Extreme Networks et Purple WiFi : Intégration ExtremeCloud IQ
Ce guide de référence technique fournit un plan complet pour l'intégration de Purple WiFi avec la plateforme ExtremeCloud IQ d'Extreme Networks. Il détaille le flux architectural, les étapes de configuration pour la redirection du Captive Portal et l'authentification RADIUS, ainsi que les meilleures pratiques pour un accès invité sécurisé et riche en données dans les environnements d'entreprise.
🎧 Écouter ce guide
Voir la transcription
- Résumé Exécutif
- Approfondissement Technique
- Aperçu Architectural
- Le Flux d'Authentification RADIUS
- Compatibilité Matérielle
- Guide d'Implémentation
- Étape 1 : Configuration du SSID et du Captive Portal
- Étape 2 : Configuration des serveurs AAA et RADIUS
- Étape 3 : Attribution Dynamique de VLAN (Facultatif mais Recommandé)
- Bonnes Pratiques
- Dépannage et Atténuation des Risques
- ROI et Impact Commercial

Résumé Exécutif
Pour les entreprises qui standardisent leur infrastructure sur Extreme Networks, le déploiement d'une solution WiFi invité de qualité professionnelle nécessite une intégration étroite entre la couche réseau physique et la couche d'intelligence applicative. Ce guide de référence technique détaille l'architecture, la configuration et le déploiement opérationnel de Purple WiFi dans un environnement ExtremeCloud IQ. En tirant parti de la redirection du Captive Portal et de l'authentification RADIUS, les équipes informatiques peuvent transformer le Guest WiFi standard en un atout sécurisé, conforme et riche en données. Cette intégration permet l'attribution dynamique de VLAN, une comptabilité de session précise et des WiFi Analytics complètes sans introduire de complexité architecturale. Ce guide fournit des stratégies de déploiement exploitables pour les professionnels informatiques seniors gérant des environnements à haute densité dans les secteurs de l' Hôtellerie , du Commerce de détail et des administrations publiques.
