Ley DPDP de la India: Cumplimiento del WiFi para Invitados en Establecimientos Indios
Esta guía técnica de referencia autorizada desglosa la Ley de Protección de Datos Personales Digitales (DPDP) de 2023 para establecimientos indios que operan WiFi para invitados. Ofrece estrategias de cumplimiento accionables, consideraciones arquitectónicas para captive portals y marcos prácticos para la retención de datos y las transferencias transfronterizas.
🎧 Escuchar esta guía
Ver transcripción
- Resumen Ejecutivo
- Análisis Técnico Detallado: Arquitectura de la Ley DPDP para WiFi para Invitados
- El Flujo de Consentimiento del Captive Portal
- Pistas de Auditoría de Consentimiento Inmutables
- Responsabilidad del Fiduciario de Datos vs. Procesador de Datos
- Guía de Implementación: Estrategias de Despliegue
- Paso 1: Desacoplamiento de la Autenticación del Marketing
- Paso 2: Implementación del Ciclo de Vida de los Datos
- Paso 3: Gestión de Transferencias Transfronterizas
- Mejores Prácticas y Estándares de la Industria
- Solución de Problemas y Mitigación de Riesgos
- ROI e Impacto Empresarial
- Escuche el Resumen

Resumen Ejecutivo
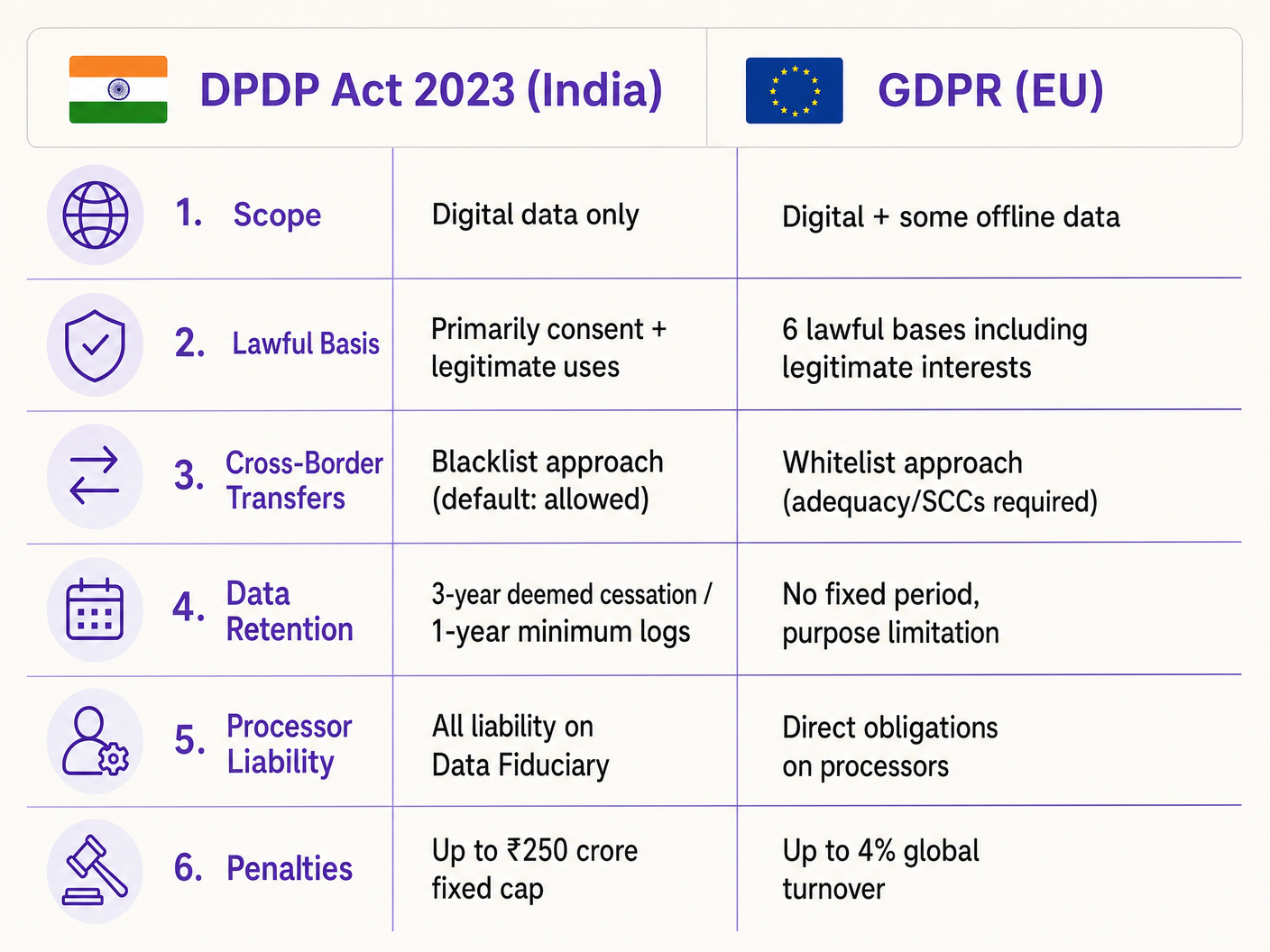
La Ley de Protección de Datos Personales Digitales de 2023 (Ley DPDP) altera fundamentalmente la forma en que los establecimientos indios —desde grupos hoteleros hasta propiedades minoristas— deben gestionar los datos del WiFi para invitados. Para los gerentes de TI y arquitectos de red, esto no es meramente una actualización legal; requiere cambios arquitectónicos significativos en los captive portals, las bases de datos de gestión de consentimiento y la automatización del ciclo de vida de los datos. A diferencia del GDPR, la