Technical Guides
Deep, expert-led guides covering guest WiFi, analytics, captive portals, and modern venue technology. Each guide includes diagrams, worked examples, and audio podcasts.
209 guides
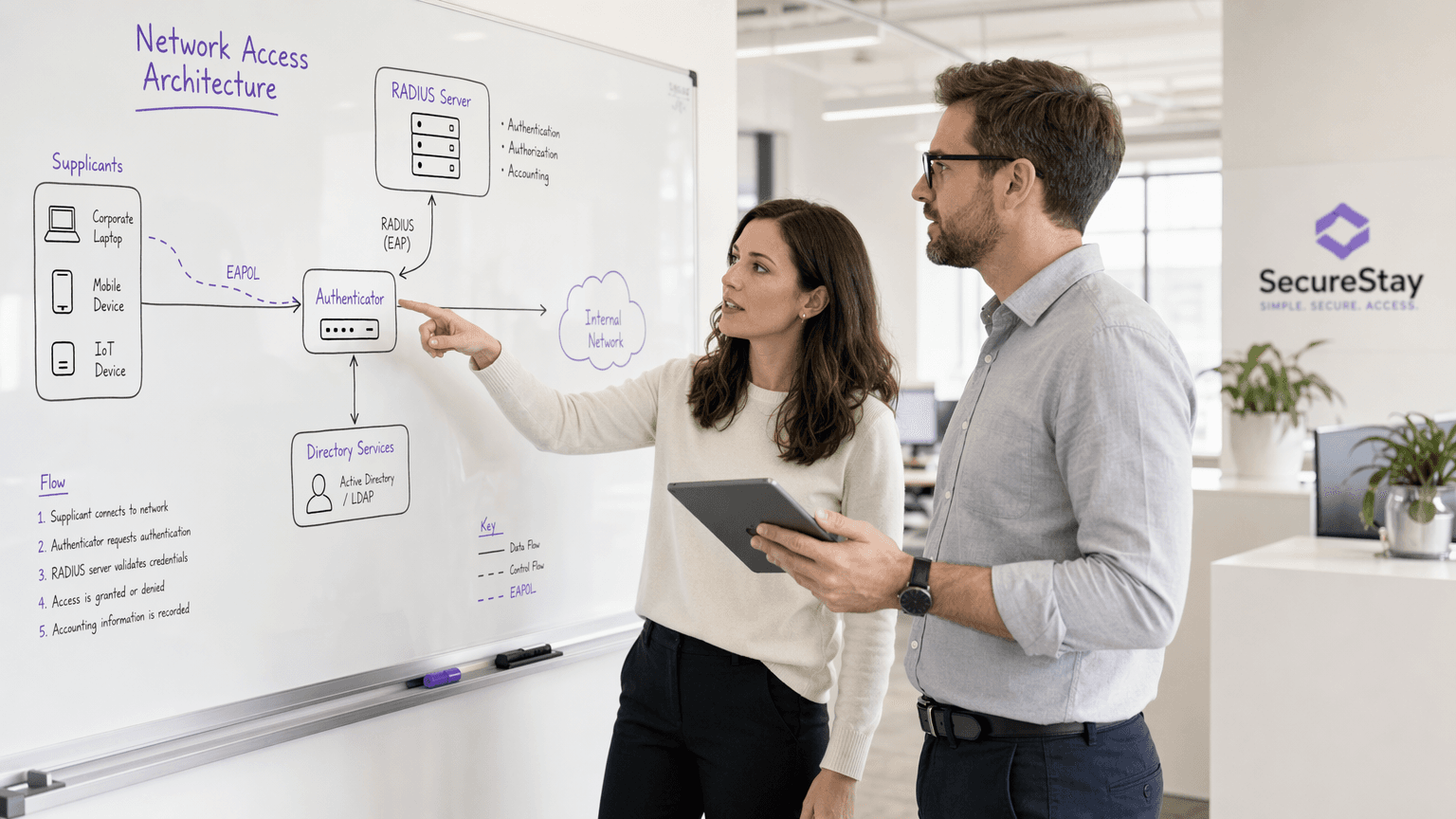
What Is 802.1X Authentication? How It Works and Why It Matters
A comprehensive technical reference guide for IT managers and network architects on IEEE 802.1X authentication. This guide covers the underlying architecture, implementation strategies, security benefits over PSK, and how to effectively deploy enterprise-grade access control alongside guest WiFi solutions.

WPA3: The Next Generation of WiFi Security Explained
This comprehensive technical reference guide explains the architectural shifts introduced by WPA3, including SAE, OWE, and Forward Secrecy. It provides actionable deployment strategies for IT managers and network architects to upgrade enterprise and public venue networks securely.
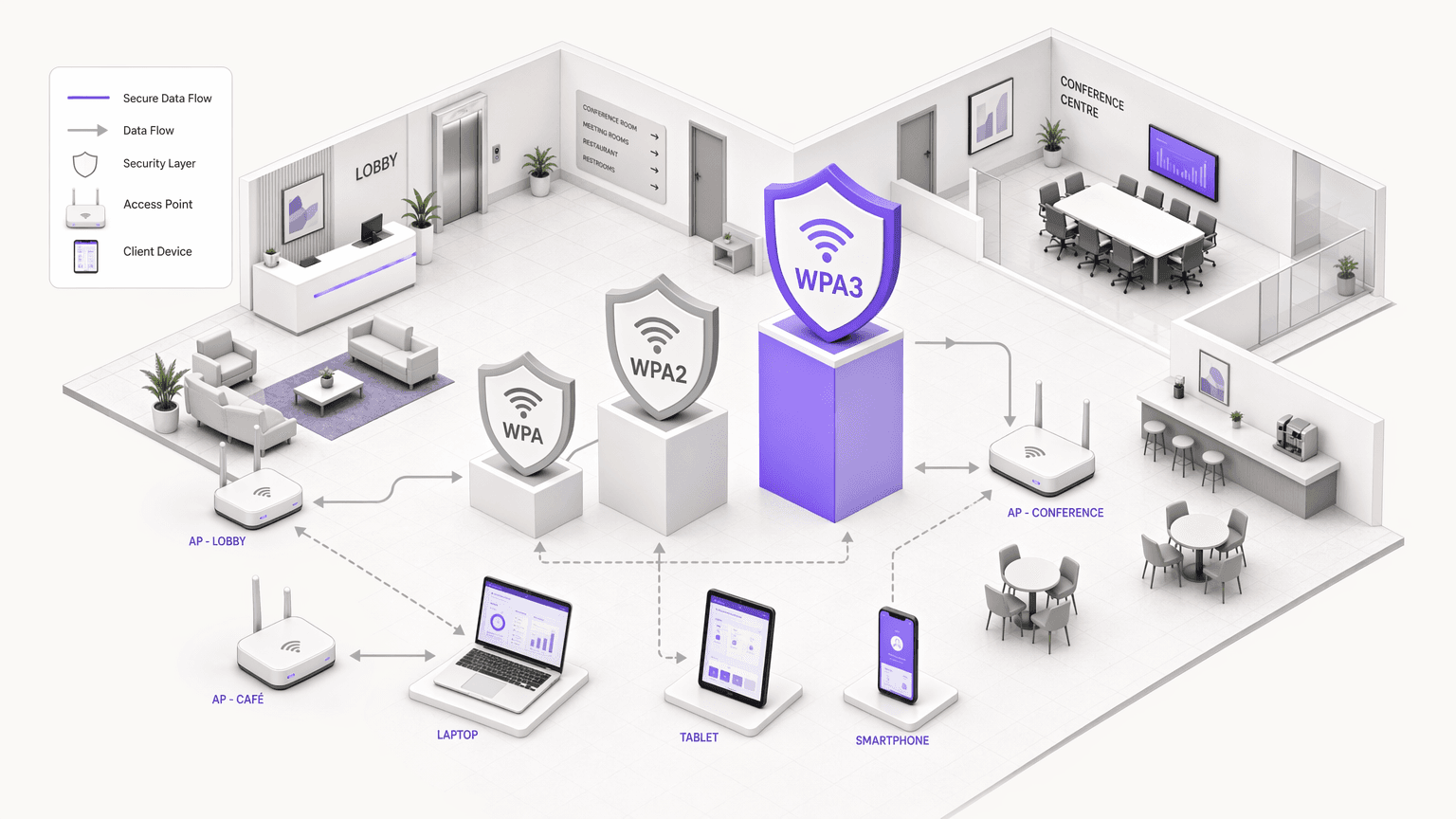
WPA, WPA2 and WPA3: What's the Difference and Which Should You Use?
