Technical Guides
Deep, expert-led guides covering guest WiFi, analytics, captive portals, and modern venue technology. Each guide includes diagrams, worked examples, and audio podcasts.
249 guides
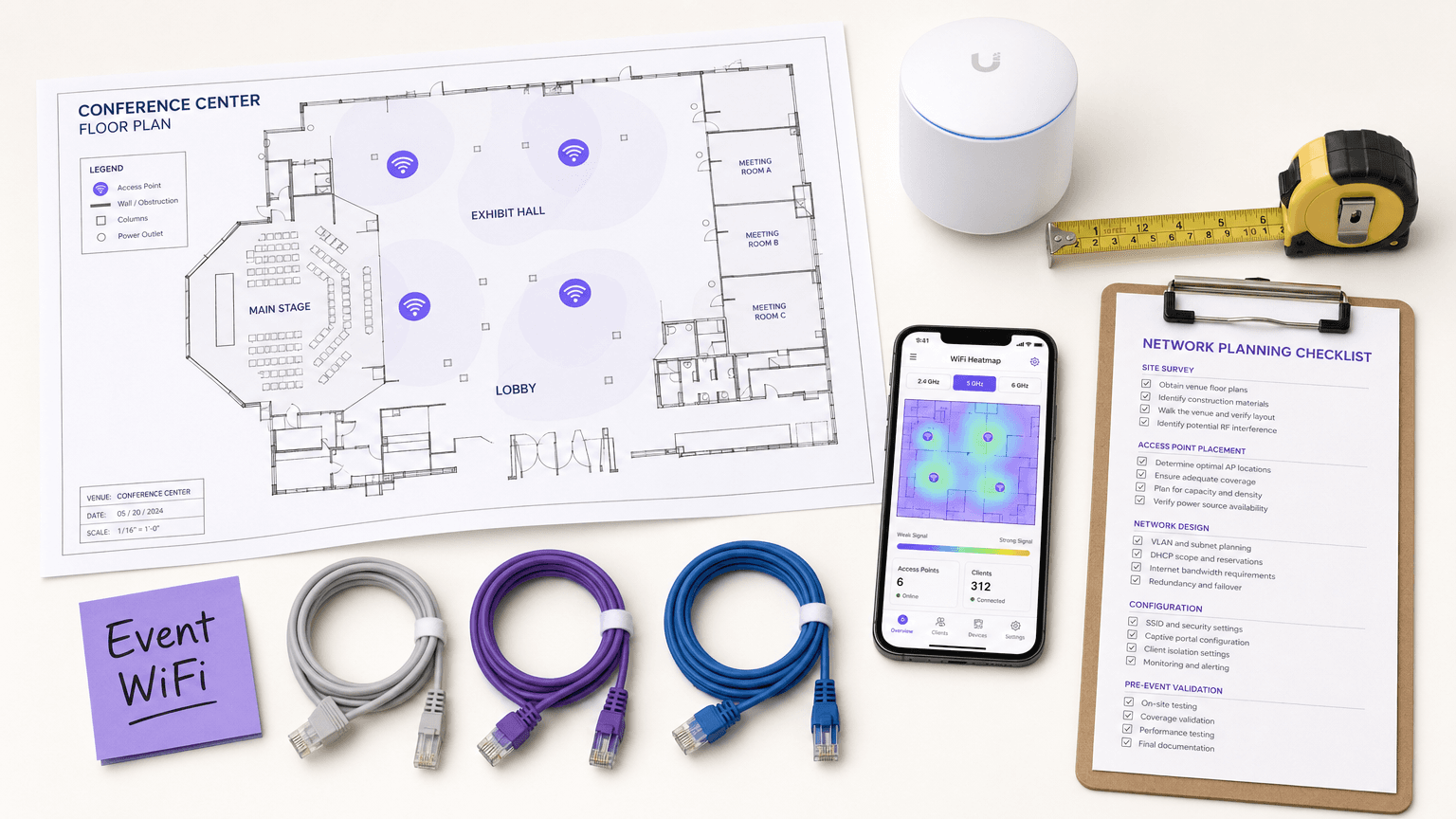
WiFi for Events: How to Deliver Reliable Connectivity for Large Crowds
This authoritative guide provides IT leaders, network architects, and venue operators with actionable strategies for designing, deploying, and managing high-density temporary WiFi networks for large-scale events — from corporate conferences to outdoor festivals. It covers RF design principles, capacity planning, security compliance, and how to leverage guest WiFi analytics to turn the network into a revenue-generating asset.
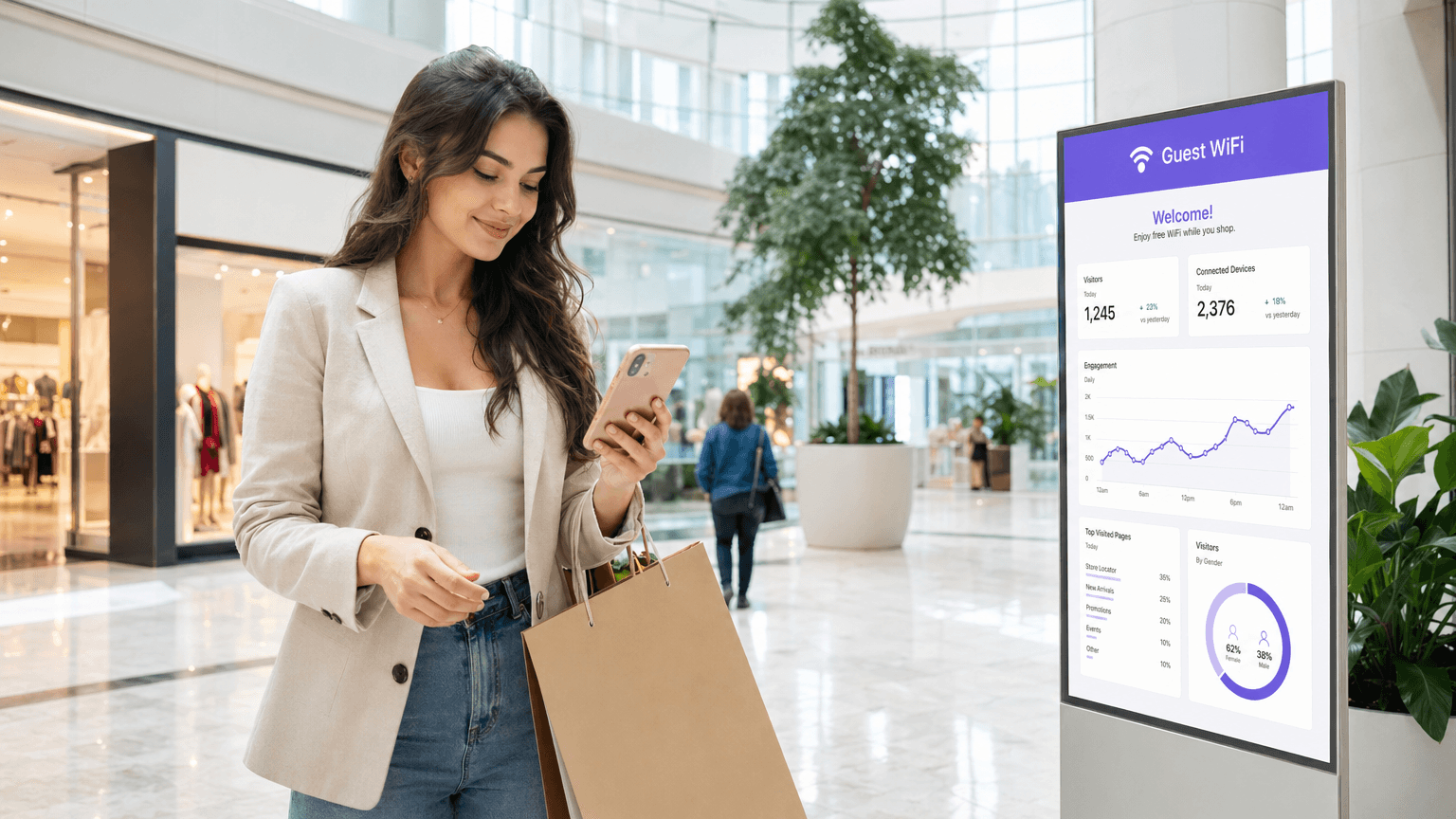
Commercial WiFi Systems: What Large Businesses Need to Know
This technical reference guide provides IT leaders and venue operators with actionable insights on designing, deploying, and managing commercial WiFi systems. It covers high-density architecture, security compliance, supplier selection, and how to utilise network data for business intelligence.