Ley DPDP sitúa toda la responsabilidad del cumplimiento directamente en el Fiduciario de Datos (el establecimiento), lo que significa que no se puede transferir el riesgo al proveedor de la plataforma WiFi. Además, la Ley introduce una estricta incondicionalidad para el consentimiento y exige la eliminación rápida y orientada a un propósito de los datos. Esta guía proporciona un manual de cumplimiento neutral para proveedores, detallando la implementación técnica de flujos de consentimiento granulares, sólidas pistas de auditoría y políticas de retención automatizadas necesarias para mitigar los sustanciales riesgos financieros asociados con el incumplimiento.
Análisis Técnico Detallado: Arquitectura de la Ley DPDP para WiFi para Invitados
La implementación del cumplimiento de la Ley DPDP para el WiFi para invitados requiere un cambio de la recopilación pasiva de datos a una gestión de consentimiento activa y verificable. La arquitectura técnica debe soportar la captura de consentimiento granular, pistas de auditoría inmutables y la gestión automatizada del ciclo de vida de los datos.
El Flujo de Consentimiento del Captive Portal
El captive portal tradicional de "clic para aceptar los términos" está obsoleto bajo la Sección 6 de la Ley DPDP. El consentimiento debe ser "libre, específico, informado, incondicional e inequívoco". El requisito de consentimiento incondicional significa que los establecimientos no pueden hacer de las comunicaciones de marketing un requisito previo para el acceso a la red.
Cuando un invitado se conecta al SSID y el Asistente de Red Cautiva (CNA) activa el portal, el flujo arquitectónico debe asegurar el cumplimiento antes de otorgar el token de autenticación RADIUS.
