India DPDP Act: Guest WiFi Compliance for Indian Venues
This authoritative technical reference guide unpacks the Digital Personal Data Protection (DPDP) Act 2023 for Indian venues operating guest WiFi. It provides actionable compliance strategies, architectural considerations for captive portals, and practical frameworks for data retention and cross-border transfers.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: DPDP Act Architecture for Guest WiFi
- The Captive Portal Consent Flow
- Immutable Consent Audit Trails
- Data Fiduciary vs. Data Processor Liability
- Implementation Guide: Deployment Strategies
- Step 1: Decoupling Authentication from Marketing
- Step 2: Implementing the Data Lifecycle
- Step 3: Handling Cross-Border Transfers
- Best Practices & Industry Standards
- Troubleshooting & Risk Mitigation
- ROI & Business Impact
- Listen to the Briefing

Executive Summary
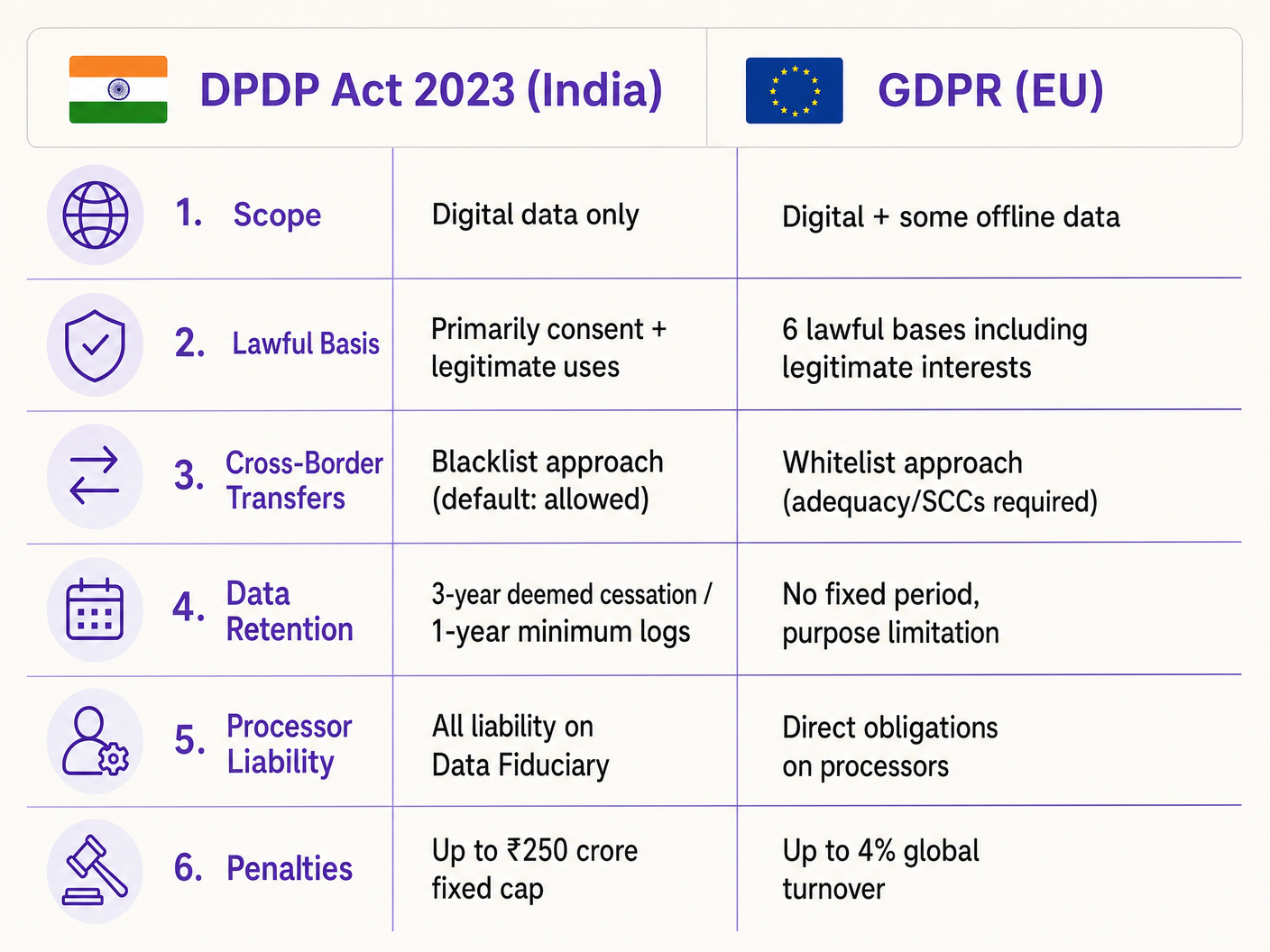
The Digital Personal Data Protection Act 2023 (DPDP Act) fundamentally alters how Indian venues—from hospitality groups to retail estates—must handle guest WiFi data. For IT managers and network architects, this is not merely a legal update; it requires significant architectural changes to captive portals, consent management databases, and data lifecycle automation. Unlike GDPR, the DPDP Act places all compliance liability squarely on the Data Fiduciary (the venue), meaning you cannot transfer risk to your WiFi platform provider. Furthermore, the Act introduces strict unconditionality for consent and mandates rapid, purpose-driven data erasure. This