Technical Guides
Deep, expert-led guides covering guest WiFi, analytics, captive portals, and modern venue technology. Each guide includes diagrams, worked examples, and audio podcasts.
249 guides
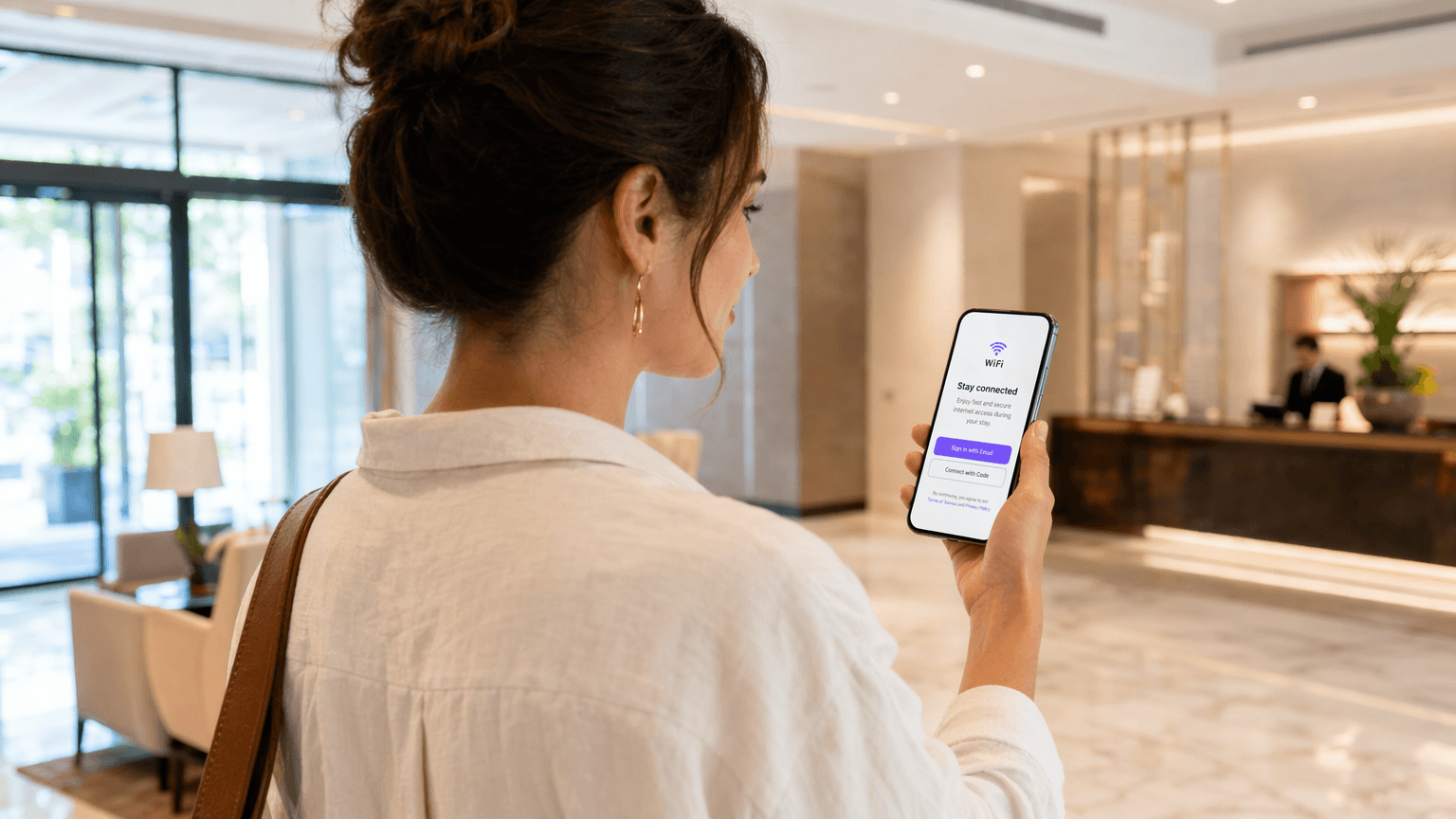
Streamlining User Onboarding for Secure Network Access
This guide provides a comprehensive technical reference for IT managers, network architects, and venue operations directors on how to streamline user onboarding for secure network access. It covers the full authentication stack — from self-service captive portals and identity federation to IEEE 802.1X, WPA3, RADIUS, and OpenRoaming — with practical deployment guidance for hospitality, retail, events, and public-sector environments. The guide addresses GDPR and PCI DSS compliance requirements, role-based access control, and MAC caching strategies, equipping teams to reduce onboarding friction and administrative overhead without compromising security posture.
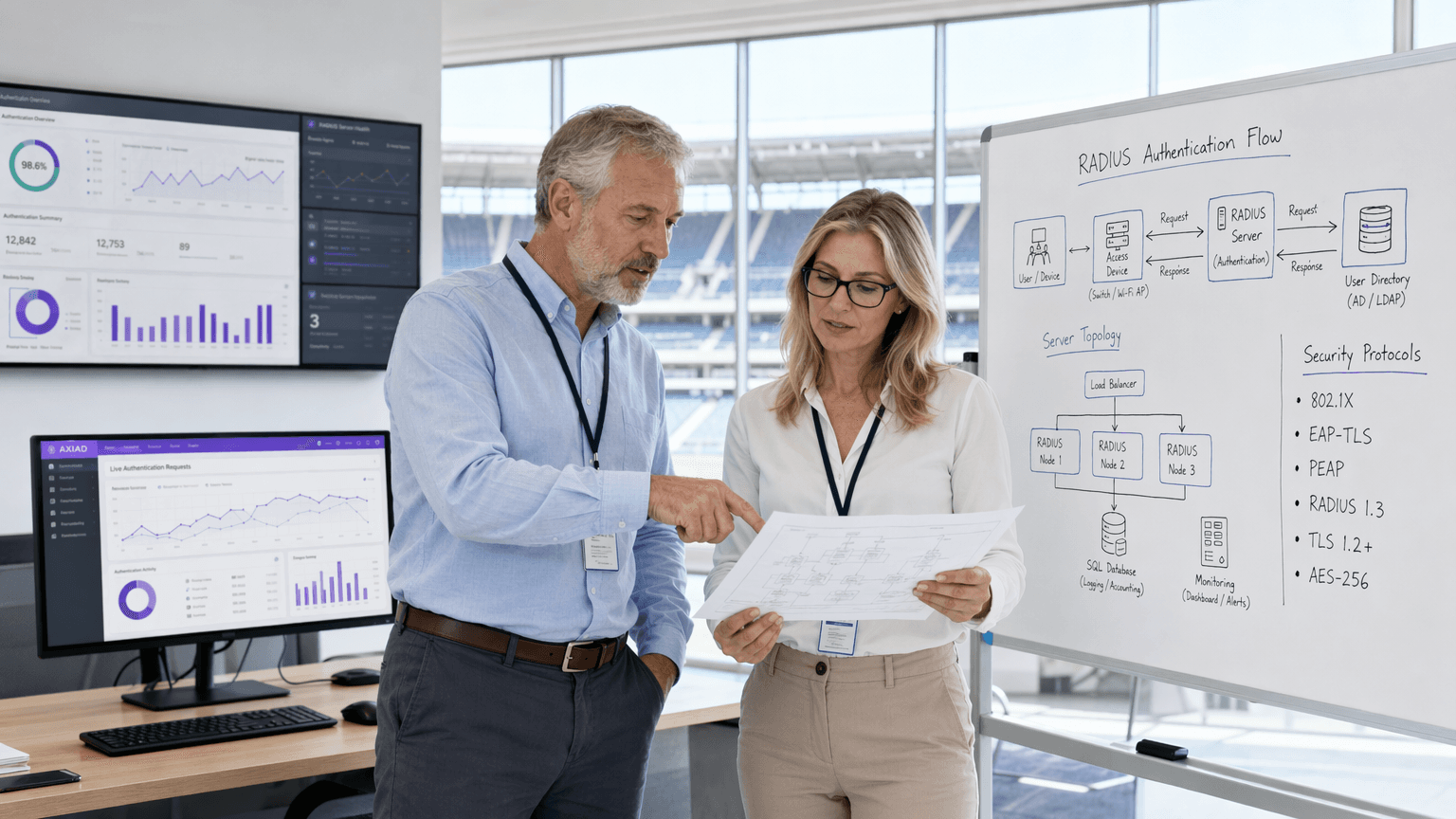
Mitigating RADIUS Vulnerabilities: A Security Hardening Guide
This guide provides a comprehensive, actionable reference for IT managers, network architects, and CTOs responsible for enterprise WiFi infrastructure across hospitality, retail, events, and public-sector environments. It covers the full attack surface of RADIUS server deployments — from MD5 collision vulnerabilities and weak shared secrets to unencrypted UDP transport and misconfigured EAP methods — and delivers a prioritised hardening roadmap aligned with IEEE 802.1X, PCI DSS, and GDPR requirements. Organisations that implement these recommendations will materially reduce their exposure to credential-based network attacks, meet compliance obligations, and build a defensible security posture for their guest and corporate WiFi infrastructure.