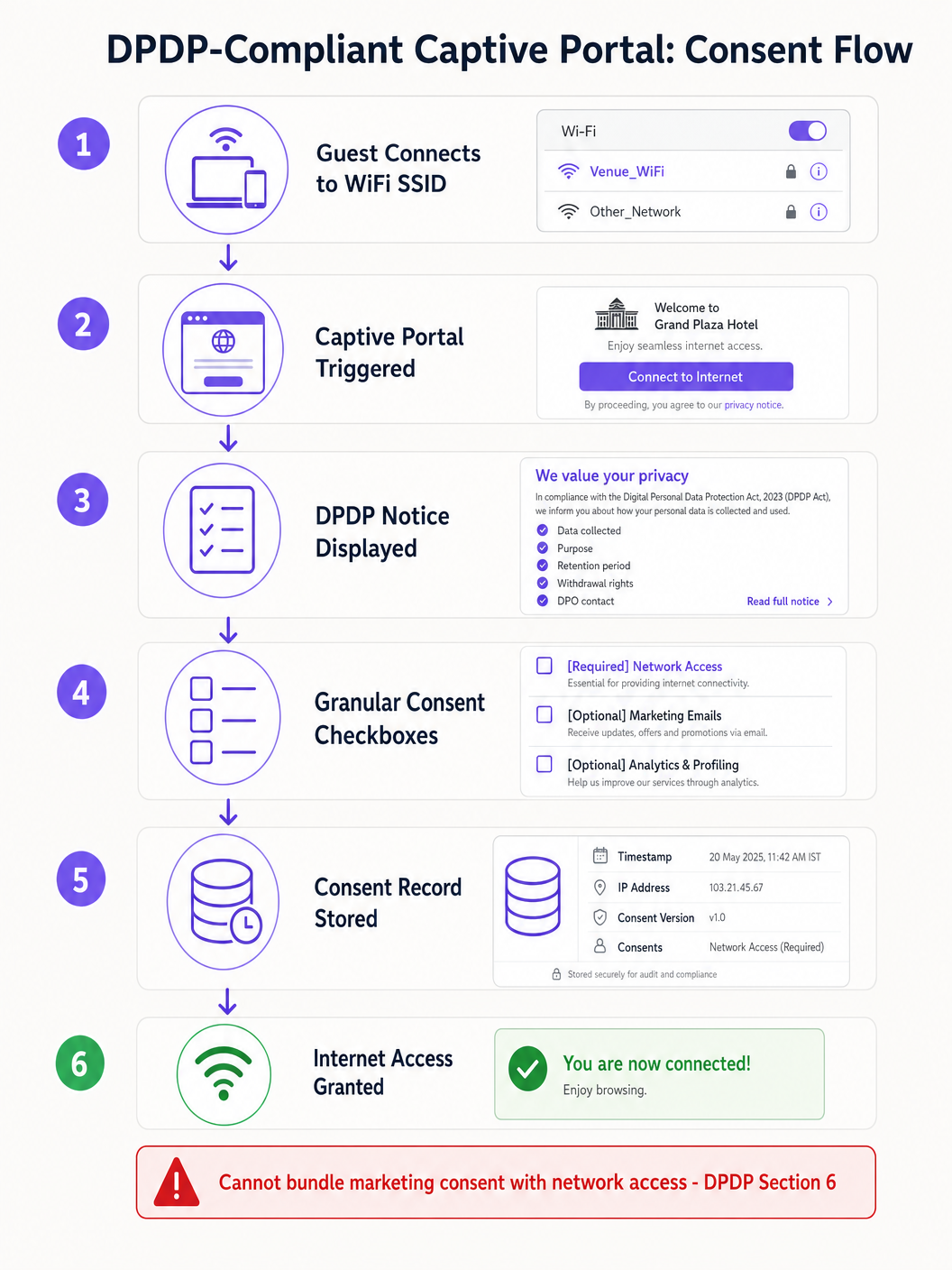
La implementación técnica debe tener en cuenta las limitaciones del CNA. Por ejemplo, Apple CNA, Android Connectivity Check, Microsoft NCSI: Cómo funciona realmente la detección de Captive Portal explica que el entorno del mini-navegador a menudo restringe las cookies y las redirecciones. Por lo tanto, el estado del consentimiento debe transmitirse y almacenarse de forma segura en el lado del servidor, asociado a la dirección MAC del dispositivo o al identificador de usuario, inmediatamente después del envío del formulario, antes de que se cierre la ventana del CNA.