This authoritative technical reference guide explores the architectural differences between WPA, WPA2, and WPA3 security protocols. It provides actionable deployment recommendations for IT managers and network architects to secure enterprise and guest WiFi environments while ensuring compliance and optimal performance.
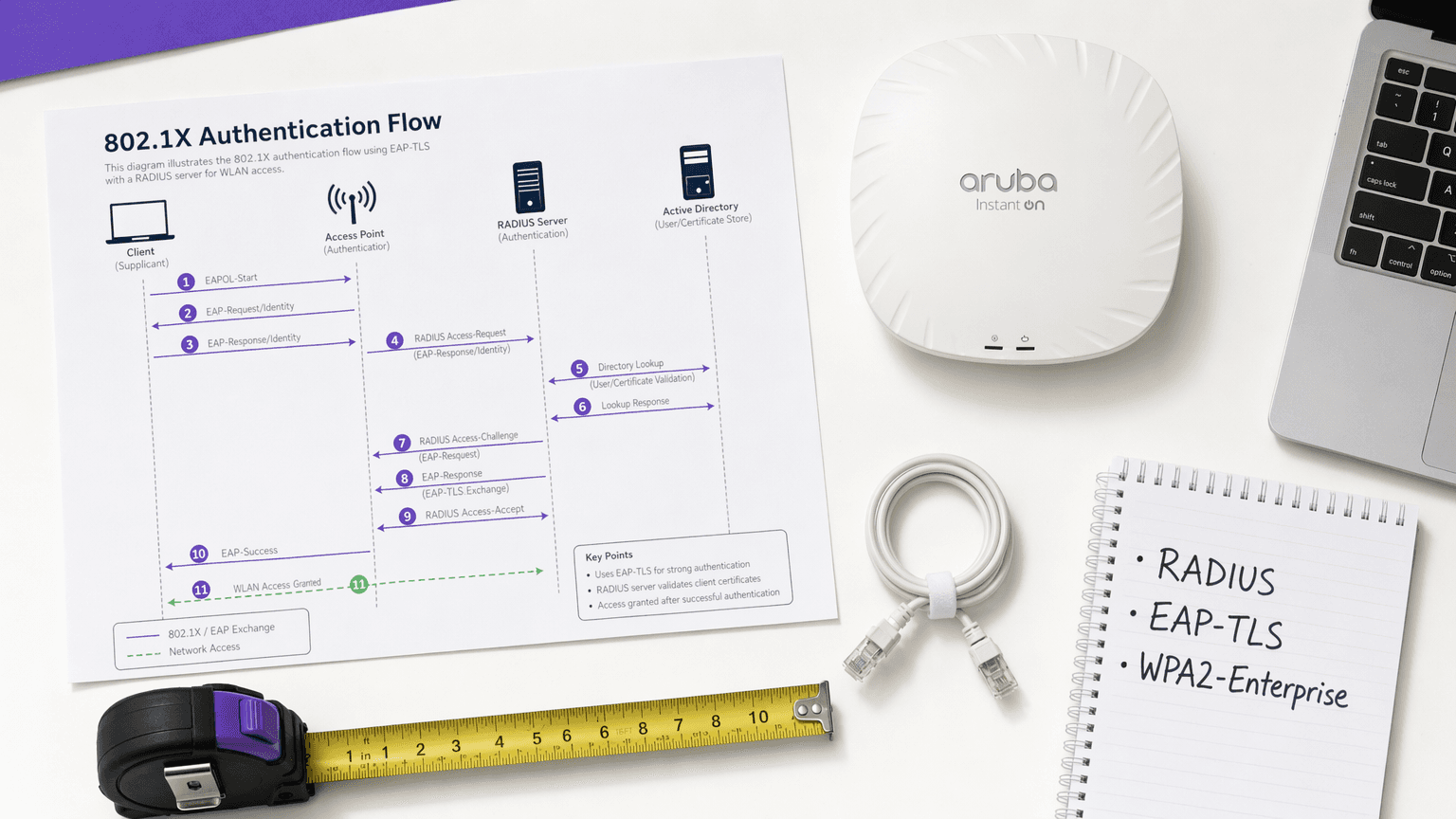
WPA2 Enterprise: The Complete Guide
This guide provides a comprehensive technical reference for WPA2-Enterprise, covering 802.1X architecture, EAP method selection, and phased deployment strategies for enterprise environments. It is designed for IT managers, network architects, and venue operations directors who need to move beyond shared-key WiFi to a scalable, auditable, and compliance-ready authentication model. Purple's platform is positioned as a practical identity management layer for venues deploying secure guest and staff WiFi at scale.
What Is WiFi Security? A Complete Guide to Wireless Network Security
A comprehensive technical reference for IT leaders on securing enterprise wireless networks. This guide covers the evolution of encryption protocols, architectural best practices for segmentation, and defense strategies against common WiFi threats.
