India DPDP Act: Conformità WiFi Ospiti per le Sedi Indiane
Questa guida di riferimento tecnico autorevole analizza il Digital Personal Data Protection (DPDP) Act 2023 per le sedi indiane che gestiscono il WiFi ospiti. Fornisce strategie di conformità attuabili, considerazioni architettoniche per i Captive Portal e framework pratici per la conservazione dei dati e i trasferimenti transfrontalieri.
🎧 Ascolta questa guida
Visualizza trascrizione
- Sintesi Esecutiva
- Approfondimento Tecnico: Architettura del DPDP Act per il WiFi Ospiti
- Il Flusso di Consenso del Captive Portal
- Tracce di Audit del Consenso Immutabili
- Responsabilità del Data Fiduciary vs. Data Processor
- Guida all'Implementazione: Strategie di Deployment
- Fase 1: Disaccoppiamento dell'Autenticazione dal Marketing
- Fase 2: Implementazione del Ciclo di Vita dei Dati
- Fase 3: Gestione dei Trasferimenti Transfrontalieri
- Migliori Pratiche e Standard di Settore
- Risoluzione dei Problemi e Mitigazione del Rischio
- ROI e Impatto sul Business
- Ascolta il Briefing

Sintesi Esecutiva
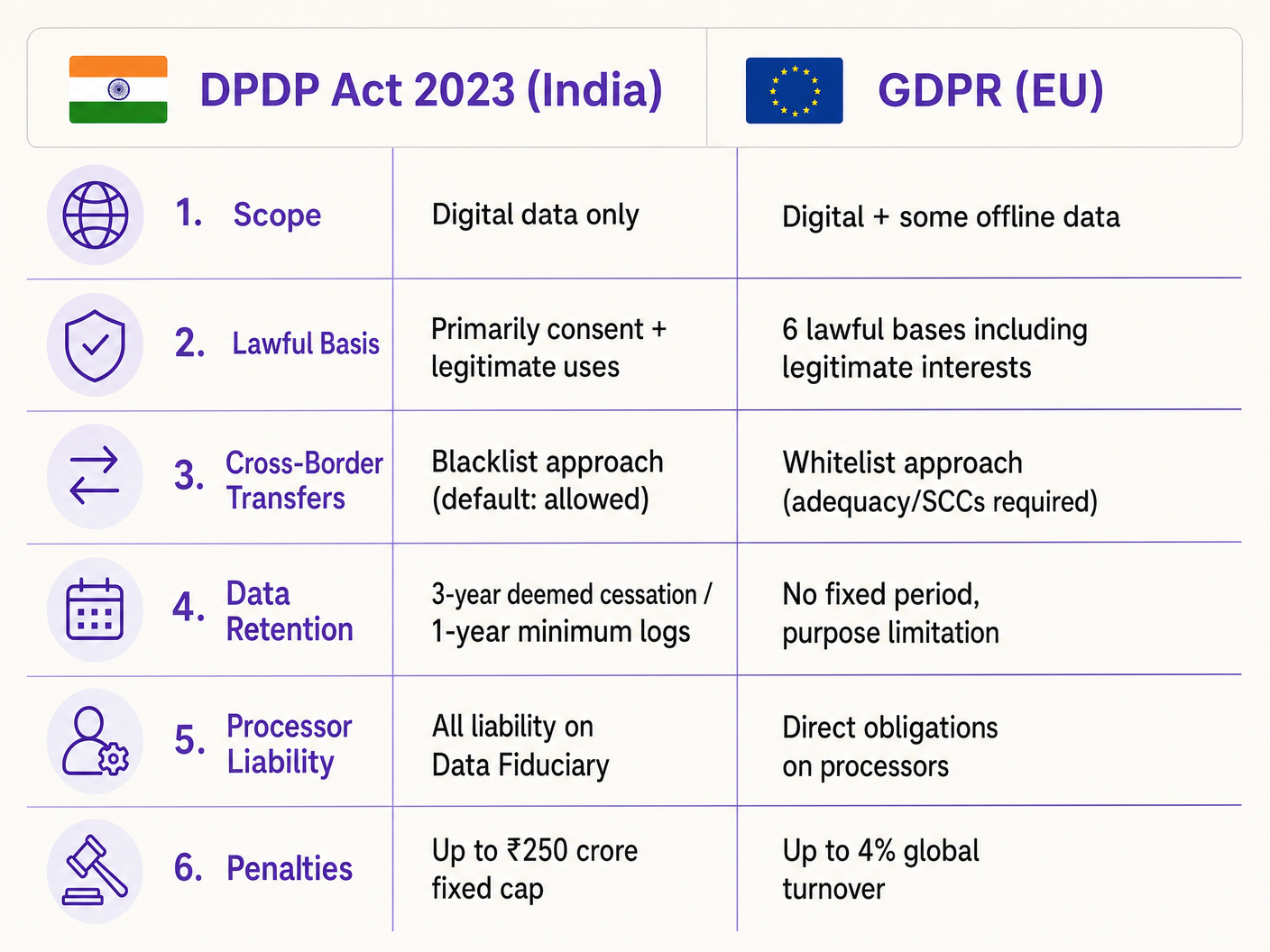
Il Digital Personal Data Protection Act 2023 (DPDP Act) altera fondamentalmente il modo in cui le sedi indiane – dai gruppi alberghieri alle proprietà commerciali – devono gestire i dati del WiFi ospiti. Per i manager IT e gli architetti di rete, questo non è semplicemente un aggiornamento legale; richiede modifiche architettoniche significative ai Captive Portal, ai database di gestione del consenso e all'automazione del ciclo di vita dei dati. A differenza del GDPR, il DPDP Act pone tutta la