Lei DPDP da Índia: Conformidade com o WiFi de Convidados para Locais Indianos
Este guia de referência técnica e autoritário desvenda a Lei de Proteção de Dados Pessoais Digitais (DPDP) de 2023 para locais indianos que operam WiFi de convidados. Oferece estratégias de conformidade acionáveis, considerações arquitetónicas para captive portals, e estruturas práticas para retenção de dados e transferências transfronteiriças.
🎧 Ouça este Guia
Ver Transcrição
- Resumo Executivo
- Análise Técnica Aprofundada: Arquitetura da Lei DPDP para WiFi de Convidados
- O Fluxo de Consentimento do Captive Portal
- Trilhas de Auditoria de Consentimento Imutáveis
- Responsabilidade do Fiduciário de Dados vs. Processador de Dados
- Guia de Implementação: Estratégias de Implementação
- Passo 1: Desacoplamento da Autenticação do Marketing
- Passo 2: Implementação do Ciclo de Vida dos Dados
- Passo 3: Lidar com Transferências Transfronteiriças
- Melhores Práticas e Padrões da Indústria
- Resolução de Problemas e Mitigação de Riscos
- ROI e Impacto no Negócio
- Ouça o Briefing

Resumo Executivo
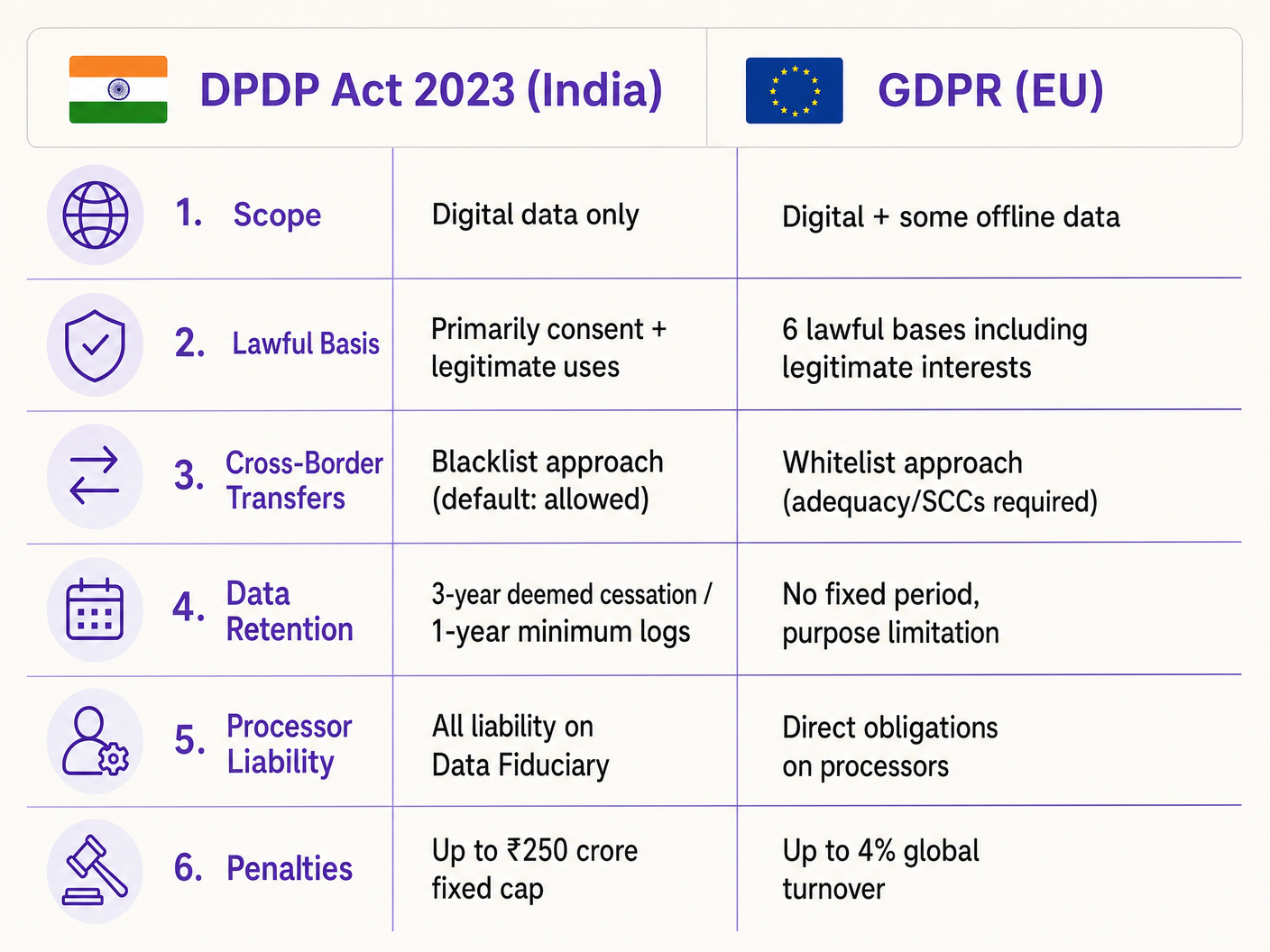
A Lei de Proteção de Dados Pessoais Digitais de 2023 (Lei DPDP) altera fundamentalmente a forma como os locais indianos — desde grupos hoteleiros a propriedades de retalho — devem lidar com os dados de WiFi de convidados. Para gestores de TI e arquitetos de rede, esta não é meramente uma atualização legal; exige alterações arquitetónicas significativas aos captive portals, bases de dados de gestão de consentimento e automação do ciclo de vida dos dados. Ao contrário do GDPR, a Lei DPDP coloca toda a responsabilidade de conformidade diretamente no Fiduciário de Dados (o local), o que significa que não pode transferir o risco para o seu fornecedor de plataforma WiFi. Além disso, a Lei introduz uma incondicionalidade rigorosa para o consentimento e exige a eliminação rápida e orientada por finalidade dos dados. Este guia fornece um manual de conformidade neutro em relação ao fornecedor, detalhando a implementação técnica de fluxos de consentimento granulares, trilhas de auditoria robustas e políticas de retenção automatizadas necessárias para mitigar os riscos financeiros substanciais associados à não conformidade.
Análise Técnica Aprofundada: Arquitetura da Lei DPDP para WiFi de Convidados
A implementação da conformidade com a DPDP para WiFi de convidados exige uma mudança da recolha passiva de dados para uma gestão de consentimento ativa e verificável. A arquitetura técnica deve suportar a captura de consentimento granular, trilhas de auditoria imutáveis e gestão automatizada do ciclo de vida dos dados.
O Fluxo de Consentimento do Captive Portal