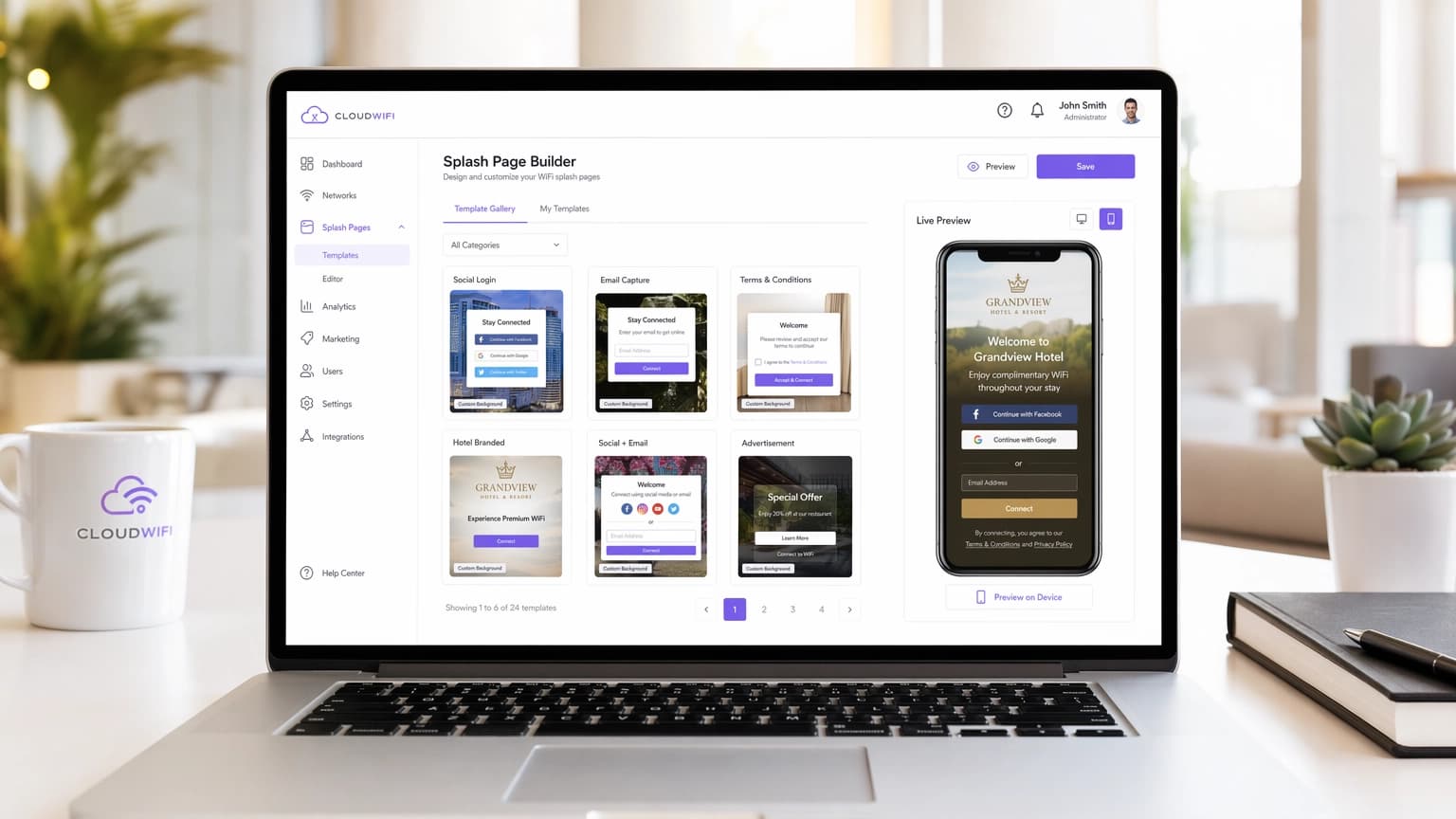
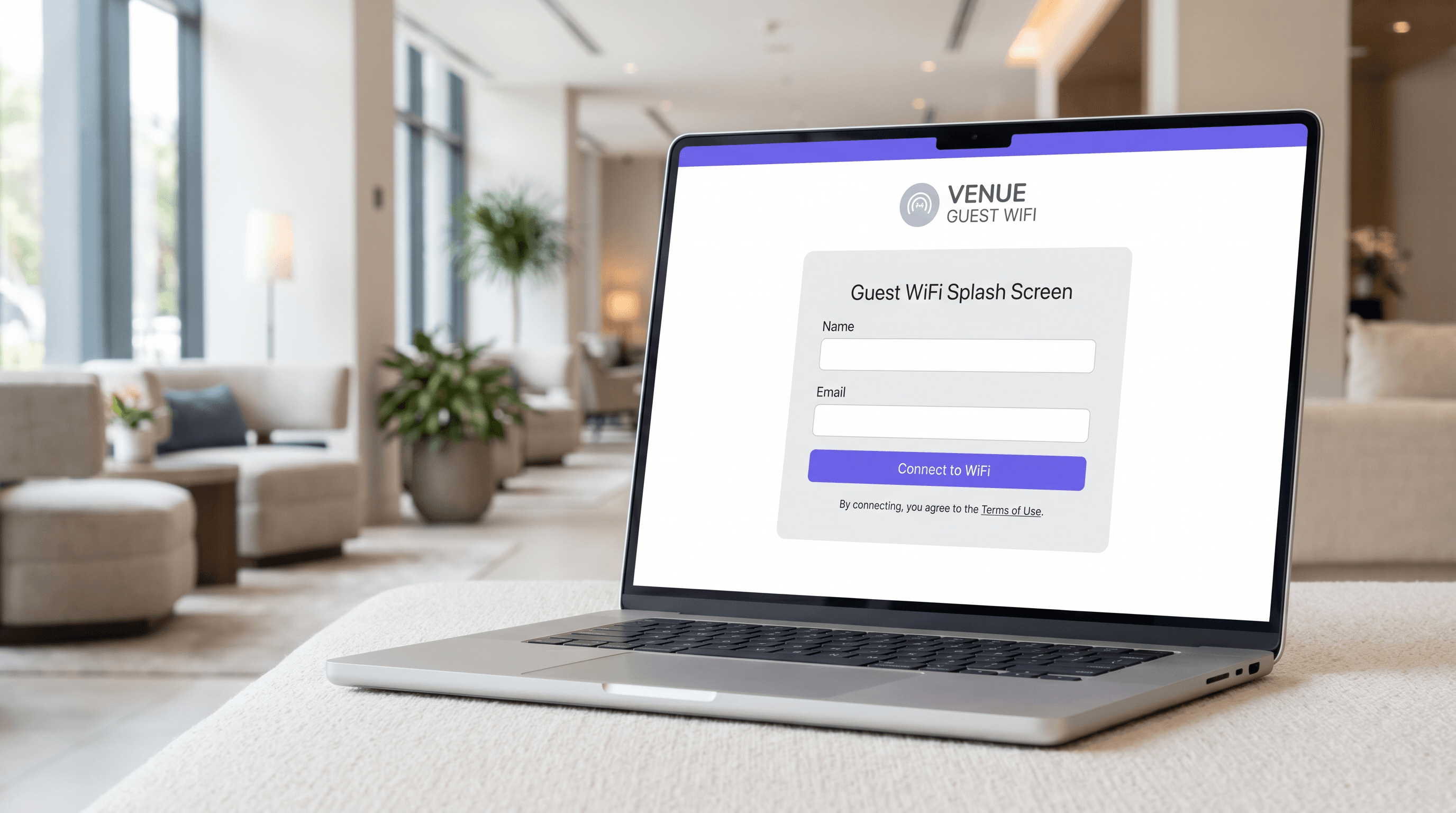
The 10 Best WiFi Splash Page Examples (And What Makes Them Work)
A technical reference guide for IT managers, network architects, and venue operations directors covering the design, architecture, and deployment of high-converting WiFi splash pages. The guide analyses 10 real-world implementation strategies across hospitality, retail, events, and public-sector environments, with specific guidance on authentication methods, GDPR compliance, walled garden configuration, and MAC randomization mitigation.
WiFi Guest Portal: What It Is and How to Optimise It
This authoritative guide details the architecture, implementation, and optimisation of WiFi guest portals. It provides actionable strategies for IT leaders to increase login completion rates, ensure GDPR compliance, and capture high-quality first-party data.
How to Create a Custom WiFi Login Page for Your Brand
This guide provides a comprehensive, implementation-ready reference for IT managers, network architects, and venue operations directors on how to create a fully branded guest WiFi login page — covering captive portal architecture, HTML/CSS customisation, GDPR compliance, and data capture strategy. It moves from technical foundations through to real-world deployment scenarios in hospitality and retail, with measurable business outcomes at each stage. For organisations running Purple's guest WiFi platform, the guide maps directly to the platform's portal builder, analytics, and consent management capabilities.
WiFi Landing Page vs. Splash Page: What's the Difference?
This technical reference guide clarifies the architectural and functional differences between WiFi landing pages and splash pages — two terms frequently conflated by both IT teams and marketing departments. It provides network architects, IT managers, and venue operations directors with actionable deployment strategies to optimise captive portal performance, ensure GDPR and PCI DSS compliance, and maximise ROI across enterprise venues including hospitality, retail, and public-sector environments.