Pistas de Auditoría de Consentimiento Inmutables
Si la Junta de Protección de Datos investiga una queja, el establecimiento debe demostrar que un Titular de Datos específico consintió un procesamiento específico en una fecha determinada. La base de datos de la plataforma WiFi debe mantener una pista de auditoría inmutable. Cada registro de consentimiento debe incluir:
- Un identificador de sesión único.
- La marca de tiempo (en IST).
- La dirección IP del cliente y la dirección MAC.
- La versión específica del aviso de privacidad mostrado.
- Los propósitos exactos consentidos (por ejemplo, acceso a la red frente a marketing).
Responsabilidad del Fiduciario de Datos vs. Procesador de Datos
Según la Sección 8 de la Ley DPDP, el establecimiento actúa como Fiduciario de Datos, mientras que el proveedor de WiFi (por ejemplo, Purple) actúa como Procesador de Datos. Crucialmente, el Fiduciario de Datos asume una responsabilidad absoluta e indelegable por el cumplimiento. La Sección 8(2) exige un contrato válido con el Procesador de Datos. Los directores de TI deben auditar sus acuerdos con los proveedores para asegurarse de que contengan adendas específicas de procesamiento de datos de la Ley DPDP, ya que depender de contratos heredados expone al establecimiento a sanciones severas.
Guía de Implementación: Estrategias de Despliegue
El despliegue de una solución de WiFi para invitados que cumpla con la Ley DPDP requiere la coordinación de la infraestructura de red, la gestión de identidades y los sistemas de automatización de marketing.
Paso 1: Desacoplamiento de la Autenticación del Marketing
La capa de autenticación (RADIUS/802.1X) debe estar lógicamente separada de la base de datos de marketing. Cuando un usuario se autentica, el sistema debe verificar las banderas de consentimiento. Si el usuario solo consintió el acceso a la red, sus datos de identidad deben ser aislados y se debe evitar que se sincronicen con el CRM o las plataformas de automatización de marketing.
Paso 2: Implementación del Ciclo de Vida de los Datos
La Sección 8(7) de la Ley DPDP exige la eliminación de datos cuando el propósito especificado ya no se cumple o se retira el consentimiento. Para los operadores de establecimientos, definir la "cesación del propósito" requiere flujos de trabajo automatizados.
Por ejemplo, en un entorno de Retail que utiliza WiFi Analytics , si un cliente no se ha conectado a la red en 24 meses, un script automatizado debería activar un flujo de trabajo de eliminación suave. La Regla 8(3) complica esto al exigir que los registros de procesamiento se conserven durante un mínimo de un año. Por lo tanto, la arquitectura de la base de datos debe soportar la eliminación por niveles: eliminando la información de identificación personal (PII) mientras se conservan los registros de conexión anonimizados para fines de auditoría.
Paso 3: Gestión de Transferencias Transfronterizas
A diferencia de los complejos mecanismos de adecuación del GDPR, la Sección 16 de la Ley DPDP utiliza un enfoque de "lista negra". Las transferencias de datos fuera de la India están permitidas por defecto, a menos que el Gobierno Central restrinja explícitamente un país específico. Para los arquitectos de TI que implementan controladores WiFi gestionados en la nube (por ejemplo, Cisco Aruba, Meraki) o plataformas de análisis alojadas en regiones de AWS/Azure fuera de la India, esto actualmente reduce la fricción. Sin embargo, las arquitecturas deben seguir siendo lo suficientemente ágiles como para migrar la residencia de datos si cambian las notificaciones gubernamentales.
Mejores Prácticas y Estándares de la Industria
Al diseñar para el cumplimiento, confíe en estándares establecidos en lugar de soluciones personalizadas.
