Indisches DPDP-Gesetz: Guest WiFi Compliance für indische Veranstaltungsorte
Dieser maßgebliche technische Leitfaden erläutert das Digital Personal Data Protection (DPDP) Act 2023 für indische Veranstaltungsorte, die Gast-WiFi betreiben. Er bietet umsetzbare Compliance-Strategien, architektonische Überlegungen für Captive Portals und praktische Rahmenwerke für Datenaufbewahrung und grenzüberschreitende Übertragungen.
🎧 Diesen Leitfaden anhören
Transkript anzeigen
- Executive Summary
- Technical Deep-Dive: DPDP Act Architecture for Guest WiFi
- The Captive Portal Consent Flow
- Immutable Consent Audit Trails
- Data Fiduciary vs. Data Processor Liability
- Implementation Guide: Deployment Strategies
- Step 1: Decoupling Authentication from Marketing
- Step 2: Implementing the Data Lifecycle
- Step 3: Handling Cross-Border Transfers
- Best Practices & Industry Standards
- Fehlerbehebung & Risikominderung
- ROI & Geschäftsauswirkungen
- Hören Sie das Briefing

Executive Summary
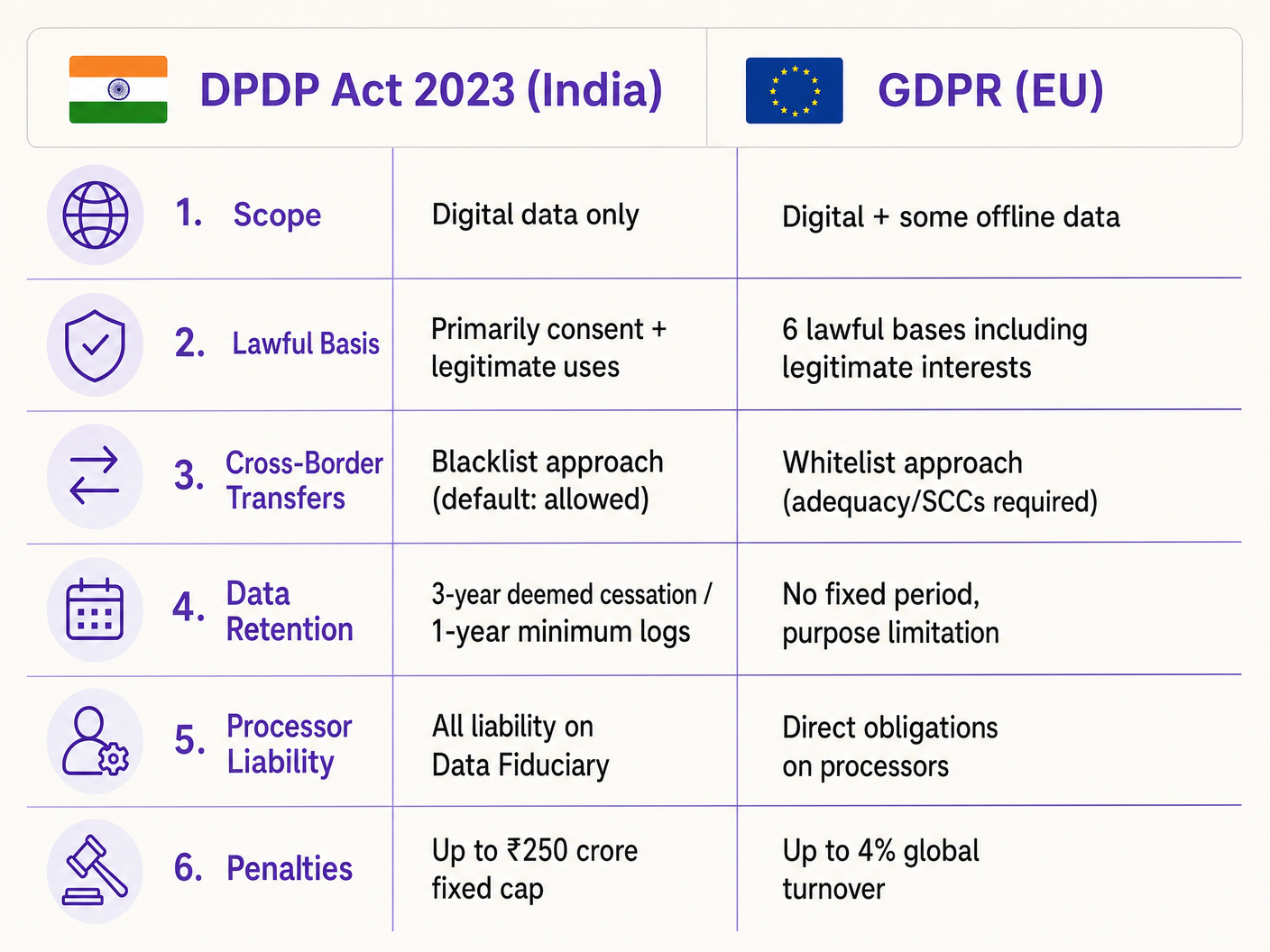
Das Digital Personal Data Protection Act 2023 (DPDP Act) verändert grundlegend, wie indische Veranstaltungsorte – von Hotelgruppen bis hin zu Einzelhandelsimmobilien – mit Gast-WiFi-Daten umgehen müssen. Für IT-Manager und Netzwerkarchitekten ist dies nicht nur ein rechtliches Update; es erfordert erhebliche architektonische Änderungen an Captive Portals, Datenbanken für die Einwilligungsverwaltung und die Automatisierung des Datenlebenszyklus. Im Gegensatz zur GDPR legt das DPDP Act die gesamte Compliance-Haftung direkt auf den Data Fiduciary (den