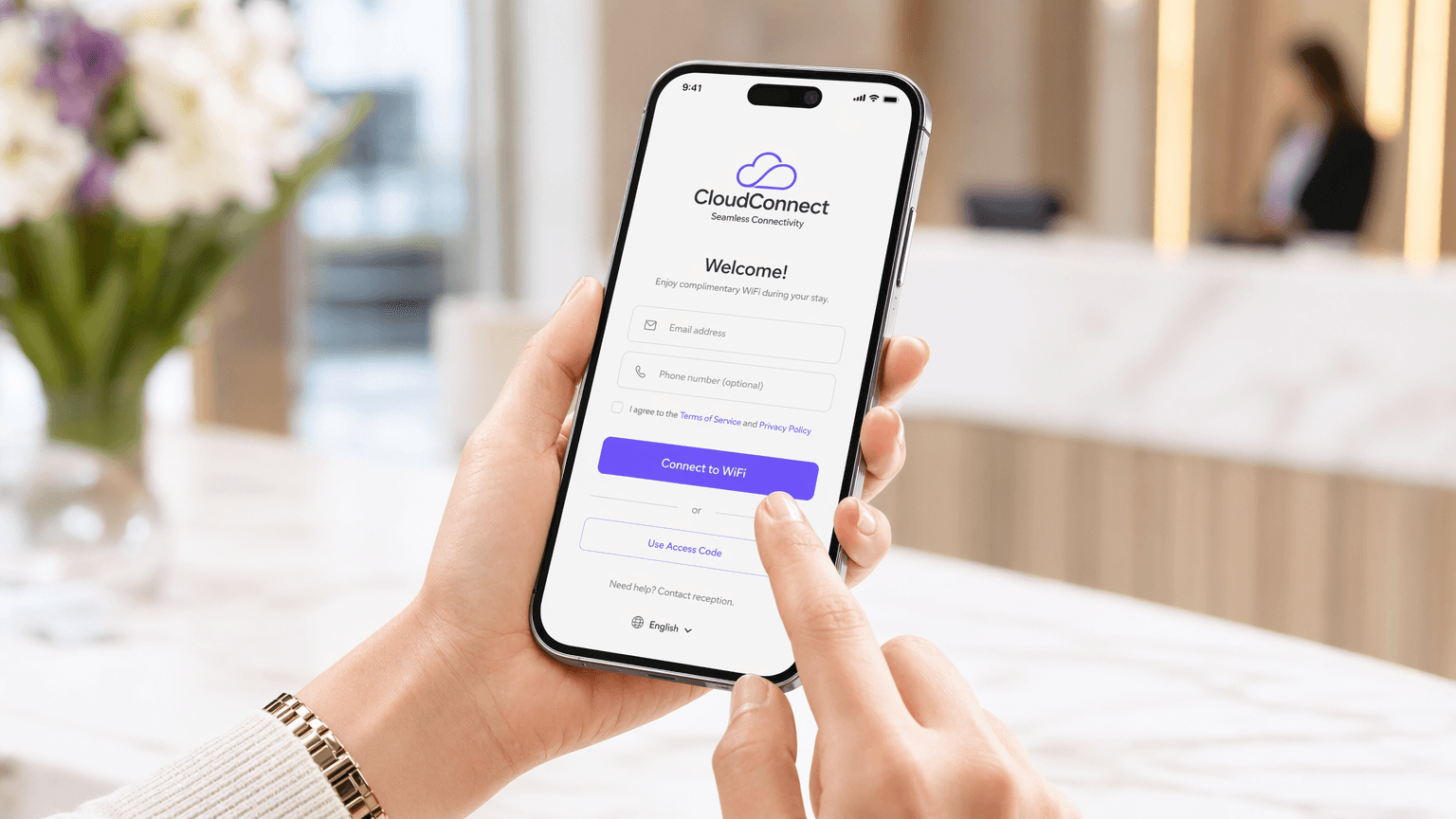
What Is a WiFi Splash Page?
This technical reference guide provides IT managers and network architects with a definitive explanation of WiFi splash pages, their architectural relationship with captive portals, and actionable deployment strategies. It covers implementation best practices, compliance requirements, and how to measure the business impact of your guest WiFi infrastructure.
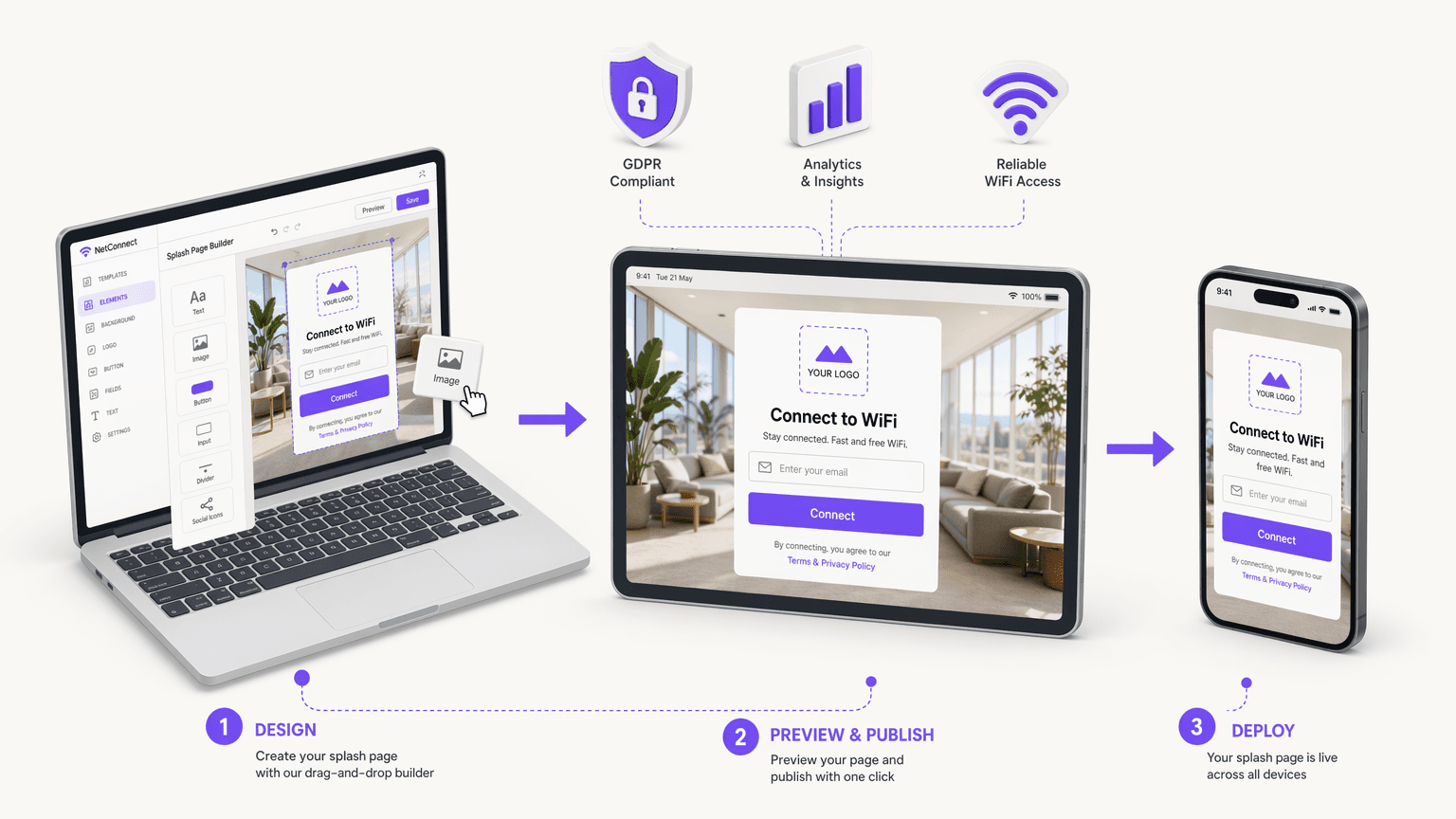
How to Create a WiFi Splash Page: Design, Content and Best Practices
This comprehensive guide explores the architecture, design principles, and deployment strategies required to build an effective WiFi splash page. It provides actionable insights for IT leaders on integrating captive portals with network infrastructure while ensuring GDPR compliance and maximising first-party data capture.