responsabilità della conformità direttamente sul Data Fiduciary (la sede), il che significa che non è possibile trasferire il rischio al proprio fornitore di piattaforma WiFi. Inoltre, la Legge introduce una rigorosa incondizionalità per il consenso e impone la cancellazione rapida e mirata dei dati. Questa guida fornisce un playbook di conformità neutrale rispetto al fornitore, che descrive in dettaglio l'implementazione tecnica di flussi di consenso granulari, robuste tracce di audit e politiche di conservazione automatizzate necessarie per mitigare i sostanziali rischi finanziari associati alla non conformità.
Approfondimento Tecnico: Architettura del DPDP Act per il WiFi Ospiti
L'implementazione della conformità al DPDP per il WiFi ospiti richiede un passaggio dalla raccolta passiva dei dati alla gestione attiva e verificabile del consenso. L'architettura tecnica deve supportare l'acquisizione granulare del consenso, tracce di audit immutabili e la gestione automatizzata del ciclo di vita dei dati.
Il Flusso di Consenso del Captive Portal
Il tradizionale Captive Portal "clicca per accettare i termini" è obsoleto ai sensi della Sezione 6 del DPDP. Il consenso deve essere "libero, specifico, informato, incondizionato e inequivocabile". Il requisito del consenso incondizionato significa che le sedi non possono rendere le comunicazioni di marketing un prerequisito per l'accesso alla rete.
Quando un ospite si connette all'SSID e il Captive Network Assistant (CNA) attiva il portale, il flusso architettonico deve garantire la conformità prima di concedere il token di autenticazione RADIUS.