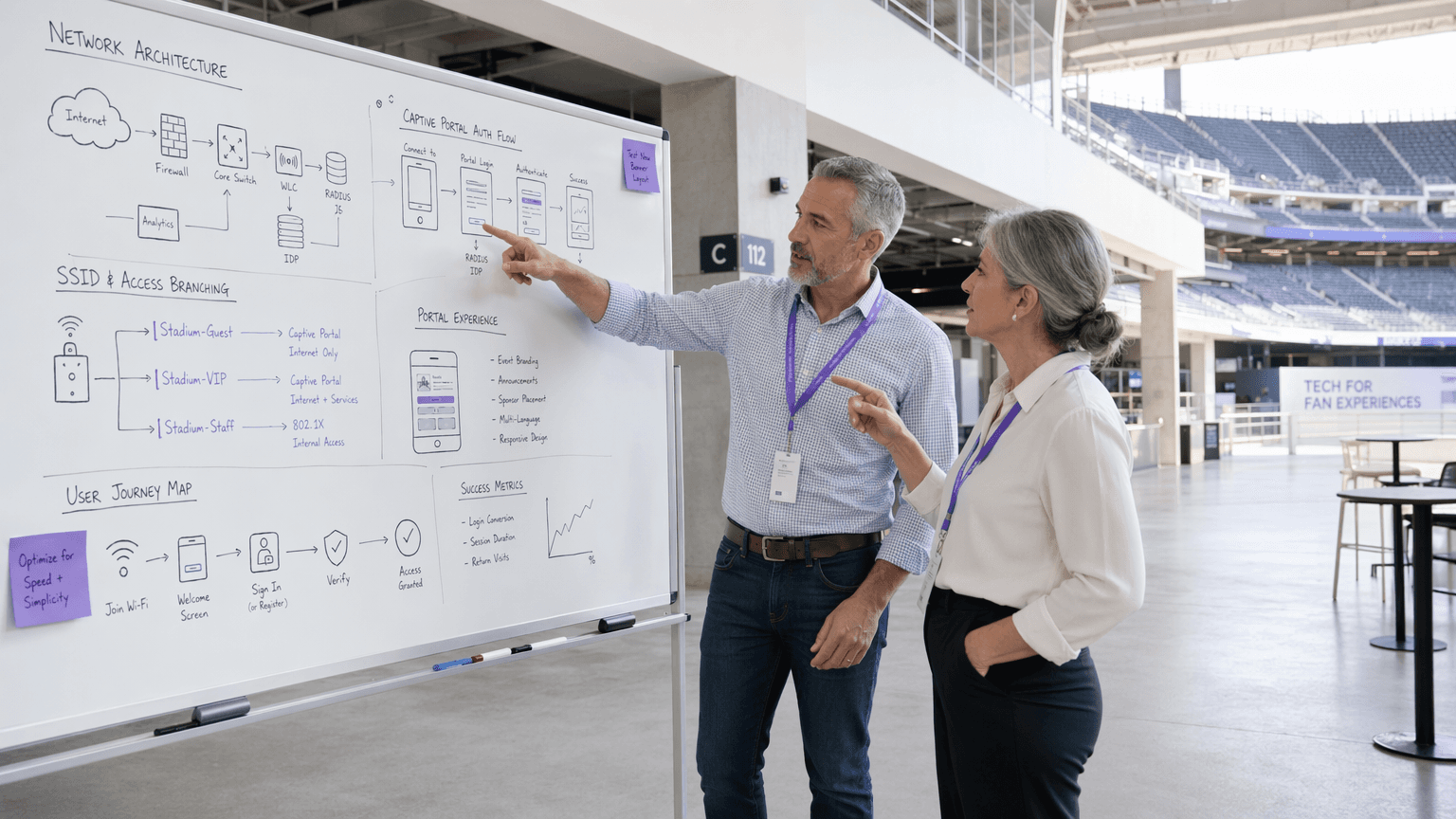
Captive Portal Customisation and Security Best Practices
This guide provides a comprehensive technical reference for IT managers, network architects, and CTOs deploying captive portals across hospitality, retail, events, and public-sector environments. It covers the full deployment lifecycle — from VLAN architecture and authentication method selection through to GDPR compliance, portal hijacking prevention, and back-end integration. Organisations that implement these practices will reduce security risk, achieve regulatory compliance, and transform guest Wi-Fi into a measurable business asset.
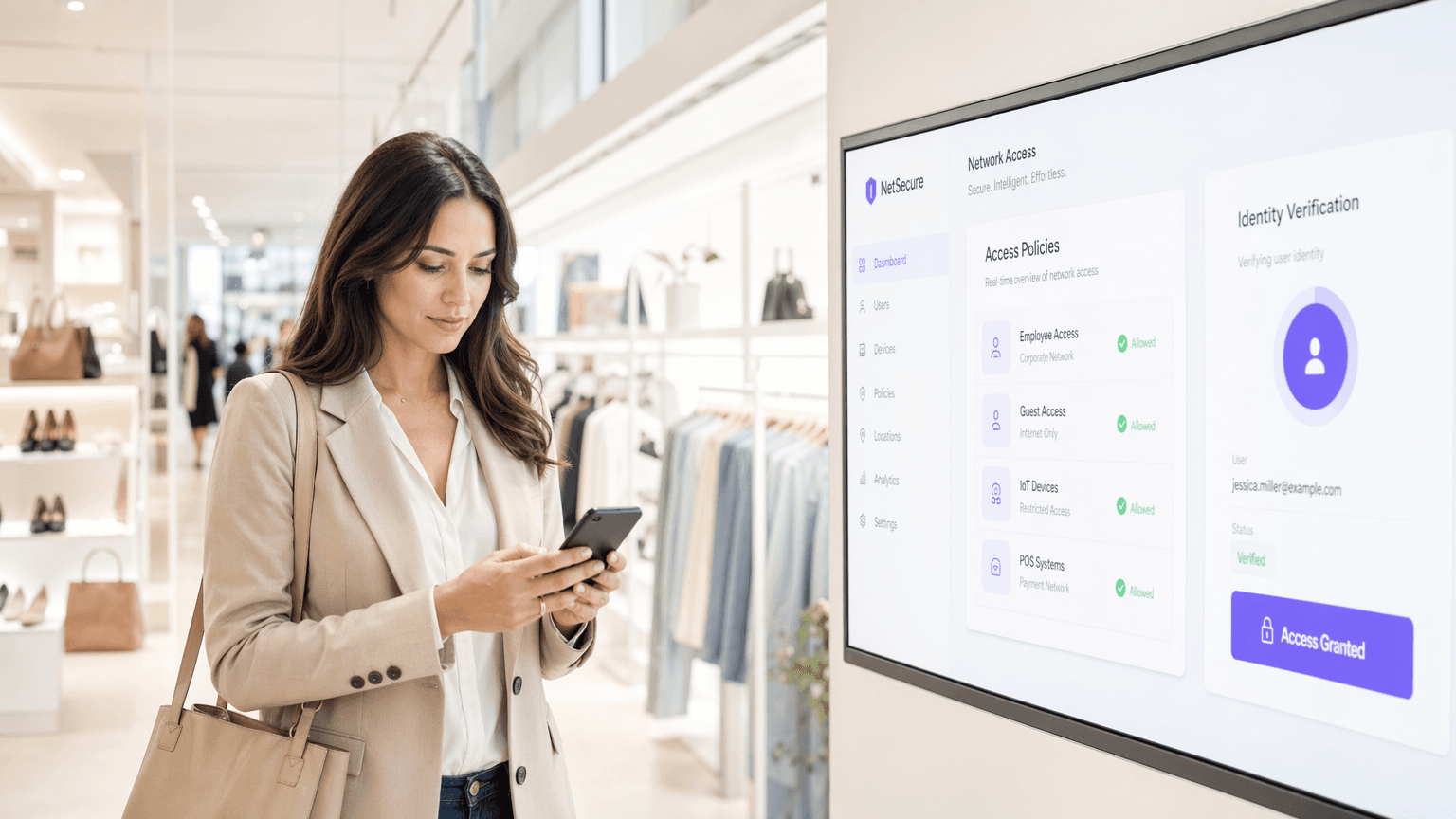
Zero Trust Network Access: Implementation Strategies and Best Practices
This technical reference guide provides IT leaders and network architects with a pragmatic blueprint for Zero Trust Network Access (ZTNA) implementation in enterprise venues. It covers core architecture, microsegmentation strategies, and step-by-step deployment methodologies to secure complex environments without disrupting operations.