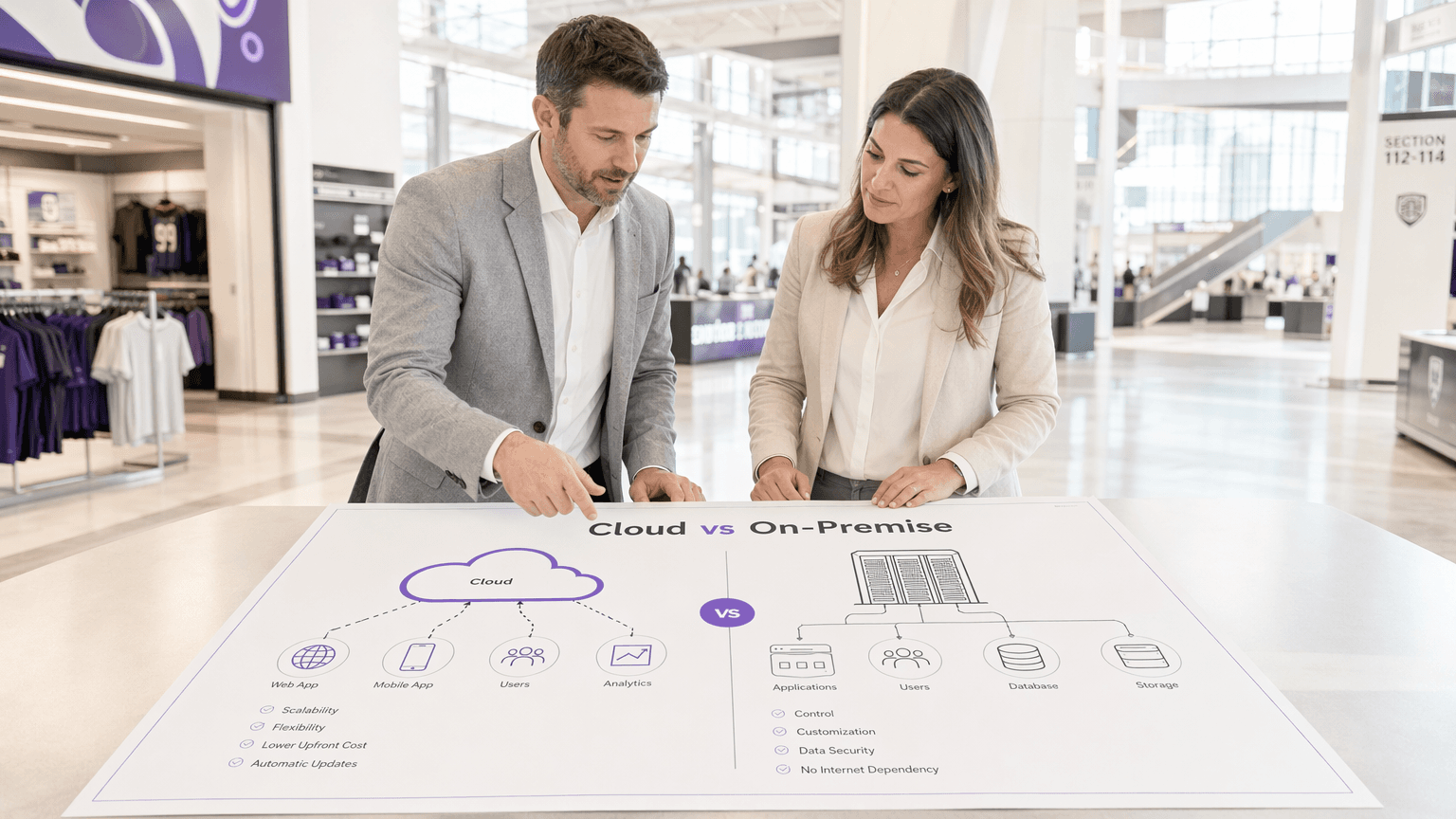
Cloud-Based vs. On-Premise Captive Portal: Which Is Right for Your Business?
A comprehensive technical comparison of cloud-based versus on-premise captive portal architectures. This guide evaluates the deployment speed, cost structures, scalability, and compliance implications to help IT leaders make informed infrastructure decisions.
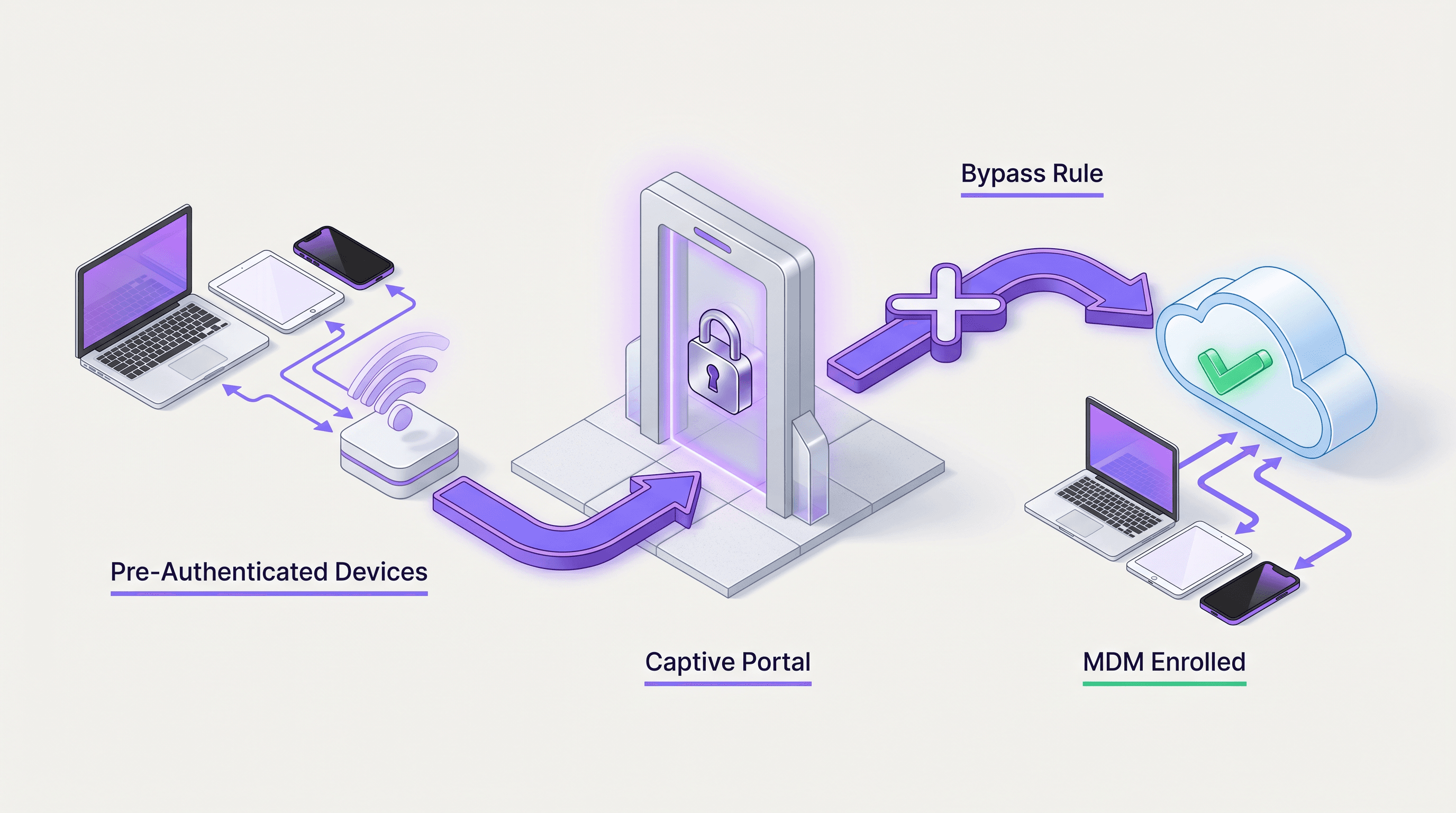
How to Remove a Captive Portal Login (And When You Should)
This authoritative guide explores the technical architecture, use cases, and implementation strategies for removing or bypassing captive portal logins. Designed for senior IT professionals, it provides actionable insights on when to utilize MAC authentication bypass, 802.1X, and OpenRoaming to streamline access while maintaining security and data collection.