Veranstaltungsort), was bedeutet, dass Sie das Risiko nicht auf Ihren WiFi-Plattformanbieter übertragen können. Darüber hinaus führt das Gesetz eine strikte Bedingungslosigkeit für die Einwilligung ein und schreibt eine schnelle, zweckgebundene Datenlöschung vor. Dieser Leitfaden bietet ein anbieterneutrales Compliance-Playbook, das die technische Implementierung granularer Einwilligungsabläufe, robuster Audit-Trails und automatisierter Aufbewahrungsrichtlinien detailliert beschreibt, die zur Minderung der erheblichen finanziellen Risiken im Zusammenhang mit Nichteinhaltung erforderlich sind.
Technical Deep-Dive: DPDP Act Architecture for Guest WiFi
Die Implementierung der DPDP-Compliance für Gast-WiFi erfordert einen Übergang von passiver Datenerfassung zu aktivem, überprüfbarem Einwilligungsmanagement. Die technische Architektur muss die Erfassung granularer Einwilligungen, unveränderliche Audit-Trails und ein automatisiertes Datenlebenszyklusmanagement unterstützen.
The Captive Portal Consent Flow
Das traditionelle „Klicken zum Akzeptieren der Bedingungen“-Captive Portal ist unter DPDP Section 6 obsolet. Die Einwilligung muss „frei, spezifisch, informiert, bedingungslos und eindeutig“ sein. Die Anforderung einer bedingungslosen Einwilligung bedeutet, dass Veranstaltungsorte Marketingkommunikation nicht zur Voraussetzung für den Netzwerkzugang machen dürfen.
Wenn ein Gast sich mit der SSID verbindet und der Captive Network Assistant (CNA) das Portal auslöst, muss der architektonische Ablauf die Compliance sicherstellen, bevor das RADIUS-Authentifizierungstoken gewährt wird.