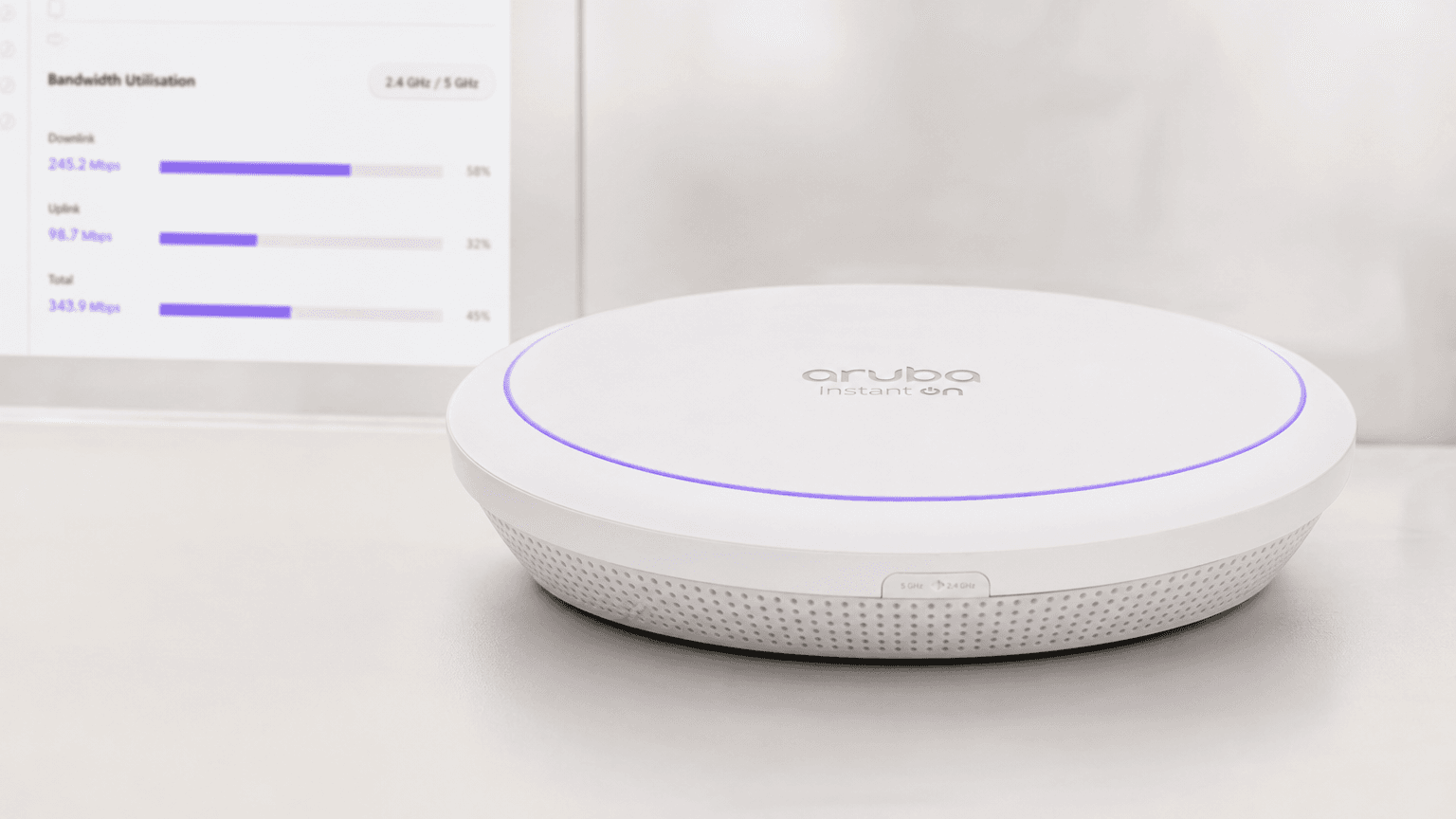
How to Manage Bandwidth on a WiFi Network
This authoritative guide provides IT managers, network architects, and CTOs with practical strategies for managing bandwidth on enterprise WiFi networks across high-density venues. It covers Quality of Service (QoS), traffic shaping, per-user rate limiting, and Deep Packet Inspection — the essential controls for running a fair, high-performance guest network. By integrating these techniques with Purple's guest WiFi and analytics platform, organisations can move from reactive firefighting to proactive, policy-driven network management.
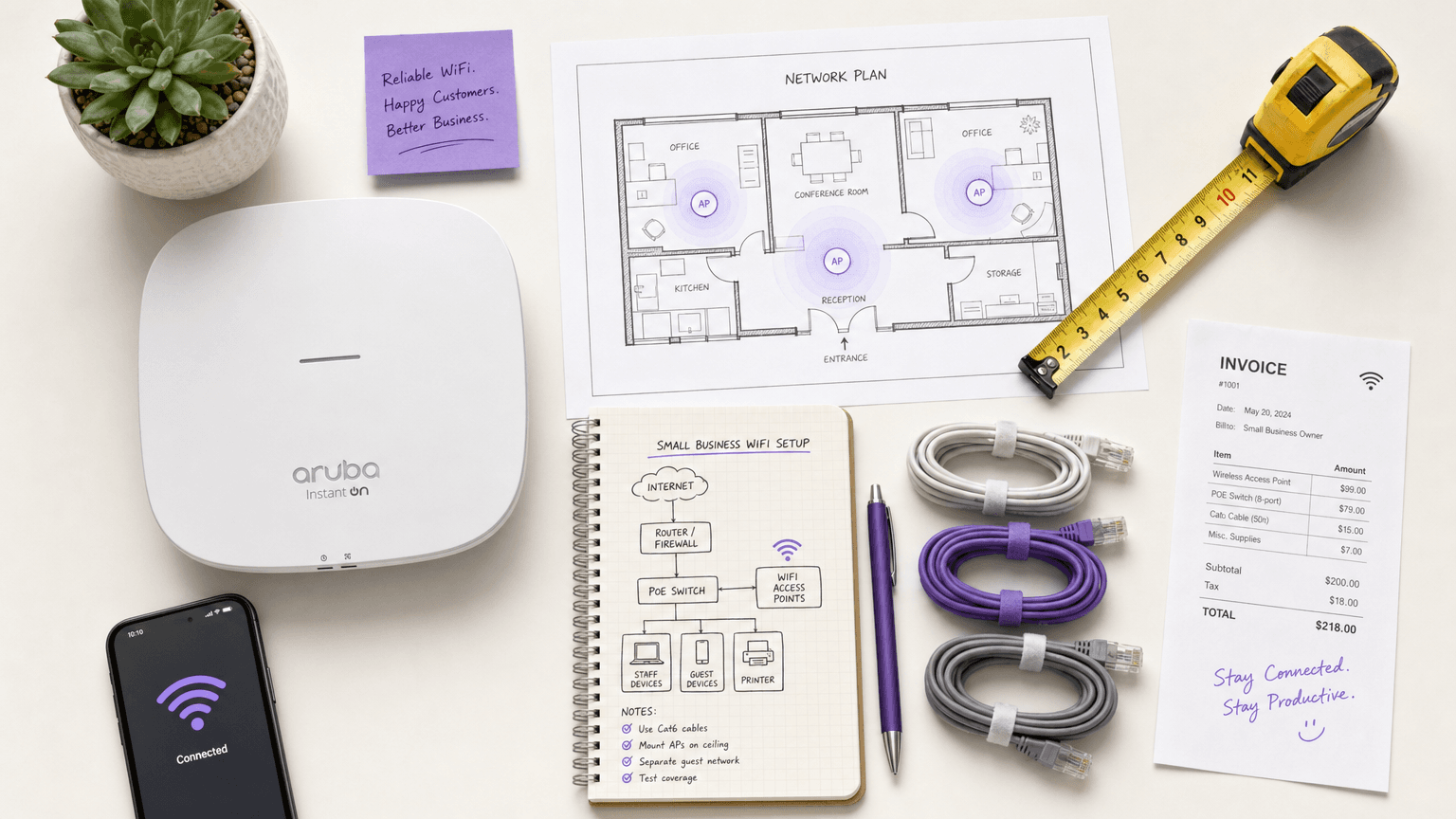
Small Business WiFi: How to Get the Set-up Right Without Breaking the Budget
This authoritative guide provides IT managers, venue operators, and CTOs with a practical blueprint for deploying enterprise-grade WiFi in small business environments without exceeding budget constraints. It covers layered network architecture, VLAN segmentation, hardware selection, and guest onboarding strategies. By integrating analytics platforms like Purple, businesses can transform their WiFi from a cost centre into a measurable revenue-generating asset.