WiFi Onboarding and Captive Portal Best Practices
This guide provides a comprehensive technical reference for deploying and optimising a captive portal for guest WiFi across hospitality, retail, events, and public-sector venues. It covers the full onboarding journey — from initial device association and DNS redirection through walled garden configuration, ACL management, authentication, and post-login session control — with concrete implementation scenarios and compliance guidance. IT managers, network architects, and CTOs will find actionable deployment frameworks, risk mitigation strategies, and ROI measurement approaches that map directly to real-world venue operations.
Is a Captive Portal Login Safe? Security Risks and How to Mitigate Them
This technical reference guide provides IT managers, network architects, and venue operations directors with a comprehensive analysis of captive portal security risks — including Man-in-the-Middle attacks, Evil Twin rogue access points, and GDPR compliance exposure. It delivers actionable, vendor-neutral mitigation strategies aligned to IEEE 802.1X, WPA3, and PCI DSS standards, and explains how Purple's guest WiFi platform enables secure, compliant, and commercially valuable guest network deployments at scale.
Captive Portal Design: How to Create a High-Converting Login Experience
This authoritative technical reference guide details how to design, secure, and optimise captive portals for enterprise guest WiFi. It provides actionable recommendations for IT managers and venue operators to maximise login completion rates while ensuring GDPR compliance and robust network security.
The Best Captive Portal Software in 2026: A Comparison Guide
This guide provides an authoritative, vendor-neutral comparison of the leading captive portal software platforms available in 2026, evaluated across features, compliance posture, integration depth, and total cost of deployment. It is written for IT managers, network architects, and CTOs at hotels, retail chains, stadiums, conference centres, and public-sector organisations who need to make a procurement or architecture decision this quarter. The guide covers technical architecture, real-world implementation scenarios, and a structured selection framework to help teams align their network access control strategy with measurable business outcomes.

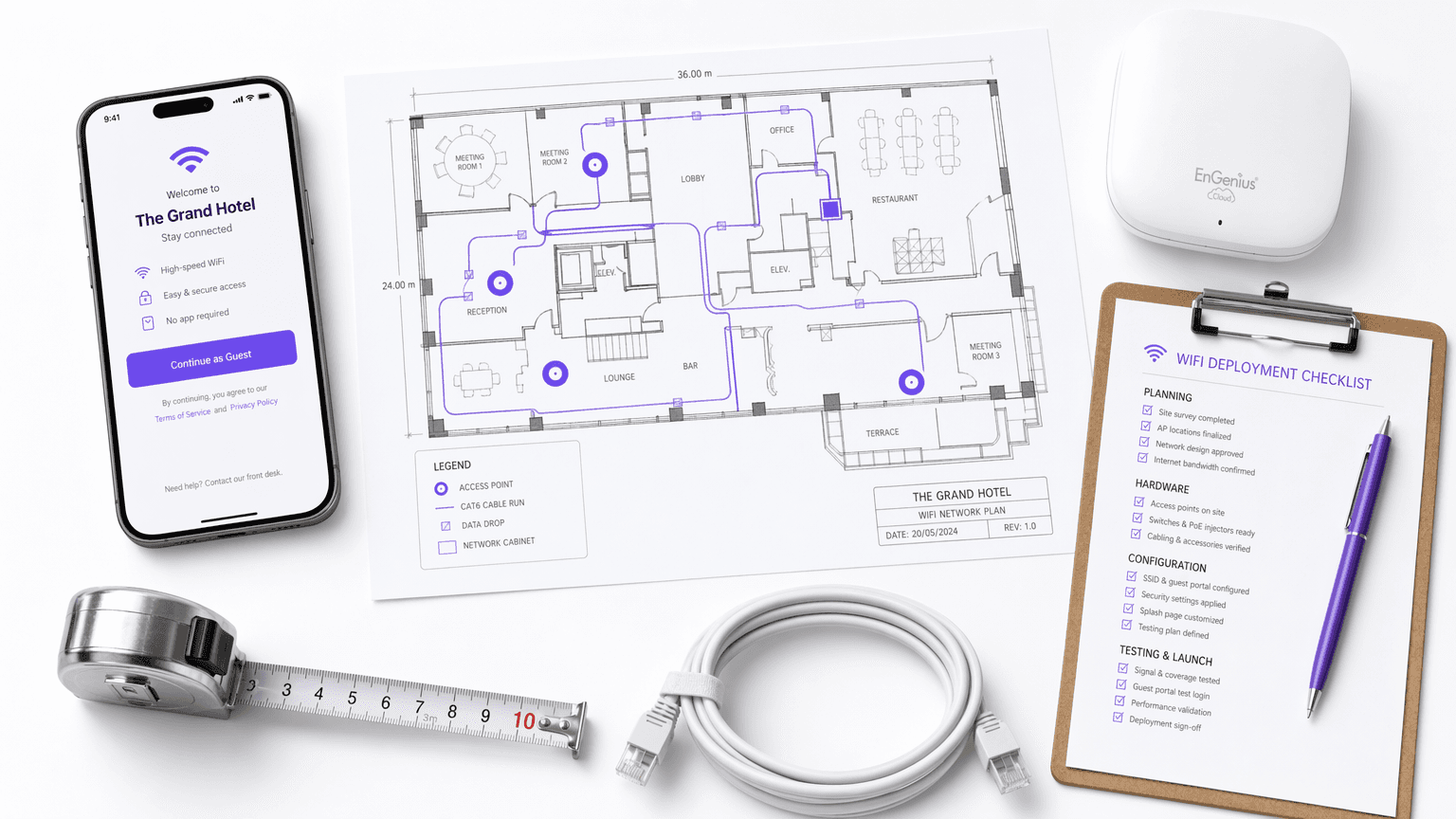
How to Set Up a Captive Portal for Your Business
This authoritative guide provides IT leaders, network architects, and venue operations directors with a step-by-step walkthrough for deploying a secure, compliant captive portal using managed platforms. It covers technical architecture including RADIUS, 802.1X, and walled garden configuration, alongside implementation best practices and how to transform guest WiFi from a cost centre into a strategic first-party data acquisition asset.
How to Build a Captive Portal: A Developer's Guide
A definitive technical guide for IT architects and network managers on building and deploying captive portals. This guide covers underlying protocols, authentication flows, open-source architectures, and a framework for deciding when to build versus when to buy an enterprise managed platform.