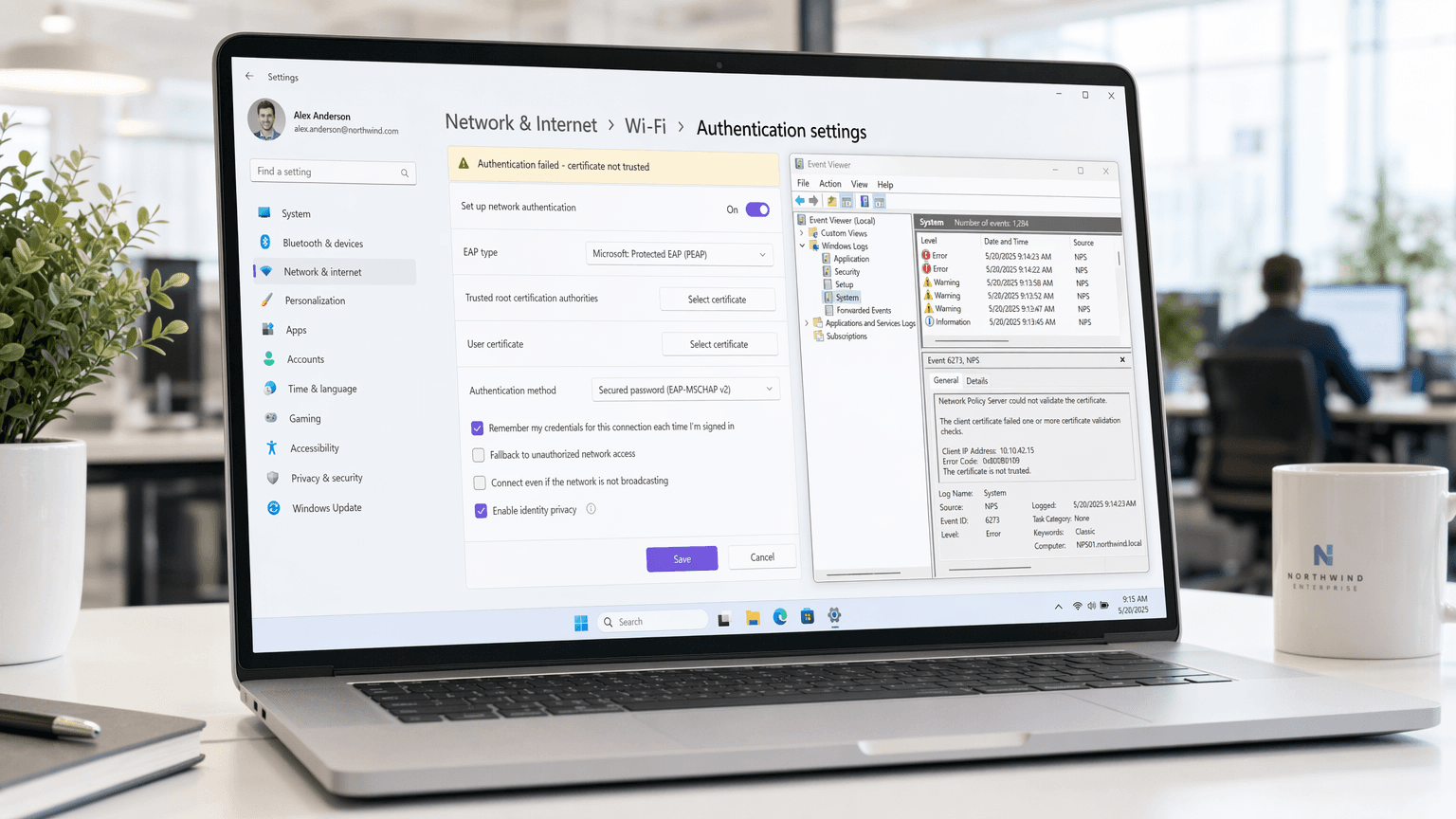
Troubleshooting Windows 11 802.1X Authentication Issues
This technical reference guide provides a definitive diagnostic and remediation path for Windows 11 802.1X authentication failures. It details how OS upgrades disrupt certificate trust chains and Credential Guard enforcement, offering actionable GPO configurations and architectural best practices for enterprise IT teams.
Securing Guest WiFi Networks: Best Practices and Implementation
This authoritative technical reference guide outlines the architecture, authentication, and operational controls required to deploy secure enterprise guest WiFi. It provides actionable best practices for IT leaders to enforce network segmentation, manage bandwidth, and ensure compliance while maximising data capture.
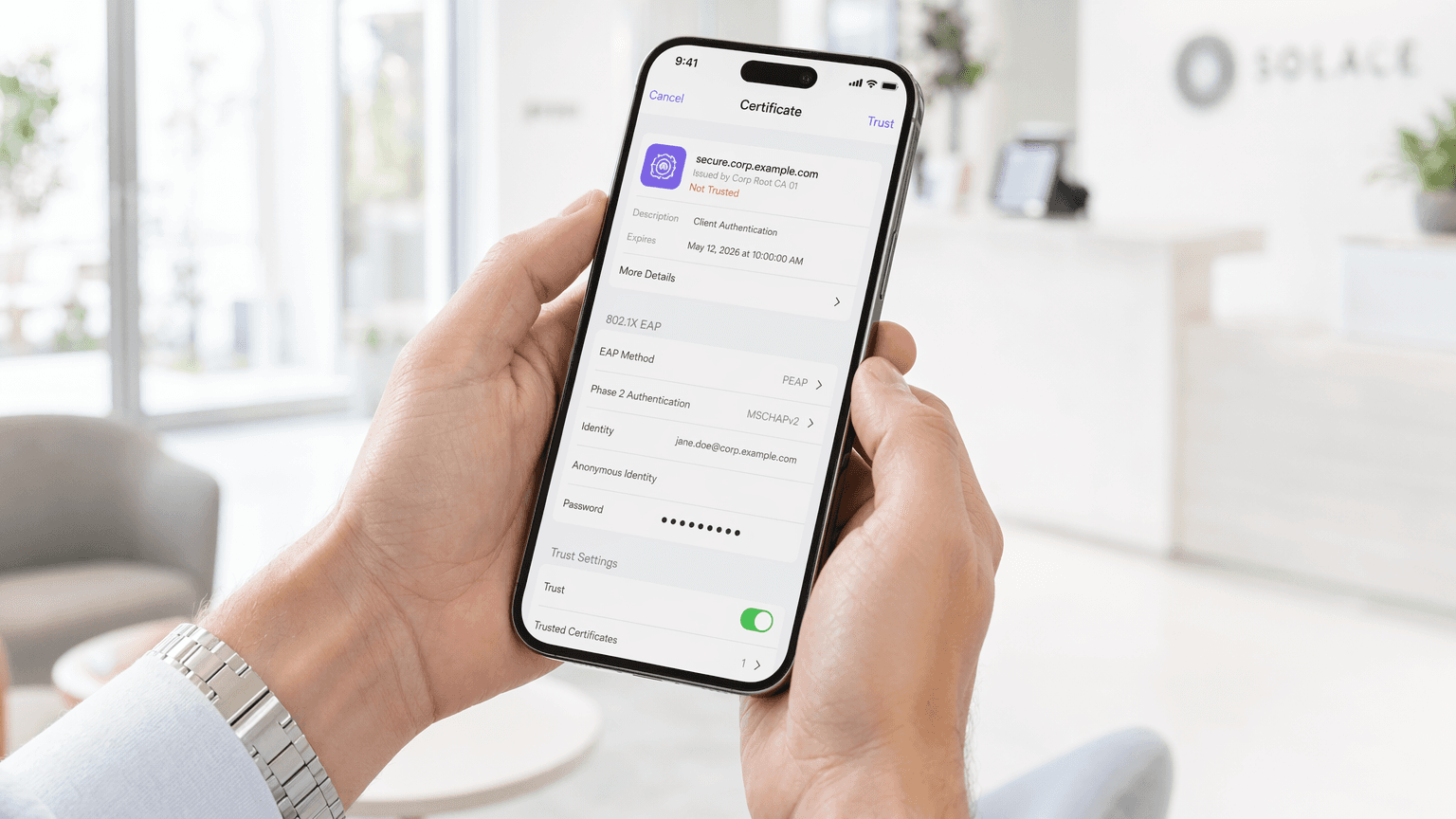
Implementing 802.1X Authentication on Mobile Devices
This comprehensive guide provides IT leaders with a technical blueprint for implementing 802.1X authentication on iOS and Android devices. It covers architecture, EAP method selection, MDM provisioning, and troubleshooting to ensure secure, scalable mobile network access.