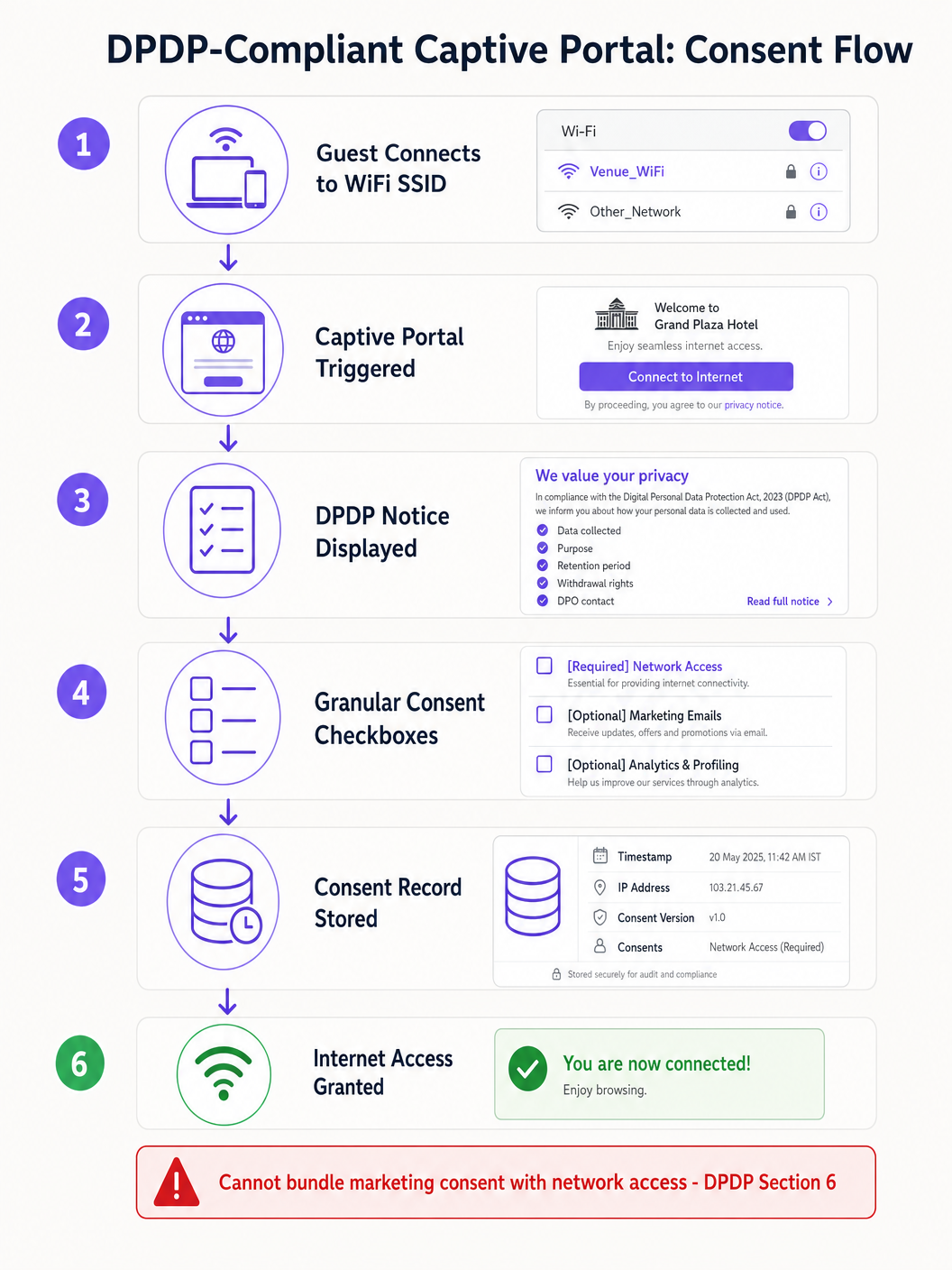
Die technische Implementierung muss CNA-Einschränkungen berücksichtigen. Zum Beispiel erklärt Apple CNA, Android Connectivity Check, Microsoft NCSI: How Captive Portal Detection Actually Works , dass die Mini-Browser-Umgebung oft Cookies und Weiterleitungen einschränkt. Daher muss der Einwilligungsstatus sofort nach dem Absenden des Formulars, bevor das CNA-Fenster geschlossen wird, sicher übertragen und serverseitig gegen die MAC address des Geräts oder die Benutzerkennung gespeichert werden.
Immutable Consent Audit Trails
Wenn das Data Protection Board eine Beschwerde untersucht, muss der Veranstaltungsort nachweisen, dass ein bestimmter Data Principal einer bestimmten Verarbeitung an einem bestimmten Datum zugestimmt hat. Die Datenbank der WiFi-Plattform muss einen unveränderlichen Audit-Trail führen. Jeder Einwilligungsdatensatz sollte Folgendes enthalten:
- Eine eindeutige Sitzungs-ID.