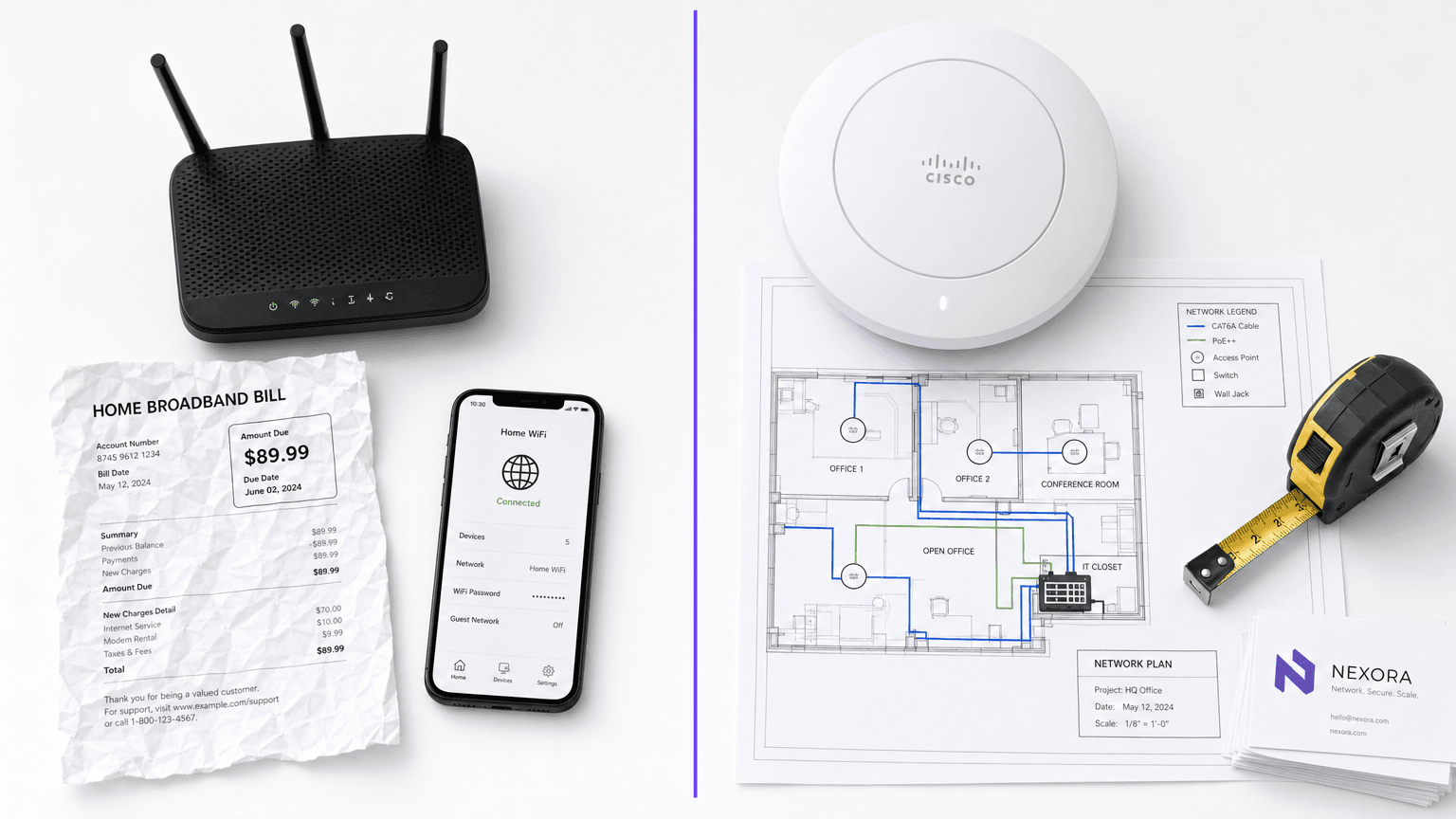
Business WiFi vs. Consumer WiFi: What's the Difference?
This authoritative guide explores the critical technical distinctions between business and consumer WiFi infrastructure. It provides IT managers and venue operators with actionable insights on hardware capabilities, security standards, and management architecture necessary for commercial deployments.

How to Set Up WiFi for Your Business: A Complete Guide
This guide provides a comprehensive, vendor-neutral blueprint for deploying enterprise-grade WiFi, covering network segmentation, hardware selection, and security protocols from WPA3 to 802.1X. It details how IT leaders across retail, hospitality, and public sector can transform wireless infrastructure from a cost centre into a strategic asset by leveraging captive portals and analytics for first-party data capture, compliance, and measurable ROI.
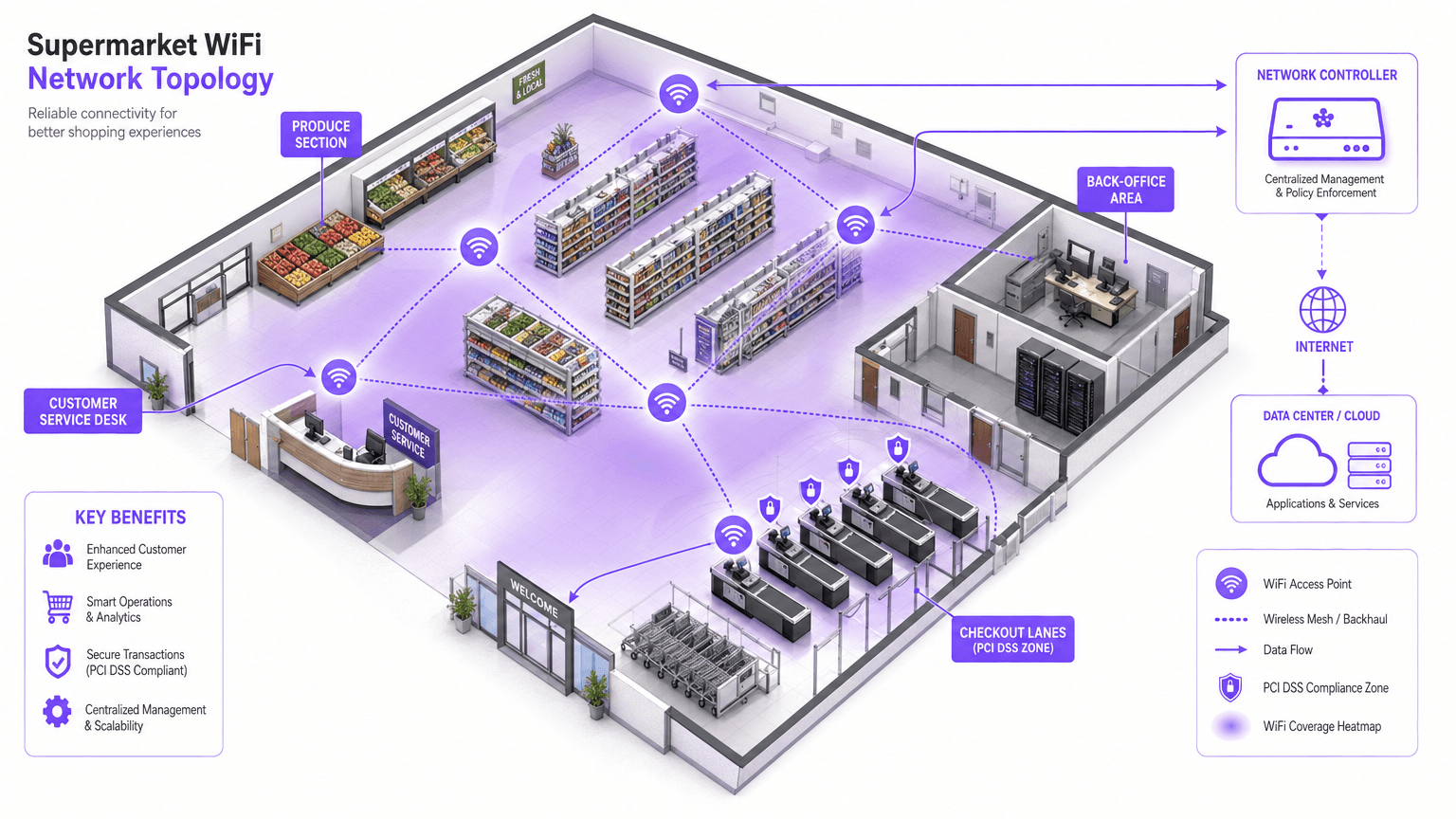
Is Supermarket WiFi Safe? A Shopper's Guide
This authoritative guide examines the technical realities of supermarket WiFi safety, providing actionable architecture and security strategies for IT leaders in the retail sector. It details the threat landscape — from Evil Twin APs to Man-in-the-Middle attacks — alongside the mitigation stack required to protect consumers and enterprise operations. Retailers and venue operators will find concrete implementation guidance covering VLAN segmentation, client isolation, WPA3, PCI DSS compliance, and GDPR-compliant guest onboarding via platforms like Purple.

Office WiFi Set-up: How to Construct a Reliable Wireless Network
This authoritative guide details the technical architecture and strategic deployment of enterprise-grade office WiFi. It covers capacity-based design, access point placement, secure user segmentation, and how to utilise network infrastructure for business intelligence.