guide provides a vendor-neutral compliance playbook, detailing the technical implementation of granular consent flows, robust audit trails, and automated retention policies required to mitigate the substantial financial risks associated with non-compliance.
Technical Deep-Dive: DPDP Act Architecture for Guest WiFi
Implementing DPDP compliance for guest WiFi requires a shift from passive data collection to active, verifiable consent management. The technical architecture must support granular consent capture, immutable audit trails, and automated data lifecycle management.
The Captive Portal Consent Flow
The traditional "click to accept terms" captive portal is obsolete under DPDP Section 6. Consent must be "free, specific, informed, unconditional, and unambiguous." The requirement for unconditional consent means that venues cannot make marketing communications a prerequisite for network access.
When a guest connects to the SSID and the Captive Network Assistant (CNA) triggers the portal, the architectural flow must ensure compliance before granting the RADIUS authentication token.
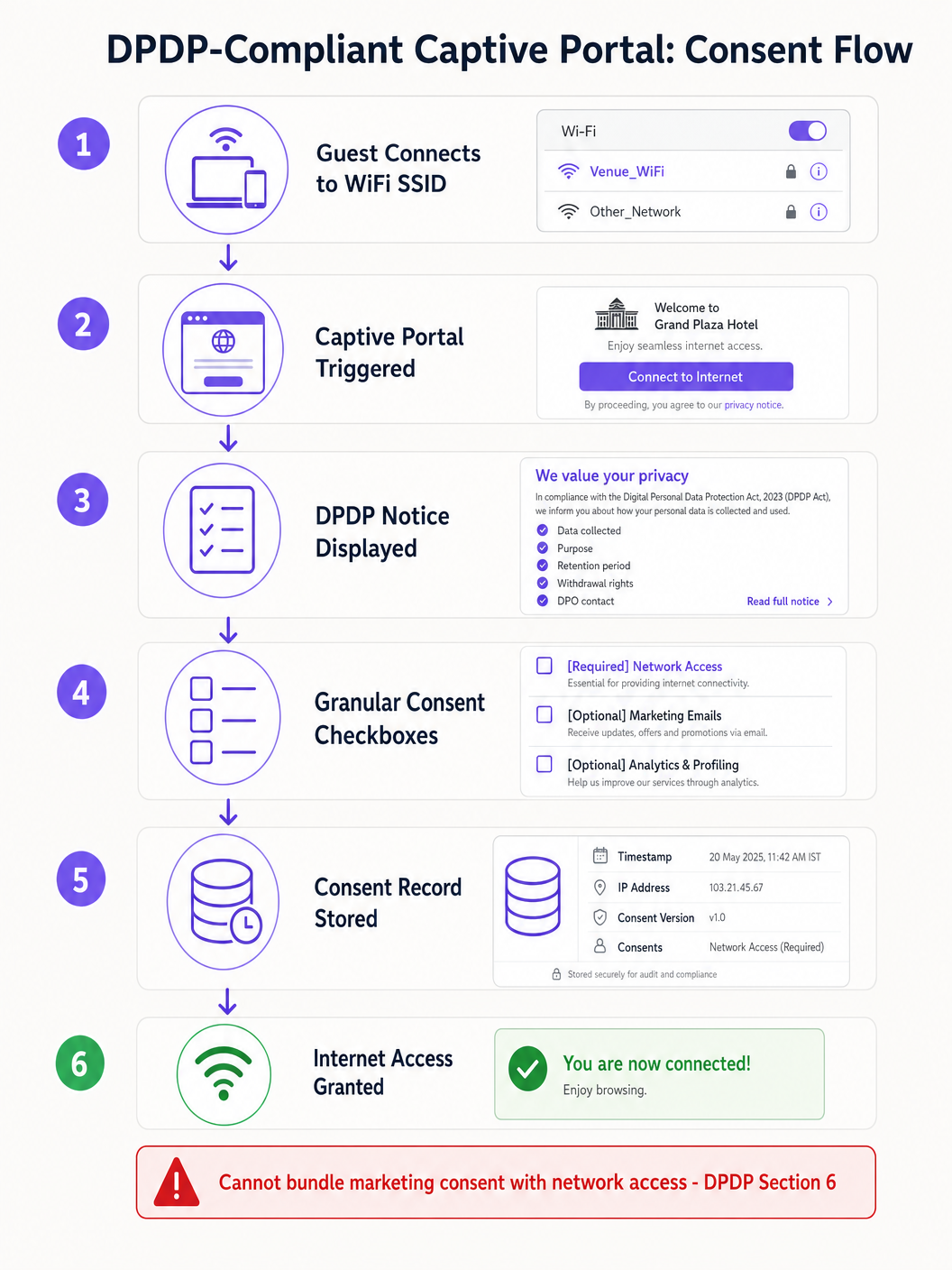
The technical implementation must account for CNA limitations. For instance, Apple CNA, Android Connectivity Check, Microsoft NCSI: How Captive Portal Detection Actually Works explains that the mini-browser environment often restricts cookies and redirects. Therefore, the consent state must be securely transmitted and stored server-side against the device MAC address or user identifier immediately upon form submission, before the CNA window is dismissed.
