au réseau et de mouvement latéral. Pour une entreprise de 10 000 employés, l'automatisation de l'intégration WiFi via MDM et 802.1X peut économiser des centaines d'heures de support informatique par an par rapport à la gestion des rotations de PSK. De plus, la visibilité granulaire fournie par la comptabilité RADIUS prend en charge les exigences de conformité et facilite la planification des capacités.
Écoutez notre briefing podcast complet pour plus d'informations :
Définitions clés
802.1X
An IEEE standard for port-based network access control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational standard replacing insecure shared passwords (PSKs) in enterprise environments.
Supplicant
The software client on the mobile device that requests network access and handles the EAP exchange.
The native WiFi settings on iOS or Android act as the supplicant.
Authenticator
The network device (AP or WLC) that facilitates the authentication process between the supplicant and the RADIUS server.
The AP blocks traffic until authentication succeeds.
RADIUS Server
Remote Authentication Dial-In User Service; a networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management.
The decision engine that validates credentials against a directory (e.g., Active Directory).
EAP (Extensible Authentication Protocol)
An authentication framework frequently used in wireless networks and point-to-point connections.
The protocol carrying the authentication data between the mobile device and the RADIUS server.
EAP-TLS
An EAP method that uses Public Key Infrastructure (PKI) to require both the client and server to present certificates for mutual authentication.
The most secure method, ideal for fully managed corporate devices.
PEAP-MSCHAPv2
Protected EAP; creates an encrypted TLS tunnel within which the client authenticates using a username and password.
The most common method, balancing security with ease of deployment for environments without a PKI.
MDM (Mobile Device Management)
Software used by IT departments to monitor, manage, and secure employees' mobile devices.
Essential for silently configuring 802.1X settings and distributing certificates without user intervention.
Exemples concrets
A 500-room hotel needs to deploy secure WiFi for staff mobile devices (a mix of corporate-owned iOS and BYOD Android). They currently use a shared WPA2-PSK.
Deploy an 802.1X SSID using PEAP-MSCHAPv2. Integrate a cloud RADIUS server with the hotel's Azure AD. For corporate iOS devices, use an MDM to push the WiFi profile and the trusted CA certificate. For BYOD Android, provide an onboarding portal (like SecureW2) to automatically configure the device supplicant and install the CA certificate, avoiding manual configuration errors.
A large public-sector organisation is rolling out 5,000 corporate-owned Android tablets for field workers and requires the highest level of network security.
Implement EAP-TLS. Deploy an internal PKI or cloud CA. Use the organisation's MDM (e.g., VMware Workspace ONE) to generate and push unique client certificates to each Android tablet, along with the WiFi configuration profile and the Root CA certificate. Configure the RADIUS server to only accept EAP-TLS connections.
Questions d'entraînement
Q1. Your organisation is deploying 802.1X for a fleet of BYOD Android devices. You do not have an MDM solution. Users are complaining that they cannot connect to the new SSID, and they see a 'Must specify a domain' or 'CA certificate required' error.
Conseil : Consider how modern Android versions handle server certificate validation compared to older versions.
Voir la réponse type
Modern Android versions (11+) no longer allow users to bypass server certificate validation ('Do not validate'). Without an MDM to push the CA certificate, users must manually download and install the CA certificate into their device's trust store, and then manually configure the WiFi profile to use that specific certificate. A better long-term solution is implementing an onboarding portal to automate this process.
Q2. You have deployed EAP-TLS using an internal Microsoft ADCS PKI. Windows laptops connect flawlessly, but iOS devices deployed via Jamf MDM are failing authentication silently.
Conseil : Think about the full certificate chain and what the iOS device needs to trust the server.
Voir la réponse type
The iOS devices likely lack the Root CA certificate (and any Intermediate CAs) of the internal PKI. Windows laptops automatically trust the ADCS Root CA via Group Policy. The Jamf MDM WiFi profile must be updated to explicitly include the Root CA certificate payload so the iOS device can validate the RADIUS server's certificate during the TLS handshake.
Q3. During a high-traffic event at a stadium, many mobile devices are failing to connect to the 802.1X network, while others connect fine. Packet captures show the APs sending RADIUS Access-Requests, but the RADIUS server is responding with Access-Rejects after several seconds, or not responding at all.
Conseil : Consider the '3-Second Rule' for mobile devices and RADIUS performance.
Voir la réponse type
The RADIUS server is likely overwhelmed by the volume of simultaneous authentication requests, leading to high latency. Mobile devices have short timeout thresholds (often 3 seconds) and will abort the connection or retry, further exacerbating the load. The solution is to scale the RADIUS infrastructure (e.g., adding more nodes or deploying regional proxies) and tuning the WLC timeout/retry settings.
Continuer la lecture de cette série
PSK par appareil par fournisseur : comparaison entre iPSK, DPSK, MPSK et PPSK (et support WPA3)
Une comparaison complète des implémentations PSK par appareil chez Cisco Meraki, HPE Aruba, Ruckus, Juniper Mist, Extreme, Fortinet et Ubiquiti UniFi. Découvrez comment le WPA3-SAE impacte les stratégies de clés par appareil et quand déployer des modes de transition plutôt que de passer au 802.1X.
Qu'est-ce que l'authentification par adresse MAC ? Quand l'utiliser et quand l'éviter
Ce guide de référence technique fait autorité sur l'authentification par adresse MAC dans les environnements WiFi d'entreprise – comment l'authentification MAC basée sur RADIUS fonctionne à la Couche 2, ses vulnérabilités de sécurité inhérentes (y compris l'usurpation d'adresse MAC et l'impact de la randomisation MAC au niveau du système d'exploitation), et les contextes opérationnels précis où elle reste un outil valide pour la gestion des appareils IoT et sans tête. Il fournit des conseils de déploiement exploitables pour les responsables informatiques et les architectes réseau dans les secteurs de l'hôtellerie, du commerce de détail, de la santé et des lieux publics, avec des exemples concrets, des cadres de décision et un contexte d'intégration pour la plateforme de WiFi invité et d'analyse de Purple.
Comment configurer le WiFi d'entreprise sur iOS et macOS avec 802.1X
This authoritative guide provides senior IT leaders with actionable steps for deploying 802.1X enterprise WiFi on iOS and macOS devices. It covers certificate-based authentication (EAP-TLS), MDM configuration profiles, and architecture integration to secure corporate networks while supporting BYOD initiatives.