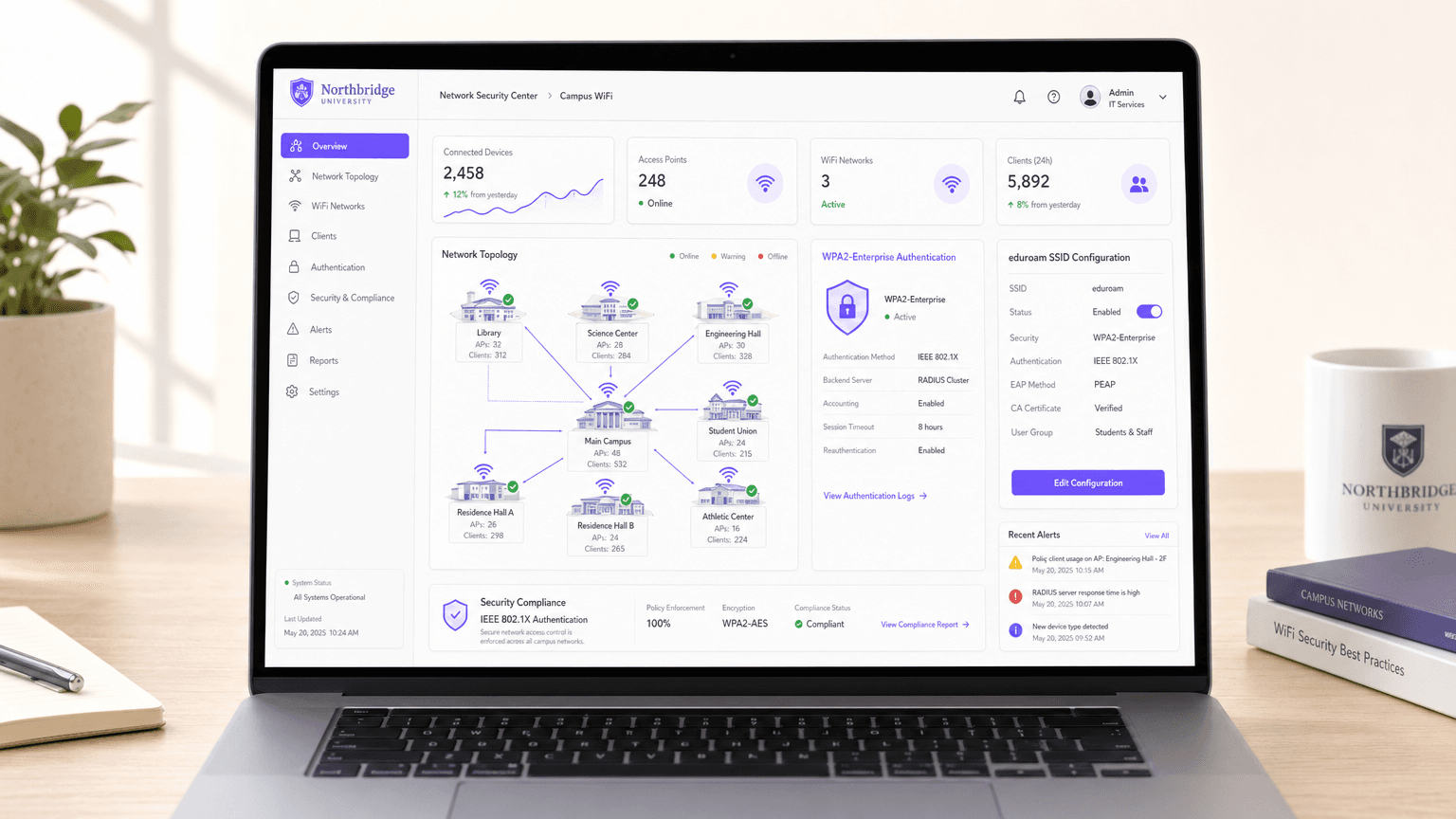
Is University WiFi Safe? A Guide for Students
A comprehensive technical reference for IT managers and venue operators on the security architecture of university WiFi (eduroam/802.1X). This guide unpacks how enterprise-grade authentication works, its implementation pitfalls, and how these principles apply to hospitality, retail, and public sector deployments.
Is Train WiFi Safe? What Rail Passengers Need to Know
This guide examines the security architecture of passenger rail WiFi networks, dissecting the threat landscape from packet sniffing and Evil Twin attacks to Man-in-the-Middle exploits. It provides actionable deployment guidance for operators and corporate IT teams, covering client isolation, captive portal authentication, DNS filtering, and the path to Hotspot 2.0 — with direct integration points for Purple's Guest WiFi and analytics platform.
Is Hospital WiFi Safe? What Patients and Visitors Should Know
This comprehensive technical reference guide examines the security architecture of hospital guest WiFi networks. It provides IT managers and venue operators with actionable implementation strategies, focusing on network segmentation, encryption standards, and compliance frameworks to ensure patient data remains protected without compromising clinical operations.

Is Café and Coffee Shop WiFi Safe?
This authoritative technical guide examines the real security risks of café and coffee shop WiFi for both consumers and venue operators, covering threat vectors including Evil Twin attacks, packet sniffing, and client-to-client exploits. It provides IT managers and network architects with a practical, standards-referenced deployment framework — from VLAN segmentation and WPA3 migration to captive portal implementation and GDPR-compliant analytics. Purple's Guest WiFi and analytics platform is positioned as a concrete solution across hospitality, retail, and public-sector environments.
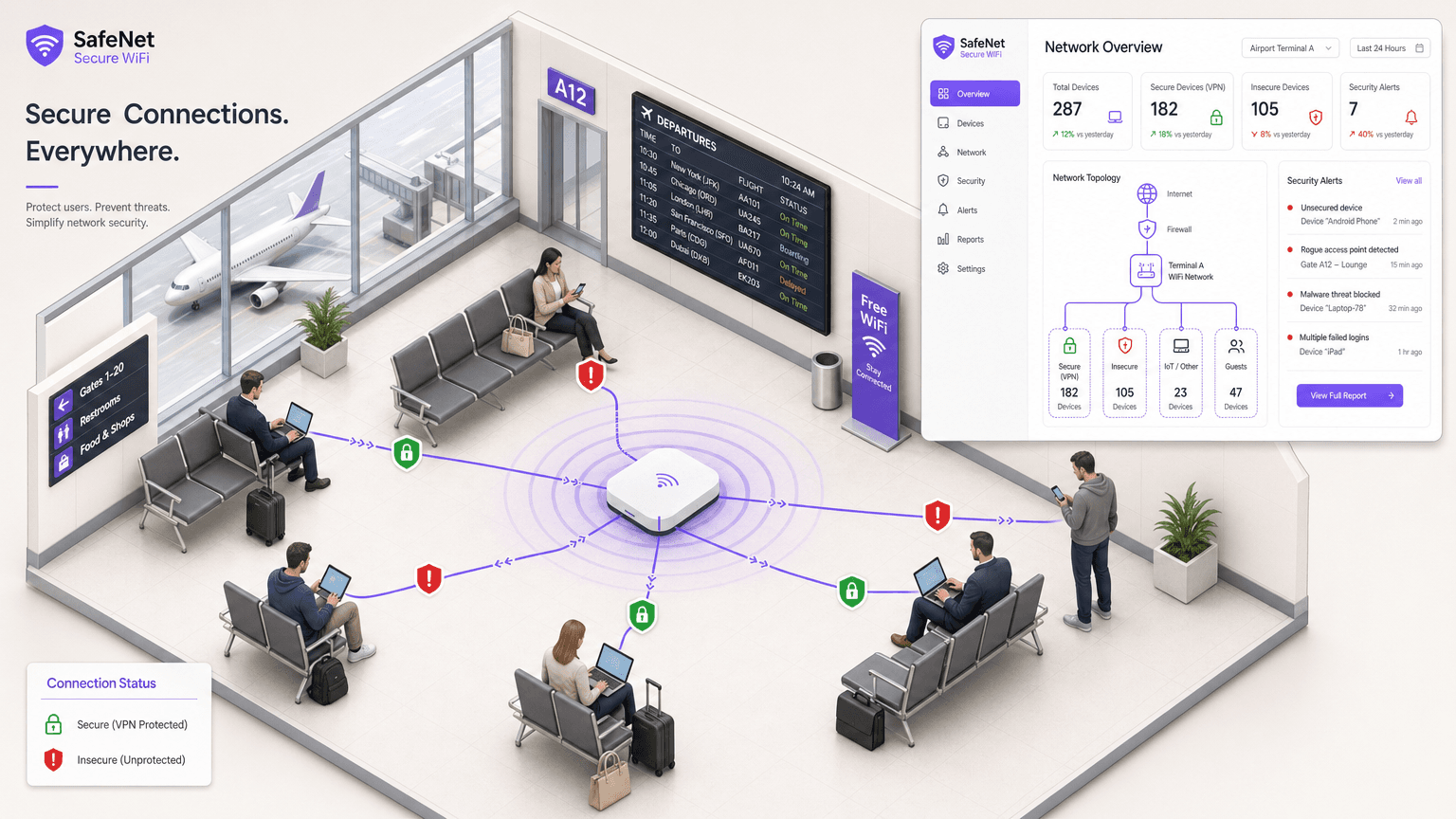
Is Airport WiFi Safe? A Traveller's Security Guide
This guide provides an authoritative technical reference for IT managers, network architects, and venue operations directors on the security risks of airport WiFi and how to mitigate them. It covers the full threat landscape — from Evil Twin access points to rogue DHCP servers — and delivers a practical, standards-based deployment framework using IEEE 802.1X, WPA3, and network segmentation. It also maps Purple's Guest WiFi and analytics platform to each risk vector, providing concrete integration points for operators looking to deploy secure, GDPR-compliant, and commercially viable public WiFi.