Immutable Consent Audit Trails
If the Data Protection Board investigates a complaint, the venue must prove that a specific Data Principal consented to specific processing on a specific date. The WiFi platform's database must maintain an immutable audit trail. Each consent record should include:
- A unique session identifier.
- The timestamp (in IST).
- The client IP address and MAC address.
- The specific version of the privacy notice displayed.
- The exact purposes consented to (e.g., network access vs. marketing).
Data Fiduciary vs. Data Processor Liability
Under DPDP Section 8, the venue acts as the Data Fiduciary, while the WiFi vendor (e.g., Purple) acts as the Data Processor. Crucially, the Data Fiduciary bears absolute, non-delegable liability for compliance. Section 8(2) mandates a valid contract with the Data Processor. IT directors must audit their vendor agreements to ensure they contain specific DPDP data processing addendums, as relying on legacy contracts exposes the venue to severe penalties.
Implementation Guide: Deployment Strategies
Deploying a DPDP-compliant guest WiFi solution requires coordinating network infrastructure, identity management, and marketing automation systems.
Step 1: Decoupling Authentication from Marketing
The authentication layer (RADIUS/802.1X) must be logically separated from the marketing database. When a user authenticates, the system must check the consent flags. If the user only consented to network access, their identity data must be isolated and prevented from syncing to the CRM or marketing automation platforms.
