Loi indienne sur la DPDP : Conformité du WiFi invité pour les établissements indiens
Ce guide de référence technique faisant autorité décortique la loi de 2023 sur la protection des données personnelles numériques (DPDP) pour les établissements indiens exploitant un WiFi invité. Il fournit des stratégies de conformité exploitables, des considérations architecturales pour les Captive Portals et des cadres pratiques pour la conservation des données et les transferts transfrontaliers.
🎧 Écouter ce guide
Voir la transcription
- Résumé Exécutif
- Plongée Technique : Architecture de la DPDP Act pour le WiFi invité
- Le Flux de Consentement du Captive Portal
- Pistes d'Audit de Consentement Immuables
- Responsabilité du Fiduciaire de Données vs. du Sous-traitant de Données
- Guide d'Implémentation : Stratégies de Déploiement
- Étape 1 : Dissocier l'Authentification du Marketing
- Étape 2 : Mettre en œuvre le Cycle de Vie des Données
- Étape 3 : Gérer les Transferts Transfrontaliers
- Bonnes Pratiques et Normes de l'Industrie
- Dépannage et Atténuation des Risques
- ROI et Impact Commercial
- Écoutez le Briefing

Résumé Exécutif
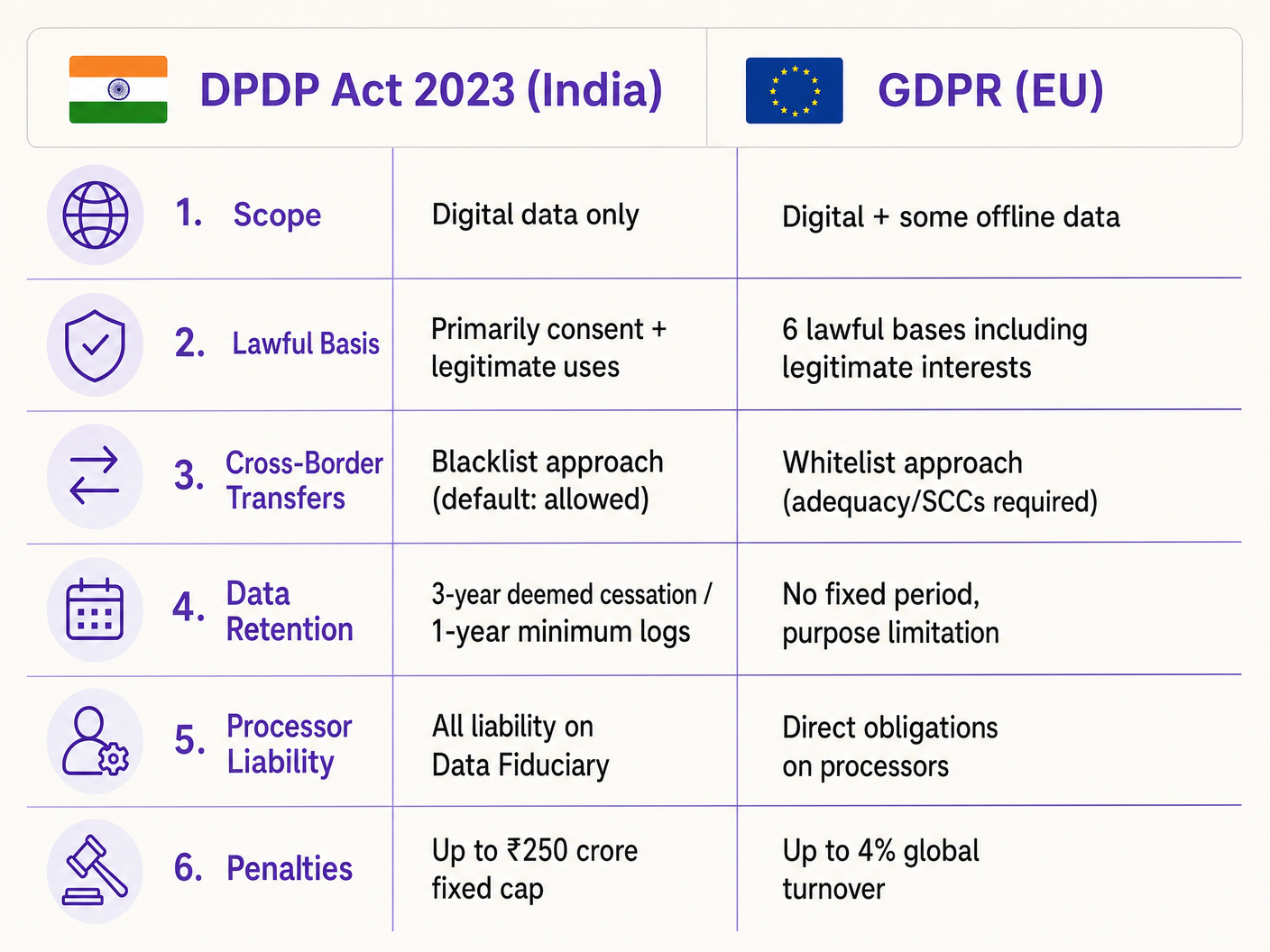
La loi de 2023 sur la protection des données personnelles numériques (DPDP Act) modifie fondamentalement la manière dont les établissements indiens — des groupes hôteliers aux propriétés commerciales — doivent gérer les données du