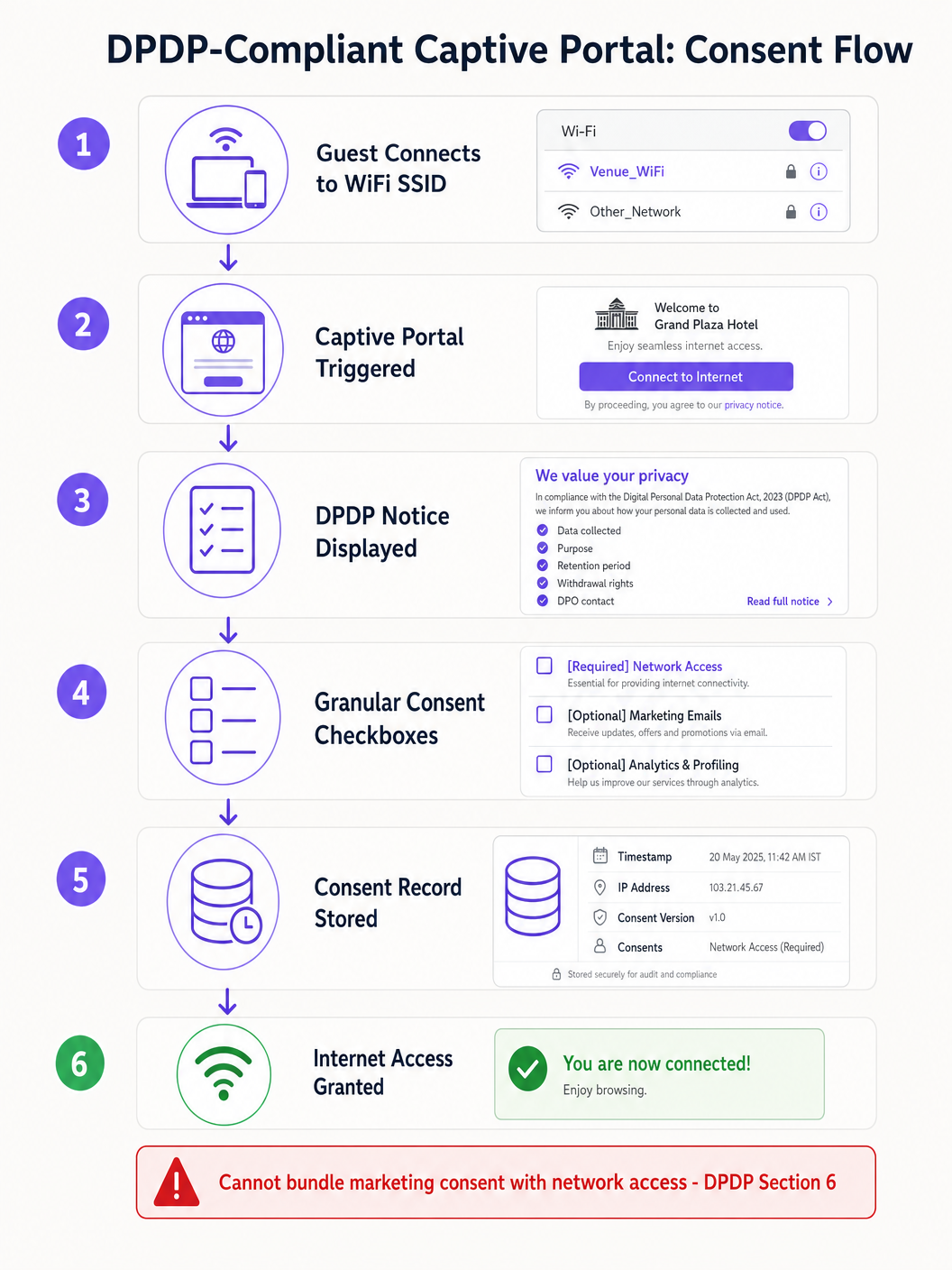
L'implementazione tecnica deve tenere conto delle limitazioni del CNA. Ad esempio, Apple CNA, Android Connectivity Check, Microsoft NCSI: Come funziona realmente il rilevamento del Captive Portal spiega che l'ambiente mini-browser spesso limita i cookie e i reindirizzamenti. Pertanto, lo stato del consenso deve essere trasmesso e archiviato in modo sicuro lato server rispetto all'indirizzo MAC del dispositivo o all'identificatore utente immediatamente dopo l'invio del modulo, prima che la finestra CNA venga chiusa.