Step 2: Implementing the Data Lifecycle
DPDP Section 8(7) requires data erasure when the specified purpose is no longer served or consent is withdrawn. For venue operators, defining "purpose cessation" requires automated workflows.
For example, in a Retail environment using WiFi Analytics , if a customer hasn't connected to the network in 24 months, an automated script should trigger a soft-delete workflow. Rule 8(3) complicates this by requiring processing logs to be retained for a minimum of one year. Therefore, the database architecture must support tiered deletion: removing personally identifiable information (PII) while retaining anonymised connection logs for audit purposes.
Step 3: Handling Cross-Border Transfers
Unlike GDPR's complex adequacy mechanisms, DPDP Section 16 uses a "blacklist" approach. Data transfers outside India are permitted by default unless the Central Government explicitly restricts a specific country. For IT architects deploying cloud-managed WiFi controllers (e.g., Cisco Aruba, Meraki) or analytics platforms hosted in AWS/Azure regions outside India, this currently reduces friction. However, architectures should remain agile enough to migrate data residency if government notifications change.
Best Practices & Industry Standards
When architecting for compliance, rely on established standards rather than bespoke workarounds.
- Anonymisation at the Edge: For footfall counting and Indoor Positioning Systems , implement MAC address hashing at the access point level before data reaches the cloud controller. If the data is genuinely anonymised, it falls outside DPDP scope.
- Centralised Consent Management: Do not rely on the WiFi platform as the sole source of truth if the user interacts with the venue through other channels (e.g., a hotel booking engine). Implement a master consent API that syncs preferences across the stack.
- Secure API Integrations: Ensure all data transfers between the Guest WiFi platform and downstream systems use TLS 1.3 and require API key rotation, aligning with PCI DSS and ISO 27001 principles.
Troubleshooting & Risk Mitigation
Failure modes in compliance deployments often stem from system integration gaps rather than the core WiFi platform.
Common Failure Mode: Orphaned Data in Downstream Systems When a user withdraws consent via the captive portal, the WiFi platform updates its database. However, if the API webhook to the CRM fails, the marketing team may continue emailing the user, resulting in a DPDP violation. Mitigation: Implement robust webhook retry logic and daily reconciliation scripts between the WiFi database and the CRM.
Common Failure Mode: CNA Dismissal Before Consent Sync Users eager for internet access may close the Apple CNA window the moment the "Done" button appears, potentially interrupting the API call that logs their granular consent preferences. Mitigation: Ensure the captive portal backend processes the consent payload asynchronously and returns the RADIUS success message only after the database commit is confirmed.
ROI & Business Impact
While DPDP compliance requires investment, it drives significant operational benefits. Clean, consent-verified data improves marketing ROI by ensuring campaigns only target engaged users, reducing bounce rates and improving sender reputation. Furthermore, demonstrating robust data protection builds trust. In sectors like Healthcare and Hospitality , where data sensitivity is paramount, a transparent, compliant WiFi onboarding experience becomes a competitive differentiator.
The ultimate business impact, however, is risk mitigation. With DPDP penalties reaching up to ₹250 crore for security failures, the cost of architecting a compliant solution is negligible compared to the regulatory exposure.
Listen to the Briefing
For a concise overview of these requirements, listen to our technical podcast briefing:
Key Terms & Definitions
Data Fiduciary
The entity that determines the purpose and means of processing personal data.
In the context of guest WiFi, the venue operator (e.g., the hotel or mall) is the Data Fiduciary and holds all legal liability.
Data Processor
Any person who processes personal data on behalf of a Data Fiduciary.
The WiFi platform vendor (like Purple) acts as the Data Processor and must operate under a strict contract.
Data Principal
The individual to whom the personal data relates.
The guest or customer connecting to the WiFi network.
Unconditional Consent
Consent that is not made contingent on the provision of a good or service.
Venues cannot force guests to accept marketing emails in exchange for free WiFi.
Deemed Cessation
The legal presumption that the purpose for data collection is no longer served after a period of inactivity.