WiFi invité. Pour les responsables informatiques et les architectes réseau, il ne s'agit pas seulement d'une mise à jour juridique ; cela exige des changements architecturaux significatifs aux Captive Portals, aux bases de données de gestion du consentement et à l'automatisation du cycle de vie des données. Contrairement au GDPR, la DPDP Act place toute la responsabilité de la conformité directement sur le Fiduciaire de Données (l'établissement), ce qui signifie que vous ne pouvez pas transférer le risque à votre fournisseur de plateforme WiFi. De plus, la loi introduit une inconditionnalité stricte pour le consentement et exige une suppression rapide des données, axée sur la finalité. Ce guide fournit un manuel de conformité neutre vis-à-vis des fournisseurs, détaillant la mise en œuvre technique de flux de consentement granulaires, de pistes d'audit robustes et de politiques de rétention automatisées nécessaires pour atténuer les risques financiers substantiels associés à la non-conformité.
Plongée Technique : Architecture de la DPDP Act pour le WiFi invité
La mise en œuvre de la conformité DPDP pour le WiFi invité exige un passage de la collecte passive de données à une gestion active et vérifiable du consentement. L'architecture technique doit prendre en charge la capture granulaire du consentement, des pistes d'audit immuables et la gestion automatisée du cycle de vie des données.