- Anonimización en el Borde: Para el conteo de afluencia y Sistema de Posicionamiento Interiors , implemente el hash de direcciones MAC a nivel del punto de acceso antes de que los datos lleguen al controlador en la nube. Si los datos están realmente anonimizados, quedan fuera del alcance de la DPDP.
- Gestión Centralizada del Consentimiento: No confíe en la plataforma WiFi como única fuente de verdad si el usuario interactúa con el lugar a través de otros canales (por ejemplo, un motor de reservas de hotel). Implemente una API maestra de consentimiento que sincronice las preferencias en todo el stack.
- Integraciones Seguras de API: Asegúrese de que todas las transferencias de datos entre la plataforma Guest WiFi y los sistemas posteriores utilicen TLS 1.3 y requieran la rotación de claves API, en línea con los principios PCI DSS e ISO 27001.
Solución de Problemas y Mitigación de Riesgos
Los modos de fallo en las implementaciones de cumplimiento a menudo provienen de lagunas en la integración del sistema, más que de la plataforma WiFi central.
Modo de Fallo Común: Datos Huérfanos en Sistemas Posteriores Cuando un usuario retira el consentimiento a través del captive portal, la plataforma WiFi actualiza su base de datos. Sin embargo, si el webhook de la API al CRM falla, el equipo de marketing puede seguir enviando correos electrónicos al usuario, lo que resulta en una violación de la DPDP. Mitigación: Implemente una lógica robusta de reintento de webhook y scripts de conciliación diarios entre la base de datos WiFi y el CRM.
Modo de Fallo Común: Descarte de CNA Antes de la Sincronización del Consentimiento Los usuarios ansiosos por el acceso a internet pueden cerrar la ventana de Apple CNA en el momento en que aparece el botón "Done", interrumpiendo potencialmente la llamada API que registra sus preferencias de consentimiento granular. Mitigación: Asegúrese de que el backend del captive portal procese la carga útil de consentimiento de forma asíncrona y devuelva el mensaje de éxito RADIUS solo después de que se confirme la confirmación de la base de datos.
ROI e Impacto Empresarial
Aunque el cumplimiento de la DPDP requiere inversión, genera importantes beneficios operativos. Los datos limpios y con consentimiento verificado mejoran el ROI de marketing al garantizar que las campañas solo se dirijan a usuarios comprometidos, reduciendo las tasas de rebote y mejorando la reputación del remitente. Además, demostrar una protección de datos robusta genera confianza. En sectores como Healthcare y Hospitality , donde la sensibilidad de los datos es primordial, una experiencia de incorporación WiFi transparente y conforme a la normativa se convierte en un diferenciador competitivo.
El impacto empresarial final, sin embargo, es la mitigación de riesgos. Con sanciones de la DPDP que alcanzan hasta ₹250 crore por fallos de seguridad, el coste de diseñar una solución conforme a la normativa es insignificante en comparación con la exposición regulatoria.
Escuche el Resumen
Para una visión concisa de estos requisitos, escuche nuestro resumen técnico en podcast:
Términos clave y definiciones
Data Fiduciary
The entity that determines the purpose and means of processing personal data.
In the context of guest WiFi, the venue operator (e.g., the hotel or mall) is the Data Fiduciary and holds all legal liability.
Data Processor
Any person who processes personal data on behalf of a Data Fiduciary.
The WiFi platform vendor (like Purple) acts as the Data Processor and must operate under a strict contract.
Data Principal
The individual to whom the personal data relates.
The guest or customer connecting to the WiFi network.
Unconditional Consent
Consent that is not made contingent on the provision of a good or service.
Venues cannot force guests to accept marketing emails in exchange for free WiFi.
Deemed Cessation
The legal presumption that the purpose for data collection is no longer served after a period of inactivity.
Forces IT teams to implement automated data erasure workflows for inactive WiFi users.
Blacklist Transfer Approach
A regulatory model where cross-border data transfers are allowed by default, unless explicitly restricted.