Écoutez notre podcast de briefing de consultant ci-dessous pour un aperçu complet de l'architecture d'intégration et des meilleures pratiques de mise en œuvre.
Approfondissement Technique
Aperçu Architectural
L'intégration entre ExtremeCloud IQ et la plateforme Purple WiFi repose sur des protocoles standards de l'industrie, principalement la redirection HTTP/HTTPS et RADIUS (Remote Authentication Dial-In User Service). Cette architecture garantit que les points d'accès (APs) Extreme Networks gèrent l'environnement RF et le plan de données, tandis que Purple gère la gestion des identités, l'application des politiques et la capture des données.
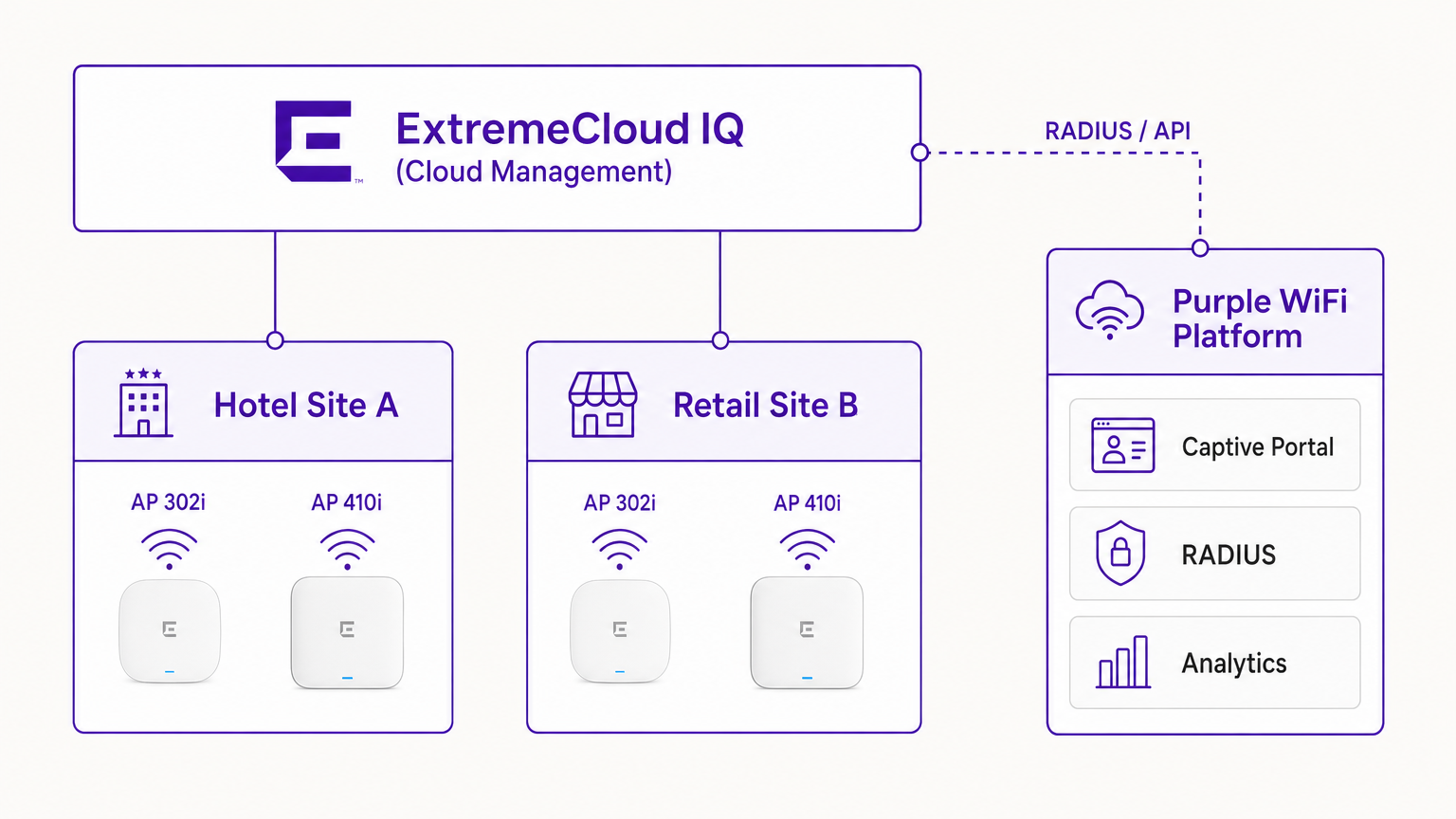
Dans un déploiement typique, le contrôleur ExtremeCloud IQ (ou l'AP fonctionnant de manière autonome sous gestion cloud) est configuré avec un SSID ouvert ou WPA3-SAE. Lorsqu'un appareil invité s'associe, l'AP place l'appareil dans un état de pré-authentification. L'AP intercepte les requêtes HTTP initiales et redirige le client vers l'URL du Captive Portal Purple.
Le Flux d'Authentification RADIUS
Le cœur de la sécurité et de l'application des politiques est l'échange RADIUS.
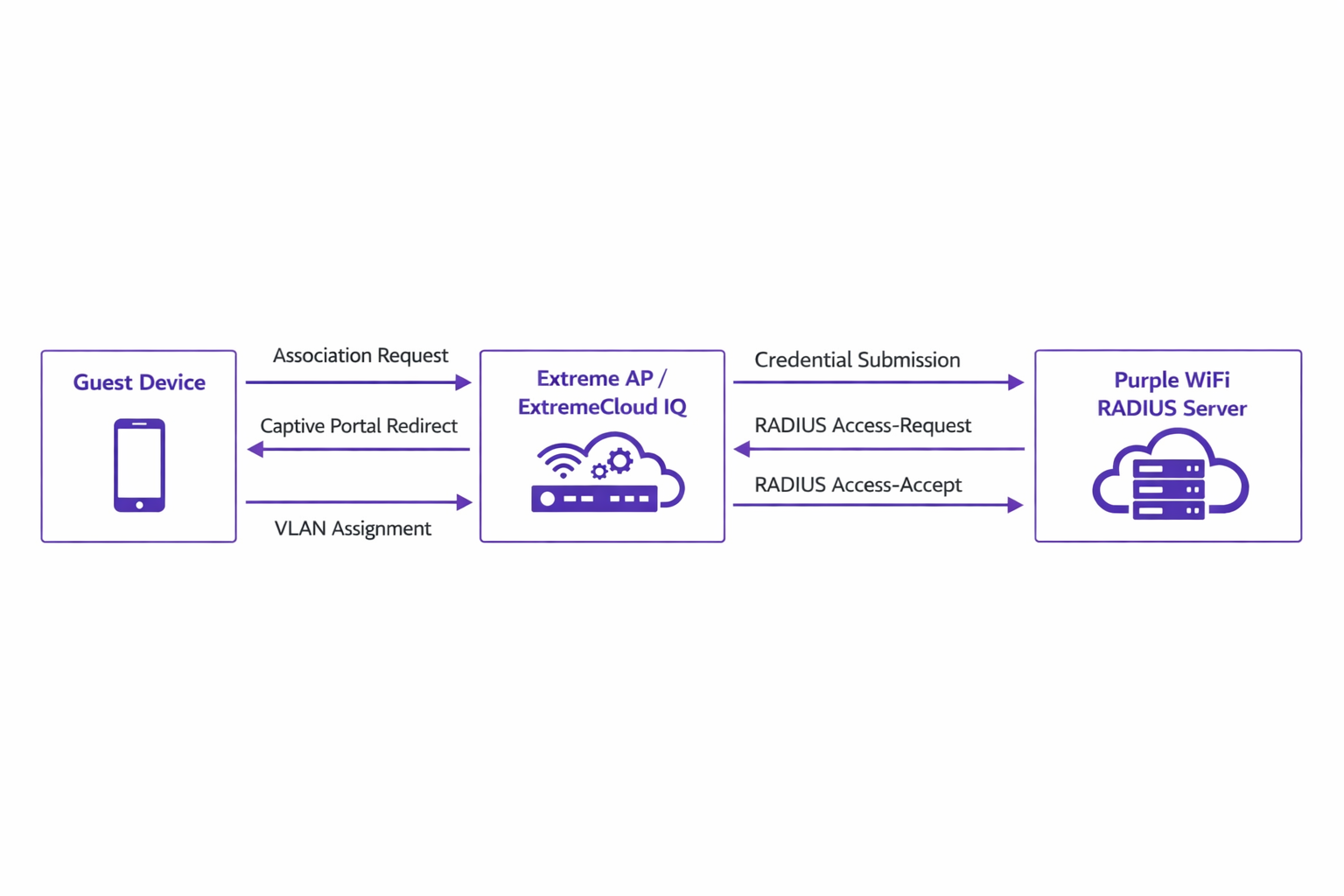
- Association : L'appareil invité s'associe à l'AP Extreme.
- Redirection : L'AP redirige le navigateur de l'appareil vers le portail Purple.
- Authentification : L'utilisateur complète le flux d'authentification (par exemple, connexion sociale, soumission de formulaire) sur la plateforme Purple.
- RADIUS Access-Request : Le backend de Purple communique avec l'AP Extreme via RADIUS.
- RADIUS Access-Accept : Purple envoie un message Access-Accept, contenant souvent des attributs spécifiques tels que
Tunnel-Private-Group-IDpour l'attribution de VLAN. - Autorisation : L'AP déplace le client vers l'état authentifié, en appliquant le VLAN et les politiques QoS désignés.
Ce flux est essentiel pour maintenir la sécurité du réseau et s'aligner sur des normes telles que IEEE 802.1X, offrant un contrôle d'accès basé sur les ports adapté aux environnements WiFi invités sans fil.