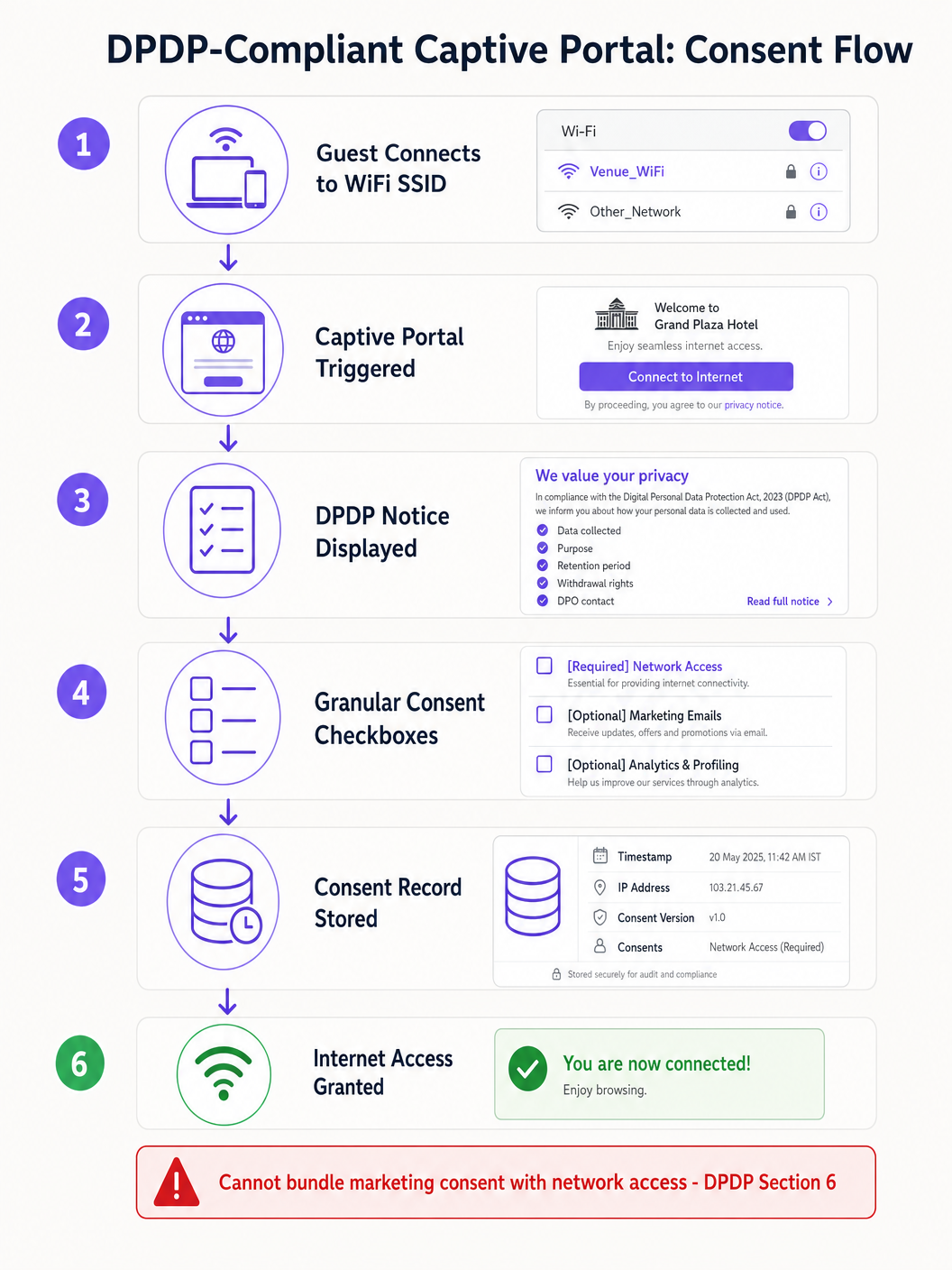
Le Flux de Consentement du Captive Portal
Le Captive Portal traditionnel "cliquer pour accepter les conditions" est obsolète en vertu de la section 6 de la DPDP. Le consentement doit être "libre, spécifique, éclairé, inconditionnel et univoque." L'exigence d'un consentement inconditionnel signifie que les établissements ne peuvent pas faire des communications marketing une condition préalable à l'accès au réseau.
Lorsqu'un invité se connecte au SSID et que le Captive Network Assistant (CNA) déclenche le portail, le flux architectural doit assurer la conformité avant d'accorder le jeton d'authentification RADIUS.
La mise en œuvre technique doit tenir compte des limitations du CNA. Par exemple, Apple CNA, Android Connectivity Check, Microsoft NCSI: How Captive Portal Detection Actually Works explique que l'environnement du mini-navigateur restreint souvent les cookies et les redirections. Par conséquent, l'état du consentement doit être transmis et stocké en toute sécurité côté serveur, associé à l'adresse MAC de l'appareil ou à l'identifiant de l'utilisateur, immédiatement après la soumission du formulaire, avant que la fenêtre CNA ne soit fermée.