Simplifies cloud architecture for Indian venues, as they can use foreign data centres unless the government issues a specific restriction.
Captive Network Assistant (CNA)
The mini-browser triggered by mobile operating systems when they detect a captive portal.
CNA limitations require careful technical implementation of consent forms to ensure data is captured reliably before the window closes.
Granular Consent
Providing separate options for different types of data processing.
Required on captive portals to separate necessary network access from optional marketing and analytics.
Casos de éxito
A 200-room business hotel in Mumbai wants to offer free guest WiFi. They currently require guests to provide their email address and agree to receive promotional offers before granting internet access. How must they re-architect this flow for DPDP compliance?
The hotel must decouple network access from marketing consent. They should deploy a captive portal with two distinct checkboxes. Checkbox 1 (Required): 'I agree to the terms of service for network access.' Checkbox 2 (Optional, unchecked by default): 'I consent to receive promotional offers via email.' The backend RADIUS server must grant access if only Checkbox 1 is ticked. The system must log the exact consent state (timestamp, IP, and which boxes were ticked) in an immutable database.
A large Indian retail chain uses WiFi probes to track customer footfall and dwell time across 50 stores. They capture device MAC addresses. How should they handle this data under the DPDP Act?
The IT team should implement edge-level anonymisation. The WiFi access points should be configured to hash and salt the MAC addresses before transmitting the data to the central analytics server. If the data is irreversibly anonymised and cannot identify a Data Principal, it falls outside the scope of the DPDP Act. For identified analytics (e.g., tracking a specific registered user's journey), they must obtain explicit consent via the captive portal when the user connects to the network.
Análisis de escenarios
Q1. Your marketing director requests that the captive portal be updated to require users to provide their date of birth to access the WiFi, aiming to build better demographic profiles. How should you, as the IT Director, respond based on DPDP principles?
💡 Sugerencia:Consider the principles of data minimisation and unconditional consent.
Mostrar enfoque recomendado
You should reject the request to make it mandatory. Under the DPDP Act's data minimisation principles, you should only collect data necessary for the specified purpose (providing network access). Date of birth is not required for network routing. Furthermore, making it mandatory violates the 'unconditional' consent rule. You can include the date of birth field, but it must be entirely optional, and the user must be able to connect to the WiFi even if they leave it blank.
Q2. A guest who used your stadium WiFi six months ago emails your support desk demanding that all their personal data be deleted immediately under their DPDP rights. What technical steps must your team take?
💡 Sugerencia:Consider both the primary database and downstream systems, as well as Rule 8(3) exceptions.
Mostrar enfoque recomendado
- Verify the identity of the Data Principal. 2. Locate their record in the WiFi platform's database. 3. Execute a soft-delete or anonymisation of their PII (name, email, phone). 4. Trigger webhooks/APIs to ensure this deletion propagates to any downstream systems (CRM, email marketing platforms). 5. Crucially, under Rule 8(3), you must retain the anonymised processing logs (connection times, data volume) for a minimum of one year from the date of processing for audit purposes. 6. Respond to the user within the mandatory 90-day window confirming the erasure.
Q3. Your multinational hotel group uses a central CRM hosted in a data centre in Singapore. Can you transfer Indian guest WiFi data to this server under the DPDP Act?
💡 Sugerencia:Recall the difference between DPDP's blacklist approach and GDPR's whitelist approach.
Mostrar enfoque recomendado
Yes, you can. The DPDP Act utilizes a 'blacklist' approach for cross-border data transfers. This means transfers are permitted to any country by default, unless the Central Government of India has issued a specific notification restricting transfers to that territory. Since Singapore is not currently restricted, the transfer is legally permissible without requiring complex adequacy mechanisms like Standard Contractual Clauses (SCCs) used under GDPR. However, you must still ensure the data is protected with reasonable security safeguards during transit and at rest.