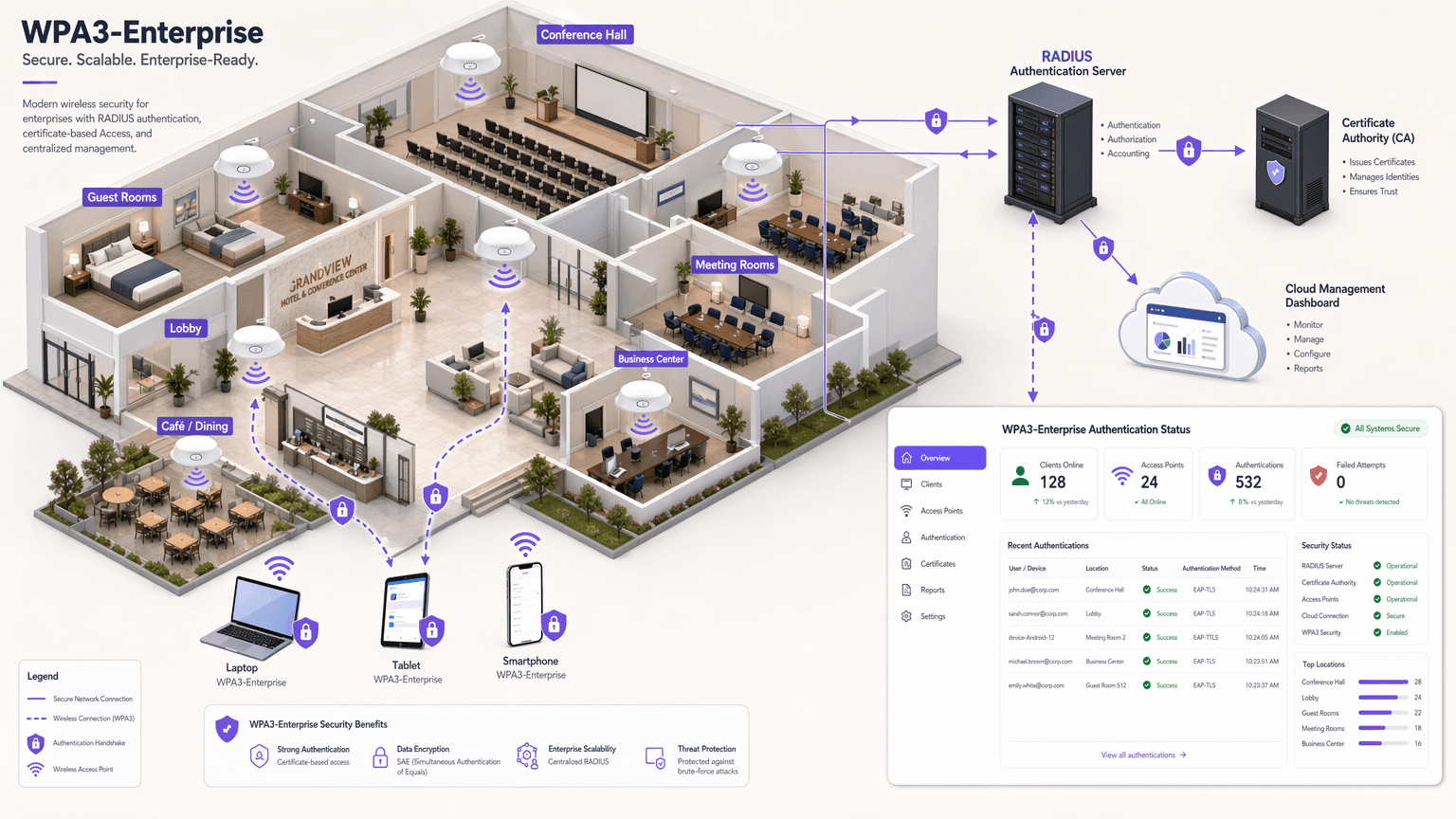
Implementing WPA3-Enterprise for Enhanced Wireless Security
This technical reference guide provides a comprehensive, actionable roadmap for IT leaders transitioning from WPA2 to WPA3-Enterprise. It covers the architectural shifts, mandatory security enhancements like EAP-TLS and PMF, and practical deployment strategies to secure corporate networks across complex enterprise environments.
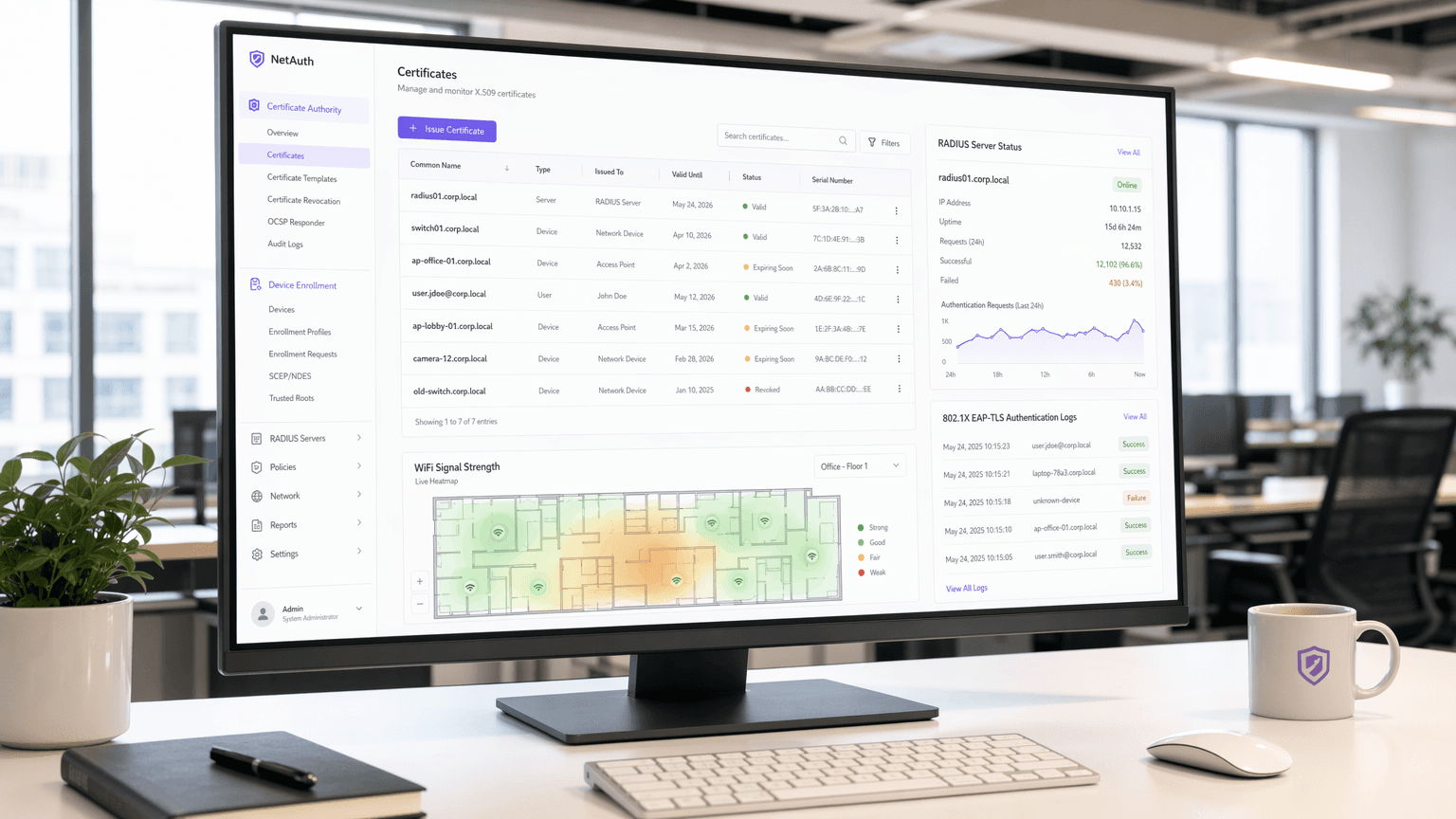
WiFi Certificate Authentication: How Digital Certificates Secure Wireless Networks
This authoritative guide details how X.509 digital certificates and EAP-TLS replace vulnerable passwords in enterprise WiFi. It provides network architects and IT managers with practical implementation steps, PKI architecture design, and business ROI analysis.