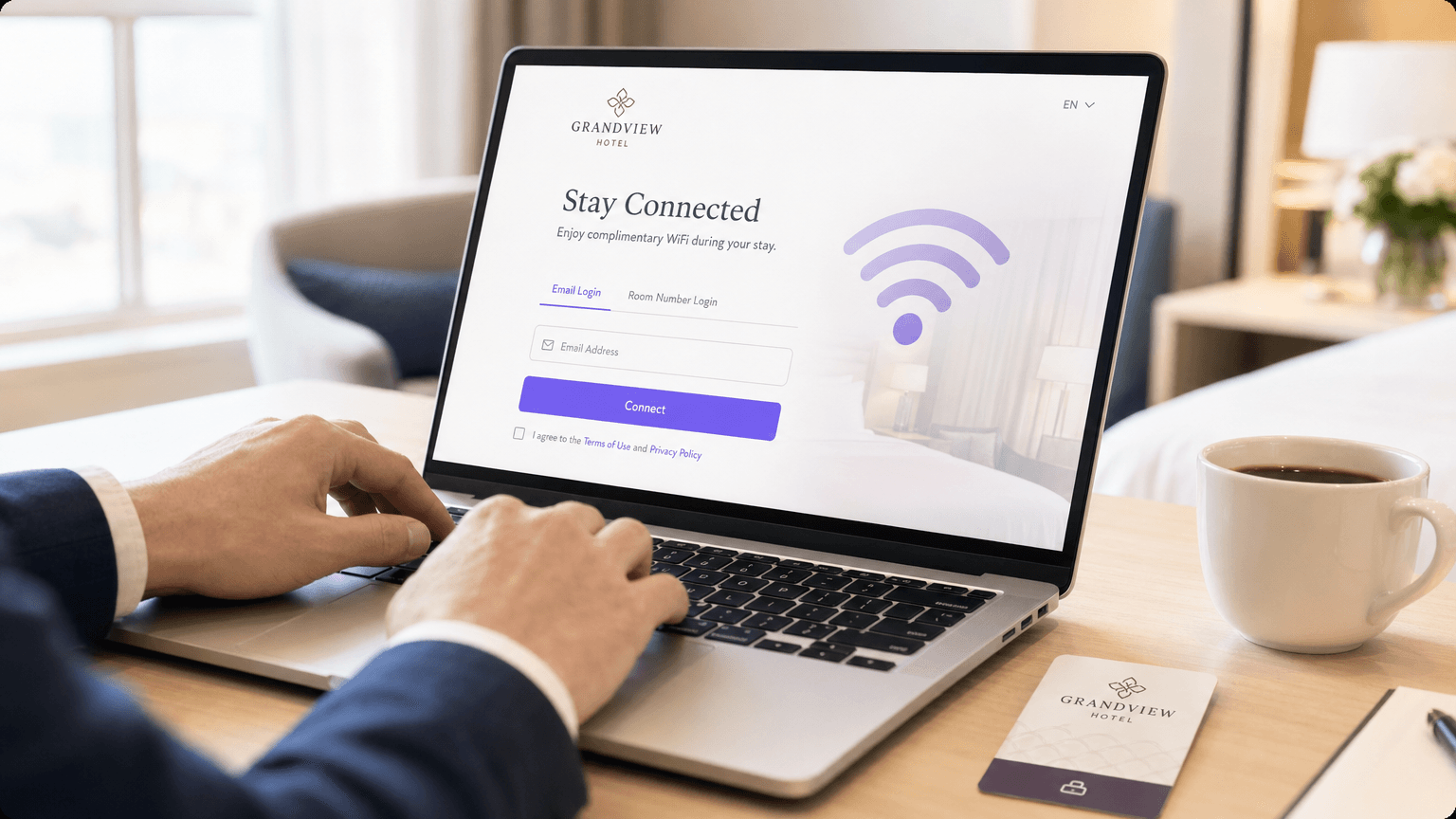
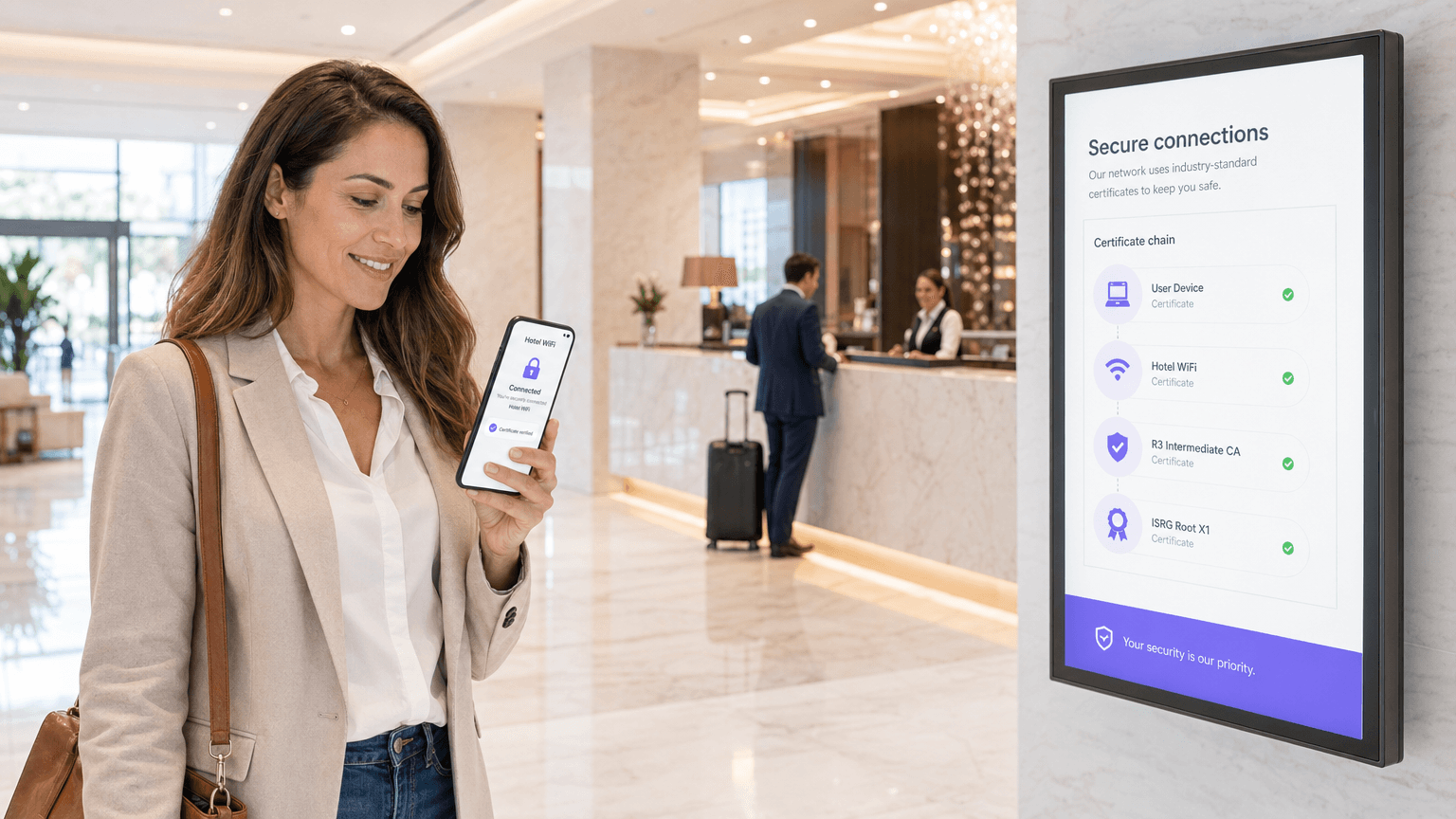
Is Hotel WiFi Safe? What Every Traveller Needs to Know
This comprehensive technical guide details the specific security risks inherent in hotel WiFi networks, including rogue APs and MITM attacks. It provides actionable, vendor-neutral implementation steps for IT managers and network architects to secure their wireless infrastructure and utilise managed guest WiFi platforms.

Is Public WiFi Safe? The Definitive Guide
This definitive guide provides enterprise IT leaders with actionable strategies for architecting secure public WiFi networks. It details the technical mitigation of primary threats like MITM attacks and rogue access points, while outlining how to leverage platforms like Purple to ensure compliance, protect corporate infrastructure, and safely monetise guest connectivity.