Tracce di Audit del Consenso Immutabili
Se il Garante per la Protezione dei Dati indaga su un reclamo, la sede deve dimostrare che un determinato Titolare dei Dati ha acconsentito a un trattamento specifico in una data specifica. Il database della piattaforma WiFi deve mantenere una traccia di audit immutabile. Ogni record di consenso dovrebbe includere:
- Un identificatore di sessione univoco.
- Il timestamp (in IST).
- L'indirizzo IP del client e l'indirizzo MAC.
- La versione specifica dell'informativa sulla privacy visualizzata.
- Gli scopi esatti a cui si è acconsentito (es. accesso alla rete vs. marketing).
Responsabilità del Data Fiduciary vs. Data Processor
Ai sensi della Sezione 8 del DPDP, la sede agisce come Data Fiduciary, mentre il fornitore WiFi (es. Purple) agisce come Data Processor. Fondamentalmente, il Data Fiduciary si assume una responsabilità assoluta e non delegabile per la conformità. La Sezione 8(2) impone un contratto valido con il Data Processor. I direttori IT devono verificare i loro accordi con i fornitori per assicurarsi che contengano addendum specifici per il trattamento dei dati DPDP, poiché fare affidamento su contratti legacy espone la sede a gravi sanzioni.
Guida all'Implementazione: Strategie di Deployment
Il deployment di una soluzione WiFi ospiti conforme al DPDP richiede il coordinamento dell'infrastruttura di rete, della gestione delle identità e dei sistemi di automazione del marketing.
Fase 1: Disaccoppiamento dell'Autenticazione dal Marketing
Lo strato di autenticazione (RADIUS/802.1X) deve essere logicamente separato dal database di marketing. Quando un utente si autentica, il sistema deve controllare i flag di consenso. Se l'utente ha acconsentito solo all'accesso alla rete, i suoi dati di identità devono essere isolati e impediti di sincronizzarsi con il CRM o le piattaforme di automazione del marketing.
Fase 2: Implementazione del Ciclo di Vita dei Dati
La Sezione 8(7) del DPDP richiede la cancellazione dei dati quando lo scopo specificato non è più servito o il consenso viene ritirato. Per gli operatori di sedi, la definizione di "cessazione dello scopo" richiede flussi di lavoro automatizzati.
Ad esempio, in un ambiente Retail che utilizza WiFi Analytics , se un cliente non si è connesso alla rete per 24 mesi, uno script automatizzato dovrebbe attivare un flusso di lavoro di soft-delete. La Regola 8(3) complica questo aspetto richiedendo che i log di elaborazione siano conservati per un minimo di un anno. Pertanto, l'architettura del database deve supportare la cancellazione a livelli: rimozione delle informazioni di identificazione personale (PII) mantenendo i log di connessione anonimizzati per scopi di audit.
Fase 3: Gestione dei Trasferimenti Transfrontalieri
A differenza dei complessi meccanismi di adeguatezza del GDPR, la Sezione 16 del DPDP utilizza un approccio a "lista nera". I trasferimenti di dati al di fuori dell'India sono consentiti per impostazione predefinita, a meno che il Governo Centrale non limiti esplicitamente un paese specifico. Per gli architetti IT che implementano controller WiFi gestiti in cloud (es. Cisco Aruba, Meraki) o piattaforme di analisi ospitate in regioni AWS/Azure al di fuori dell'India, questo attualmente riduce l'attrito. Tuttavia, le architetture dovrebbero rimanere sufficientemente agili da migrare la residenza dei dati se le notifiche governative cambiano.
Migliori Pratiche e Standard di Settore
Quando si progetta per la conformità, affidarsi a standard consolidati piuttosto che a soluzioni personalizzate.