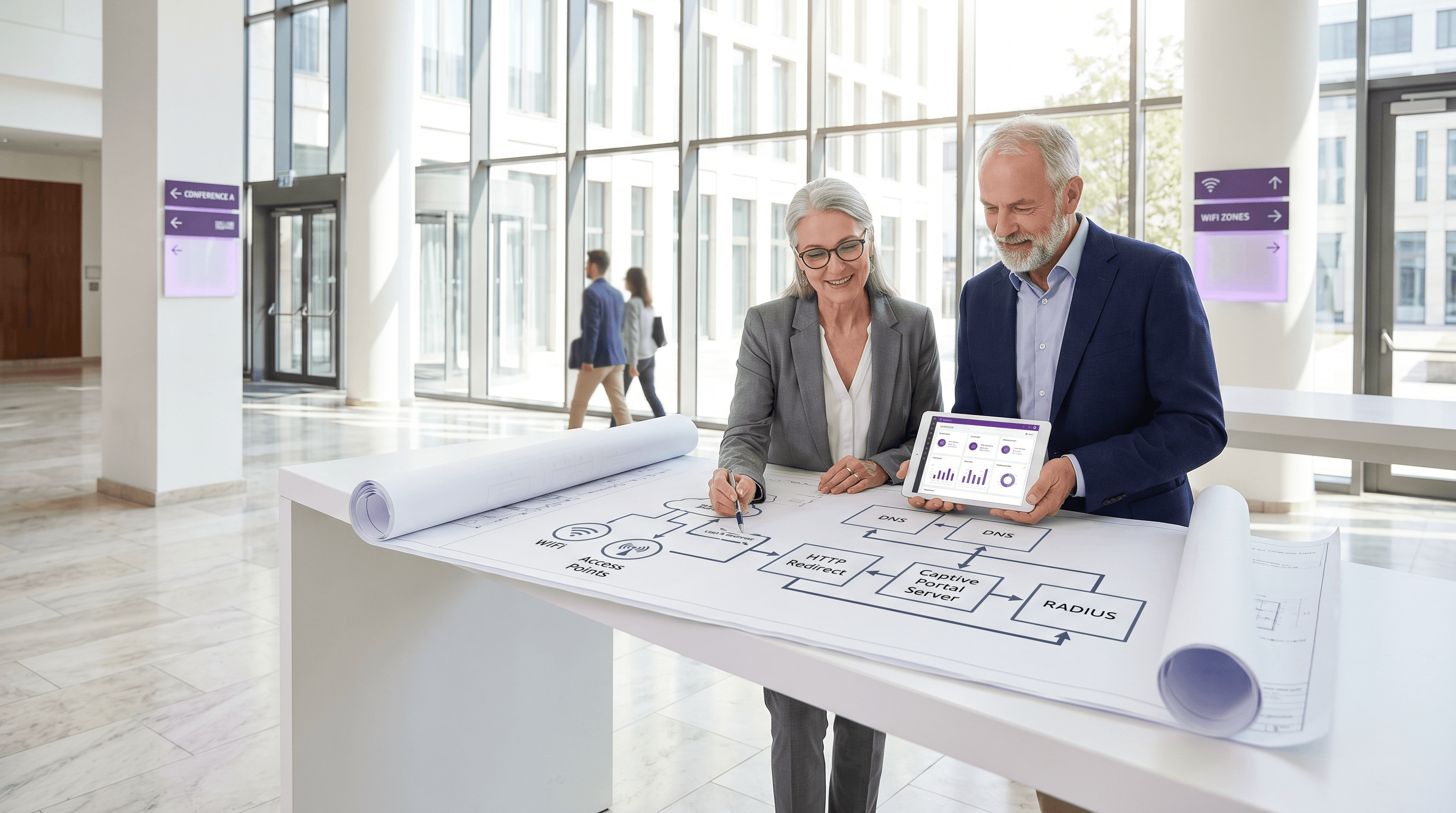
How Does a Captive Portal Work? Technical Deep Dive
A comprehensive technical deep dive into the architecture of captive portals, explaining DNS interception, HTTP redirection, walled gardens, and RADIUS authentication for IT professionals.
What Is a Captive Portal? The Complete Guide
This complete technical guide explains how captive portals work, their underlying network architecture, and how IT leaders can transform basic guest WiFi into a secure, compliant first-party data engine. It covers authentication methods, segmentation best practices, and troubleshooting for enterprise deployments.
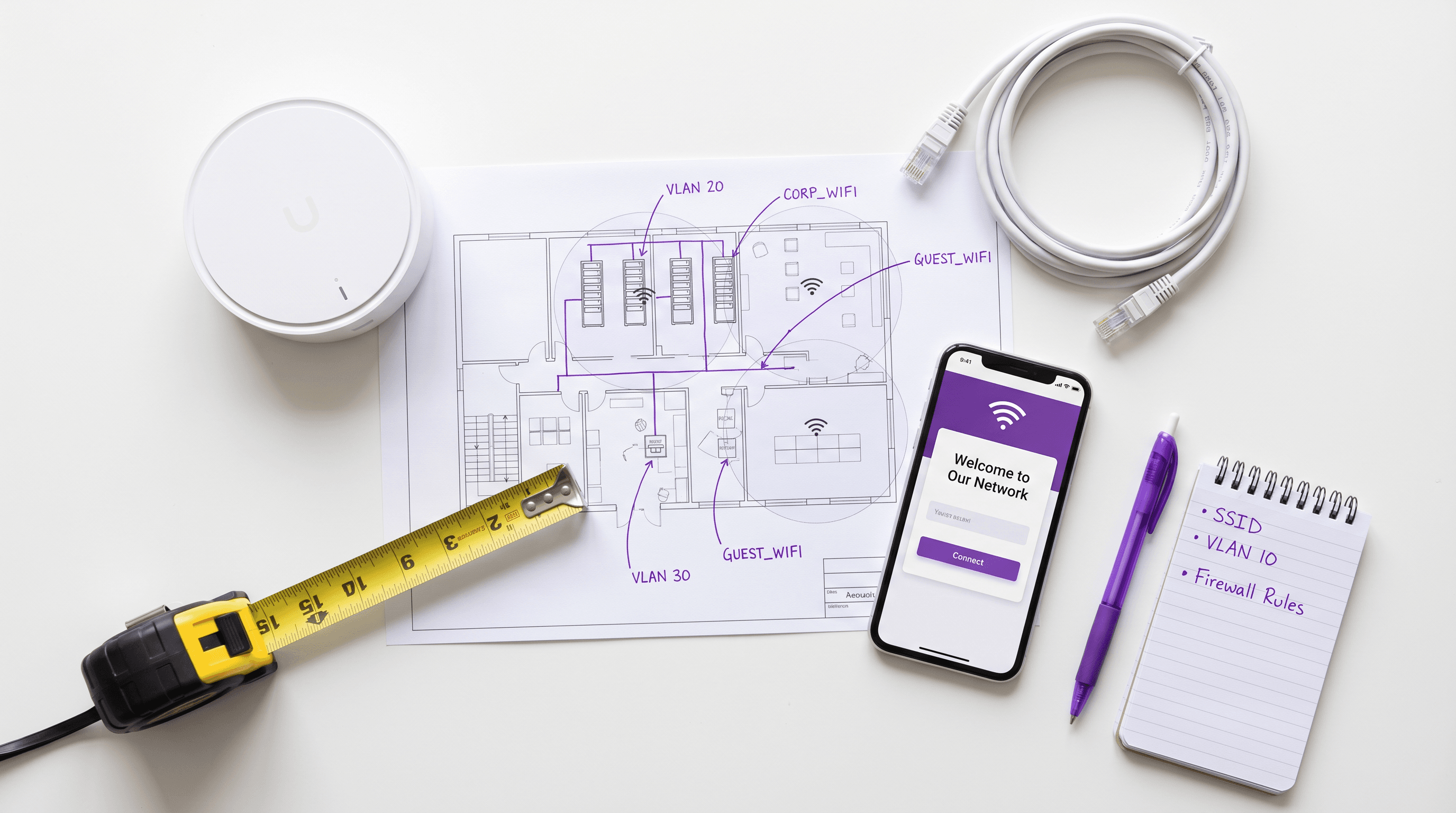
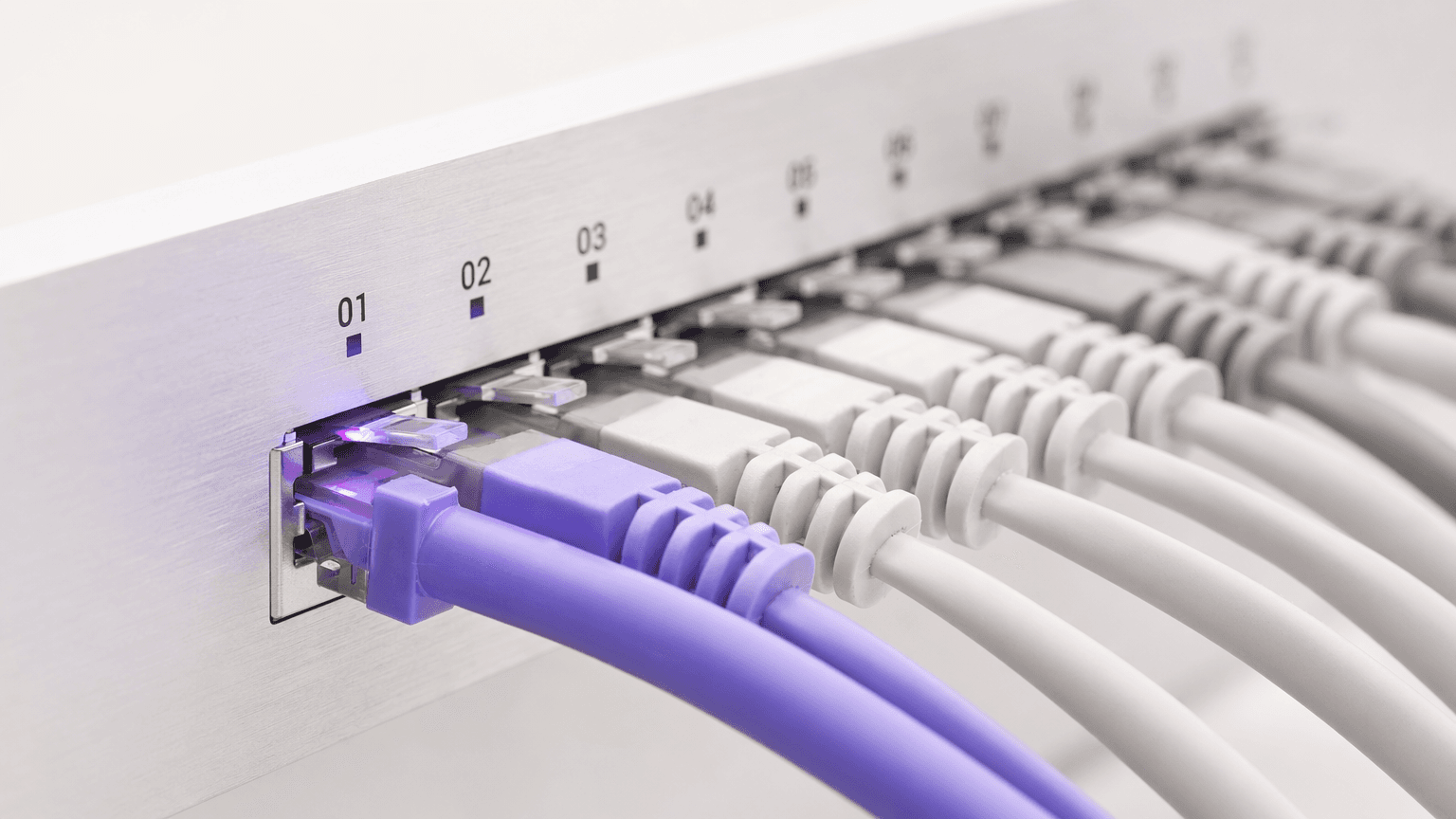
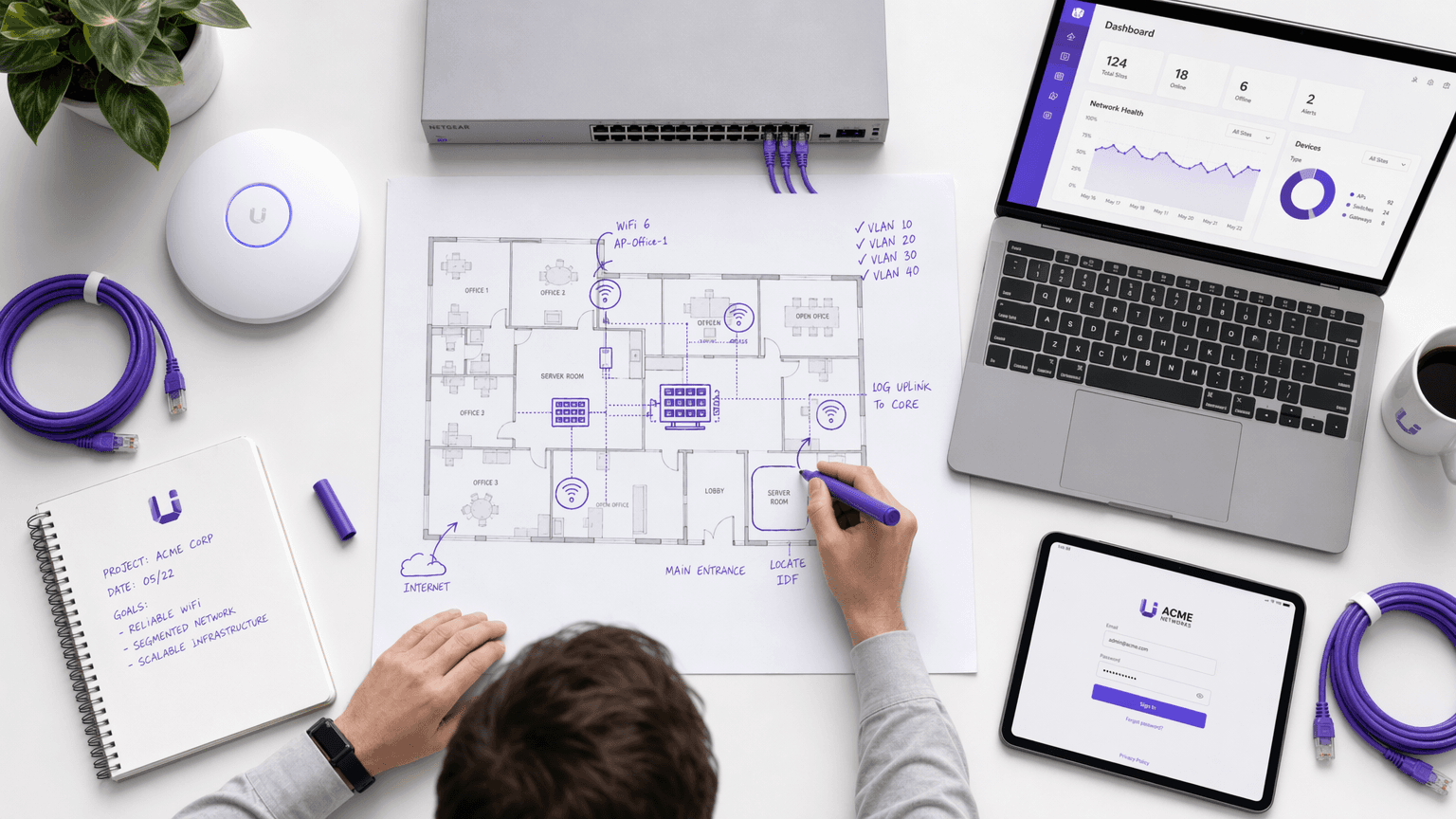
How to Set Up a Secure Guest WiFi Network: Step-by-Step
This guide provides a comprehensive technical walkthrough for IT teams on designing and deploying a secure guest WiFi network from scratch. It covers VLAN segmentation, firewall rule design, captive portal integration, and bandwidth management, with real-world implementation scenarios from hospitality and retail environments. Venue operators and network architects will find actionable, vendor-neutral guidance that addresses both security and compliance requirements.

Guest WiFi Providers: What to Look for When Choosing a WiFi Platform
This technical reference guide provides IT leaders, network architects, and venue operations directors with a definitive framework for evaluating and deploying enterprise guest WiFi platforms. It covers critical architecture standards (IEEE 802.1X, WPA3, GDPR, PCI DSS), integration requirements, and deployment best practices across hospitality, retail, and public-sector environments. The guide demonstrates how modern guest WiFi providers transform connectivity from a cost centre into a strategic data acquisition and revenue-generating asset.
Guest WiFi Use Cases: How Different Industries Are Using Free WiFi
A comprehensive technical reference for IT leaders on deploying guest WiFi as a strategic data acquisition and analytics platform. This guide covers architecture, industry-specific use cases, and best practices for transforming connectivity into measurable business value.