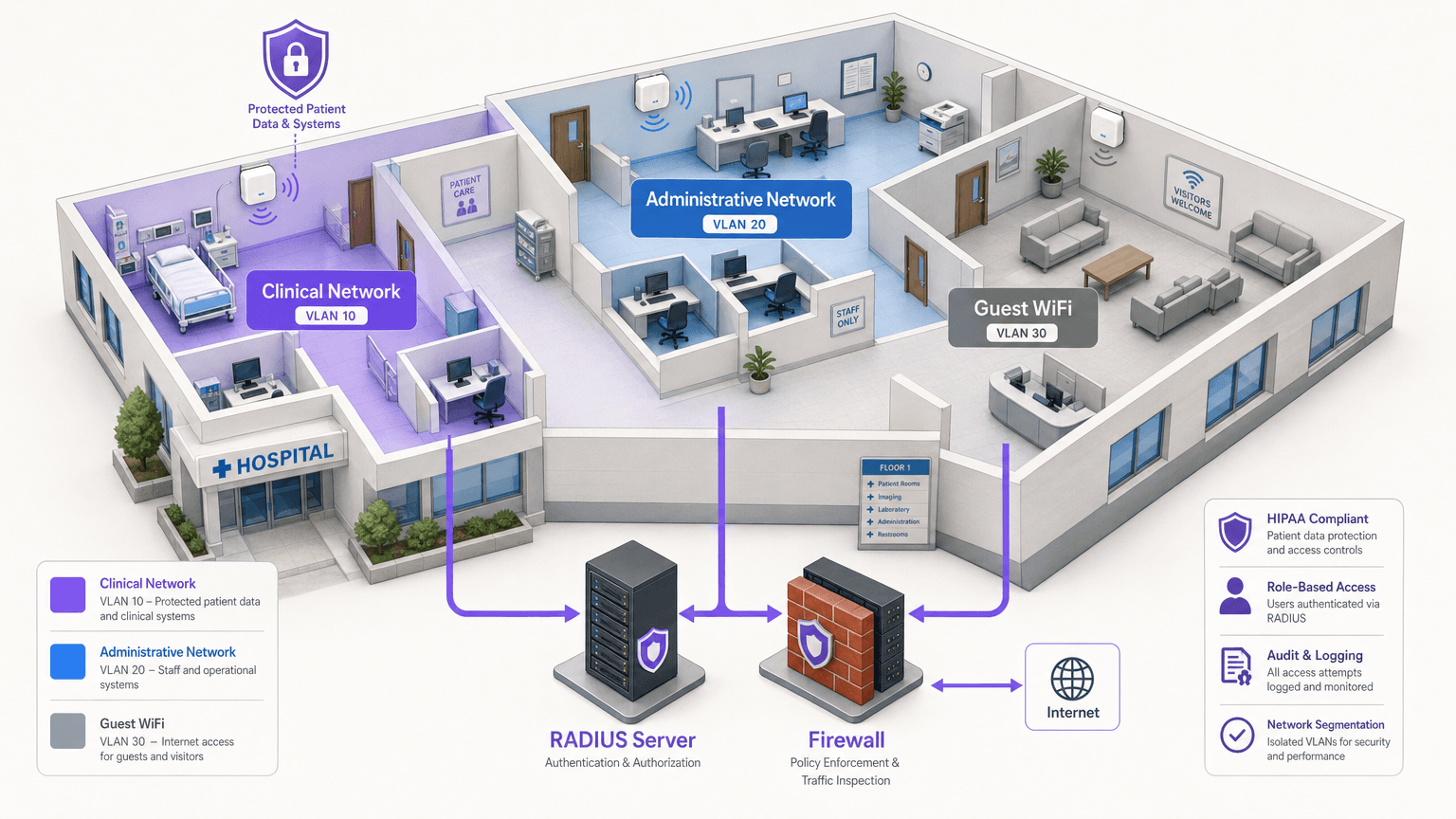
HIPAA-Compliant WiFi: A Guide for Healthcare Organisations
This technical reference guide provides actionable compliance strategies for healthcare IT teams deploying enterprise and guest WiFi. It covers network segmentation, 802.1X authentication, audit logging, and how to implement secure, isolated wireless access using Purple's platform.

Enterprise WiFi Solutions: A Buyer's Guide
A comprehensive, vendor-agnostic technical reference for IT managers and CTOs evaluating enterprise WiFi solutions. Covers hardware architecture, cloud management, security standards, and the strategic deployment of guest WiFi and analytics to drive ROI.

How to Monitor WiFi Network Traffic: A Guide for IT Teams
This technical guide provides actionable strategies for monitoring enterprise WiFi traffic, focusing on architecture, security, and performance. It equips IT teams in hospitality, retail, and public sectors with the frameworks needed to deploy scalable, secure network monitoring solutions.
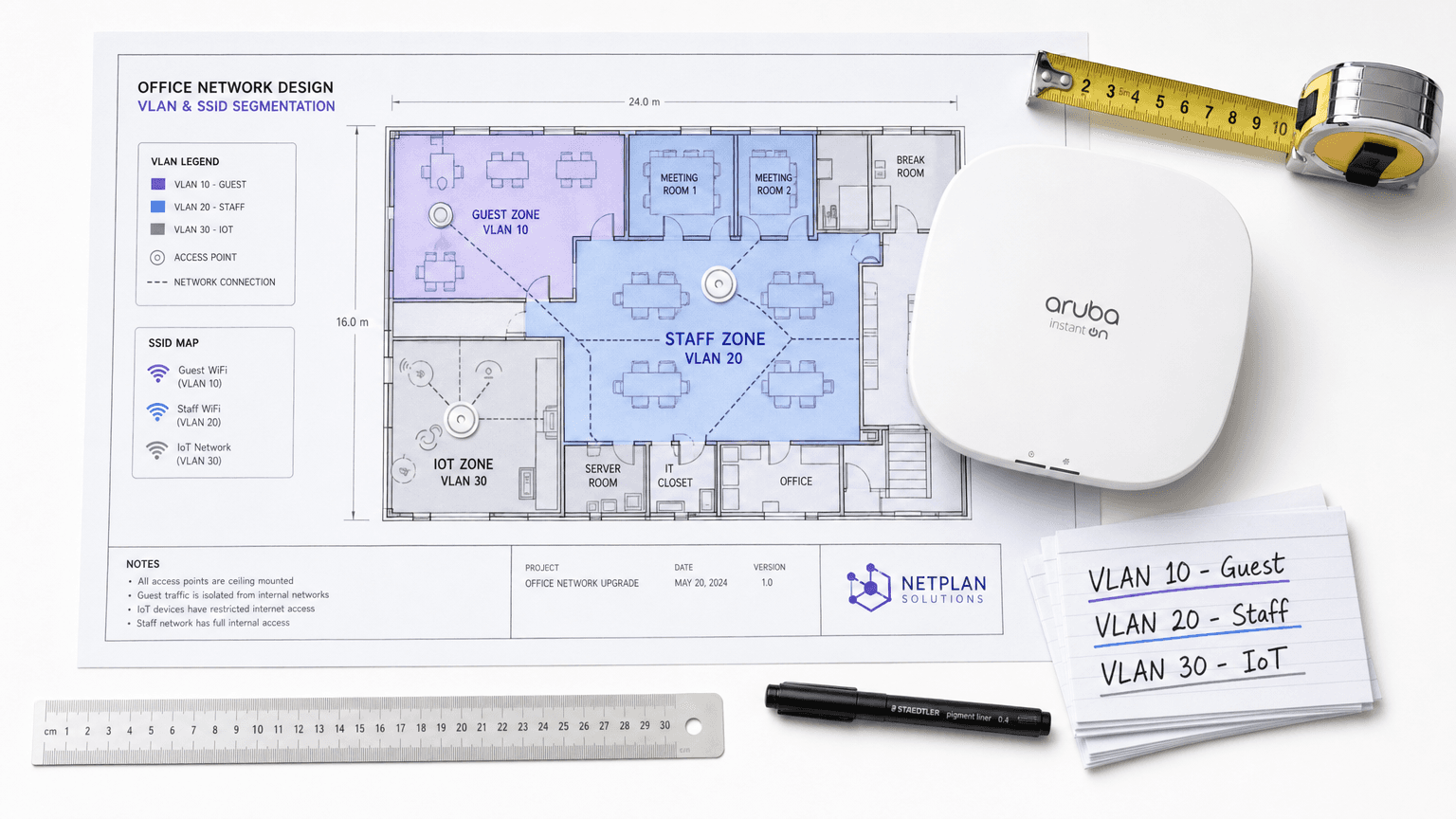
WiFi Network Segmentation: VLANs, SSIDs and Guest Traffic
This authoritative guide explores the critical role of WiFi network segmentation using VLANs and multiple SSIDs. It provides actionable implementation strategies for IT leaders across hospitality, retail, and public sectors to secure networks, isolate guest traffic, and ensure compliance without sacrificing performance.