O captive portal tradicional de "clicar para aceitar os termos" está obsoleto sob a Secção 6 da DPDP. O consentimento deve ser "livre, específico, informado, incondicional e inequívoco." A exigência de consentimento incondicional significa que os locais não podem tornar as comunicações de marketing um pré-requisito para o acesso à rede.
Quando um convidado se conecta ao SSID e o Captive Network Assistant (CNA) aciona o portal, o fluxo arquitetónico deve garantir a conformidade antes de conceder o token de autenticação RADIUS.

A implementação técnica deve ter em conta as limitações do CNA. Por exemplo, Apple CNA, Android Connectivity Check, Microsoft NCSI: Como a Deteção de Captive Portal Realmente Funciona explica que o ambiente do mini-navegador frequentemente restringe cookies e redirecionamentos. Portanto, o estado do consentimento deve ser transmitido e armazenado de forma segura no lado do servidor, associado ao endereço MAC do dispositivo ou identificador do utilizador, imediatamente após o envio do formulário, antes que a janela do CNA seja fechada.
Trilhas de Auditoria de Consentimento Imutáveis
Se o Conselho de Proteção de Dados investigar uma queixa, o local deve provar que um Titular de Dados específico consentiu num processamento específico numa data específica. A base de dados da plataforma WiFi deve manter uma trilha de auditoria imutável. Cada registo de consentimento deve incluir:
- Um identificador de sessão único.
- O carimbo de data/hora (em IST).
- O endereço IP do cliente e o endereço MAC.
- A versão específica do aviso de privacidade exibido.
- Os propósitos exatos para os quais foi dado consentimento (por exemplo, acesso à rede vs. marketing).
Responsabilidade do Fiduciário de Dados vs. Processador de Dados
Nos termos da Secção 8 da DPDP, o local atua como Fiduciário de Dados, enquanto o fornecedor de WiFi (por exemplo, Purple) atua como Processador de Dados. Crucialmente, o Fiduciário de Dados assume uma responsabilidade absoluta e não delegável pela conformidade. A Secção 8(2) exige um contrato válido com o Processador de Dados. Os diretores de TI devem auditar os seus acordos com fornecedores para garantir que contêm adendas específicas de processamento de dados da DPDP, uma vez que depender de contratos legados expõe o local a penalidades severas.
Guia de Implementação: Estratégias de Implementação
A implementação de uma solução WiFi de convidados em conformidade com a DPDP exige a coordenação da infraestrutura de rede, gestão de identidade e sistemas de automação de marketing.
Passo 1: Desacoplamento da Autenticação do Marketing
A camada de autenticação (RADIUS/802.1X) deve ser logicamente separada da base de dados de marketing. Quando um utilizador se autentica, o sistema deve verificar as sinalizações de consentimento. Se o utilizador apenas consentiu no acesso à rede, os seus dados de identidade devem ser isolados e impedidos de sincronizar com o CRM ou plataformas de automação de marketing.