The Most Secure Method of WiFi Authentication: A Comparison
This technical reference guide provides a definitive ranked comparison of WiFi authentication methods — from the deprecated WEP standard through to EAP-TLS certificate-based authentication — helping IT managers, network architects, and CTOs at enterprise venues make informed, compliance-aligned security decisions. It covers the technical architecture of each protocol, real-world deployment scenarios in hospitality and retail, and practical implementation guidance for organisations operating under PCI DSS and GDPR obligations. For venue operators and IT teams, this guide translates complex cryptographic standards into actionable deployment decisions with measurable business outcomes.
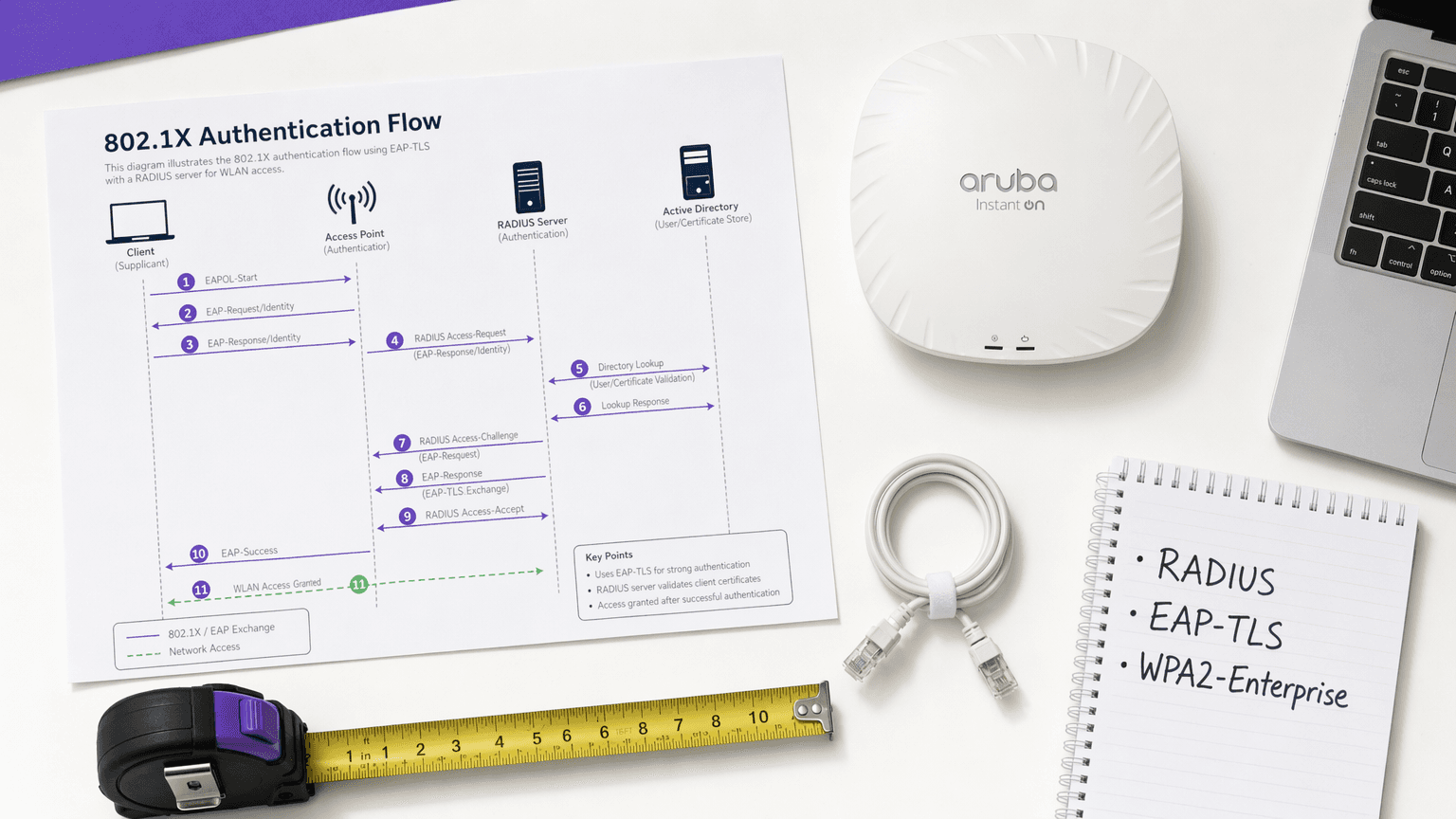
WPA2 vs. 802.1X: What's the Difference?
This guide demystifies the relationship between WPA2 encryption and the IEEE 802.1X authentication framework — two complementary standards that are frequently conflated in vendor documentation and network design discussions. It provides IT directors, network architects, and venue operations leaders with a clear technical breakdown of how these protocols interact, practical deployment strategies across hospitality, retail, and public-sector environments, and actionable guidance on compliance, risk mitigation, and guest WiFi integration.
WPA-PSK Explained: What It Is, How It Works, and Its Security Risks
This authoritative technical reference breaks down the mechanics of WPA-PSK — its 4-way handshake, cryptographic architecture, and inherent security vulnerabilities — and explains precisely why enterprise networks must transition to robust 802.1X or managed captive portal architectures. It provides actionable deployment guidance for IT leaders managing complex venue environments across hospitality, retail, events, and public-sector organisations.

EAP-TLS vs. PEAP: Which Authentication Protocol Is Right for Your Network?
A comprehensive technical comparison of EAP-TLS and PEAP authentication protocols, covering security architecture, deployment complexity, and compliance implications. This guide provides actionable decision frameworks for IT leaders in hospitality, retail, events, and public-sector environments who need to select the right 802.1X authentication method for their enterprise WiFi infrastructure.

What Is PEAP Authentication? How PEAP Secures Your WiFi
This authoritative guide breaks down PEAP authentication for enterprise WiFi networks, detailing its architecture, security limitations compared to EAP-TLS, and practical deployment strategies. Designed for IT managers and network architects, it provides actionable insights on when PEAP-MSCHAPv2 remains appropriate and how to secure it against modern threats.
What Is EAP-TLS? Certificate-Based WiFi Authentication Explained
This guide provides a comprehensive technical reference on EAP-TLS (Extensible Authentication Protocol with Transport Layer Security), the most secure 802.1X authentication method available for enterprise WiFi. It covers the X.509 certificate infrastructure required, the mutual authentication handshake, and practical deployment patterns for hospitality, retail, healthcare, and public sector environments. IT managers, network architects, and CTOs will find practical guidance on PKI design, MDM-integrated certificate provisioning, RADIUS configuration, and compliance alignment with PCI DSS and GDPR.