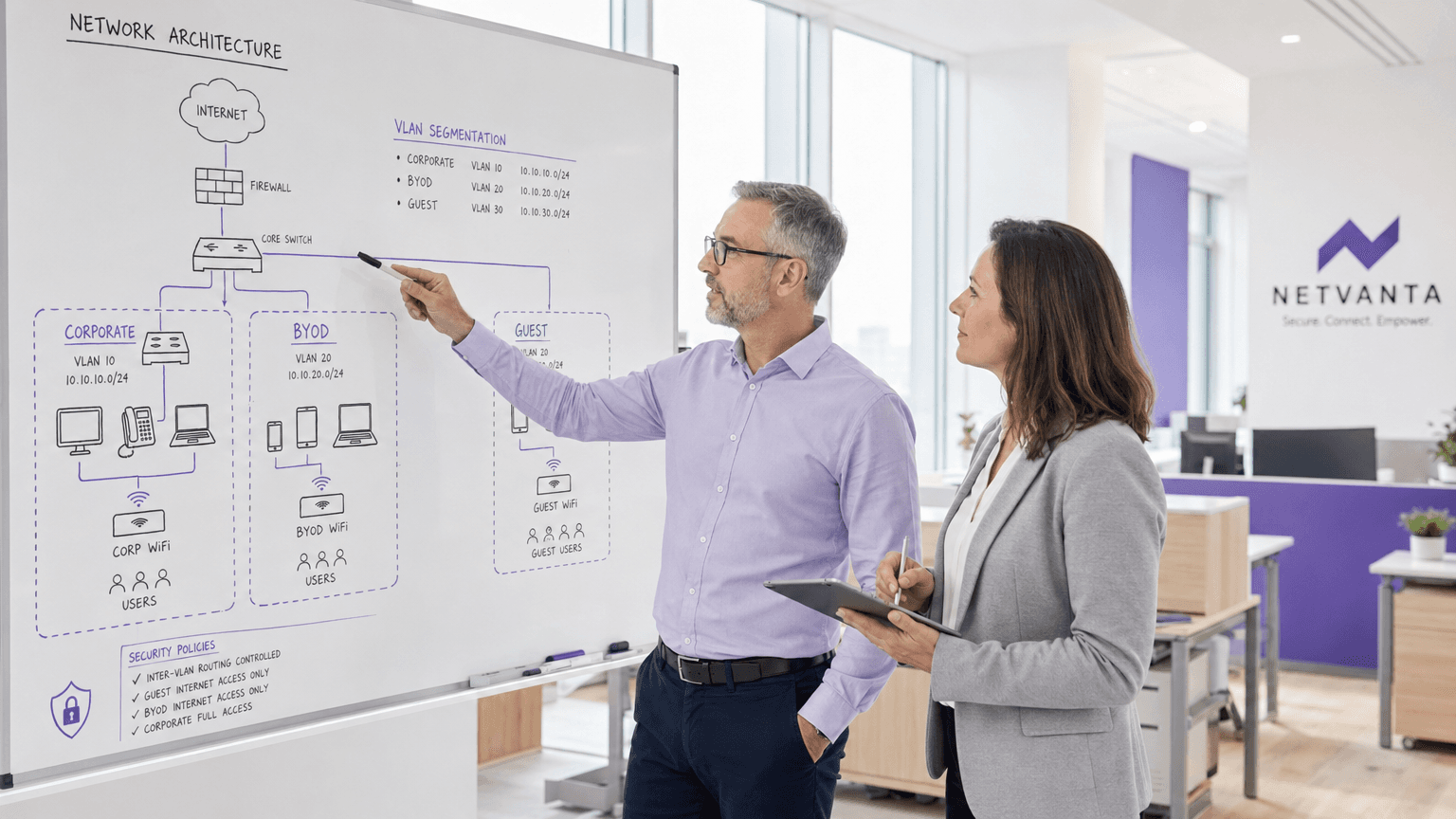
BYOD WiFi Security: How to Safely Allow Personal Devices onto Your Network
A pragmatic, vendor-neutral guide for IT leaders on securing BYOD WiFi access. It covers implementing 802.1X authentication, MDM integration, and strict network segmentation to protect corporate assets while enabling personal devices.
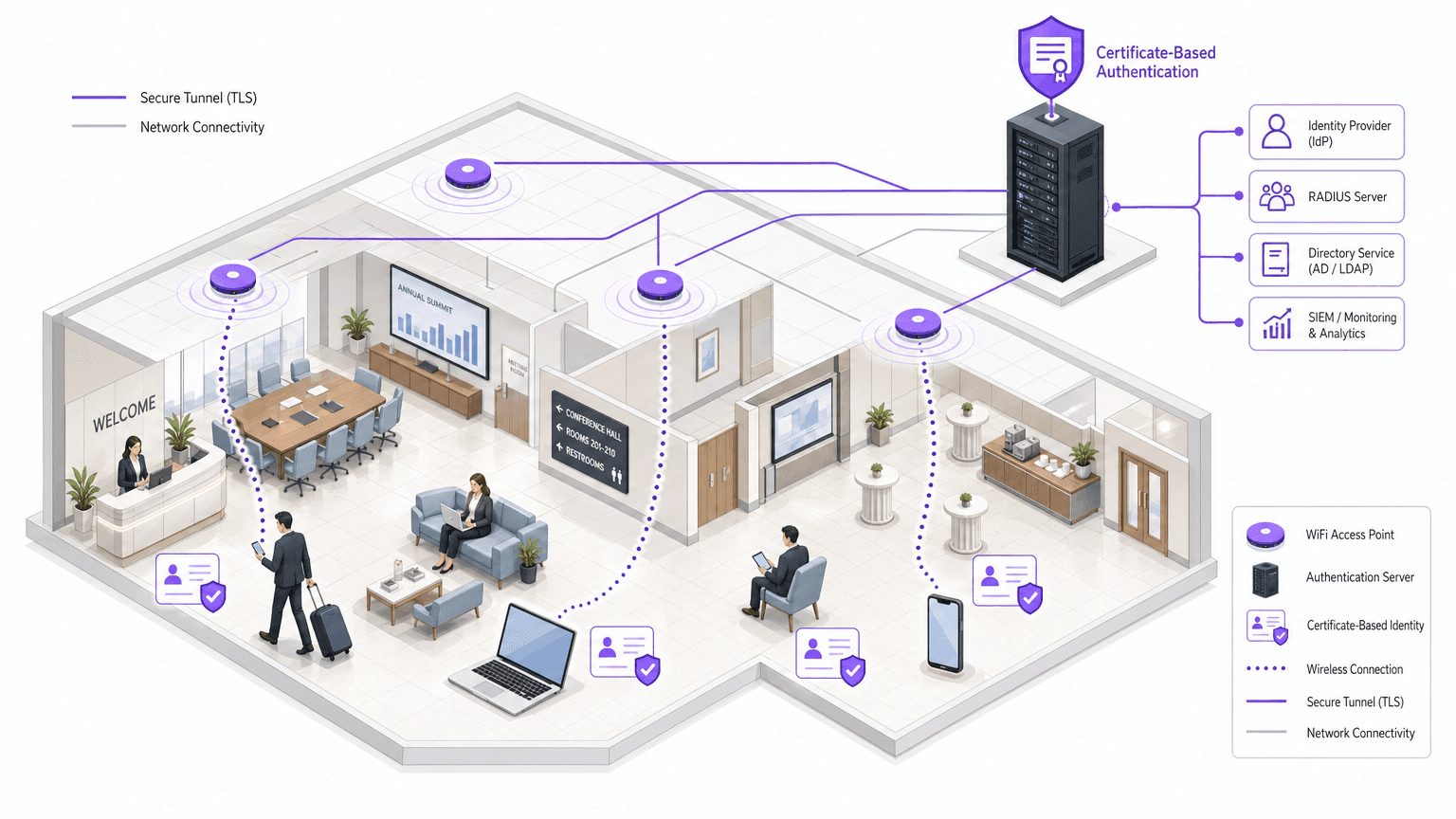
Passwordless WiFi: What It Is and How to Implement It
This technical reference guide provides network architects and IT managers with a comprehensive blueprint for transitioning from vulnerable shared passwords to secure, certificate-based WiFi authentication. It covers 802.1X architecture, EAP-TLS deployment strategies, PKI management, and the measurable business impact of reducing helpdesk overheads while enhancing enterprise security posture and compliance readiness.
What Is PKI? How Public Key Infrastructure Powers WiFi Security
This authoritative technical reference guide explains Public Key Infrastructure (PKI) and its critical role in securing enterprise WiFi networks across hospitality, retail, and public-sector venues. Designed for IT managers, network architects, and CTOs, it provides actionable guidance on certificate-based authentication, IEEE 802.1X deployment with EAP-TLS, and how Purple's platform leverages these standards for scalable, compliant connectivity. Readers will leave with a concrete deployment roadmap, real-world case studies, and a clear understanding of how PKI eliminates the vulnerabilities of shared-secret WiFi.