- Anonimizzazione al Confine: Per il conteggio degli accessi e Indoor Positioning Systems , implementare l'hashing degli indirizzi MAC a livello di punto di accesso prima che i dati raggiungano il controller cloud. Se i dati sono realmente anonimizzati, rientrano al di fuori dell'ambito del DPDP.
- Gestione Centralizzata del Consenso: Non fare affidamento sulla piattaforma WiFi come unica fonte di verità se l'utente interagisce con la sede tramite altri canali (ad esempio, un motore di prenotazione alberghiero). Implementare una master consent API che sincronizzi le preferenze attraverso lo stack.
- Integrazioni API Sicure: Assicurarsi che tutti i trasferimenti di dati tra la piattaforma Guest WiFi e i sistemi a valle utilizzino TLS 1.3 e richiedano la rotazione delle chiavi API, allineandosi ai principi PCI DSS e ISO 27001.
Risoluzione dei Problemi e Mitigazione del Rischio
Le modalità di fallimento nelle implementazioni di conformità derivano spesso da lacune nell'integrazione dei sistemi piuttosto che dalla piattaforma WiFi principale.
Modalità di Fallimento Comune: Dati Orfani nei Sistemi a Valle Quando un utente ritira il consenso tramite il captive portal, la piattaforma WiFi aggiorna il suo database. Tuttavia, se il webhook API al CRM fallisce, il team di marketing potrebbe continuare a inviare e-mail all'utente, con conseguente violazione del DPDP. Mitigazione: Implementare una robusta logica di retry per i webhook e script di riconciliazione giornaliera tra il database WiFi e il CRM.
Modalità di Fallimento Comune: Chiusura della CNA Prima della Sincronizzazione del Consenso Gli utenti desiderosi di accedere a internet potrebbero chiudere la finestra CNA di Apple nel momento in cui appare il pulsante "Done", interrompendo potenzialmente la chiamata API che registra le loro preferenze di consenso granulare. Mitigazione: Assicurarsi che il backend del captive portal elabori il payload di consenso in modo asincrono e restituisca il messaggio di successo RADIUS solo dopo che il commit del database è stato confermato.
ROI e Impatto sul Business
Sebbene la conformità al DPDP richieda investimenti, essa porta a significativi benefici operativi. Dati puliti e con consenso verificato migliorano il ROI del marketing assicurando che le campagne mirino solo agli utenti coinvolti, riducendo i tassi di rimbalzo e migliorando la reputazione del mittente. Inoltre, dimostrare una robusta protezione dei dati costruisce fiducia. In settori come Healthcare e Hospitality , dove la sensibilità dei dati è fondamentale, un'esperienza di onboarding WiFi trasparente e conforme diventa un fattore di differenziazione competitivo.
L'impatto finale sul business, tuttavia, è la mitigazione del rischio. Con sanzioni DPDP che raggiungono fino a ₹250 crore per fallimenti di sicurezza, il costo di architettare una soluzione conforme è trascurabile rispetto all'esposizione normativa.
Ascolta il Briefing
Per una panoramica concisa di questi requisiti, ascolta il nostro briefing tecnico in podcast:
Termini chiave e definizioni
Data Fiduciary
The entity that determines the purpose and means of processing personal data.
In the context of guest WiFi, the venue operator (e.g., the hotel or mall) is the Data Fiduciary and holds all legal liability.
Data Processor
Any person who processes personal data on behalf of a Data Fiduciary.
The WiFi platform vendor (like Purple) acts as the Data Processor and must operate under a strict contract.
Data Principal
The individual to whom the personal data relates.
The guest or customer connecting to the WiFi network.
Unconditional Consent
Consent that is not made contingent on the provision of a good or service.
Venues cannot force guests to accept marketing emails in exchange for free WiFi.
Deemed Cessation
The legal presumption that the purpose for data collection is no longer served after a period of inactivity.
Forces IT teams to implement automated data erasure workflows for inactive WiFi users.