Pistes d'Audit de Consentement Immuables
Si le Conseil de Protection des Données enquête sur une plainte, l'établissement doit prouver qu'un Responsable de Données spécifique a consenti à un traitement spécifique à une date spécifique. La base de données de la plateforme WiFi doit maintenir une piste d'audit immuable. Chaque enregistrement de consentement doit inclure :
- Un identifiant de session unique.
- L'horodatage (en IST).
- L'adresse IP du client et l'adresse MAC.
- La version spécifique de l'avis de confidentialité affiché.
- Les finalités exactes auxquelles il a été consenti (par exemple, accès au réseau vs. marketing).
Responsabilité du Fiduciaire de Données vs. du Sous-traitant de Données
En vertu de la section 8 de la DPDP, l'établissement agit en tant que Fiduciaire de Données, tandis que le fournisseur WiFi (par exemple, Purple) agit en tant que Sous-traitant de Données. Il est crucial que le Fiduciaire de Données assume une responsabilité absolue et non délégable en matière de conformité. La section 8(2) exige un contrat valide avec le Sous-traitant de Données. Les directeurs informatiques doivent auditer leurs accords avec les fournisseurs pour s'assurer qu'ils contiennent des avenants spécifiques au traitement des données DPDP, car s'appuyer sur des contrats existants expose l'établissement à de lourdes sanctions.
Guide d'Implémentation : Stratégies de Déploiement
Le déploiement d'une solution WiFi invité conforme à la DPDP exige la coordination de l'infrastructure réseau, de la gestion des identités et des systèmes d'automatisation marketing.
Étape 1 : Dissocier l'Authentification du Marketing
La couche d'authentification (RADIUS/802.1X) doit être logiquement séparée de la base de données marketing. Lorsqu'un utilisateur s'authentifie, le système doit vérifier les indicateurs de consentement. Si l'utilisateur n'a consenti qu'à l'accès au réseau, ses données d'identité doivent être isolées et empêchées de se synchroniser avec le CRM ou les plateformes d'automatisation marketing.
Étape 2 : Mettre en œuvre le Cycle de Vie des Données
La section 8(7) de la DPDP exige la suppression des données lorsque la finalité spécifiée n'est plus servie ou que le consentement est retiré. Pour les opérateurs d'établissements, la définition de la "cessation de la finalité" nécessite des flux de travail automatisés.
Par exemple, dans un environnement de Commerce de détail utilisant l'Analyse WiFi , si un client ne s'est pas connecté au réseau depuis 24 mois, un script automatisé devrait déclencher un flux de travail de suppression douce. La règle 8(3) complique cela en exigeant que les journaux de traitement soient conservés pendant un minimum d'un an. Par conséquent, l'architecture de la base de données doit prendre en charge la suppression échelonnée : suppression des informations personnellement identifiables (PII) tout en conservant les journaux de connexion anonymisés à des fins d'audit.
Étape 3 : Gérer les Transferts Transfrontaliers
Contrairement aux mécanismes complexes d'adéquation du GDPR, la section 16 de la DPDP utilise une approche de "liste noire". Les transferts de données en dehors de l'Inde sont autorisés par défaut, à moins que le gouvernement central ne restreigne explicitement un pays spécifique. Pour les architectes informatiques déployant des contrôleurs WiFi gérés dans le cloud (par exemple, Cisco Aruba, Meraki) ou des plateformes d'analyse hébergées dans des régions AWS/Azure en dehors de l'Inde, cela réduit actuellement les frictions. Cependant, les architectures doivent rester suffisamment agiles pour migrer la résidence des données si les notifications gouvernementales changent.
Bonnes Pratiques et Normes de l'Industrie
Lors de la conception pour la conformité, appuyez-vous sur des normes établies plutôt que sur des solutions de contournement sur mesure.