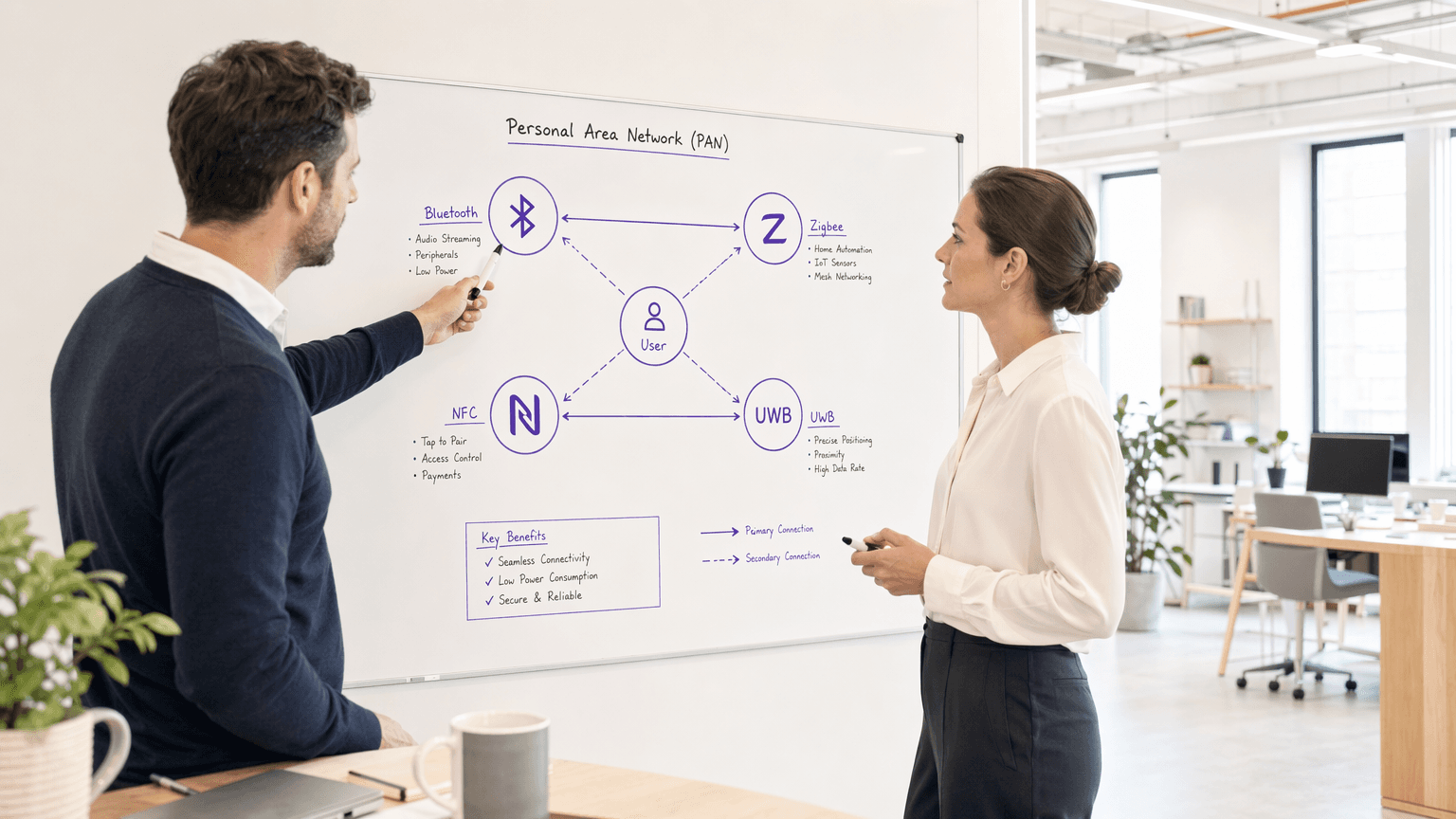
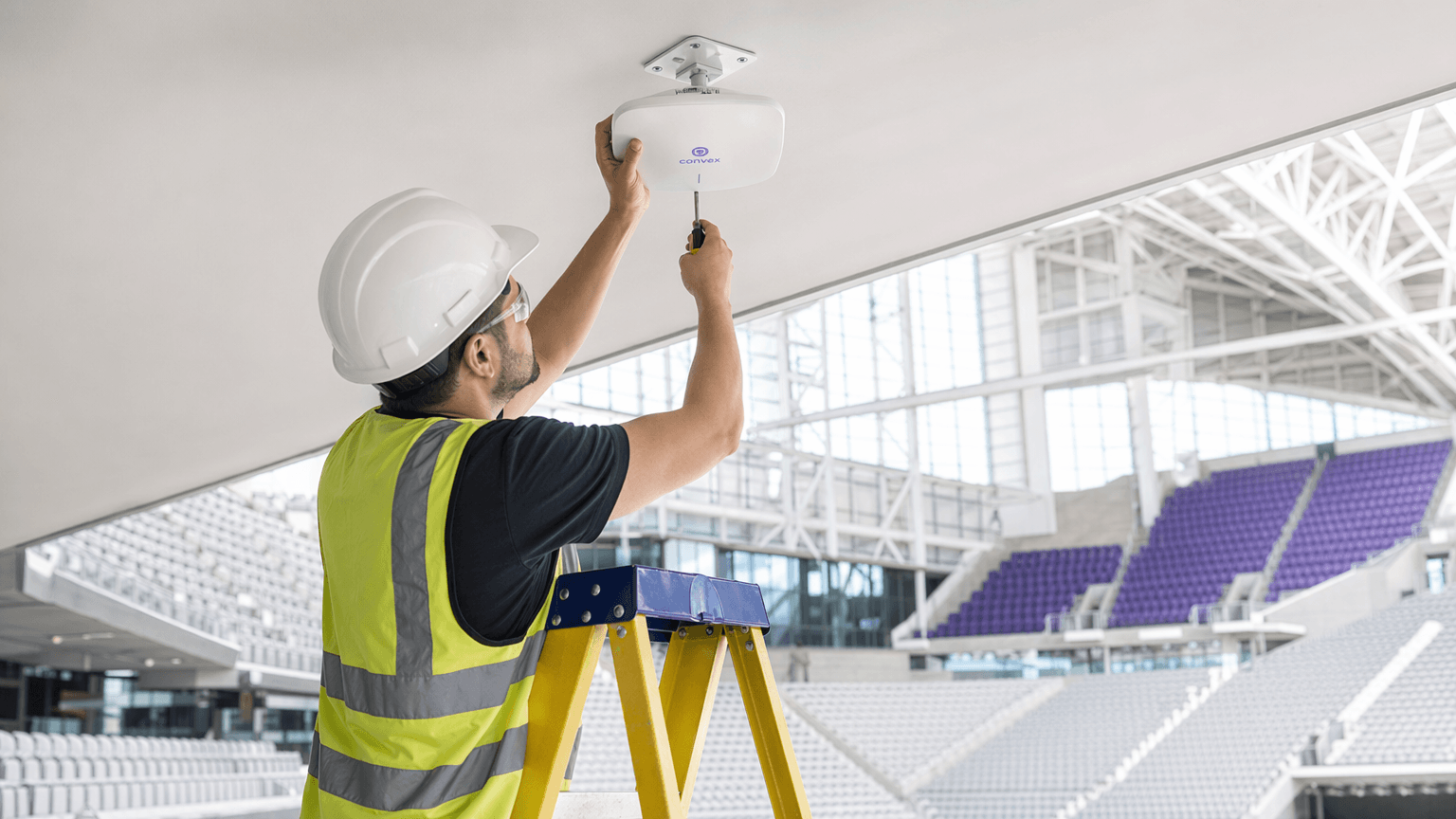
Personal Area Networks (PANs): Technologies, Applications, Security, and Future Trends
This authoritative technical reference guide covers the architecture, deployment, and security of Personal Area Networks (PANs) for enterprise environments, examining Bluetooth Low Energy, Zigbee, NFC, and Ultra-Wideband in detail. It provides actionable guidance for IT managers and network architects managing high-density venues such as hotels, retail chains, stadiums, and healthcare facilities. The guide addresses RF spectrum management, network segmentation, compliance requirements, and emerging PAN trends to help senior IT leaders make informed deployment decisions.
802.11ac (WiFi 5): A Technical Deep Dive into Features, Performance, and Deployment Strategies
This comprehensive technical guide provides a deep dive into the 802.11ac (WiFi 5) standard, detailing its architecture, performance characteristics, and practical deployment strategies. It equips IT managers and network architects with the knowledge required to optimise existing infrastructure, manage high-density environments, and make evidence-based decisions regarding future upgrades.