Blacklist Transfer Approach
A regulatory model where cross-border data transfers are allowed by default, unless explicitly restricted.
Simplifies cloud architecture for Indian venues, as they can use foreign data centres unless the government issues a specific restriction.
Captive Network Assistant (CNA)
The mini-browser triggered by mobile operating systems when they detect a captive portal.
CNA limitations require careful technical implementation of consent forms to ensure data is captured reliably before the window closes.
Granular Consent
Providing separate options for different types of data processing.
Required on captive portals to separate necessary network access from optional marketing and analytics.
Casi di studio
A 200-room business hotel in Mumbai wants to offer free guest WiFi. They currently require guests to provide their email address and agree to receive promotional offers before granting internet access. How must they re-architect this flow for DPDP compliance?
The hotel must decouple network access from marketing consent. They should deploy a captive portal with two distinct checkboxes. Checkbox 1 (Required): 'I agree to the terms of service for network access.' Checkbox 2 (Optional, unchecked by default): 'I consent to receive promotional offers via email.' The backend RADIUS server must grant access if only Checkbox 1 is ticked. The system must log the exact consent state (timestamp, IP, and which boxes were ticked) in an immutable database.
A large Indian retail chain uses WiFi probes to track customer footfall and dwell time across 50 stores. They capture device MAC addresses. How should they handle this data under the DPDP Act?
The IT team should implement edge-level anonymisation. The WiFi access points should be configured to hash and salt the MAC addresses before transmitting the data to the central analytics server. If the data is irreversibly anonymised and cannot identify a Data Principal, it falls outside the scope of the DPDP Act. For identified analytics (e.g., tracking a specific registered user's journey), they must obtain explicit consent via the captive portal when the user connects to the network.
Analisi degli scenari
Q1. Your marketing director requests that the captive portal be updated to require users to provide their date of birth to access the WiFi, aiming to build better demographic profiles. How should you, as the IT Director, respond based on DPDP principles?
💡 Suggerimento:Consider the principles of data minimisation and unconditional consent.
Mostra l'approccio consigliato
You should reject the request to make it mandatory. Under the DPDP Act's data minimisation principles, you should only collect data necessary for the specified purpose (providing network access). Date of birth is not required for network routing. Furthermore, making it mandatory violates the 'unconditional' consent rule. You can include the date of birth field, but it must be entirely optional, and the user must be able to connect to the WiFi even if they leave it blank.
Q2. A guest who used your stadium WiFi six months ago emails your support desk demanding that all their personal data be deleted immediately under their DPDP rights. What technical steps must your team take?
💡 Suggerimento:Consider both the primary database and downstream systems, as well as Rule 8(3) exceptions.
Mostra l'approccio consigliato
- Verify the identity of the Data Principal. 2. Locate their record in the WiFi platform's database. 3. Execute a soft-delete or anonymisation of their PII (name, email, phone). 4. Trigger webhooks/APIs to ensure this deletion propagates to any downstream systems (CRM, email marketing platforms). 5. Crucially, under Rule 8(3), you must retain the anonymised processing logs (connection times, data volume) for a minimum of one year from the date of processing for audit purposes. 6. Respond to the user within the mandatory 90-day window confirming the erasure.
Q3. Your multinational hotel group uses a central CRM hosted in a data centre in Singapore. Can you transfer Indian guest WiFi data to this server under the DPDP Act?
💡 Suggerimento:Recall the difference between DPDP's blacklist approach and GDPR's whitelist approach.
Mostra l'approccio consigliato
Yes, you can. The DPDP Act utilizes a 'blacklist' approach for cross-border data transfers. This means transfers are permitted to any country by default, unless the Central Government of India has issued a specific notification restricting transfers to that territory. Since Singapore is not currently restricted, the transfer is legally permissible without requiring complex adequacy mechanisms like Standard Contractual Clauses (SCCs) used under GDPR. However, you must still ensure the data is protected with reasonable security safeguards during transit and at rest.