- Anonymisation en périphérie : Pour le comptage de la fréquentation et les Systèmes de Positionnement Intérieurs , implémentez le hachage des adresses MAC au niveau du point d'accès avant que les données n'atteignent le contrôleur cloud. Si les données sont véritablement anonymisées, elles ne relèvent pas du champ d'application du DPDP.
- Gestion Centralisée du Consentement : Ne vous fiez pas à la plateforme WiFi comme seule source de vérité si l'utilisateur interagit avec le lieu via d'autres canaux (par exemple, un moteur de réservation d'hôtel). Implémentez une API de consentement maître qui synchronise les préférences sur l'ensemble de la pile.
- Intégrations API Sécurisées : Assurez-vous que tous les transferts de données entre la plateforme Guest WiFi et les systèmes en aval utilisent TLS 1.3 et nécessitent une rotation des clés API, conformément aux principes PCI DSS et ISO 27001.
Dépannage et Atténuation des Risques
Les modes de défaillance dans les déploiements de conformité proviennent souvent de lacunes dans l'intégration des systèmes plutôt que de la plateforme WiFi elle-même.
Mode de Défaillance Courant : Données Orphelines dans les Systèmes en Aval Lorsqu'un utilisateur retire son consentement via le captive portal, la plateforme WiFi met à jour sa base de données. Cependant, si le webhook API vers le CRM échoue, l'équipe marketing peut continuer à envoyer des e-mails à l'utilisateur, entraînant une violation du DPDP. Atténuation : Implémentez une logique de nouvelle tentative de webhook robuste et des scripts de réconciliation quotidiens entre la base de données WiFi et le CRM.
Mode de Défaillance Courant : Rejet du CNA avant la Synchronisation du Consentement Les utilisateurs désireux d'accéder à Internet peuvent fermer la fenêtre Apple CNA dès l'apparition du bouton "Done", interrompant potentiellement l'appel API qui enregistre leurs préférences de consentement granulaires. Atténuation : Assurez-vous que le backend du captive portal traite la charge utile de consentement de manière asynchrone et ne renvoie le message de succès RADIUS qu'après confirmation de la validation de la base de données.
ROI et Impact Commercial
Bien que la conformité au DPDP exige des investissements, elle génère des avantages opérationnels significatifs. Des données propres et vérifiées par consentement améliorent le ROI marketing en garantissant que les campagnes ne ciblent que les utilisateurs engagés, réduisant les taux de rebond et améliorant la réputation de l'expéditeur. De plus, la démonstration d'une protection robuste des données renforce la confiance. Dans des secteurs comme la Santé et l' Hôtellerie , où la sensibilité des données est primordiale, une expérience d'intégration WiFi transparente et conforme devient un avantage concurrentiel.
L'impact commercial ultime est cependant l'atténuation des risques. Avec des pénalités DPDP pouvant atteindre 250 crores de roupies pour les défaillances de sécurité, le coût de l'architecture d'une solution conforme est négligeable par rapport à l'exposition réglementaire.
Écoutez le Briefing
Pour un aperçu concis de ces exigences, écoutez notre briefing technique en podcast :
Termes clés et définitions
Data Fiduciary
The entity that determines the purpose and means of processing personal data.
In the context of guest WiFi, the venue operator (e.g., the hotel or mall) is the Data Fiduciary and holds all legal liability.
Data Processor
Any person who processes personal data on behalf of a Data Fiduciary.
The WiFi platform vendor (like Purple) acts as the Data Processor and must operate under a strict contract.
Data Principal
The individual to whom the personal data relates.
The guest or customer connecting to the WiFi network.
Unconditional Consent
Consent that is not made contingent on the provision of a good or service.
Venues cannot force guests to accept marketing emails in exchange for free WiFi.
Deemed Cessation
The legal presumption that the purpose for data collection is no longer served after a period of inactivity.
Forces IT teams to implement automated data erasure workflows for inactive WiFi users.