- Den Zeitstempel (in IST).
- Die Client-IP address und MAC address.
- Die spezifische Version des angezeigten Datenschutzhinweises.
- Die genauen Zwecke, denen zugestimmt wurde (z. B. Netzwerkzugang vs. Marketing).
Data Fiduciary vs. Data Processor Liability
Gemäß DPDP Section 8 fungiert der Veranstaltungsort als Data Fiduciary, während der WiFi-Anbieter (z. B. Purple) als Data Processor agiert. Entscheidend ist, dass der Data Fiduciary die absolute, nicht delegierbare Haftung für die Compliance trägt. Section 8(2) schreibt einen gültigen Vertrag mit dem Data Processor vor. IT-Direktoren müssen ihre Anbietervereinbarungen prüfen, um sicherzustellen, dass sie spezifische DPDP-Datenverarbeitungszusätze enthalten, da das Vertrauen auf alte Verträge den Veranstaltungsort schweren Strafen aussetzt.
Implementation Guide: Deployment Strategies
Die Bereitstellung einer DPDP-konformen Gast-WiFi-Lösung erfordert die Koordination von Netzwerkinfrastruktur, Identitätsmanagement und Marketing-Automatisierungssystemen.
Step 1: Decoupling Authentication from Marketing
Die Authentifizierungsschicht (RADIUS/802.1X) muss logisch von der Marketingdatenbank getrennt sein. Wenn ein Benutzer sich authentifiziert, muss das System die Einwilligungs-Flags überprüfen. Wenn der Benutzer nur dem Netzwerkzugang zugestimmt hat, müssen seine Identitätsdaten isoliert und daran gehindert werden, mit dem CRM oder Marketing-Automatisierungsplattformen synchronisiert zu werden.
Step 2: Implementing the Data Lifecycle
DPDP Section 8(7) verlangt die Datenlöschung, wenn der angegebene Zweck nicht mehr erfüllt wird oder die Einwilligung widerrufen wird. Für Veranstaltungsbetreiber erfordert die Definition des „Zweckwegfalls“ automatisierte Workflows.
Zum Beispiel in einer Retail -Umgebung, die WiFi Analytics verwendet: Wenn ein Kunde sich seit 24 Monaten nicht mit dem Netzwerk verbunden hat, sollte ein automatisiertes Skript einen Soft-Delete-Workflow auslösen. Regel 8(3) erschwert dies, indem sie vorschreibt, dass Verarbeitungslogs für mindestens ein Jahr aufbewahrt werden müssen. Daher muss die Datenbankarchitektur eine gestufte Löschung unterstützen: Entfernung von persönlich identifizierbaren Informationen (PII) bei gleichzeitiger Beibehaltung anonymisierter Verbindungslogs für Audit-Zwecke.
Step 3: Handling Cross-Border Transfers
Im Gegensatz zu den komplexen Angemessenheitsmechanismen der GDPR verwendet DPDP Section 16 einen „Blacklist“-Ansatz. Datenübertragungen außerhalb Indiens sind standardmäßig erlaubt, es sei denn, die Zentralregierung schränkt ein bestimmtes Land explizit ein. Für IT-Architekten, die Cloud-verwaltete WiFi-Controller (z. B. Cisco Aruba, Meraki) oder Analyseplattformen, die in AWS/Azure-Regionen außerhalb Indiens gehostet werden, einsetzen, reduziert dies derzeit die Reibung. Architekturen sollten jedoch agil genug bleiben, um die Datenresidenz zu migrieren, falls sich Regierungsmitteilungen ändern.
Best Practices & Industry Standards
Beim Entwurf für Compliance sollten Sie sich auf etablierte Standards verlassen und nicht auf maßgeschneiderte Workarounds.
- Anonymisation at the Edge: Für die Zählung von Besucherzahlen und Indoor Positioning Systems , implementieren Sie MAC-Adressen-Hashing auf der Ebene des Access Points, bevor Daten den Cloud-Controller erreichen. Wenn die Daten wirklich anonymisiert sind, fallen sie nicht in den Geltungsbereich des DPDP.