Passo 2: Implementação do Ciclo de Vida dos Dados
A Secção 8(7) da DPDP exige a eliminação de dados quando a finalidade especificada já não é servida ou o consentimento é retirado. Para os operadores de locais, definir a "cessação da finalidade" exige fluxos de trabalho automatizados.
Por exemplo, num ambiente de Retalho que utiliza WiFi Analytics , se um cliente não se conectou à rede em 24 meses, um script automatizado deve acionar um fluxo de trabalho de eliminação suave. A Regra 8(3) complica isto ao exigir que os registos de processamento sejam retidos por um mínimo de um ano. Portanto, a arquitetura da base de dados deve suportar a eliminação em camadas: remover informações de identificação pessoal (PII) enquanto retém registos de conexão anonimizados para fins de auditoria.
Passo 3: Lidar com Transferências Transfronteiriças
Ao contrário dos complexos mecanismos de adequação do GDPR, a Secção 16 da DPDP utiliza uma abordagem de "lista negra". As transferências de dados para fora da Índia são permitidas por padrão, a menos que o Governo Central restrinja explicitamente um país específico. Para arquitetos de TI que implementam controladores WiFi geridos na nuvem (por exemplo, Cisco Aruba, Meraki) ou plataformas de análise alojadas em regiões AWS/Azure fora da Índia, isto atualmente reduz o atrito. No entanto, as arquiteturas devem permanecer suficientemente ágeis para migrar a residência dos dados caso as notificações governamentais mudem.
Melhores Práticas e Padrões da Indústria
Ao arquitetar para conformidade, confie em padrões estabelecidos em vez de soluções personalizadas.
- Anonimização na Borda: Para contagem de tráfego e Sistema de Posicionamento Interiors , implemente o hashing de endereços MAC ao nível do ponto de acesso antes que os dados cheguem ao controlador na cloud. Se os dados forem genuinamente anonimizados, ficam fora do âmbito do DPDP.
- Gestão Centralizada de Consentimento: Não dependa da plataforma WiFi como a única fonte de verdade se o utilizador interagir com o local através de outros canais (por exemplo, um motor de reservas de hotel). Implemente uma API de consentimento mestre que sincronize as preferências em toda a stack.
- Integrações Seguras de API: Garanta que todas as transferências de dados entre a plataforma Guest WiFi e os sistemas a jusante utilizem TLS 1.3 e exijam a rotação de chaves API, alinhando-se com os princípios PCI DSS e ISO 27001.
Resolução de Problemas e Mitigação de Riscos
Os modos de falha em implementações de conformidade resultam frequentemente de lacunas na integração de sistemas, em vez da plataforma WiFi central.
Modo de Falha Comum: Dados Órfãos em Sistemas a Jusante Quando um utilizador retira o consentimento através do captive portal, a plataforma WiFi atualiza a sua base de dados. No entanto, se o webhook da API para o CRM falhar, a equipa de marketing pode continuar a enviar e-mails ao utilizador, resultando numa violação do DPDP. Mitigação: Implemente uma lógica robusta de repetição de webhook e scripts de reconciliação diária entre a base de dados WiFi e o CRM.
Modo de Falha Comum: Descarte de CNA Antes da Sincronização de Consentimento Os utilizadores ansiosos por acesso à internet podem fechar a janela Apple CNA no momento em que o botão "Done" aparece, potencialmente interrompendo a chamada API que regista as suas preferências de consentimento granular. Mitigação: Garanta que o backend do captive portal processa o payload de consentimento de forma assíncrona e devolve a mensagem de sucesso RADIUS apenas após a confirmação da gravação na base de dados.
ROI e Impacto no Negócio
Embora a conformidade com o DPDP exija investimento, impulsiona benefícios operacionais significativos. Dados limpos e com consentimento verificado melhoram o ROI de marketing, garantindo que as campanhas visam apenas utilizadores envolvidos, reduzindo as taxas de rejeição e melhorando a reputação do remetente. Além disso, demonstrar uma proteção de dados robusta constrói confiança. Em setores como Healthcare e Hospitality , onde a sensibilidade dos dados é primordial, uma experiência de onboarding WiFi transparente e em conformidade torna-se um diferenciador competitivo.
O impacto final no negócio, no entanto, é a mitigação de riscos. Com penalidades DPDP que podem atingir até ₹250 crore por falhas de segurança, o custo de arquitetar uma solução em conformidade é insignificante em comparação com a exposição regulatória.
Ouça o Briefing
Para uma visão geral concisa destes requisitos, ouça o nosso briefing técnico em podcast:
Termos-Chave e Definições
Data Fiduciary
The entity that determines the purpose and means of processing personal data.