Compatibilité Matérielle
L'intégration est entièrement prise en charge sur l'ensemble du portefeuille Extreme Networks géré par ExtremeCloud IQ. Cela inclut la série 302 économique (par exemple, AP302W) idéale pour les chambres d'hôtel, les séries 410 et 460 à haute densité adaptées aux centres de conférence, et les derniers AP de la série 630 prenant en charge le Wi-Fi 6E pour une efficacité spectrale maximale. De plus, les sites utilisant des commutateurs ExtremeXOS sur site peuvent obtenir des résultats similaires en configurant les profils de serveur RADIUS et les redirections de Captive Portal via la CLI ou les interfaces de gestion héritées.
Guide d'Implémentation
Le déploiement de Purple au sein d'ExtremeCloud IQ nécessite une configuration précise des politiques réseau et des paramètres AAA.
Étape 1 : Configuration du SSID et du Captive Portal
Naviguez vers la Politique Réseau dans ExtremeCloud IQ et créez un nouveau SSID pour l'accès invité. Sous les paramètres du Captive Portal, sélectionnez 'External Captive Portal' et saisissez l'URL spécifique fournie par votre tableau de bord Purple.
Il est crucial de configurer correctement le Walled Garden. Le walled garden permet aux appareils pré-authentifiés d'accéder aux domaines nécessaires pour charger le Captive Portal. Vous devez mettre sur liste blanche tous les domaines du portail Purple, les réseaux de diffusion de contenu (CDN) associés et tous les fournisseurs d'authentification tiers (par exemple, Facebook, Google) que vous avez l'intention de prendre en charge. Une configuration incorrecte du walled garden entraînera l'échec du chargement du portail.
Étape 2 : Configuration des serveurs AAA et RADIUS
Dans la configuration du SSID, naviguez vers les paramètres AAA (Authentication, Authorization, and Accounting). Ajoutez les serveurs RADIUS de Purple comme serveurs d'authentification primaire et secondaire.