Blacklist Transfer Approach
A regulatory model where cross-border data transfers are allowed by default, unless explicitly restricted.
Simplifies cloud architecture for Indian venues, as they can use foreign data centres unless the government issues a specific restriction.
Captive Network Assistant (CNA)
The mini-browser triggered by mobile operating systems when they detect a captive portal.
CNA limitations require careful technical implementation of consent forms to ensure data is captured reliably before the window closes.
Granular Consent
Providing separate options for different types of data processing.
Required on captive portals to separate necessary network access from optional marketing and analytics.
Études de cas
A 200-room business hotel in Mumbai wants to offer free guest WiFi. They currently require guests to provide their email address and agree to receive promotional offers before granting internet access. How must they re-architect this flow for DPDP compliance?
The hotel must decouple network access from marketing consent. They should deploy a captive portal with two distinct checkboxes. Checkbox 1 (Required): 'I agree to the terms of service for network access.' Checkbox 2 (Optional, unchecked by default): 'I consent to receive promotional offers via email.' The backend RADIUS server must grant access if only Checkbox 1 is ticked. The system must log the exact consent state (timestamp, IP, and which boxes were ticked) in an immutable database.
A large Indian retail chain uses WiFi probes to track customer footfall and dwell time across 50 stores. They capture device MAC addresses. How should they handle this data under the DPDP Act?
The IT team should implement edge-level anonymisation. The WiFi access points should be configured to hash and salt the MAC addresses before transmitting the data to the central analytics server. If the data is irreversibly anonymised and cannot identify a Data Principal, it falls outside the scope of the DPDP Act. For identified analytics (e.g., tracking a specific registered user's journey), they must obtain explicit consent via the captive portal when the user connects to the network.
Analyse de scénario
Q1. Your marketing director requests that the captive portal be updated to require users to provide their date of birth to access the WiFi, aiming to build better demographic profiles. How should you, as the IT Director, respond based on DPDP principles?
💡 Astuce :Consider the principles of data minimisation and unconditional consent.
Afficher l'approche recommandée
You should reject the request to make it mandatory. Under the DPDP Act's data minimisation principles, you should only collect data necessary for the specified purpose (providing network access). Date of birth is not required for network routing. Furthermore, making it mandatory violates the 'unconditional' consent rule. You can include the date of birth field, but it must be entirely optional, and the user must be able to connect to the WiFi even if they leave it blank.
Q2. A guest who used your stadium WiFi six months ago emails your support desk demanding that all their personal data be deleted immediately under their DPDP rights. What technical steps must your team take?
💡 Astuce :Consider both the primary database and downstream systems, as well as Rule 8(3) exceptions.
Afficher l'approche recommandée
- Verify the identity of the Data Principal. 2. Locate their record in the WiFi platform's database. 3. Execute a soft-delete or anonymisation of their PII (name, email, phone). 4. Trigger webhooks/APIs to ensure this deletion propagates to any downstream systems (CRM, email marketing platforms). 5. Crucially, under Rule 8(3), you must retain the anonymised processing logs (connection times, data volume) for a minimum of one year from the date of processing for audit purposes. 6. Respond to the user within the mandatory 90-day window confirming the erasure.
Q3. Your multinational hotel group uses a central CRM hosted in a data centre in Singapore. Can you transfer Indian guest WiFi data to this server under the DPDP Act?
💡 Astuce :Recall the difference between DPDP's blacklist approach and GDPR's whitelist approach.
Afficher l'approche recommandée
Yes, you can. The DPDP Act utilizes a 'blacklist' approach for cross-border data transfers. This means transfers are permitted to any country by default, unless the Central Government of India has issued a specific notification restricting transfers to that territory. Since Singapore is not currently restricted, the transfer is legally permissible without requiring complex adequacy mechanisms like Standard Contractual Clauses (SCCs) used under GDPR. However, you must still ensure the data is protected with reasonable security safeguards during transit and at rest.