- Zentralisiertes Einwilligungsmanagement: Verlassen Sie sich nicht ausschließlich auf die WiFi-Plattform als einzige Quelle der Wahrheit, wenn der Nutzer über andere Kanäle (z. B. eine Hotelbuchungsmaschine) mit dem Veranstaltungsort interagiert. Implementieren Sie eine Master-Einwilligungs-API, die Präferenzen über den gesamten Stack hinweg synchronisiert.
- Sichere API-Integrationen: Stellen Sie sicher, dass alle Datentransfers zwischen der Guest WiFi -Plattform und nachgelagerten Systemen TLS 1.3 verwenden und eine API-Schlüsselrotation erfordern, im Einklang mit den Prinzipien von PCI DSS und ISO 27001.
Fehlerbehebung & Risikominderung
Fehlermodi bei Compliance-Implementierungen resultieren oft aus Lücken in der Systemintegration und nicht aus der Kern-WiFi-Plattform.
Häufiger Fehlermodus: Verwaiste Daten in nachgelagerten Systemen Wenn ein Nutzer seine Einwilligung über das captive portal widerruft, aktualisiert die WiFi-Plattform ihre Datenbank. Wenn jedoch der API-Webhook an das CRM fehlschlägt, kann das Marketingteam dem Nutzer weiterhin E-Mails senden, was zu einem DPDP-Verstoß führt. Minderung: Implementieren Sie eine robuste Webhook-Wiederholungslogik und tägliche Abgleichskripte zwischen der WiFi-Datenbank und dem CRM.
Häufiger Fehlermodus: CNA-Schließung vor der Einwilligungssynchronisierung Nutzer, die schnell Internetzugang wünschen, schließen möglicherweise das Apple CNA-Fenster in dem Moment, in dem die Schaltfläche „Fertig“ erscheint, was potenziell den API-Aufruf unterbrechen könnte, der ihre detaillierten Einwilligungseinstellungen protokolliert. Minderung: Stellen Sie sicher, dass das captive portal Backend die Einwilligungs-Payload asynchron verarbeitet und die RADIUS-Erfolgsmeldung erst nach Bestätigung des Datenbank-Commits zurückgibt.
ROI & Geschäftsauswirkungen
Obwohl die DPDP-Compliance Investitionen erfordert, führt sie zu erheblichen operativen Vorteilen. Saubere, einwilligungsgeprüfte Daten verbessern den Marketing-ROI, indem sie sicherstellen, dass Kampagnen nur engagierte Nutzer ansprechen, was Absprungraten reduziert und die Reputation des Absenders verbessert. Darüber hinaus schafft der Nachweis eines robusten Datenschutzes Vertrauen. In Branchen wie Healthcare und Hospitality , wo Datensensibilität von größter Bedeutung ist, wird ein transparentes, konformes WiFi-Onboarding-Erlebnis zu einem Wettbewerbsvorteil.
Der ultimative Geschäftsnutzen ist jedoch die Risikominderung. Da DPDP-Strafen bei Sicherheitsversagen bis zu ₹250 Crore erreichen können, sind die Kosten für die Entwicklung einer konformen Lösung im Vergleich zum regulatorischen Risiko vernachlässigbar.
Hören Sie das Briefing
Für einen prägnanten Überblick über diese Anforderungen hören Sie unser technisches Podcast-Briefing:
Schlüsselbegriffe & Definitionen
Data Fiduciary
The entity that determines the purpose and means of processing personal data.
In the context of guest WiFi, the venue operator (e.g., the hotel or mall) is the Data Fiduciary and holds all legal liability.
Data Processor
Any person who processes personal data on behalf of a Data Fiduciary.
The WiFi platform vendor (like Purple) acts as the Data Processor and must operate under a strict contract.
Data Principal
The individual to whom the personal data relates.
The guest or customer connecting to the WiFi network.
Unconditional Consent
Consent that is not made contingent on the provision of a good or service.
Venues cannot force guests to accept marketing emails in exchange for free WiFi.