- Port d'authentification : UDP 1812
- Port de comptabilité : UDP 1813
Assurez-vous que le secret partagé correspond exactement à ce qui est configuré dans le portail Purple. Ne négligez pas la comptabilité RADIUS. Les paquets de comptabilité fournissent à Purple des données de session, y compris la durée de connexion et les volumes de transfert de données, qui sont fondamentales pour générer des analyses précises et maintenir des registres de conformité.
Étape 3 : Attribution Dynamique de VLAN (Facultatif mais Recommandé)
Pour une sécurité et une segmentation réseau améliorées, configurez ExtremeCloud IQ pour accepter les attributs RADIUS pour l'attribution de VLAN. Lorsque Purple envoie le message Access-Accept, il peut inclure l'attribut Tunnel-Private-Group-ID. ExExtremeCloud IQ lira ceci et placera l'appareil client sur le VLAN correspondant. Cela permet une segmentation dynamique — par exemple, isoler les invités standards des membres fidèles ou des appareils IoT, en s'alignant sur les principes robustes de Internet of Things Architecture: A Complete Guide .
Bonnes Pratiques
- Gestion des Certificats: Assurez-vous que votre réseau n'effectue pas d'inspection SSL sur le trafic destiné au Captive Portal Purple. Les systèmes d'exploitation mobiles modernes (en particulier iOS) mettent en œuvre une validation stricte des certificats ; le trafic intercepté déclenchera des avertissements de sécurité et interrompra le flux du Captive Portal.
- Maintenance du Walled Garden: Révisez et mettez à jour régulièrement les entrées du walled garden. Les fournisseurs d'authentification tiers mettent fréquemment à jour leurs plages d'adresses IP et leurs points de terminaison CDN.
- Authentification Basée sur le Profil: Tirez parti de l'authentification basée sur le profil de Purple pour simplifier l'accès des visiteurs récurrents, améliorant l'expérience utilisateur tout en maintenant la sécurité.
- Stratégie de Contenu: Lors de la conception du Captive Portal, envisagez d'utiliser des outils modernes pour optimiser le message. Consultez Generative AI for Captive Portal Copy and Creative pour des stratégies visant à améliorer les taux de conversion.
Dépannage et Atténuation des Risques
Lors de l'intégration d'ExtremeCloud IQ avec Purple, les modes de défaillance les plus courants se produisent pendant la phase de configuration initiale.
Symptôme: Le Captive Portal ne se charge pas
- Cause: Configuration incorrecte du walled garden ou échecs de résolution DNS dans l'état de pré-authentification.
- Atténuation: Vérifiez que l'appareil client reçoit une adresse IP et un serveur DNS valides via DHCP. Confirmez que tous les domaines Purple et les points de terminaison CDN requis sont explicitement autorisés dans la politique du walled garden.
Symptôme: L'authentification échoue (le client reste non authentifié)
- Cause: Inadéquation du secret partagé RADIUS ou problèmes d'accessibilité réseau entre l'AP Extreme et les serveurs RADIUS de Purple.
- Atténuation: Vérifiez le secret partagé dans ExtremeCloud IQ et le tableau de bord Purple. Assurez-vous que le trafic UDP sortant sur les ports 1812 et 1813 est autorisé à travers les pare-feu d'entreprise.
Symptôme: Les tableaux de bord d'analyse n'affichent aucune donnée de session
- Cause: La comptabilité RADIUS n'est pas activée ou est mal configurée.
- Atténuation: Confirmez que le port de comptabilité (UDP 1813) est configuré dans le profil AAA et que l'AP transmet avec succès les paquets de demande de comptabilité.
ROI et Impact Commercial
La mise en œuvre de Purple WiFi sur une infrastructure Extreme Networks transforme l'accès invité d'une utilité fondamentale en un atout commercial stratégique.
Pour les environnements de Retail , l'intégration fournit des informations granulaires sur la fréquentation, le temps de présence et les taux de conversion, comparables aux analyses e-commerce. Dans l' Hospitality , l'attribution dynamique de VLAN assure une segmentation sécurisée tandis que l'authentification basée sur le profil offre une expérience fluide aux clients récurrents, impactant directement les scores de satisfaction.
De plus, les mécanismes robustes de capture de données garantissent la conformité avec les réglementations de protection des données (telles que GDPR) en enregistrant en toute sécurité le consentement de l'utilisateur au point d'accès. En standardisant cette architecture, les organisations peuvent obtenir un retour sur investissement rapide grâce à des campagnes de marketing ciblées, des efficacités opérationnelles et des risques de sécurité atténués.