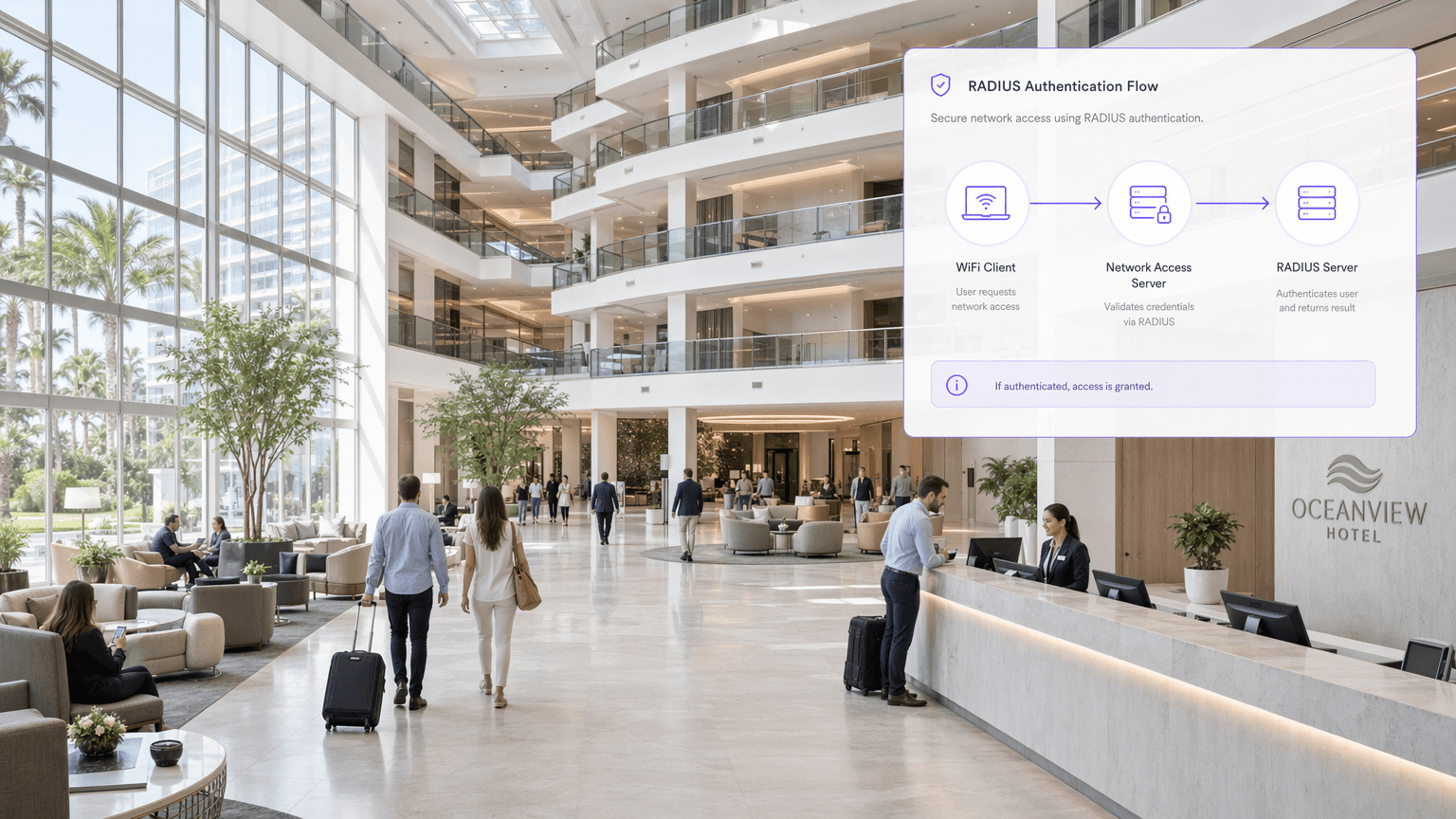
What Is RADIUS? How RADIUS Servers Secure WiFi Networks
This authoritative technical reference guide explains how RADIUS (Remote Authentication Dial-In User Service) underpins enterprise WiFi security through the IEEE 802.1X framework, covering architecture, deployment, and compliance. Designed for IT managers, network architects, and venue operations directors, it provides actionable guidance on moving from shared Pre-Shared Keys to per-user authentication with dynamic policy enforcement. The guide also maps RADIUS integration points to Purple's guest WiFi and analytics platform, with concrete case studies from hospitality and retail environments.
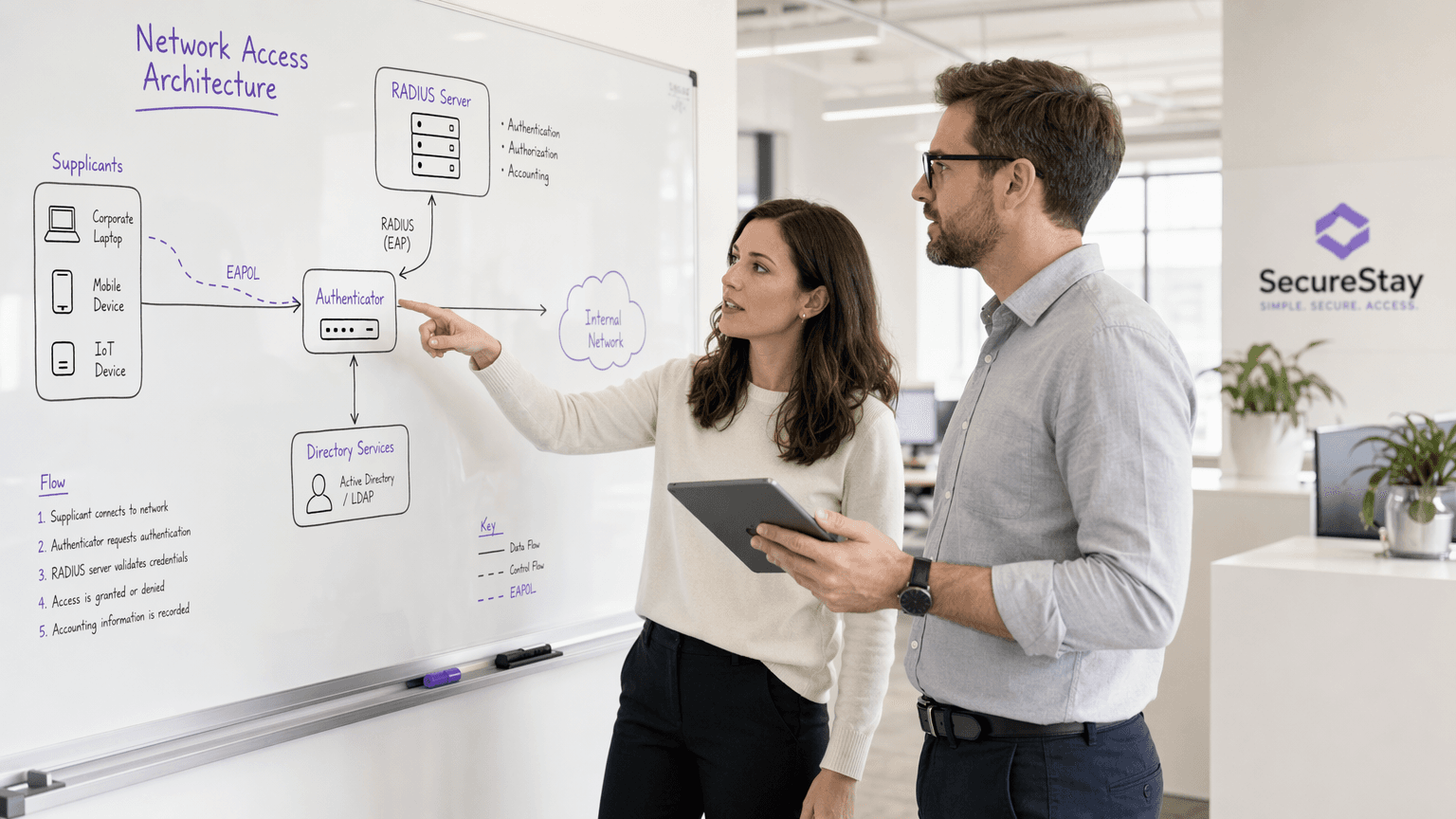
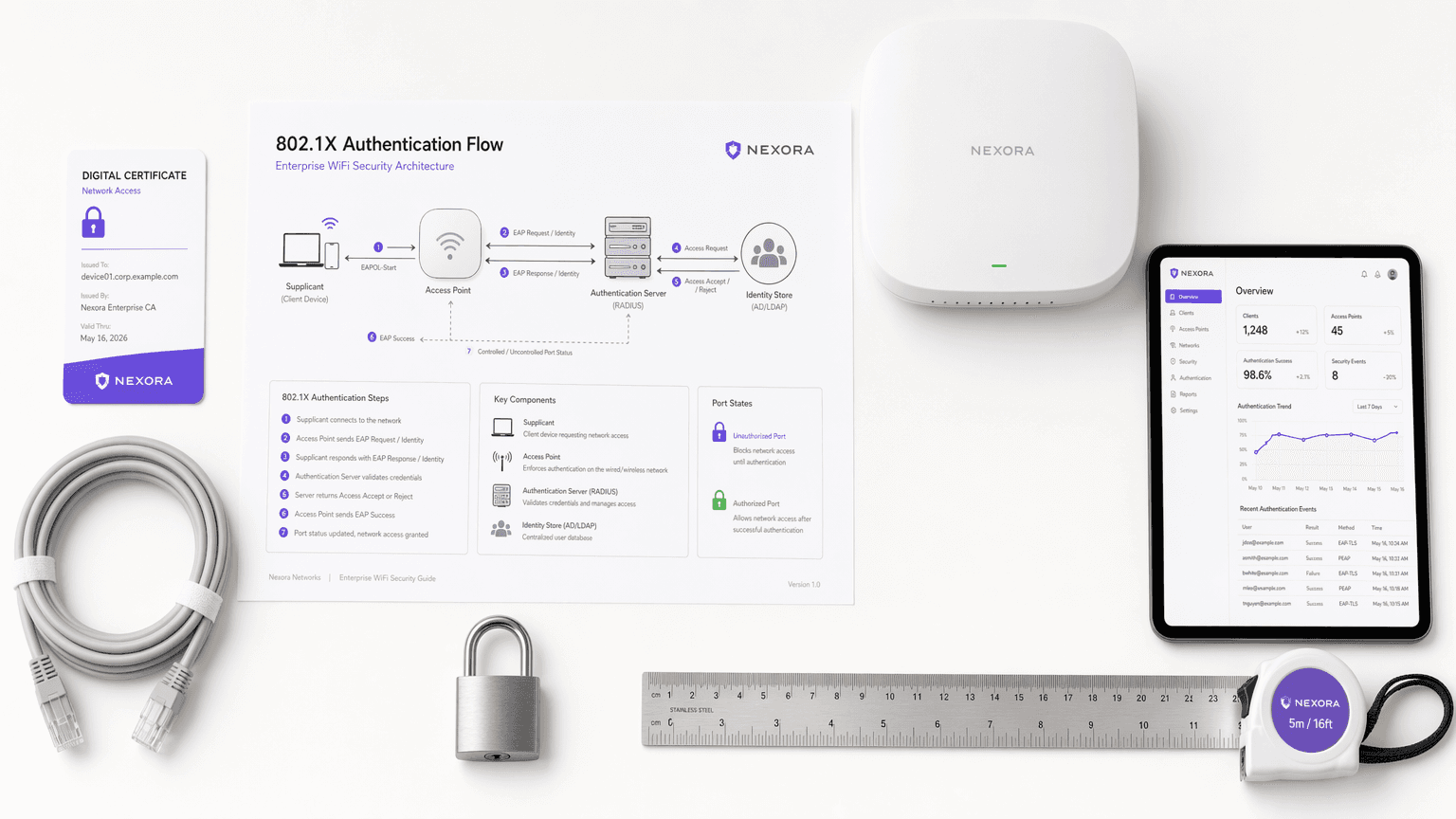
What Is 802.1X Authentication? How It Works and Why It Matters
A comprehensive technical reference guide for IT managers and network architects on IEEE 802.1X authentication. This guide covers the underlying architecture, implementation strategies, security benefits over PSK, and how to effectively deploy enterprise-grade access control alongside guest WiFi solutions.

WPA3: The Next Generation of WiFi Security Explained
This comprehensive technical reference guide explains the architectural shifts introduced by WPA3, including SAE, OWE, and Forward Secrecy. It provides actionable deployment strategies for IT managers and network architects to upgrade enterprise and public venue networks securely.