Deemed Cessation
The legal presumption that the purpose for data collection is no longer served after a period of inactivity.
Forces IT teams to implement automated data erasure workflows for inactive WiFi users.
Blacklist Transfer Approach
A regulatory model where cross-border data transfers are allowed by default, unless explicitly restricted.
Simplifies cloud architecture for Indian venues, as they can use foreign data centres unless the government issues a specific restriction.
Captive Network Assistant (CNA)
The mini-browser triggered by mobile operating systems when they detect a captive portal.
CNA limitations require careful technical implementation of consent forms to ensure data is captured reliably before the window closes.
Granular Consent
Providing separate options for different types of data processing.
Required on captive portals to separate necessary network access from optional marketing and analytics.
Fallstudien
A 200-room business hotel in Mumbai wants to offer free guest WiFi. They currently require guests to provide their email address and agree to receive promotional offers before granting internet access. How must they re-architect this flow for DPDP compliance?
The hotel must decouple network access from marketing consent. They should deploy a captive portal with two distinct checkboxes. Checkbox 1 (Required): 'I agree to the terms of service for network access.' Checkbox 2 (Optional, unchecked by default): 'I consent to receive promotional offers via email.' The backend RADIUS server must grant access if only Checkbox 1 is ticked. The system must log the exact consent state (timestamp, IP, and which boxes were ticked) in an immutable database.
A large Indian retail chain uses WiFi probes to track customer footfall and dwell time across 50 stores. They capture device MAC addresses. How should they handle this data under the DPDP Act?
The IT team should implement edge-level anonymisation. The WiFi access points should be configured to hash and salt the MAC addresses before transmitting the data to the central analytics server. If the data is irreversibly anonymised and cannot identify a Data Principal, it falls outside the scope of the DPDP Act. For identified analytics (e.g., tracking a specific registered user's journey), they must obtain explicit consent via the captive portal when the user connects to the network.
Szenarioanalyse
Q1. Your marketing director requests that the captive portal be updated to require users to provide their date of birth to access the WiFi, aiming to build better demographic profiles. How should you, as the IT Director, respond based on DPDP principles?
💡 Hinweis:Consider the principles of data minimisation and unconditional consent.
Empfohlenen Ansatz anzeigen
You should reject the request to make it mandatory. Under the DPDP Act's data minimisation principles, you should only collect data necessary for the specified purpose (providing network access). Date of birth is not required for network routing. Furthermore, making it mandatory violates the 'unconditional' consent rule. You can include the date of birth field, but it must be entirely optional, and the user must be able to connect to the WiFi even if they leave it blank.
Q2. A guest who used your stadium WiFi six months ago emails your support desk demanding that all their personal data be deleted immediately under their DPDP rights. What technical steps must your team take?
💡 Hinweis:Consider both the primary database and downstream systems, as well as Rule 8(3) exceptions.
Empfohlenen Ansatz anzeigen
- Verify the identity of the Data Principal. 2. Locate their record in the WiFi platform's database. 3. Execute a soft-delete or anonymisation of their PII (name, email, phone). 4. Trigger webhooks/APIs to ensure this deletion propagates to any downstream systems (CRM, email marketing platforms). 5. Crucially, under Rule 8(3), you must retain the anonymised processing logs (connection times, data volume) for a minimum of one year from the date of processing for audit purposes. 6. Respond to the user within the mandatory 90-day window confirming the erasure.
Q3. Your multinational hotel group uses a central CRM hosted in a data centre in Singapore. Can you transfer Indian guest WiFi data to this server under the DPDP Act?
💡 Hinweis:Recall the difference between DPDP's blacklist approach and GDPR's whitelist approach.
Empfohlenen Ansatz anzeigen
Yes, you can. The DPDP Act utilizes a 'blacklist' approach for cross-border data transfers. This means transfers are permitted to any country by default, unless the Central Government of India has issued a specific notification restricting transfers to that territory. Since Singapore is not currently restricted, the transfer is legally permissible without requiring complex adequacy mechanisms like Standard Contractual Clauses (SCCs) used under GDPR. However, you must still ensure the data is protected with reasonable security safeguards during transit and at rest.