Forces IT teams to implement automated data erasure workflows for inactive WiFi users.
Blacklist Transfer Approach
A regulatory model where cross-border data transfers are allowed by default, unless explicitly restricted.
Simplifies cloud architecture for Indian venues, as they can use foreign data centres unless the government issues a specific restriction.
Captive Network Assistant (CNA)
The mini-browser triggered by mobile operating systems when they detect a captive portal.
CNA limitations require careful technical implementation of consent forms to ensure data is captured reliably before the window closes.
Granular Consent
Providing separate options for different types of data processing.
Required on captive portals to separate necessary network access from optional marketing and analytics.
Case Studies
A 200-room business hotel in Mumbai wants to offer free guest WiFi. They currently require guests to provide their email address and agree to receive promotional offers before granting internet access. How must they re-architect this flow for DPDP compliance?
The hotel must decouple network access from marketing consent. They should deploy a captive portal with two distinct checkboxes. Checkbox 1 (Required): 'I agree to the terms of service for network access.' Checkbox 2 (Optional, unchecked by default): 'I consent to receive promotional offers via email.' The backend RADIUS server must grant access if only Checkbox 1 is ticked. The system must log the exact consent state (timestamp, IP, and which boxes were ticked) in an immutable database.
A large Indian retail chain uses WiFi probes to track customer footfall and dwell time across 50 stores. They capture device MAC addresses. How should they handle this data under the DPDP Act?
The IT team should implement edge-level anonymisation. The WiFi access points should be configured to hash and salt the MAC addresses before transmitting the data to the central analytics server. If the data is irreversibly anonymised and cannot identify a Data Principal, it falls outside the scope of the DPDP Act. For identified analytics (e.g., tracking a specific registered user's journey), they must obtain explicit consent via the captive portal when the user connects to the network.
Scenario Analysis
Q1. Your marketing director requests that the captive portal be updated to require users to provide their date of birth to access the WiFi, aiming to build better demographic profiles. How should you, as the IT Director, respond based on DPDP principles?
💡 Hint:Consider the principles of data minimisation and unconditional consent.
Show Recommended Approach
You should reject the request to make it mandatory. Under the DPDP Act's data minimisation principles, you should only collect data necessary for the specified purpose (providing network access). Date of birth is not required for network routing. Furthermore, making it mandatory violates the 'unconditional' consent rule. You can include the date of birth field, but it must be entirely optional, and the user must be able to connect to the WiFi even if they leave it blank.
Q2. A guest who used your stadium WiFi six months ago emails your support desk demanding that all their personal data be deleted immediately under their DPDP rights. What technical steps must your team take?
💡 Hint:Consider both the primary database and downstream systems, as well as Rule 8(3) exceptions.
Show Recommended Approach
- Verify the identity of the Data Principal. 2. Locate their record in the WiFi platform's database. 3. Execute a soft-delete or anonymisation of their PII (name, email, phone). 4. Trigger webhooks/APIs to ensure this deletion propagates to any downstream systems (CRM, email marketing platforms). 5. Crucially, under Rule 8(3), you must retain the anonymised processing logs (connection times, data volume) for a minimum of one year from the date of processing for audit purposes. 6. Respond to the user within the mandatory 90-day window confirming the erasure.
Q3. Your multinational hotel group uses a central CRM hosted in a data centre in Singapore. Can you transfer Indian guest WiFi data to this server under the DPDP Act?
💡 Hint:Recall the difference between DPDP's blacklist approach and GDPR's whitelist approach.
Show Recommended Approach
Yes, you can. The DPDP Act utilizes a 'blacklist' approach for cross-border data transfers. This means transfers are permitted to any country by default, unless the Central Government of India has issued a specific notification restricting transfers to that territory. Since Singapore is not currently restricted, the transfer is legally permissible without requiring complex adequacy mechanisms like Standard Contractual Clauses (SCCs) used under GDPR. However, you must still ensure the data is protected with reasonable security safeguards during transit and at rest.