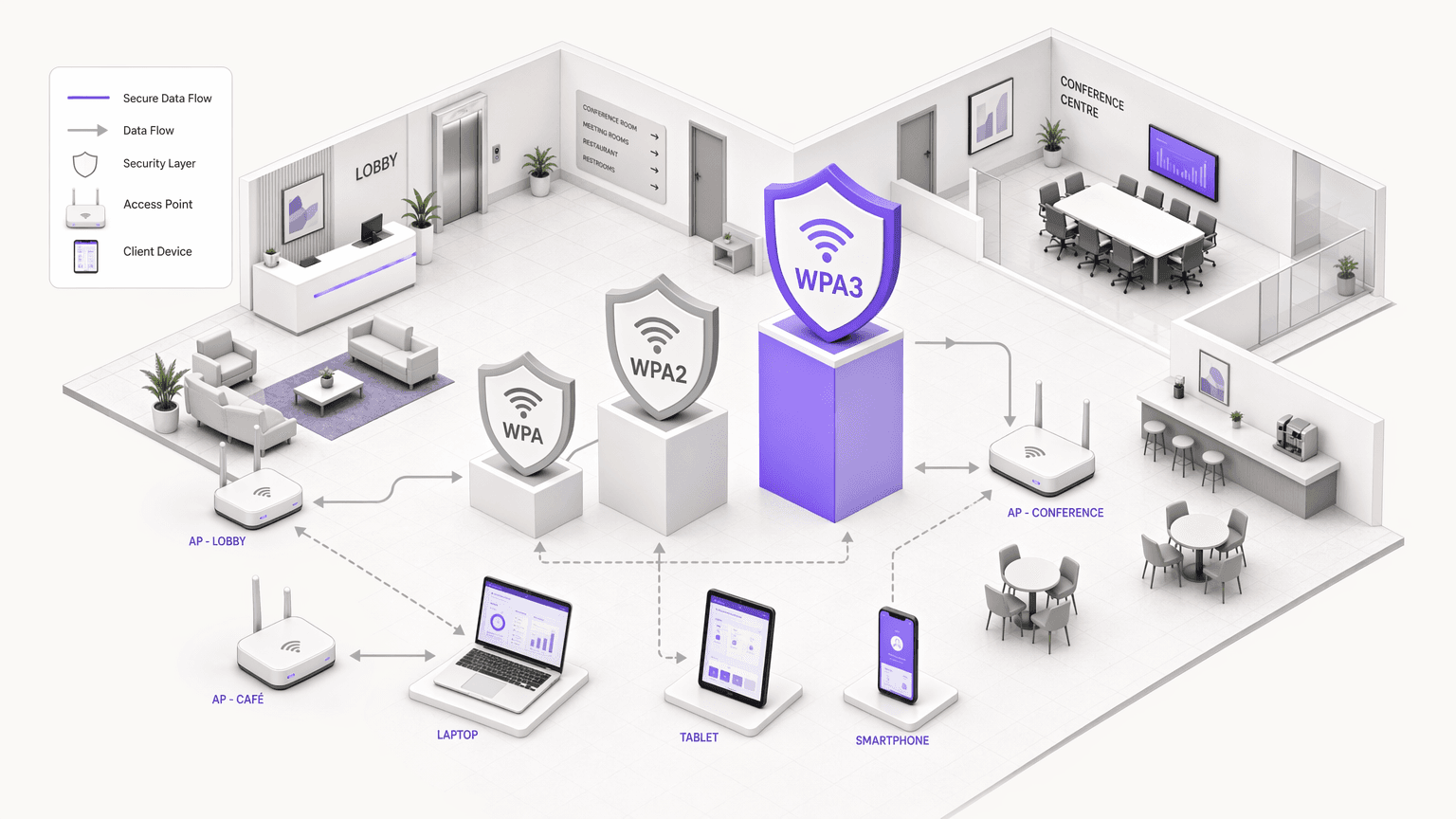
WPA, WPA2 and WPA3: What's the Difference and Which Should You Use?
This authoritative technical reference guide explores the architectural differences between WPA, WPA2, and WPA3 security protocols. It provides actionable deployment recommendations for IT managers and network architects to secure enterprise and guest WiFi environments while ensuring compliance and optimal performance.
WPA2 Enterprise: The Complete Guide
This guide provides a comprehensive technical reference for WPA2-Enterprise, covering 802.1X architecture, EAP method selection, and phased deployment strategies for enterprise environments. It is designed for IT managers, network architects, and venue operations directors who need to move beyond shared-key WiFi to a scalable, auditable, and compliance-ready authentication model. Purple's platform is positioned as a practical identity management layer for venues deploying secure guest and staff WiFi at scale.
What Is WiFi Security? A Complete Guide to Wireless Network Security
A comprehensive technical reference for IT leaders on securing enterprise wireless networks. This guide covers the evolution of encryption protocols, architectural best practices for segmentation, and defence strategies against common WiFi threats.