In the context of guest WiFi, the venue operator (e.g., the hotel or mall) is the Data Fiduciary and holds all legal liability.
Data Processor
Any person who processes personal data on behalf of a Data Fiduciary.
The WiFi platform vendor (like Purple) acts as the Data Processor and must operate under a strict contract.
Data Principal
The individual to whom the personal data relates.
The guest or customer connecting to the WiFi network.
Unconditional Consent
Consent that is not made contingent on the provision of a good or service.
Venues cannot force guests to accept marketing emails in exchange for free WiFi.
Deemed Cessation
The legal presumption that the purpose for data collection is no longer served after a period of inactivity.
Forces IT teams to implement automated data erasure workflows for inactive WiFi users.
Blacklist Transfer Approach
A regulatory model where cross-border data transfers are allowed by default, unless explicitly restricted.
Simplifies cloud architecture for Indian venues, as they can use foreign data centres unless the government issues a specific restriction.
Captive Network Assistant (CNA)
The mini-browser triggered by mobile operating systems when they detect a captive portal.
CNA limitations require careful technical implementation of consent forms to ensure data is captured reliably before the window closes.
Granular Consent
Providing separate options for different types of data processing.
Required on captive portals to separate necessary network access from optional marketing and analytics.
Estudos de Caso
A 200-room business hotel in Mumbai wants to offer free guest WiFi. They currently require guests to provide their email address and agree to receive promotional offers before granting internet access. How must they re-architect this flow for DPDP compliance?
The hotel must decouple network access from marketing consent. They should deploy a captive portal with two distinct checkboxes. Checkbox 1 (Required): 'I agree to the terms of service for network access.' Checkbox 2 (Optional, unchecked by default): 'I consent to receive promotional offers via email.' The backend RADIUS server must grant access if only Checkbox 1 is ticked. The system must log the exact consent state (timestamp, IP, and which boxes were ticked) in an immutable database.
A large Indian retail chain uses WiFi probes to track customer footfall and dwell time across 50 stores. They capture device MAC addresses. How should they handle this data under the DPDP Act?
The IT team should implement edge-level anonymisation. The WiFi access points should be configured to hash and salt the MAC addresses before transmitting the data to the central analytics server. If the data is irreversibly anonymised and cannot identify a Data Principal, it falls outside the scope of the DPDP Act. For identified analytics (e.g., tracking a specific registered user's journey), they must obtain explicit consent via the captive portal when the user connects to the network.
Análise de Cenários
Q1. Your marketing director requests that the captive portal be updated to require users to provide their date of birth to access the WiFi, aiming to build better demographic profiles. How should you, as the IT Director, respond based on DPDP principles?
💡 Dica:Consider the principles of data minimisation and unconditional consent.
Mostrar Abordagem Recomendada
You should reject the request to make it mandatory. Under the DPDP Act's data minimisation principles, you should only collect data necessary for the specified purpose (providing network access). Date of birth is not required for network routing. Furthermore, making it mandatory violates the 'unconditional' consent rule. You can include the date of birth field, but it must be entirely optional, and the user must be able to connect to the WiFi even if they leave it blank.
Q2. A guest who used your stadium WiFi six months ago emails your support desk demanding that all their personal data be deleted immediately under their DPDP rights. What technical steps must your team take?
💡 Dica:Consider both the primary database and downstream systems, as well as Rule 8(3) exceptions.
Mostrar Abordagem Recomendada
- Verify the identity of the Data Principal. 2. Locate their record in the WiFi platform's database. 3. Execute a soft-delete or anonymisation of their PII (name, email, phone). 4. Trigger webhooks/APIs to ensure this deletion propagates to any downstream systems (CRM, email marketing platforms). 5. Crucially, under Rule 8(3), you must retain the anonymised processing logs (connection times, data volume) for a minimum of one year from the date of processing for audit purposes. 6. Respond to the user within the mandatory 90-day window confirming the erasure.
Q3. Your multinational hotel group uses a central CRM hosted in a data centre in Singapore. Can you transfer Indian guest WiFi data to this server under the DPDP Act?
💡 Dica:Recall the difference between DPDP's blacklist approach and GDPR's whitelist approach.
Mostrar Abordagem Recomendada
Yes, you can. The DPDP Act utilizes a 'blacklist' approach for cross-border data transfers. This means transfers are permitted to any country by default, unless the Central Government of India has issued a specific notification restricting transfers to that territory. Since Singapore is not currently restricted, the transfer is legally permissible without requiring complex adequacy mechanisms like Standard Contractual Clauses (SCCs) used under GDPR. However, you must still ensure the data is protected with reasonable security safeguards during transit and at rest.