Termes clés et définitions
ExtremeCloud IQ
Extreme Networks' cloud-driven network management platform that provides centralized visibility, control, and analytics for wired and wireless infrastructure.
Used by IT teams to manage the AP configuration, including the SSID, AAA policies, and captive portal redirect settings.
Captive Portal Redirect
A network technique where HTTP/HTTPS traffic from an unauthenticated client is intercepted and forced to a specific web page (the splash page) for authentication.
The primary mechanism used to present the Purple branded login experience to the guest device.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
The backend communication channel between the Extreme AP and the Purple platform to verify credentials and enforce policies.
Walled Garden
A limited environment that controls the user's access to web content and services before they have fully authenticated to the network.
Crucial for allowing client devices to reach the Purple portal servers, CDNs, and social login providers during the pre-authentication phase.
Dynamic VLAN Assignment
The process of assigning a network client to a specific Virtual LAN based on their identity or profile, rather than the physical port or SSID they connected to.
Enables IT to segment traffic (e.g., separating standard guests from VIPs) using a single SSID, driven by RADIUS attributes from Purple.
RADIUS Accounting
The component of the RADIUS protocol that tracks network resource consumption, such as session duration and data transferred.
Essential for populating the Purple analytics dashboard with accurate user session data.
WPA3-SAE
Wi-Fi Protected Access 3 - Simultaneous Authentication of Equals. The latest wireless security standard providing robust protection even on open networks.
Supported by modern Extreme APs to provide encrypted guest access while still allowing captive portal redirection.
Tunnel-Private-Group-ID
A specific RADIUS attribute (Attribute 81) used to specify the VLAN ID that should be assigned to an authenticated user.
The specific technical parameter Purple sends back to ExtremeCloud IQ to trigger dynamic VLAN assignment.
Études de cas
A 400-room hotel deploying Extreme AP410i units needs to provide tiered WiFi access: standard guests receive 5 Mbps bandwidth on VLAN 100, while loyalty members receive 20 Mbps on VLAN 101. How is this achieved using ExtremeCloud IQ and Purple?
- Configure a single open guest SSID in ExtremeCloud IQ with captive portal redirection pointing to Purple.
- In the Purple dashboard, create two user profiles: 'Standard Guest' and 'Loyalty Member', assigning the corresponding bandwidth limits and RADIUS return attributes (Tunnel-Private-Group-ID = 100 and 101, respectively).
- In ExtremeCloud IQ, enable dynamic VLAN assignment within the SSID's AAA policy to accept RADIUS attributes.
- When a user authenticates, Purple verifies their loyalty status, applies the bandwidth policy, and sends the VLAN attribute in the RADIUS Access-Accept message, dynamically segmenting the traffic.
A large retail chain is rolling out ExtremeCloud IQ across 50 locations. They require consistent guest analytics but are experiencing issues where returning users are not being tracked accurately across different stores.
- Ensure all 50 locations are configured under a unified venue hierarchy within the Purple platform.
- Verify that RADIUS Accounting (UDP 1813) is explicitly configured and permitted through the firewall at every site.
- Implement Purple's profile-based authentication to recognize returning devices via their MAC address across the entire estate, ensuring seamless roaming and accurate cross-venue analytics.
Analyse de scénario
Q1. You have configured the captive portal redirect in ExtremeCloud IQ, but when users connect, their devices show a connection timeout instead of the Purple splash page. What is the most likely configuration error?
💡 Astuce :Consider what network access is permitted before the user is fully authenticated.
Afficher l'approche recommandée
The walled garden is misconfigured or too restrictive. The AP is blocking the HTTP/HTTPS traffic required to reach the Purple portal domains and associated CDNs. You must verify and update the walled garden whitelist in the ExtremeCloud IQ policy.
Q2. A venue requires standard guests to be placed on VLAN 20 and staff devices on VLAN 30 using a single SSID. How do you configure ExtremeCloud IQ to support this requirement?
💡 Astuce :Look at the AAA policy settings related to RADIUS responses.
Afficher l'approche recommandée
Enable dynamic VLAN assignment in the AAA policy within ExtremeCloud IQ. Configure the Purple platform to return the 'Tunnel-Private-Group-ID' RADIUS attribute with the value '20' for standard guests and '30' for staff profiles upon successful authentication.
Q3. Users are successfully authenticating and accessing the internet, but the Purple analytics dashboard shows zero data for session duration and data usage. What step was missed during deployment?
💡 Astuce :Which protocol component tracks resource consumption?
Afficher l'approche recommandée
RADIUS Accounting has not been configured. You must configure the AAA profile in ExtremeCloud IQ to send accounting packets to Purple's RADIUS server on UDP port 1813.