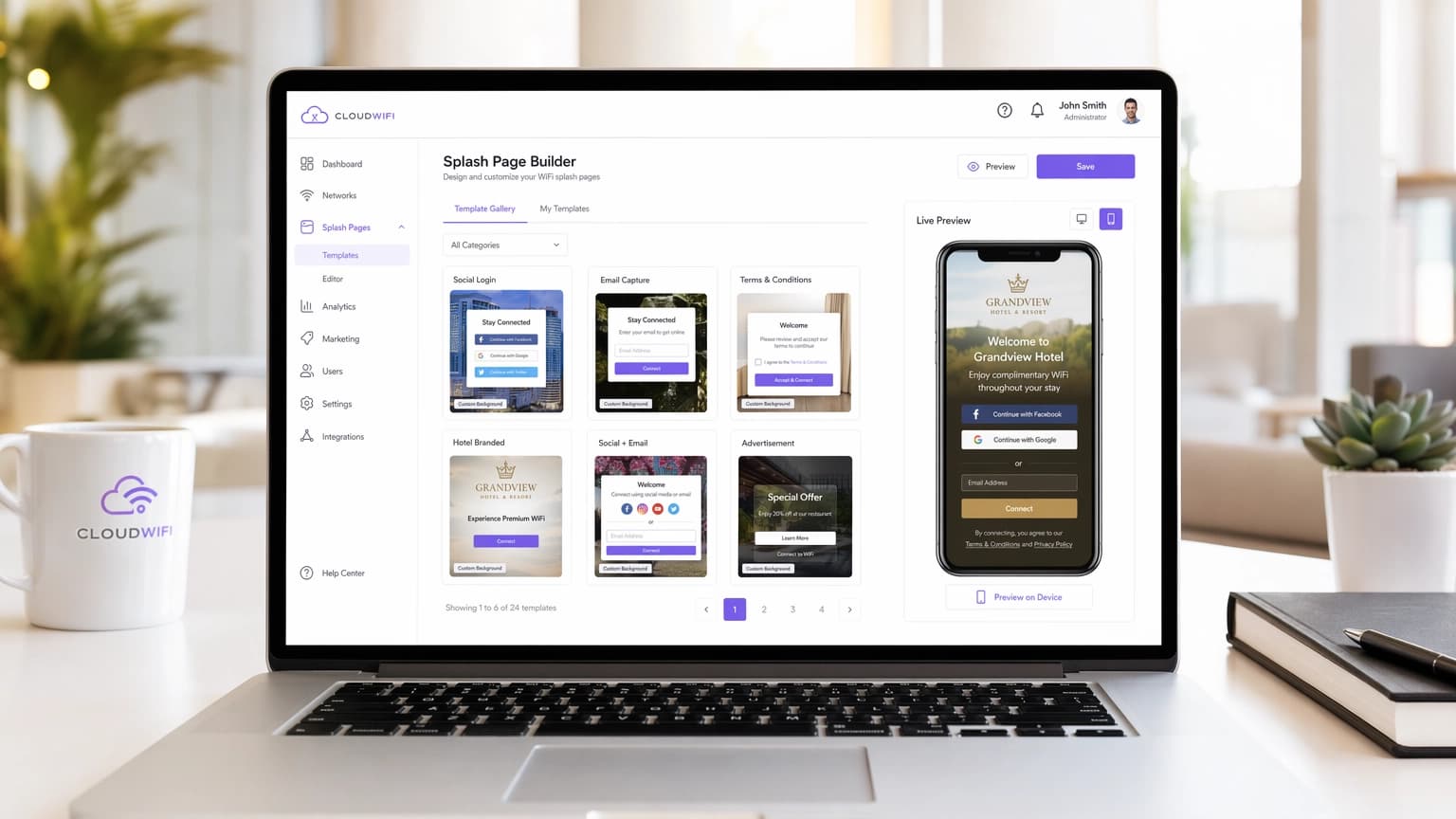
The 10 Top WiFi Splash Page Examples (And What Makes Them Work)
A technical reference guide for IT managers, network architects, and venue operations directors covering the design, architecture, and deployment of high-converting WiFi splash pages. The guide analyses 10 real-world implementation strategies across hospitality, retail, events, and public-sector environments, with specific guidance on authentication methods, GDPR compliance, walled garden configuration, and MAC randomization mitigation.
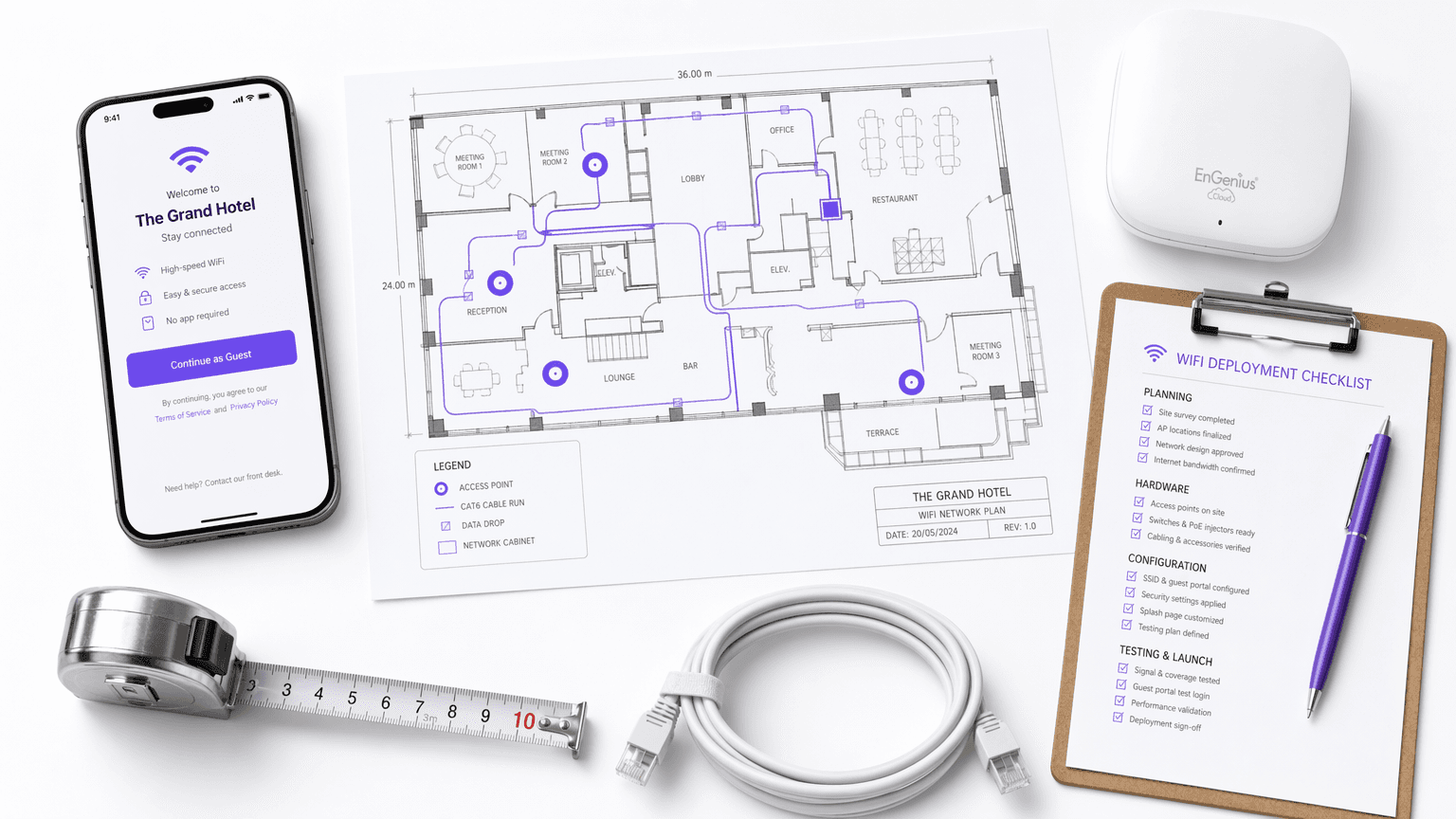
WiFi Guest Portal: What It Is and How to Optimise It
This authoritative guide details the architecture, implementation, and optimisation of WiFi guest portals. It provides actionable strategies for IT leaders to increase login completion rates, ensure GDPR compliance, and capture high-quality first-party data.
How to Create a Bespoke WiFi Login Page for Your Brand
This guide provides a comprehensive, implementation-ready reference for IT managers, network architects, and venue operations directors on how to create a fully branded guest WiFi login page — covering captive portal architecture, HTML/CSS customisation, GDPR compliance, and data capture strategy. It moves from technical foundations through to real-world deployment scenarios in hospitality and retail, with measurable business outcomes at each stage. For organisations running Purple's guest WiFi platform, the guide maps directly to the platform's portal builder, analytics, and consent management capabilities.



